Job Scam "Internship" From A Compromised UMBC Account
Check The "Reply-To" Address
The job scam below was recently reported to DoIT. The subject of the email is just “Internship” and has a very short message as can be seen below. The name and email of the from and to fields were removed for privacy reasons.
From: COMPROMISED EMAIL <@umbc.edu> Date: Sun, 6 Sep 2020 Subject: Internship To: <@umbc.edu>
Personal_Assistant urgently needed. Contact charlenabolinlyco21@gmail.com for more information or to sign up.
Regards, HR Manager. |
Please note that the phishing message above is supposedly coming froman umbc email but the reply-to in the emails header is set to <charlenabolinlyco21@gmail.com>. This would mean if the user tried to respond to the email above they would not be responding to the umbc email address, but instead they would be directly emailing the scammers at <charlenabolinlyco21@gmail.com>.
If you do receive this or any other email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
The job scam below was recently reported to DoIT. The subject of the email is just “Internship” and has a very short message as can be seen below. The name and email of the from and to fields were...
https://beta.my.umbc.edu/api/v0/pixel/news/95624/guest@my.umbc.edu/41139130f1ac2db6741b2caedb190a9a/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Wed, 09 Sep 2020 19:42:24 -0400
FAKE Offer Of A "Personal Assistant" Job
NOTICE: "Ryan Glenn" Does NOT Want To Hire You.
In the last several days, the UMBC
community has received thousands of fake job offers from "Ryan
Glenn". An example is shown below:
|
You are eligible to apply for an
opening as an Online Personal
Assistant to Ryan Glenn,
Investor Relations Paylocity. You will be working remotely and
getting paid weekly.
You will be required to work for a maximum of an hour daily or six hours
weekly.
Fill the required information if interested in this opportunity.
Name:
Physical Address:
State:
City:
Zip Code:
Phone #:
Email:
Alternate Email:
A little about you and why you think you should be considered:
Send replies to charlenabolinlyco21@gmail.com to apply.
Warm Regards
Charlena B
Publicity Manager.
|
Summary: The message above is coming from
someone you don’t know and who doesn’t offer a last name. The message asks for detailed information that
can be used for identity theft. It is
from a Gmail account which anyone can create under any name not already in use.
If you respond to this message, you will get
something like the one below:
|
From: Ryan Glenn <ryan.glenn.pay@gmail.com>
Date: Sat, Aug 29, 2020 at 5:13 PM
Subject: CONFIRMATION
To:
Hello, further to the interview
session I had with you, I am
pleased to confirm your
appointment as my Personal Assistant.
Please find attached detailed
offer letter which you will be required
to sign, scan and email back to
me, you can as well e-sign and send
a copy as a confirmation of your
acceptance.
Sincerely,
Ryan Glenn
Vice President
FP&A and IR Paylocity
|
There is a Ryan Glenn and he is, in fact, a Vice
President with a corporation called Paylocity.
However, he does not want to hire you.
This is a scam. Please do not reply.
If you do receive email
similar to these examples, or any other email that you suspect is a scam, please
do not click on any URL or reply. Either of those actions confirms to the
sender that your email address is valid. Please forward the message (with the
email headers) tosecurity@umbc.edu.
How do I forward full
email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
To read more articles
published by DOIT Security, visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
In the last several days, the UMBC community has received thousands of fake job offers from "Ryan Glenn". An example is shown below: You are eligible to apply for an opening as...
https://beta.my.umbc.edu/api/v0/pixel/news/95316/guest@my.umbc.edu/61d0213e9f4ecc0a9d49638ca2ff0614/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Mon, 31 Aug 2020 15:01:58 -0400
Mon, 31 Aug 2020 15:02:36 -0400
Fake Cisco Phishing Job Scams
Cisco Systems Is NOT Offering You A Job In A Mass Emailing!
DoIT has been notified of another malicious actor sending out phishing emails claiming to offer job opportunities with Cisco Systems. The email below is similar to the previous phishing attempts, but with a new subject line: “UMBC STUDENT EMPOWERMENT PART TIME JOB OPPORTUNITY.”
