Account Data Breach: START
Russian streaming service impacts over 7 million accounts
In August 2022, news broke of an attack against the Russian streaming service "START". The incident led to the exposure of 44 million records containing 7.4 million unique email addresses. The impacted data also included the subscriber's country and password hash. START subsequently acknowledged the incident in a Telegram post and stated that the data dated back to 2021.
One UMBC account was a victim of this breach. The victim is being notified via their UMBC email and/or their alternate email. If you have an account with START, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach visit:
https://haveibeenpwned.com/.
More about the START data breach:
Information about this breach was provided to us by Have I Been Pwned (HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
]]>
In August 2022, news broke of an attack against the Russian streaming service "START". The incident led to the exposure of 44 million records containing 7.4 million unique email addresses. The...
https://beta.my.umbc.edu/api/v0/pixel/news/128974/guest@my.umbc.edu/967983b89900a274c9e058a36c6afce8/api/pixel
edb
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/974/45ca75a5b04745b3f08b746b39c5afa3/xxlarge.jpg?1667588368
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/974/45ca75a5b04745b3f08b746b39c5afa3/xlarge.jpg?1667588368
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/974/45ca75a5b04745b3f08b746b39c5afa3/large.jpg?1667588368
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/974/45ca75a5b04745b3f08b746b39c5afa3/medium.jpg?1667588368
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/974/45ca75a5b04745b3f08b746b39c5afa3/small.jpg?1667588368
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/974/45ca75a5b04745b3f08b746b39c5afa3/xsmall.jpg?1667588368
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/974/45ca75a5b04745b3f08b746b39c5afa3/xxsmall.jpg?1667588368
1
0
false
Fri, 04 Nov 2022 15:08:12 -0400
Account Data Breach: TAP Air Portugal
Portugal's national airline victim of ransomware attack
In August 2022, the Portuguese airline TAP Air Portugal was the target of a ransomware attack perpetrated by the Ragnar Locker gang who later leaked the compromised data via a public dark web site. Over five million unique email addresses were exposed alongside other personal data including names, genders, dates of birth, phone numbers, and physical addresses.
Fifteen UMBC accounts were potential victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have an account with TAP Air Portugal, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach visit
https://haveibeenpwned.com/.
More about the TAP Air Portugal data breach:
Information about this breach was provided to us by Have I Been Pwned (HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
]]>
In August 2022, the Portuguese airline TAP Air Portugal was the target of a ransomware attack perpetrated by the Ragnar Locker gang who later leaked the compromised data via a public dark web...
https://beta.my.umbc.edu/api/v0/pixel/news/128816/guest@my.umbc.edu/00d4106f0cec7ba1e21de54bf420b7b3/api/pixel
edb
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/816/f81234f0ac157e55a7e01005e4392a8a/xxlarge.jpg?1666983644
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/816/f81234f0ac157e55a7e01005e4392a8a/xlarge.jpg?1666983644
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/816/f81234f0ac157e55a7e01005e4392a8a/large.jpg?1666983644
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/816/f81234f0ac157e55a7e01005e4392a8a/medium.jpg?1666983644
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/816/f81234f0ac157e55a7e01005e4392a8a/small.jpg?1666983644
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/816/f81234f0ac157e55a7e01005e4392a8a/xsmall.jpg?1666983644
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/816/f81234f0ac157e55a7e01005e4392a8a/xxsmall.jpg?1666983644
0
0
false
Fri, 28 Oct 2022 15:07:34 -0400
Account Data Breach: Twitter
Hackers list database of 5.4 million records for sale
In January 2022, a vulnerability in Twitter's platform allowed an attacker to build a database of email addresses and phone numbers of millions of users of the social platform. In a disclosure notice later shared in August 2022, Twitter advised that the vulnerability was related to a bug introduced in June 2021 and that they are directly notifying impacted customers. The impacted data included either email address or phone number alongside other public information including username, display name, bio, location, and profile photo. The data, which included the information on 5.4 million accounts, was posted for sale with an asking price of more than $30,000.
