Seventeen tips to secure your phone
Advice From Smartphone Insight
Smartphone Insight has published a handy guide with step-by-step instructions to protect your IoS or Android phone data. With these 17 tips, your device will continuously be up to date. In addition, you will see the cool tricks and tips available on your phone to help encrypt your phone data, best practices to use while in public, and how to secure your data and phone while browsing the internet.
To read the guide visit: https://smartphoneinsight.com/how-to-keep-your-phone-secure/
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Smartphone Insight has published a handy guide with step-by-step instructions to protect your IoS or Android phone data. With these 17 tips, your device will continuously be up to date. In...
https://beta.my.umbc.edu/api/v0/pixel/news/112659/guest@my.umbc.edu/a034862b4e4287514f38cda29f7d5f22/api/pixel
learn
noltice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Sun, 26 Sep 2021 21:15:37 -0400
Mon, 01 Nov 2021 16:42:37 -0400
Account data breach: Epik
Epik Accounts Posted Online
On September 13, 2021, the domain registrar and web hosting company, Epik, suffered a data breach. This breach contained data for approximately 15 million Epik and non-Epik customers. Allegedly, this was done in retaliation for hosting alt-right websites. The information included email addresses, names, phone numbers, geographical addresses, purchases, and WHOIS records.
The compromised accounts were subsequently made public. Fifty-three UMBC accounts were victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have an Epik account, please contact them to see if you have been affected by this breach.
To see if you were involved in any other breach, visit: https://haveibeenpwned.com/.
More about Epik data breach:
https://amp.cnn.com/cnn/2021/09/21/politics/anonymous-epik-hack/index.html
If you have any questions or concerns, email us at: security@umbc.edu.
Information about this breach was provided to us by Have I Been Pwned(HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
On September 13, 2021, the domain registrar and web hosting company, Epik, suffered a data breach. This breach contained data for approximately 15 million Epik and non-Epik customers. Allegedly,...
https://beta.my.umbc.edu/api/v0/pixel/news/112658/guest@my.umbc.edu/763b3c489c221ab0f1bc2d79eb004aa2/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Sun, 26 Sep 2021 21:13:40 -0400
A Phishing Scam With A Malicious Attachment
A Well-Designed Attempt to Gather Your Account and Password
DoIT received a report of a phishing scam that depends on the download and execution of an attachment. The message, as seen below, appears to come from Joel Avila, the CEO of Edwards Label in Ventura, California. Mr. Avila exists and really is CEO of that company, but he has nothing to do with this message.
from: Joel Avila <renqingiot@163.com> to: removed for privacy date: Aug 10, 2021, 12:08:50 PM subject: PO1088EDW88
Hi,
I need your company to confirm if you can supply the attached PO. Remember that we have encrypted your removed for privacy@umbc.edu product
Download PO1088_EDW88 and get back to us with your best price asap
Thanks,
Joel Avila CEO/CFO Edwards Label 2277 West Knoll Drive Ventura, CA 93003 P (805) 658-2444 Ext.116 F (805) 658-0233 |
Email scams generally try to create a sense of urgency, often around money. They either threaten the recipient with imminent financial loss or offer the promise of immediate financial gain as long as the recipient acts quickly. This scam takes a more subtle approach by suggesting that the recipient has been confused with some company that can supply a product that Mr. Avila is looking for. A supposed purchase order is attached and the recipient might well consider looking at it for more information.
Once downloaded and clicked, the attachment displays a web page asking for a username and password. Whatever is entered, the user will get a message that the entry is invalid. In the meantime, the entered information will be stored on a remote server (in Nigeria in this particular instance). Eventually, that server will accumulate a list of account/password pairs from people all over the world.
The moral is: If you aren’t sure what’s in it, don’t click it!