From: John Williams <jw821859@gmail.com> Subject: UMBC STUDENT EMPOWERMENT PART TIME JOB OPPORTUNITY Date: August 24, 2020 To: <@umbc.edu>
Dear student,
We got your contact through your school database and I'm happy to inform you that our reputable company CISCOsystems® is currently running a student empowerment program. This program is completely school oriented as it has been designed not to deter you from all school activities which is priority for you and this organization. This program is to help loyal and hardworking students like you secure a part time job with an attractive weekly salary. TO PROCEED WITH THIS JOB OFFER, KINDLY REPLY TO THIS MAIL WITH YOUR ALTERNATE E-MAIL ADDRESS IN ORDER TO RECEIVE THE FULL JOB DESCRIPTION.
Best Regards,
John Williams, HR Recruit Manager/Consultant CISCOsystems Inc®. |
If you do receive this or any other email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
DoIT has been notified of another malicious actor sending out phishing emails claiming to offer job opportunities with Cisco Systems. The email below is similar to the previous phishing attempts,...
https://beta.my.umbc.edu/api/v0/pixel/news/95307/guest@my.umbc.edu/438bd33a7dc8c63388be709df4731cd9/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Mon, 31 Aug 2020 14:06:12 -0400
Mon, 31 Aug 2020 14:07:20 -0400
Job Scam “Offer” From A Compromised UMBC Account
Fake Job Offer For "Online Personal Assistant"
Recently the DoIT has been notified of a job scam using a compromised UMBC email account to send out fake job offers. An example of the email (with the name of the sender removed for privacy) is shown below.
From: COMPROMISED ACCOUNT <@umbc.edu> Date: Thu, Aug 27, 2020 Subject: Offer To:
You are eligible to apply for an opening as an Online Personal Assistant to Ryan Glenn, Investor Relations Paylocity. You will be working remotely and getting paid weekly.
You will be required to work for a maximum of an hour daily or six hours weekly.
Fill the required information if interested in this opportunity.
Name: Physical Address: State: City: Zip Code: Phone #: Email: Alternate Email: A little about you and why you think you should be considered:
Send replies to charlenabolinlyco21@gmail.com to apply.
Warm Regards Charlena B Publicity Manager |
Please note that this phishing message is coming from a umbc email but the reply-to in the emails headers is set to <charlenabolinlyco21@gmail.com>. This means if the user responds to the email above they would not be responding to the umbc email, instead their email would be sent to the <charlenabolinlyco21@gmail.com>.
If you do receive this or any other email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
Recently the DoIT has been notified of a job scam using a compromised UMBC email account to send out fake job offers. An example of the email (with the name of the sender removed for privacy) is...
https://beta.my.umbc.edu/api/v0/pixel/news/95305/guest@my.umbc.edu/8d43dd99b51da03f52decbba3c7b5892/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Mon, 31 Aug 2020 14:01:40 -0400
Mon, 31 Aug 2020 14:08:25 -0400
Tips to Avoid ID Theft on Campus
Simple Ways To Secure Your Identity
With classes starting back up, malicious actors will try even harder to steal people's information or commit Identity theft. The article that is linked below has some tips for college students to help avoid Identity theft by monitoring your inbox and detecting fraud.
Here are some of the tips that are recommended for college students:
Send sensitive mail to your permanent home or post office box. Sending your more sensitive mail to a PO box or permanent home is considered much more secure.
Important documents should be stored away safely. Make sure documents like your Social Security card, passport, and bank and credit card statements are stored securely. As well to often shred credit card offers and any other paper document that has sensitive financial information.
Never lend your card or debit card to anyone. If you feel uncomfortable about lending your card just say no. This includes lending your card to a friend, or co-signing for a loan or financing for items like a TV. Also at an ATM making sure that no one is ‘shoulder surfing’ your PIN.
Guard your passwords. Do not give out your passwords to anyone, use strong passwords and do not use the same password for multiple accounts.
Watch out for phishing emails. Be careful not to click on links in unsolicited emails and texts. For more information on phishing email campaigns that could affect UMBC please check out the DoIT Security page main page for more updated information.
Make sure that your computer is up-to-date with antivirus and spyware softwares. Always install any updates and patches to your computer's operating system or browser software. These will help to keep your computer safe from malicious softwares.
Be careful while shopping online. For more information on tips to safely online please check out this article from the Better Business Bureau, https://www.bbb.org/article/news-releases/22474-bbb-warning-be-careful-purchasing-from-unknown-websites-during-covid-19
Check your credit report at least once a year. According to the article you are entitled to one free report a year from each of the tree reporting bureaus: TransUnion, Experian, and Equifax. Look for any suspicious activity or inaccuracies. For more information on this please check the BBB article linked below, this article by the Federal Trade Commision (FTC), https://www.consumer.ftc.gov/articles/0155-free-credit-reports.
