Amazon Account Phishing Scam
Contact By A Fake Amazon Rep About A Fake Account
According to the article linked below, malicious actors have been recently noticed in the UK. The actors pose as an Amazon customer service representative. The goals of this phishing campaign is to steal personal and financial information from Amazon users.
The article warns that users are being contacted through emails and/or phone calls claiming that they have opened an Amazon Prime account. The malicious actor then will inform the users that the account was opened fraudulently through a security flaw on their computer.
The malicious actor then asks the user for remote access to their computer to fix the breach. Allowing this will let the malicious actor steal personal and financial information, including passwords and even banking information.
Another version of this scam is very similar but claims there is an Amazon-Music subscription instead of an Amazon Prime subscription.
Amazon has stated that that they will never cold-call a customer, and will never ask for remote access to a computer or payment over the phone. Never give any details to an unknown caller, and if you’re not sure if the call is legitimate or not, log into your official Amazon account and contact customer support through there.
If you do receive any email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
For more information, please check out:
http://www.irishnews.com/magazine/technology/2020/07/17/news/warning-issued-over-amazon-prime-phishing-scam-2008855/
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
]]>
According to the article linked below, malicious actors have been recently noticed in the UK. The actors pose as an Amazon customer service representative. The goals of this phishing campaign is...
https://beta.my.umbc.edu/api/v0/pixel/news/94777/guest@my.umbc.edu/ab0205fb3f452f797b4af1677ac26bdc/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Tue, 11 Aug 2020 21:14:19 -0400
How to setup an account recovery email address
A Backup If You Forget Your Password
Don't have a recovery email on your UMBC account?
Follow these steps to set up your recovery email. Please use an email address that is not your UMBC email.
Login to your myUMBC account: http://my.umbc.edu/account
Go to https://webadmin.umbc.edu/admin//Security/Setup/View
Click Account security setup
At the top of the page, enter your alternate email address
Scroll down to the bottom of the page and click Update my security settings
Don’t have a secondary email address?
Create one with Google or Yahoo. Instructions can be found here:
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867956
If you have any questions or concerns email us: security@umbc.edu_________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for displaying the headers (you normally don't see them) so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
Don't have a recovery email on your UMBC account? Follow these steps to set up your recovery email. Please use an email address that is not your UMBC email. Login to your myUMBC account:...
https://beta.my.umbc.edu/api/v0/pixel/news/94776/guest@my.umbc.edu/16d6c0be3e248a816b1595d450bb4a06/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Tue, 11 Aug 2020 21:05:31 -0400
Tue, 11 Aug 2020 21:06:12 -0400
Account Data Breach: Wattpad
Major Data Breach: Wattpad
In June 2020, Wattpad suffered a data breach that exposed approximately 270 million records. These records include, names, usernames, email and IP addresses, genders, birth dates and passwords. This information was sold and then published on a public hacking forum.
234 UMBC accounts suffered from this breach; DOIT is currently notifying these individuals via their UMBC emails and/or alternate emails. However, if you have a Wattpad account don't wait; contact the site to see if your information has been exposed.
If you don’t have a alternate email address listed on your UMBC account, follow these instructions below:
Login to your myUMBC account: http://my.umbc.edu/account
Go to https://webadmin.umbc.edu/admin//Security/Setup/View
Click Account security setup
At the top of the page, enter your alternate email address
Scroll down to the bottom of the page and click Update my security settings
DOIT has been notified of this breach via Have I Been Pwned(HIBP).
More about Wattpad data breach visit:
https://www.bleepingcomputer.com/news/security/wattpad-data-breach-exposes-account-info-for-millions-of-users/
https://bestofprivacy.com/data-breaches/wattpad-data-breach-exposes-account-info-for-millions-of-users/#:~:text=Wattpad%20data%20breach%20exposes%20account%20info%20for%20millions,user-generated%20stories%20on%20a%20variety%20of%20different%20topics.
If you have any questions or concerns email us: security@umbc.edu_________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
In June 2020, Wattpad suffered a data breach that exposed approximately 270 million records. These records include, names, usernames, email and IP addresses, genders, birth dates and passwords....
https://beta.my.umbc.edu/api/v0/pixel/news/94775/guest@my.umbc.edu/7a6c7bd768d58c2f9716d0ce3f7190f2/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Tue, 11 Aug 2020 21:01:34 -0400
Be Wary Of These Covid-19 Scams
Some Of The Scams Coming Over Email, Phone, and Text
In the article linked below, BBC News warns of different Covid-19 themed frauds and scams. Many malicious actors follow the headlines just like the rest of us, and when they see a crisis like Covid-19, they take the opportunity to jump on the fear and try to scam as many people as they can.