For more information about phishing, visit:https://itsecurity.umbc.edu/critical/?id=98136.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit:https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit:https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
DoIT received a report of a phishing scam that depends on the download and execution of an attachment. The message, as seen below, appears to come from Joel Avila, the CEO of Edwards Label in...
https://beta.my.umbc.edu/api/v0/pixel/news/112400/guest@my.umbc.edu/3eeed98b2ef9b3658526ff16b9f51589/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Thu, 16 Sep 2021 20:34:47 -0400
False Payment Scams
A Promise To Return A Payment You Never Made
Recently, DOIT received reports of email messages containing variations on the same financial scam. Examples are included below. Both the From and the To addresses are fake. The recipient is informed of a payment made or owed to some known vendor and is provided with a phone number to be used to dispute that payment. The goal is to get the recipient to call the number and provide credit card, PayPal, or banking information under the guise of ‘fixing’ the fake order.
Example 1
From: rani sob <rani7654rob@gmail.com> Date: Thu, Sep 16, 2021 at 9:26 AM Subject: MacBook Pro Bill receipt To: <koi7654ran@gmail.com>
PayPal User, This email confirms that you made a payment . You sent a payment of $701 to Flipkart LTD. This charge will appear on your credit card statement as payment to PayPal. It may take a few moments to appear this transaction in your PayPal account. PAYMENT DETAILS: Transaction Id: 875DDER4Q Product Name: MacBook Pro Quantity: 1 Total Price: $729 Thank you for using PayPal as your method of payment. If you haven’t authorized this charge ,call us to dispute the transaction and get a full refund. Contact us at: + 1(800) - (201) - (9132) Good day to You PayPal.
|
Example 2
From: julitte bik <julitte5333bik@gmail.com> Date: Thu, Sep 16, 2021 at 12:37 PM Subject: thanks of paying for the subscription ..# ie 406 bk To: <consumer949@gmail.com>
prime subscriber of Norton . We wish to begin by expressing our profound gratitude for you being the loyal user of Norton life lock 360 security forpc and laptop. Wewish toinform youthat your subscription is renewed as you have selected autopay while initiating the services. Product details are mentioned below:- 1. Invoice id : : - ie 406 bk 2. Renewal date :- 16th sep 2021 3. Debited amount: :- $ 409.01 usd 4. Validityperiod: :- ( twelve ) month’s if u wish to upgrade theplan or cancel the subscription OR the subscription was not been activated by you,then kindly contact to the number given below….. For queries and complain please call =……………………… + (1) - ( 877 - 328 - 6947 ).
|
Example 3
From: elizabeth tho <elizabeth1997tho@gmail.com> To: consumer992 <consumer992@gmail.com> Date: Sep 13, 2021, 1:50:16 PM Subject: @ - ALL right reserved customer #EWQ321QW
dear……PAYER your purchase play for norton security HAS successfully renewed and update been the charged sum WILL be reflected inside next to 48 hrs in your account statement FOR your order norton security just acts like a vaccine for your system preventing THE system against all the suspicious threats.. we wish to inform you the details for your order as we BELIVE IN transparency invoice ID | EWQ321QW | expair DATE | 13/09/2021 | price | 349.61 USD | PAYMENT method | auto - debited |
please feel free to STOP by on within next 60 days . to learn more about our product and meet our team . give USA call or email us TO learn more about OUR product and services. Costumer CARE no :- ---- (877) - 328- (6947) THANKS @ - ALL right reserved customer
|
Whenever you receive such emails, always try and verify with the senders on an entirely different email if you know them. Feel free to always send the message to us to validate the email.
For more information about phishing, visit:https://itsecurity.umbc.edu/critical/?id=98136.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit:https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
_________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit:https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Recently, DOIT received reports of email messages containing variations on the same financial scam. Examples are included below. Both the From and the To addresses are fake. The recipient is...
https://beta.my.umbc.edu/api/v0/pixel/news/112393/guest@my.umbc.edu/48e384fc70b4c6a4c301626b38c9b30a/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Thu, 16 Sep 2021 15:19:08 -0400
Summary of Phishing Techniques and Defenses
A Recent Report On Phishing Attacks (And How To Avoid Them)
However you get your news, by now you have seen the term 'phishing' used to describe ways to exploit people on the Internet. You or someone you know may have been the target of a phishing attack. At UMBC, the Division of Information Technology (DoIT) saw a surge in various types of phishing attacks since the start of the lockdown in the sprint of 2020.