If you do receive any email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
For more information, please check out:
https://www.bbb.org/article/news-releases/10496-bbb-9-tips-to-avoid-id-theft-on-campus
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
With classes starting back up, malicious actors will try even harder to steal people's information or commit Identity theft. The article that is linked below has some tips for college students to...
https://beta.my.umbc.edu/api/v0/pixel/news/95304/guest@my.umbc.edu/2a53eb72186e06dd9d301ba1ce8d21f4/api/pixel
learn
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Mon, 31 Aug 2020 13:58:28 -0400
Wed, 03 Nov 2021 11:47:07 -0400
“WorkStudy Update!” Job Phishing Scam
Same Scam, Different Details
The UMBC DoIT has been notified of a compromised UMBC account used to send out phishing emails. An example of the email chain is shown below. The name and email address of the compromised UMBC account have been removed for privacy reasons, as well as the name of the user who reported the email.
Initial Scam Message
From: COMPROMISED ACCOUNT <@umbc.edu> Date: Fri, Aug 28, 2020 at 7:47 AM Subject: WorkStudy Update! To:
Good morning! My name is <COMPROMISED ACCOUNT>and i currently work with the UMBC educational planning center and i would like to inform you that there is a job opening opportunity available to you, This opportunity is only part time and is not expected to clash with your current school/study schedule.Kindly send in an instant reply if you are in search of a job so you can receive further information.. |
Follow-up Scam Message
From: career management jobs <careerjobsdepartment@outlook.com> Date: Fri, Aug 28, 2020 at 8:48 AM Subject: Re: WorkStudy Update! To: <@umbc.edu>
Hello <NAME>
Thank you for your interest in the available job position, kindly click on the URL below to view the application portal
https://tinyurl .com/JOB-UPDATE |
The first email is similar to a recent trend in phishing campaigns that we have recently seen, except this one uses the compromised account holder’s name in the email message and has changed the subject to “WorkStudy Update!” These campaigns, even if sent from different users with different subjects do seem to have a pattern of using “WorkStudy” in the subject as well as having a similar email format for both messages.
If the user does respond to the first message showing interest, they will receive the second message from a different email address. This is because in the email headers of the first email from the UMBC account, the reply-to is set to the <careerjobsdepartment@outlook.com> so instead of the user emailing the <@umbc.edu> email they are emailing the scammer directly.
The second email contains a link to a malicious site. If you do receive this email please do not click on the URL. In previous similar scams, the scammer is seeking personal information such as name, phone number, email address, home address, age and current occupation. It also invites the user to ‘tell a bit about themselves’ in a free-form text box.
If you do receive this or any other email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
The UMBC DoIT has been notified of a compromised UMBC account used to send out phishing emails. An example of the email chain is shown below. The name and email address of the compromised UMBC...
https://beta.my.umbc.edu/api/v0/pixel/news/95303/guest@my.umbc.edu/8fc84deb666ad9242e9f0e474365a6e7/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Mon, 31 Aug 2020 13:54:34 -0400
“WorkStudy Offer!” Job Phishing Scam
Compromised UMBC Exploited To Send Fake Job Offer
DoIT was notified today of a scammer sending out emails claiming to be offering a job opportunity. The message came from a compromised Umbc email account, so the From name was removed for privacy in the example below.
From: COMPROMISED ACCOUNT <@umbc.edu> Date: Wed, Aug 26, 2020 Subject: WorkStudy Offer! To:
Good morning! I hope you are well. I would like to share with you this job opportunity,you could earn between $100- $240 weekly. This opportunity is only part time and is not expected to clash with your current school/study schedule.Kindly send in an instant reply if you are in search of a job so you can receive further information |
If the victim responds showing interest they will receive a message from a different email address <careerjobsdepartment@outlook.com> and this email will contain a malicious URL. The scammer is seeking personal information such as name, phone number, email address, home address, age and current occupation. It also invites the victim to ‘tell a bit about themselves’ in a free-form text box.
This first email shows a few red flags. For instance, some parts of the message have no spacing, an example of this is “schedule.Kindly”. The email also expresses a sense of urgency with the email asking for the victim to send an “an instant reply.”