Of the accounts listed, approximately 56 UMBC accounts were indicated in this potential breach. The victims are being notified via their UMBC emails. If you have an account with Twitter, please contact them to see if you have been affected by this breach.
Receive any suspicious emails?
]]>
In January 2022, a vulnerability in Twitter's platform allowed an attacker to build a database of email addresses and phone numbers of millions of users of the social platform. In a disclosure...
https://beta.my.umbc.edu/api/v0/pixel/news/128602/guest@my.umbc.edu/8677200beb2ca3005a4d2000ae48c886/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/602/1580743208a1d7a22b65875c78ca84ba/xxlarge.jpg?1666206795
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/602/1580743208a1d7a22b65875c78ca84ba/xlarge.jpg?1666206795
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/602/1580743208a1d7a22b65875c78ca84ba/large.jpg?1666206795
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/602/1580743208a1d7a22b65875c78ca84ba/medium.jpg?1666206795
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/602/1580743208a1d7a22b65875c78ca84ba/small.jpg?1666206795
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/602/1580743208a1d7a22b65875c78ca84ba/xsmall.jpg?1666206795
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/602/1580743208a1d7a22b65875c78ca84ba/xxsmall.jpg?1666206795
3
0
false
Wed, 19 Oct 2022 15:23:27 -0400
Account Data Breach: StripChat
Millions of records exposed from an adult cam site
In November 2021, the live sex cams and adult chat website StripChat left several databases exposed and unsecured. In June the following year, over 65 million StripChat records appeared on a popular hacking forum. The exposed data included usernames, email addresses and IP addresses, biographical data, transaction data, and chat messages.
Of the accounts listed, approximately four UMBC accounts were indicated in this potential breach. The victims have been notified via their UMBC email. If you have an account with Stripchat, please contact them to see if you have been affected by this breach.
Receive any suspicious emails?
]]>
In November 2021, the live sex cams and adult chat website StripChat left several databases exposed and unsecured. In June the following year, over 65 million StripChat records appeared on a...
https://beta.my.umbc.edu/api/v0/pixel/news/128572/guest@my.umbc.edu/2c8176cd85861b131b7c89fc52a2808c/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/572/69c8124eec2f7e45217a63461dcbfa5b/xxlarge.jpg?1666205828
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/572/69c8124eec2f7e45217a63461dcbfa5b/xlarge.jpg?1666205828
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/572/69c8124eec2f7e45217a63461dcbfa5b/large.jpg?1666205828
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/572/69c8124eec2f7e45217a63461dcbfa5b/medium.jpg?1666205828
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/572/69c8124eec2f7e45217a63461dcbfa5b/small.jpg?1666205828
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/572/69c8124eec2f7e45217a63461dcbfa5b/xsmall.jpg?1666205828
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/572/69c8124eec2f7e45217a63461dcbfa5b/xxsmall.jpg?1666205828
2
0
false
Wed, 19 Oct 2022 15:03:55 -0400
Account Data Breach: SitePoint
Shared data has already been used in attacks
In June 2020, the web development site SitePoint suffered a data breach that exposed over one million customer records. Impacted data included email and IP addresses, names, usernames, bios and passwords stored as bcrypt hashes.
Of the accounts listed, approximately 17 UMBC accounts were indicated in this potential breach. The victims are being notified via their UMBC emails. If you have an account with SitePoint, please contact them to see if you have been affected by this breach.
Receive any suspicious emails?
]]>
In June 2020, the web development site SitePoint suffered a data breach that exposed over one million customer records. Impacted data included email and IP addresses, names, usernames, bios and...