The article warns of these scams to be wary of:
For more information on these and other phishing attempts at UMBC please visit the DoIT Security page which can be found here https://itsecurity.umbc.edu/.
If you do receive any email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
For more information, please visit:
https://www.bbc.com/news/business-53573408
To read more articles published by DoIT Security please visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
In the article linked below, BBC News warns of different Covid-19 themed frauds and scams. Many malicious actors follow the headlines just like the rest of us, and when they see a crisis like...
https://beta.my.umbc.edu/api/v0/pixel/news/94676/guest@my.umbc.edu/236ccbcd1893176b192d2ab2f0ea31f7/api/pixel
covid19
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Wed, 05 Aug 2020 18:12:32 -0400
Wed, 05 Aug 2020 18:14:26 -0400
Gift Cards Phishing Scams
Another Variant Of A Common Scam
Recently DoIT has been notified of a phishing email scam where the malicious actor is impersonating a UMBC staff member. The name has been removed from the From for privacy reasons, but an example of the email can be seen below:
From: Forged Name <hjacj00909@gmail.com> Date: Mon, Aug 3, 2020 at 1:20 PM Subject: Urgent To: <@umbc.edu>
I have a task I need you to get done for me Asap, I want to send out a couple gifts cards to some selected staffs, even though we all put in all our best to move this organization forward, some individuals really stand out and I want to surprise them with a little gifts.this is really urgent and important, Please let me know if you can head out to purchase the gift cards so I can advise certain product and denominations.
Thanks |
The phishing email above not only is impersonating a UMBC staff member, but the email has many grammatical mistakes, and there is a feeling of urgency with the subject line “Urgent” and words like “ASAP” being used. These are just some of the examples of the red flags for identifying this and other phishing email scams.
The main goal of this phishing email scam is to get the users to purchase the gift cards and give the gift codes to the malicious actors. Other scams similar to this one might ask for products like iTunes cards, gift cards, prepaid debit cards, or even bitcoin.
If you do receive this or a similar email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
For more information on a similar scam to the one above:
https://itsecurity.umbc.edu/critical/?id=94550
]]>
Recently DoIT has been notified of a phishing email scam where the malicious actor is impersonating a UMBC staff member. The name has been removed from the From for privacy reasons, but an example...
https://beta.my.umbc.edu/api/v0/pixel/news/94675/guest@my.umbc.edu/d44c17a5fdf99b5cc9b2372eedcd518d/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Wed, 05 Aug 2020 17:59:00 -0400
Account Data Breach: Dave
Data Breach On Digital Banking App
In June 2020, Dave, a digital banking app, suffered a data breach. 7.5 million rows of data were leaked to the public on a hacking forum. The breach exposed individuals’ Personal Identifiable Information (PII) such as names, dates of birth, encrypted social security numbers and passwords.
UMBC’s Division of Information Technology (DoIT) has been notified that over 20 UMBC accounts might have been affected by this breach.
The individuals who have been affected by the data breach were notified via their UMBC email and/or their alternate emails. If you do not have an alternate email listed on your UMBC account, we suggest that you create one, preferably different from your UMBC email account.
To link an alternate email account to your UMBC account follow the instructions below:
Login to your myUMBC account: http://my.umbc.edu/account
Go to https://webadmin.umbc.edu/admin//Security/Setup/View
Click Account security setup
At the top of the page, enter your alternate email address
Scroll down to the bottom of the page and click Update my security settings
If you have a Dave account we suggest that you contact them to see if your information has been leaked.
The data about Dave was provided to the breach notification service Have I Been Pwned (HIBP) by dehashed.com.
For more information on Dave data breach visit:
https://www.zdnet.com/article/tech-unicorn-dave-admits-to-security-breach-impacting-7-5-million-users/
https://www.tomsguide.com/news/dave-data-breach
If you have any questions or concerns email us: security@umbc.edu
_________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
]]>
In June 2020, Dave, a digital banking app, suffered a data breach. 7.5 million rows of data were leaked to the public on a hacking forum. The breach exposed individuals’ Personal Identifiable...
https://beta.my.umbc.edu/api/v0/pixel/news/94634/guest@my.umbc.edu/09cd9a32f896cbc2706abcd515234137/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Tue, 04 Aug 2020 10:34:58 -0400
Phishing Emails from SurveyMonkey
The Survey Site Is Legitimate. The Survey Is Not.