If you do receive this or a similar email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
DoIT was notified today of a scammer sending out emails claiming to be offering a job opportunity. The message came from a compromised Umbc email account, so the From name was removed for privacy...
https://beta.my.umbc.edu/api/v0/pixel/news/95196/guest@my.umbc.edu/a83372e47dd9d6c04a6489f4869a3349/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Wed, 26 Aug 2020 23:24:52 -0400
Mon, 31 Aug 2020 11:42:34 -0400
Phishing Email from Fake UMBC IT Desk
Phsihing Attack Sent To Over 1000 UMBC Accounts
A compromised UMBC account was used to send phishing emails to over 1200 other UMBC accounts today. These malicious emails, claiming to be from the “UMBC IT Desk,” contained a link to a fake myUMBC login page, potentially allowing the malicious actors to steal any passwords entered on the site. To prevent further malicious activity, DoIT Security has scrambled the password of the account used to send the emails.
From: <name removed>
Date: Mon, Aug 24, 2020 at 10:40 AM
Subject: COVID-19 Update
To:
This is the UMBC IT Desk. Kindly Update your details to avoid beinglocked out of your email account.
Follow the URLbelow to proceed to setup umbc.edu/cas-web/login/Update
IT DeskUMBC
The link leads to this fake login page:
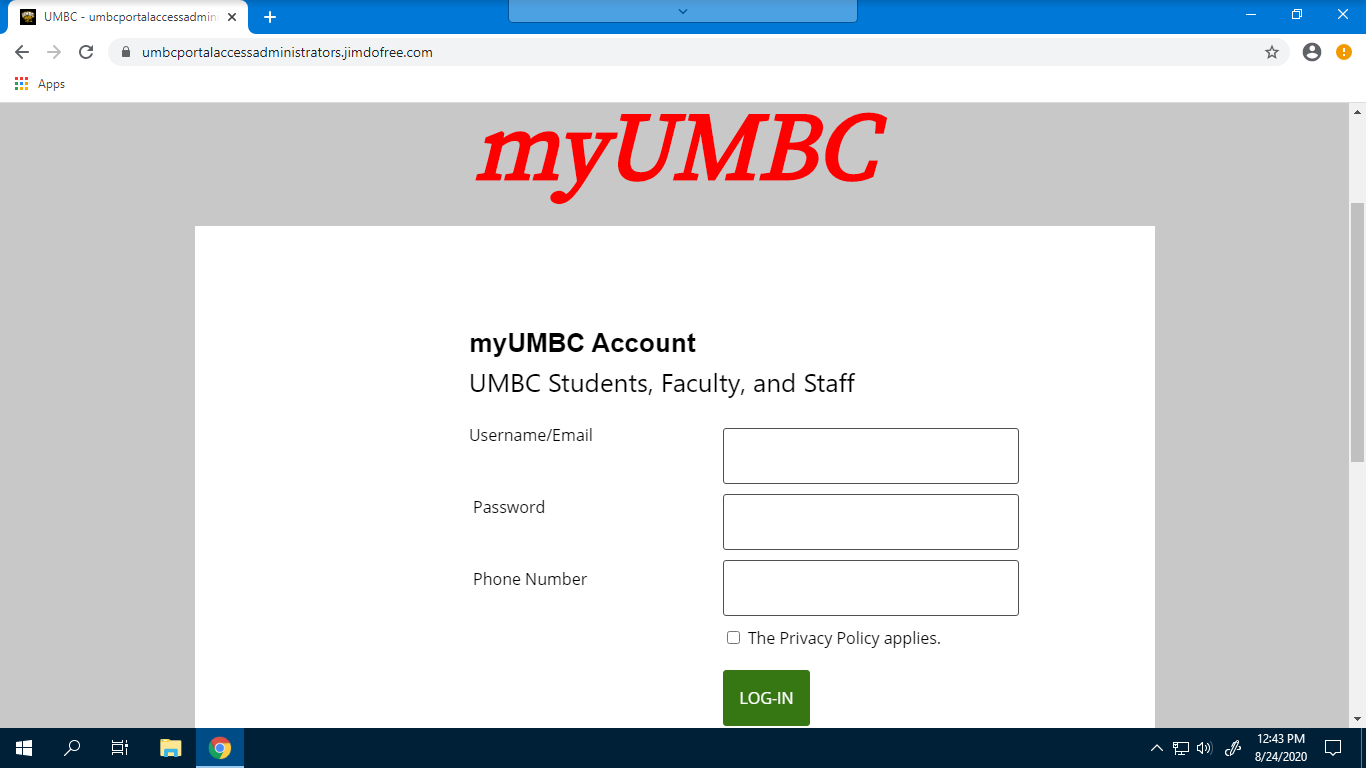
Always check the URL before entering credentials online. Notice that this site is not in the umbc.edu domain, despite claiming to be myUMBC. In addition, you can compare it to the real login page by navigating to myUMBC without using a link to see that it does not match.