https://beta.my.umbc.edu/api/v0/pixel/news/128571/guest@my.umbc.edu/795f9cd5dc641de3a61d52cc85b0b462/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/571/a3d41bd8ce327f90ec607b0e48c625c7/xxlarge.jpg?1666123306
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/571/a3d41bd8ce327f90ec607b0e48c625c7/xlarge.jpg?1666123306
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/571/a3d41bd8ce327f90ec607b0e48c625c7/large.jpg?1666123306
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/571/a3d41bd8ce327f90ec607b0e48c625c7/medium.jpg?1666123306
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/571/a3d41bd8ce327f90ec607b0e48c625c7/small.jpg?1666123306
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/571/a3d41bd8ce327f90ec607b0e48c625c7/xsmall.jpg?1666123306
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/571/a3d41bd8ce327f90ec607b0e48c625c7/xxsmall.jpg?1666123306
0
0
false
Tue, 18 Oct 2022 16:05:01 -0400
Tue, 18 Oct 2022 16:06:35 -0400
Account Data Breach: ShitExpress
In August 2022, the online feces delivery service ShitExpress suffered a data breach that exposed 24,000 unique email addresses. The addresses spanned invoices, gift cards, promotions and PayPal records. The breach also exposed the IP and email addresses of senders, physical addresses of recipients and messages accompanying the delivery.
Of the accounts listed, approximately 1 UMBC account was indicated in this potential breach. The victim has been notified via their UMBC email. If you have an account with ShitExpress, please contact them to see if you have been affected by this breach.
Receive any suspicious emails?
]]>
In August 2022, the online feces delivery service ShitExpress suffered a data breach that exposed 24,000 unique email addresses. The addresses spanned invoices, gift cards, promotions and PayPal...
https://beta.my.umbc.edu/api/v0/pixel/news/128570/guest@my.umbc.edu/09c712d944d2120df4286fdcca0cbe26/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/570/819f6c8c98a519c3f3d7377a5bc548d9/xxlarge.jpg?1666122450
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/570/819f6c8c98a519c3f3d7377a5bc548d9/xlarge.jpg?1666122450
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/570/819f6c8c98a519c3f3d7377a5bc548d9/large.jpg?1666122450
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/570/819f6c8c98a519c3f3d7377a5bc548d9/medium.jpg?1666122450
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/570/819f6c8c98a519c3f3d7377a5bc548d9/small.jpg?1666122450
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/570/819f6c8c98a519c3f3d7377a5bc548d9/xsmall.jpg?1666122450
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/128/570/819f6c8c98a519c3f3d7377a5bc548d9/xxsmall.jpg?1666122450
36
0
false
Tue, 18 Oct 2022 15:57:00 -0400
Fraud Alert: "TASK: Thursday, Oct. 13TH"
Fraudster Impersonating UMBC Officials
This morning, the Division of Information Technology(DoIT) received a report of fraudulent emails sent to the University System of Maryland office.. The fraudster is forging the name of UMBC President Sheares Ashby, probably in an attempt to get the recipient to purchase gift cards on the fraudster’s behalf. Below is an example of the email. For privacy, we removed the To field.
From: Valerie Sheares Ashby <executivedir808@gmail.com> Sent: Thursday, October 13, 2022 6:35 AM To: Subject: TASK: Thursday, Oct. 13TH Good Morning, Is your schedule open? I'll need you to run an errand for me. I'm heading into a meeting with limited communication access soon, so just reply to me via email. Sincerely, Valerie Sheares Ashby
|
A slightly different version appeared in some UMBC inboxes, this one pretending to be from Vice Provost and Dean Rutedge.
From: Janet Rutledge <executivedir808@gmail.com> Sent: Thursday, October 13, 2022 6:35 AM To: Subject: TASK: Thursday, Oct. 13TH Good Morning, Is your schedule open? I'll need you to run an errand for me. I'm heading into a meeting with limited communication access soon, so just reply to me via email. Sincerely, Janet Rutledge
|
THIS REQUEST IS NOT REAL!
This is a common scam to get the recipient to purchase gift cards or something else of value that can be sent through email.
Whatever you spend, you will not get back.
If you have responded to the message and performed any errands such as purchasing gift cards, please do not send the codes to executivedir808@gmail.com.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
If you need further assistance, please contact us at security@umbc.edu.