According to an article at https://www.infosecurity-magazine.com, Abnormal Security recently discovered a new phishing campaign using malicious emails from a legitimate SurveyMonkey domain. A malicious actor is using this legitimate domain because it allows them to bypass most security filters.
Even though these emails are sent from the actual SurveyMonkey domain, the reply-to address is in a different domain. Within the email there is a hidden URL that appears as the text ‘Navigate to access statement’ with a message ‘Please do not forward this email as its survey link is unique to you.’”
Clicking on the link will redirect the user to a form asking for their Office 365 credentials such as email address and password. If the user’s information is entered into this malicious site, then the user’s account will be compromised.
The article states that the reason this attack is so effective is due to the use of a legitimate email sender, as well as concealing the malicious site URL and the description of the email being “unique” to every user.
If you do receive any email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu and delete the message.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
For more information, please check out:
https://www.infosecurity-magazine.com/news/surveymonkey-phishers-office-365/
https://abnormalsecurity.com/blog/abnormal-attack-stories-phishing-through-surveymonkey/
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
]]>
According to an article at https://www.infosecurity-magazine.com, Abnormal Security recently discovered a new phishing campaign using malicious emails from a legitimate SurveyMonkey domain. A...
https://beta.my.umbc.edu/api/v0/pixel/news/94553/guest@my.umbc.edu/5750a760c5ff3d4c9e9d994a31d49ee0/api/pixel
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Thu, 30 Jul 2020 16:37:43 -0400
Recent Spear-phishing Emails
Faked Email Messages Looking For Your Phone Number
A new wave of Spear-phishing emails hit roughly 300 UMBC inboxes this weekend. An example is shown below, with the From field altered and the To field removed for privacy. There is no body in this particular email.
From: Forged Name <name@gmail.com>
Date: Sat, Jul 25, 2020 at 9:26 AM
Subject: Send me your available text number?
To:
This malicious email uses the name of a UMBC staffer in an attempt to appear credible. However, the Gmail address, unnatural-sounding subject line, and lack of body content are all clear red flags. More generally, be wary of emails from unverified sources with any urgent but unexplained request. Similar emails that were reported previously were precursors to gift card scams.
The best way to avoid these scams is to simply not respond. Instead, report suspicious emails by forwarding them to security@umbc.edu. Include the full email headers by following the instructions athttps://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
For more information on scams and phishing, please visit https://wiki.umbc.edu/pages/viewpage.action?pageId=36766495.
To read more articles published by DOIT visit: https://itsecurity.umbc.edu/critical/?tag=notice.
]]>
A new wave of Spear-phishing emails hit roughly 300 UMBC inboxes this weekend. An example is shown below, with the From field altered and the To field removed for privacy. There is no body in this...
https://beta.my.umbc.edu/api/v0/pixel/news/94550/guest@my.umbc.edu/cdf202fee9c64f4fbff01ee671da24d1/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Thu, 30 Jul 2020 15:42:43 -0400
Fake Job Offers from Corestaff
UMBC Community Gets More Fake Job Offers
Jobs phishing Alert: Corestaff
During the past week, DOIT has received several notifications of phishing emails impersonating Corestaff. Below is a sample message that was sent to many UMBC students. The To field was removed for privacy purposes.
From: Corestaff Services <corestaffserviceshr@gmail.com>
Date: Wed, Jul 22, 2020 at 7:42 PM
Subject: JOB DESCRIPTION
Dear applicant,
Thanks for getting back to us with your interest in the job position, CORESTAFF SERVICES Inc® is a privately held company within Allegis Group, the largest private talent management firm in the world. Our long-standing history and industry-leading position speak to our success in providing the IT staffing solutions, IT services, and talent management insight required for our clients to actualize ROI and sustain a truly competitive advantage in a fast-changing market. We have established successful relationships with thousands of companies, government agencies, and small entrepreneurial firms across all industries.
COMMITMENT: Our commitment to meeting our customers’ and consultants’ expectations is the foundation for building trust in our business relationships. Simply put, we foster an environment that demands integrity and accountability for results. To ensure our clients and consultants know exactly what they can expect from us, we make it our mission to hire smart, honest, and hardworking individuals who possess a great deal of pride in setting the bar high and keeping their word.