As of this writing, approximately 150 people have clicked this link. If you have entered your UMBC password after clicking the link in this phishing email, please change it to something substantively different as soon as possible. Instructions for doing so can be found here:https://wiki.umbc.edu/pages/viewpage.action?pageId=1867939.
If you do receive any email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
]]>
A compromised UMBC account was used to send phishing emails to over 1200 other UMBC accounts today. These malicious emails, claiming to be from the “UMBC IT Desk,” contained a link to a fake...
https://beta.my.umbc.edu/api/v0/pixel/news/95109/guest@my.umbc.edu/76a7aa4617da4d330558aa3e1cf11818/api/pixel
covid19
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 16:00:48 -0400
Account data breach: Zoosk (2020)
Credentials Breach Report
In January 2020, Zoosk 2020, an online dating service, suffered a data breach. This breach contained 24 million users data that was posted online. The user information includes dates of birth, drinking habits, education levels, email addresses, ethnicities, family structure, genders, geographic locations, income levels, names, nicknames, physical attributes, political views, relationship statuses, religions, sexual orientations,and smoking habits. While the passwords posted were not valid for access to UMBC accounts, we suggest you change your UMBC password as a safety precaution.
76 UMBC accounts were victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a Zoosk (2020) account, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach visit: https://haveibeenpwned.com/.
More about Zoosk(2020) data breach:
https://grahamcluley.com/zoosk-hacking/
https://www.justice4you.com/blog/zoosk-data-breach.html#:~:text=According%20to%20the%20notice%2C%20an%20unauthorized%20party%20breached,by%20email%2C%20including%20more%20than%20560%2C000%20California%20residents.
If you have any questions or concerns email us: security@umbc.edu
Information about this breach was provided to us by Have I Been Pwned(HIBP).
_____________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Need to set up a recovery email for your UMBC account?
Follow the instructions here: https://my3.my.umbc.edu/groups/itsecurity/posts/94776
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
In January 2020, Zoosk 2020, an online dating service, suffered a data breach. This breach contained 24 million users data that was posted online. The user information includes dates of birth,...
https://beta.my.umbc.edu/api/v0/pixel/news/95090/guest@my.umbc.edu/e19d02e85d33f6e43f12987559f2f8a4/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 13:00:41 -0400
Account data breach: Drizly
Credentials Breach Report
In July 2020, an online alcohol delivery service, Drizly, suffered a data breach. This breach contained 2.5 million customers data that was sold online, and then posted on a hacking forum. The customer information includes names, email addresses, IP addresses, physical addresses, date of birth, phone numbers, and passwords. No financial information was leaked.
106 UMBC accounts were victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a Drizly account, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach visit: https://haveibeenpwned.com/.
More about Drizly data breach:
https://techcrunch.com/2020/07/28/drizly-data-breach/
https://www.forbes.com/sites/katedingwall/2020/07/29/alcohol-e-commerce-giant-drizly-hit-with-huge-data-breach/#63b0d40b5a96
If you have any questions or concerns email us: security@umbc.edu
Information about this breach was provided to us by Have I Been Pwned(HIBP).
_____________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Need to set up a recovery email for your UMBC account?
Follow the instructions here: https://my3.my.umbc.edu/groups/itsecurity/posts/94776
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
In July 2020, an online alcohol delivery service, Drizly, suffered a data breach. This breach contained 2.5 million customers data that was sold online, and then posted on a hacking forum. The...
https://beta.my.umbc.edu/api/v0/pixel/news/95089/guest@my.umbc.edu/89316cd852a70895cf563be575901740/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776441867
https://assets1-beta.my.umbc.edu/images/avatars/group/7/large.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/small.png?1776441867
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776441867
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776441867
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 12:27:41 -0400