The term 'phishing' refers to attempts to gather personal or otherwise sensitive information from a victim. The information is usually specific and, if possible, unique enough to serve as identification for the victim. This includes obvious things like social security numbers, phone numbers, and online account passwords. It may also include less obvious information, such as birthdays, the names of family members, or even the name of the victim's old high school.
Area 1 Security has published a report based on "over 31 million threats discovered from May 1, 2020 to April 30, 2021" that describes the different types of phishing and provides some guidance in guarding against them.
The report is not long. We strongly encourage you to look at pp. 17-18, the report's Recommendation section. While it is addressing IT support groups, most of the advice can be useful to individuals as well.
]]>
However you get your news, by now you have seen the term 'phishing' used to describe ways to exploit people on the Internet. You or someone you know may have been the target of a phishing...
https://beta.my.umbc.edu/api/v0/pixel/news/112386/guest@my.umbc.edu/656ddc80653e366f3f3e13307978e7ad/api/pixel
learn
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Thu, 16 Sep 2021 15:15:12 -0400
Mon, 01 Nov 2021 16:43:10 -0400
Account data breach: Nitro
Digital Document Service Breached
In September 2020, a Portable Document Format(PDF) file and digital document service, Nitro, suffered a data breach. This breach contained data for approximately 78 million customers and was exposed online. The customer information included names, passwords and the titles of documents. No financial information was leaked.
1,440 UMBC accounts were victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a Nitro account, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach, visit: https://haveibeenpwned.com/.
More about Nitro data breach:
https://infosec.berry.edu/2021/01/19/data-breach-notification-nitro-pdf/#:~:text=In%20September%20of%202020%20there%20was%20a%20breach,or%20vikings.berry.edu%20email%20address%20 included%20in%20the%20 breach.
If you have any questions or concerns, email us at: security@umbc.edu.
Information about this breach was provided to us by Have I Been Pwned(HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
In September 2020, a Portable Document Format(PDF) file and digital document service, Nitro, suffered a data breach. This breach contained data for approximately 78 million customers and was...
https://beta.my.umbc.edu/api/v0/pixel/news/112310/guest@my.umbc.edu/b015eeb17b697f9414e770c24f4ad2a9/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Tue, 14 Sep 2021 16:04:20 -0400
Tue, 14 Sep 2021 16:05:04 -0400
Account data breach: Romwe
Online Fashion Site Breached
In June 2018, an online fashion website, Romwe, suffered a data breach. This breach has data for approximately 20 million customers. The data was sold online. The customer information includes names, email addresses, IP addresses, physical addresses, phone numbers, and passwords. No financial information was leaked.
229 UMBC accounts were potential victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a Romwe account, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach visit:https://haveibeenpwned.com/.
More about Romwe data breach:
https://us.romwe.com/datasecurityFAQs-a-1039.html?SASSource=cjunction&affiliateID=100357191_5250933&url_from=cj.com&cjevent=dd0a33c1077f11ec804300290a82b82d
If you have any questions or concerns, email us at:security@umbc.edu.
Information about this breach was provided to us by Have I Been Pwned(HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
In June 2018, an online fashion website, Romwe, suffered a data breach. This breach has data for approximately 20 million customers. The data was sold online. The customer information includes...
https://beta.my.umbc.edu/api/v0/pixel/news/112308/guest@my.umbc.edu/685d281e225088a2a9a529d5cdcfb79b/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Tue, 14 Sep 2021 16:00:50 -0400
Vendor Breaches and Account Compromises
Password Stopped Working? This Might Be Why.
Vendor Breaches and Account Compromises
Internet vendors will, at times, suffer data breaches. Sometimes the service will attempt to contact it’s account holders and other times it won’t. Often, after some time has passed, the malicious actors who stole the original data or others who have acquired it in the meantime will release it publicly. UMBC’s Division of Information Technology (DoIT) subscribes to a service called HaveIBeenPwned which looks for such public releases and searches them for email addresses ending in @umbc.edu.