JOB DESCRIPTION: CORESTAFF SERVICES Inc® is seeking a production support analyst to support our client's production environment. This person will be responsible for analyzing, reporting, and ordering production supplies. This is a remote part-time job that does not deter you from doing any other. You just need a few hours of your time to do this weekly and you can have your own part of the work completed in t your leisure time in school or at home.
SALARY/WAGES: $300 Weekly.
The successful candidate will need to be able to:
- Provide Quality communication etiquette skills and good organizational skills.
- Perform duties with accuracy, quality, and integrity.
We will always email you guidelines and instructions to follow in getting your job done perfectly as soon as you start working. if you care to proceed with the job offer, get back to us with the information listed below so we can process your information as to consider it valid to commence working with us.
NAME:
PHYSICAL CONTACT ADDRESS (PREFERRED MAILING ADDR)
CITY:
STATE:
ZIPCODE:
D.O.B:
GENDER:
MOBILE (Must be able to receive text):
PERSONAL EMAIL:
CURRENT JOB:
We shall be contacting you as soon as we receive and validate this information.
Kind Regards,
Jasmine Orozco
HR Recruiting Dept.
Corestaff Services Inc®
From addresses of Corestaff impersonator emails that we have received are listed below
If you have received any message similar to the one listed above, DO NOT RESPOND. Please forward the message to security@umbc.edu. Please attach the email headers, information on how to find the email headers can be found here: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
We have also received notification that students who have responded to this email have received checks. DO NOT DEPOSIT THE CHECKS, they are fake.
Students have also been asked for their Cash App, and other card information. DON’T SEND YOUR FINANCIAL INFORMATION. Listed below is a sample message from the impersonator asking for your financial information. For privacy purposes, the To field, and victim’s name have been removed.
From: CORESTAFF SERVICES Inc® <corestaff@consultant.com>
Date: Mon, Jul 27, 2020 at 11:54 AM
Subject: Further Information Required
Hello <VICTIM NAME> ,
I hope you are having a good day?
Our external financial institution is in the process of adding your information to the payroll system where they will be sending funds for you to complete your weekly tasks/orders and your ($300) weekly earnings via Cash-app simply because it is fast (lets you get paid early), safe and reliable and it can be used anywhere Visa is accepted, both online and in stores.
So, do you have Cash-app? Has it been verified? Do you have a cash-card too?
If yes, kindly send in the details below to make us proceed.
Account #
Routine #
If you don't have Cash-app, kindly set it up, verify it, and order a cash-card as soon as you can today. It's free/
I await your prompt response.