__________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
This morning, the Division of Information Technology(DoIT) received a report of fraudulent emails sent to the University System of Maryland office.. The fraudster is forging the name of UMBC...
https://beta.my.umbc.edu/api/v0/pixel/news/128454/guest@my.umbc.edu/0024f186aafc0459f398cecaaa363518/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Thu, 13 Oct 2022 11:49:42 -0400
Job Scam Posting
Another Scam
On October 4, 2022, a job offer was posted in at least one group on the MyUMBC site. The job offer was supposedly from Prof. Erika Fountain for "Administrative Assistants". This posting was an error and has been taken down. The job does not exist. Prof. Fountain did not post it. In the posting below, note that the phone number is not a UMBC office phone number. The number referenced has a 612 area code (Minneapolis, Minnesota).
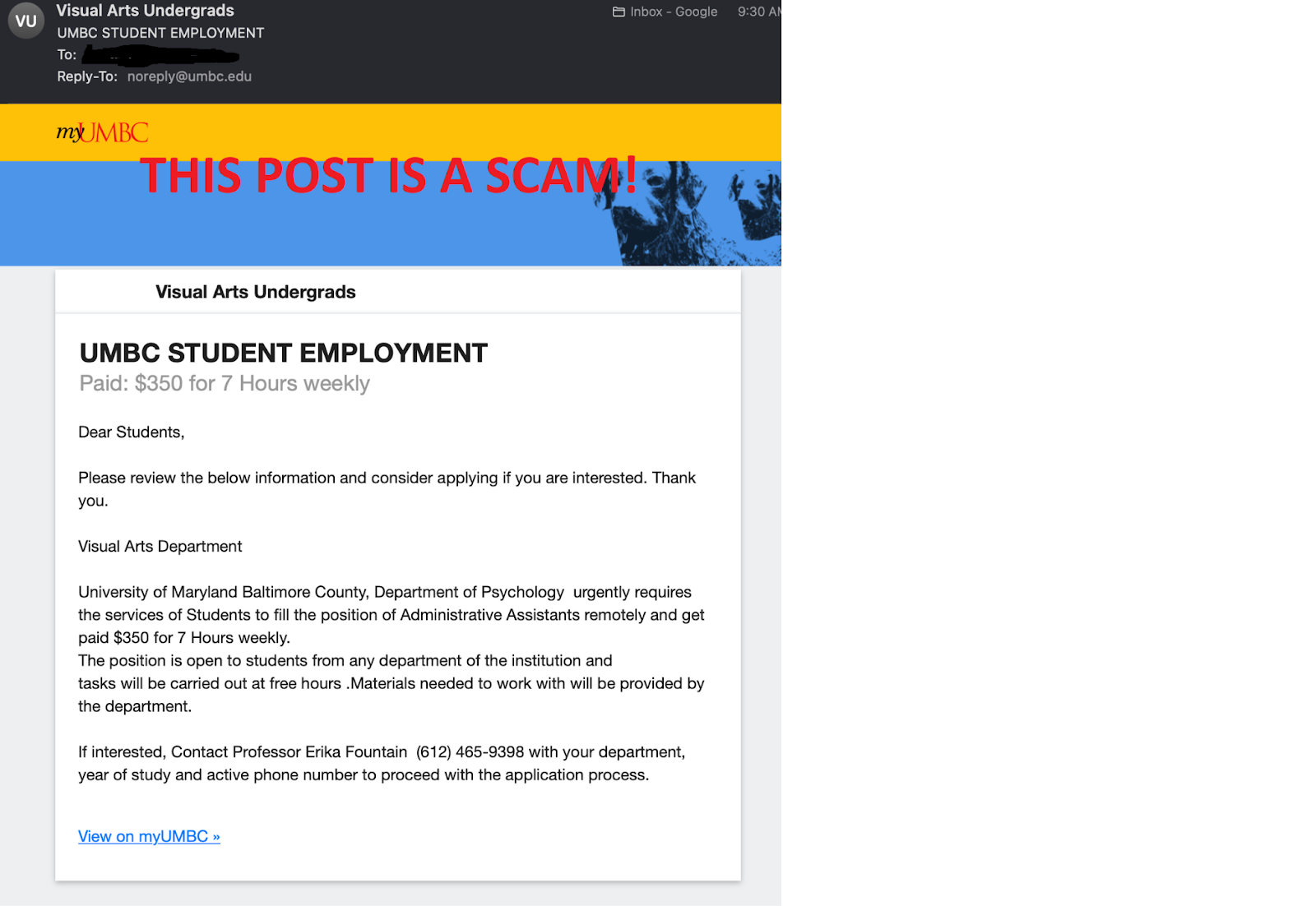
Again, THIS IS A SCAM.