For example, if you registered for a member’s discount card with Giant Food or signed-up for online banking and entered your email address as myname@umbc.edu, DoIT may receive notification if a publicly released breach included that email address. This does NOT automatically mean that your UMBC account was compromised. If you use a different password on your Giant account than you use on your UMBC account, then your UMBC account is still secure.
If DoIT determines that your UMBC account has been compromised (or if we are unable to determine that it hasn’t), your password will be replaced with a random string of text. You will also receive email in your Password Reset Email account (not your primary UMBC account) notifying you of the password change.
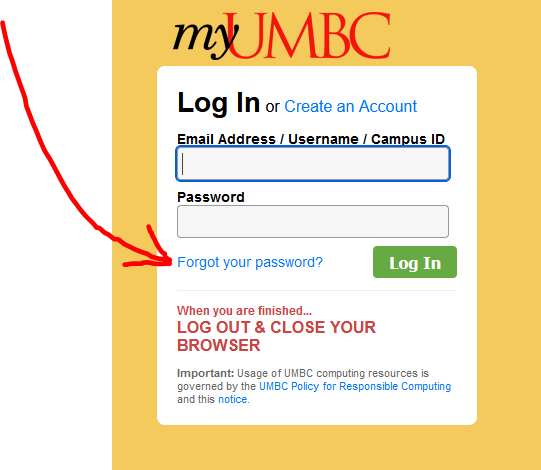
DoIT has no way of knowing what the new randomized password is, but you can recover access to your account by going to the MyUMBC login page and selecting “Forgot your password?” (see image below). You will then need to answer the security questions you set up for your account. After answering correctly, a link will be sent to your designated Password Reset Email account. If you have trouble with this, the Technology Support Center (https://doit.umbc.edu/tsc/, 410-455-3838) can assist you.
]]>
Vendor Breaches and Account Compromises Internet vendors will, at times, suffer data breaches. Sometimes the service will attempt to contact it’s account holders and other times it won’t. ...
https://beta.my.umbc.edu/api/v0/pixel/news/112307/guest@my.umbc.edu/40987f9cf2e4f4b975569be2b32010ef/api/pixel
learn
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Tue, 14 Sep 2021 15:54:43 -0400
Mon, 01 Nov 2021 16:44:36 -0400
Phishing Alert: President Freeman A. Hrabowski impersonator
This Is Not Dr. Hrabowski!
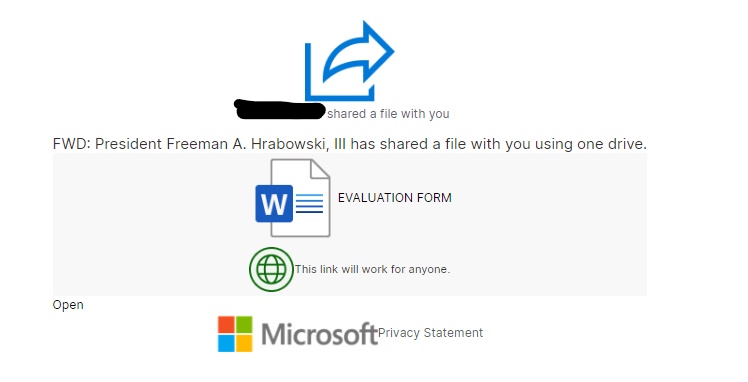
Recently, DOIT received an email from a compromised account at North Central Kansas Technical College(NCKTC) impersonating Dr Hrabowski. The email consisted of a Microsoft word document titled “EVALUATION FORM.” Below is a copy of the email. We removed the name of the NCKTC user and the To field for privacy reasons.
From: NCKTC member’s name <userID@ncktc.edu> Date: Wed, Aug 25, 2021 at 12:00 PM Subject: NCKTC member name shared "EVALUATION FORM" with you. To:
|
The link for the email will take you to the EVALUATION FORM document. See below to look inside the Word docs.