Devon Baynard
Sr. Recruiting & Account Manager
Corestaff Services Inc®
If you have received any message similar to the one listed above, DO NOT RESPOND. Please forward the message to security@umbc.edu. Please attach the email headers, information on how to find the email headers can be found here: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
By refusing to provide your financial information or depositing the checks, you might receive threats similar to the one listed below.
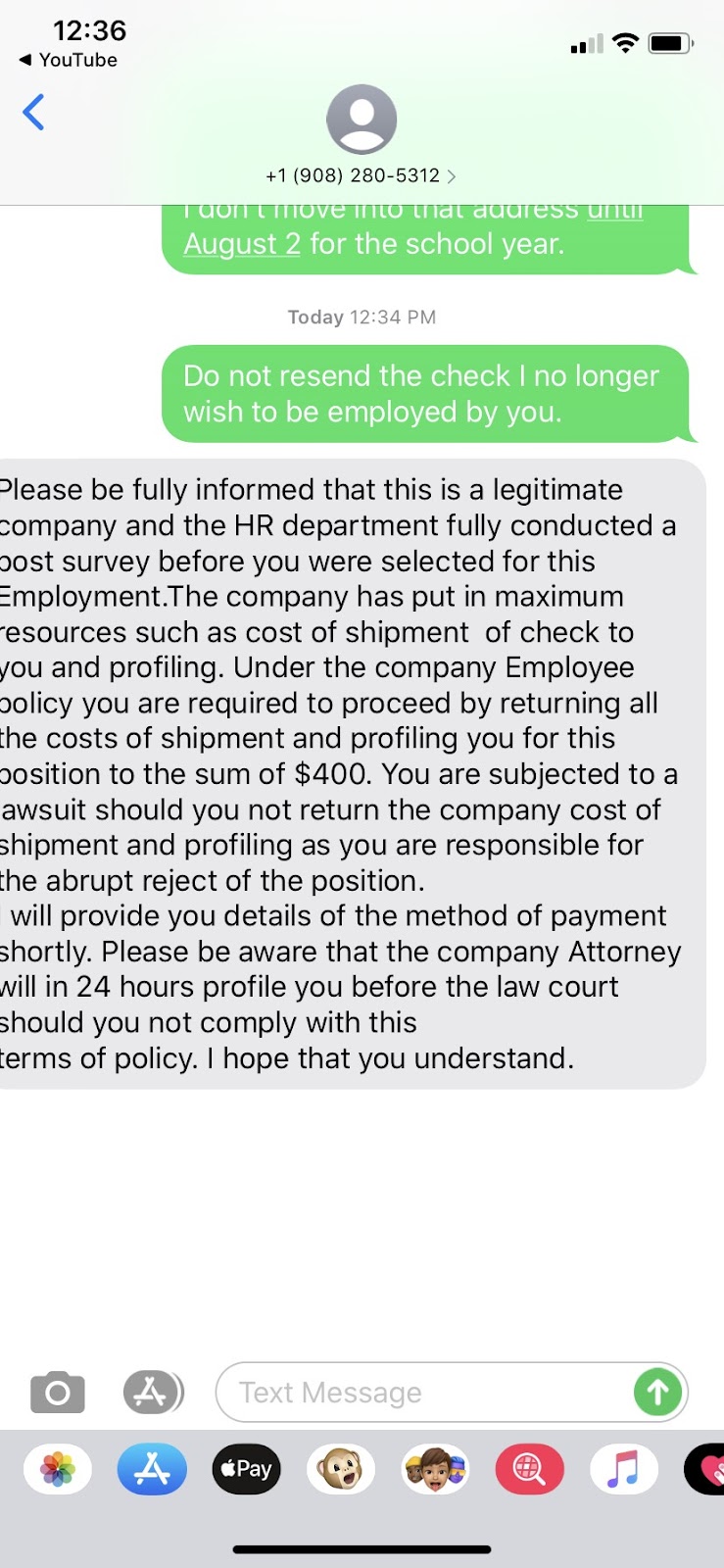
This threatening tone is often used by Scammers to strike fear into individuals which will often cause them to fall victim to scams. If you have received any threats, please send the screenshot to security@umbc.edu.
More information on other job scams can be found here: https://itsecurity.umbc.edu/critical/?tag=notice
For more information on scams and phishing handling, please visit
https://wiki.umbc.edu/pages/viewpage.action?pageId=36766495
For more information on how to spot a Scam, please visit
https://itsecurity.umbc.edu/critical/?id=94345
https://itsecurity.umbc.edu/critical/?id=93891
]]>
Jobs phishing Alert: Corestaff During the past week, DOIT has received several notifications of phishing emails impersonating Corestaff. Below is a sample message that was sent to many UMBC...
https://beta.my.umbc.edu/api/v0/pixel/news/94549/guest@my.umbc.edu/db9ff1c2ef4e4f1424ced27f53d5342b/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Thu, 30 Jul 2020 15:40:31 -0400
WORK-FROM-HOME Phishing Email Scam
Job Scams, Checks, and Threats
UMBC continues to receive phishing email campaigns from a malicious actor pretending to be from either Cisco or Corestaff. This phishing email has the goal of not only getting users personal information but also to try and get them to cash a fraudulent check. An example of the email can be seen below:
From: willliams rolase <rolasewillliams08@gmail.com> Date: Thu, Jul 9, 2020 at 2:22 AM Subject: WORK FROM HOME To: < @umbc.edu>
Dear Student,
We got your contact through your school database and I'm happy to inform you that our reputable company Cisco Systems Inc® is currently running a student empowerment program. This program is to help devoted and hardworking students secure a part time job which does not deter them from doing any other, you just need a few hours to do this weekly and with an attractive weekly wages.
KINDLY EMAIL BACK WITH YOUR PERSONAL EMAIL ADDRESS IF INTERESTED IN THIS JOB POSITION.
Best Regards,
willliams rolase HR Manager/Consultant Cisco Systems Inc® |
If the user responds to the initial message the malicious actor will then respond asking the user for more personal information like name, address, city, state, Zip code, date of birth, gender, phone number, personal email and current job. Which can be seen in the below:
Dear Applicant,
Thanks for getting back to us with your interest about the job position.