]]>
On October 4, 2022, a job offer was posted in at least one group on the MyUMBC site. The job offer was supposedly from Prof. Erika Fountain for "Administrative Assistants". This posting was an...
https://beta.my.umbc.edu/api/v0/pixel/news/128276/guest@my.umbc.edu/e31193d09d1bbf7085f5f9ba8551a95b/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
1
0
true
Thu, 06 Oct 2022 19:21:26 -0400
Thu, 06 Oct 2022 19:30:59 -0400
Phishing Alert: Final Update Warning!
They Want Your Password
Recently, the Division of Information Technology (DoIT) received a report of a phishing email that appeared to be crafted to attack users in the Computer Science department. The phishers are trying to capture, at least, your UMBC password.. The Below is an example of the email. For privacy purposes, we removed the To field.
THIS WARNING IS NOT REAL!
DoIT will not ask you to “confirm your ownership” of your email account. If we ask you to change your password, we will direct you to my.umbc.edu or to webauth.umbc.edu, not to a non-UMBC site.
Saying that “This message is from a trusted sen der” should make you suspicious from the start. If someone walked up to you in the street and, instead of introducing themselves by name, simply told you that they were trusted, would you be comfortable?
Whoever wrote this seems to think that “sender” is two words.
PLEASE DO NOT CLICK THE LINK!
If you have already clicked the link and entered your password:
If you entered your UMBC password on the form, please change your password immediately.
If you entered your UMBC password and you used that same password for any other account(s) (e.g. Social Media, Online Banking, etc.), change the passwords on the account(s) immediately.
If you entered banking, credit card, or other information, please contact your bank or other financial institution immediately and report what happened.
If you entered personal information such as your address, phone number, etc., monitor your finances and be very careful about responding to suspicious phone calls, mail, text messages, etc.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
If you need further assistance, please contact us at security@umbc.edu.
__________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Recently, the Division of Information Technology (DoIT) received a report of a phishing email that appeared to be crafted to attack users in the Computer Science department. The phishers are...
https://beta.my.umbc.edu/api/v0/pixel/news/128248/guest@my.umbc.edu/9e2c28a610ce68b50692936d454c0c14/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Thu, 06 Oct 2022 12:02:15 -0400
Hurricane-Related Scams
An Advisory From CISA
The Cybersecurity and Infrastructure Security Agency (CISA) has posted a warning about scammers pretending to be charitable agencies either soliciting contributions for hurricane victims or trying to scam the victims directly.
You can find the CISA post at:
It is unfortunately common for unscrupulous actors to take advantage of disasters and emergency conditions in order to prey upon both those who honestly wish to help and those who truly need help. The CISA post includes references to various resources that can help identify and avoid these scams. Some of these resources are useful for detecting scams in general, particularly fake charities. Be mindful when you see unsolicited email, text messages, or phone calls related to hurricane relief. Make sure that your assistance is going where you want it to go.
]]>
The Cybersecurity and Infrastructure Security Agency (CISA) has posted a warning about scammers pretending to be charitable agencies either soliciting contributions for hurricane victims or trying...
https://www.cisa.gov/uscert/ncas/current-activity/2022/09/30/hurricane-related-scams
https://beta.my.umbc.edu/api/v0/pixel/news/128066/guest@my.umbc.edu/63065da20db05e1beb905dd31c1a2c3a/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777162216
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777162216
https://assets1-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777162216
IT Security - DoIT
0
0
true
Fri, 30 Sep 2022 14:18:21 -0400