This link will ask you to sign in to your Microsoft account to view a file/form that the compromised account shared on One Drive. DO NOT CLICK ON ANY OF THE LINKS IN THE EMAIL OR THE DOCS. However, if you have done so already, please contact us immediately atsecurity@umbc.edu.
A lot of phishing emails contain a link that asks the recipients to sign into their accounts. Whenever you receive such emails, always try and verify with the senders on an entirely different email if you know them. Feel free to always send the message to us to validate the email.
For more information about phishing, visit:https://itsecurity.umbc.edu/critical/?id=98136.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Recently, DOIT received an email from a compromised account at North Central Kansas Technical College(NCKTC) impersonating Dr Hrabowski. The email consisted of a Microsoft word document titled...
https://beta.my.umbc.edu/api/v0/pixel/news/112267/guest@my.umbc.edu/5d2ed9704c24bfcbe9a7381192490342/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Mon, 13 Sep 2021 18:28:49 -0400
Email marketing and the User-Agent-String
When What Looks Like Phishing Is Just Spam
Recently, DOIT received multiple reports of suspicious messages about student loans from email addresses with the format <emails@alert###.info>. The recipients of these messages marked them as phishing, but on careful investigation, we realised that these were legitimate. We therefore classified these messages as spam instead of phishing.
According to Phishing.org, “[p]hishing is a cybercrime in which a target or targets are contacted by email, telephone or text message by someone posing as a legitimate institution to lure individuals into providing sensitive data such as personally identifiable information, banking and credit card details, and passwords.” A third party company, CollegeLoans, sent these messages on behalf of these loan companies. Therefore, they are not malicious or criminal; instead, they are commercial.
Nonetheless, you might not have subscribed to receive these messages; hence they are spam. According to Cisco.com, “[s]pam is unsolicited and unwanted junk email sent out in bulk to an indiscriminate recipient list. Typically, ...sent for commercial purposes.” These emails are advertisements. They target university students since people in this demographic may need help covering tuition costs.
As mentioned earlier, these loan messages or advertisements originated from the third party company, CollegeLoan. This company is located in Puerto Rico. When you click on the link in the email, they will earn a commission whether or not you apply for the loans. It is business. It’s email marketing.
CollegeLoans sends out links on behalf of the following companies:
We were also suspicious because clicking the link might take the reader to Amazon.com rather than the advertised site. Among the information webservers can collect when you click is something called a User-Agent-String. This string helps the website determine the version of the browser you are using in order to avoid trying to perform advanced functions on old browsers. Bad actors may use this feature to hide from browsers commonly used to analyze malicious sites. However, we determined that the link is not malicious.
We are not sure of the reason that CollegeLoans chose to use browser detection. However, it is not uncommon for developers/companies to add this feature to their code/applications. According to MDN web Docs, using a browser detection would depend on one of the following:
If you are trying to work around a specific bug in some version of a browser.
If you are trying to check for the existence of a particular feature.
If you want to provide different HTML depending on which browser.
When you receive messages like this
, plese mark them as spam or phishing and continue to report them to us at: security@umbc.edu.
Source:
https://www.phishing.org/what-is-phishing
https://www.cisco.com/c/en/us/products/security/email-security/what-is-spam.html#:~:text=Spam%20email%20is%20unsolicited%20and,botnets%2C%20networks%20of%20infected%20computers.
To read more about user agents, visit https://towardsdatascience.com/the-user-agent-that-crazy-string-underpinning-a-bunch-of-analytics-86507ef632f0.
https://developer.mozilla.org/en-US/docs/Web/HTTP/Browser_detection_using_the_user_agent
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Recently, DOIT received multiple reports of suspicious messages about student loans from email addresses with the format <emails@alert###.info>. The recipients of these messages marked them...
https://beta.my.umbc.edu/api/v0/pixel/news/112255/guest@my.umbc.edu/96ad3039ef3fff9a72053358bbb5565d/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Mon, 13 Sep 2021 14:45:05 -0400