ABOUT US: Cisco systems® is a privately held company within Allegis Group, the largest private talent management firm in the world. Our long-standing history and industry-leading position speak to our success in providing the IT staffing solutions, IT services and talent management insight required for our clients to actualize ROI and sustain a truly competitive advantage in a fast-changing market. We have established successful relationships with thousands of companies, government agencies and small entrepreneurial firms across all industries.
COMMITMENT: Our commitment to meeting our customers’ and consultants’ expectations is the foundation for building trust in our business relationships. Simply put, we foster an environment that demands integrity and accountability for results. To ensure our clients and consultants know exactly what they can expect from us, we make it our mission to hire smart, honest and hardworking individuals who possess a great deal of pride in setting the bar high and keeping their word.
JOB DESCRIPTION: Cisco systems® is seeking a production assistance to provide analysis and support for our clients production environment. This person will act as an intermediary between our suppliers and our agents in order to reduce their workload. As an intermediary/liaison, you'll be ordering production supplies, analyzing and making reports. This is a part time job that does not deter you from doing any other. You just need a few hours of your time to do this weekly and you can have your own part of the work completed at your leisure time in school or at home.
HOURS OF WORK: The specific hours of work will vary each week but you will NOT be scheduled more than 6-8 hours per week.
SALARY/WAGE: $400 Weekly.
The successful candidate will need to be able to: -Provide Quality communication etiquette skills and good organizational skills. -Perform duties with accuracy, quality, and integrity. -Strong attention to detail, while under pressure with frequent interruptions. -Demonstrated ability to effectively coordinate multiple tasks and able to react to spontaneous changes in priorities.
We will always email/text you guidelines and instructions to follow in getting your job done perfectly as soon as you start working. if you care to proceed with the job offer, kindly get back to us with the information listed below so we can process your information as to consider it valid to commence working with us.
FULL NAME: PHYSICAL CONTACT ADDRESS (NOT PO BOX): CITY: STATE: ZIP CODE: D.O.B: GENDER: MOBILE (Must be able to receive text) : PERSONAL EMAIL: CURRENT JOB:
We shall be contacting you as soon as we receive and validate this information.
Regards,
willliams rolase, HR Manager/Consultant Cisco Systems Inc®. |
If the user responds with their personal information the scammer will then inform the user that they have been accepted to the job, but due to Covid-19 they cannot do a one-on-one interview. They inform that a check will arrive with enough to cover your wage and your first task.
If you do receive this or a similar scam, please DO NOT respond any further. If you have provided any banking or financial information, please notify your bank or financial institution immediately. If you have been sent a check, you should not attempt to cash or deposit it. If you have deposited a check already, please contact your bank and tell them that it may be part of a scam.
Once you stop cooperating with the scam, you may receive a text message from the scammers. It may look something like:
Please be fully informed that this is a legitimate company and the HR department fully conducted a post survey before you were selected for this Employment.The company has put in maximum resources such as cost of shipment of check to you and profiling. Under the company Employee policy you are required to proceed by returning all the costs of shipment and profiling you for this position to the sum of $400. You are subjected to a lawsuit should you not return the company cost of shipment and profiling as you are responsible for the abrupt reject of this position. We will provide you details of the method of payment shortly. Please be aware that the company Attorney will in 24 hours profile you before the law court should you not comply with this terms of policy. I hope that you understand. |
This is part of the scam and seems to be intended to scare you. The real Cisco Systems doesn’t threaten legal action through text messaging and can afford to employ people who write grammatical sentences.
If you did receive this or any other email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Whether or not you responded to the scam, please forward the message (with the email headers) to security@umbc.edu. We will also keep track of any other information you submit about the scammers, such as phone numbers if you get a text message.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
To read more tips on how to spot and avoid phishing scams:
https://itsecurity.umbc.edu/critical/?id=93891
https://itsecurity.umbc.edu/critical/?id=93743
To read more articles published by DOIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
UMBC continues to receive phishing email campaigns from a malicious actor pretending to be from either Cisco or Corestaff. This phishing email has the goal of not only getting users personal...
https://beta.my.umbc.edu/api/v0/pixel/news/94548/guest@my.umbc.edu/249ba3bd1da978d3349ea0127be7fce8/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets1-beta.my.umbc.edu/images/avatars/group/7/original.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/large.png?1777289325
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777289325
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777289325
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777289325
IT Security - DoIT
0
0
true
Thu, 30 Jul 2020 15:36:36 -0400