Judea Pearl wins 2011 Turing Award
Judea Pearl has won the 2011 A.M. Turing Award for "fundamental contributions to artificial intelligence through the development of a calculus for probabilistic and causal reasoning." Pearl pioneered the use of Bayesian networks and causal modeling as an approach to reasoning with uncertain knowledge and made man other contributions to probabilistic approaches to artificial intelligence. He has been a Professor of Computer Science at UCLA since 1970.
The Turing Award is ACM's most prestigious technical award and given for major contributions of lasting importance to computing. The award is sometimes referred to as the "Nobel Prize" of Computing and is named in honor of the British mathematician and computer scientist Alan Mathison Turing.
]]>
Judea Pearl has won the 2011 A.M. Turing Award for "fundamental contributions to artificial intelligence through the development of a calculus for probabilistic and causal reasoning." Pearl...
http://www.csee.umbc.edu/2012/03/judea-pearl-wins-2011-turing-award/
https://beta.my.umbc.edu/api/v0/pixel/news/13006/guest@my.umbc.edu/1bf8b271128e149e1f69f58308b1054b/api/pixel
news
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 15 Mar 2012 10:12:59 -0400
talk: Transition from the Academic World to Corporate Culture, 11:30 Fri 3/16
EE Graduate Seminar
From Backpack to Briefcase: Transition from
the Academic World to Corporate Culture
George W. Reynolds
Director, Industry and University Initiatives
Northrop Grumman Electronic Systems
11:30-12:45pm Friday 16 March 2012, ITE 237
This seminar explores the pitfalls that new hires can encounter as they transition to the corporate world from academia. We explore the personal characteristics that people will evaluate, over and above performance. We will learn the importance of having appropriate, unbiased mentors and how to choose them, as well as strategies to develop key relationships that add value to our career growth and non-technical education. The importance of image and appropriate wardrobe for success will be addressed in addition to what top executives look for when selecting staff with leadership potential.
George Reynolds is a licensed professional engineer with over forty years of experience with the Westinghouse Electric and Northrop Grumman Corporations. His current responsibilities include establishing key strategic relationships with selected universities for long-term research, business and recruitment partnerships. He is also responsible for sector wide initiatives that include knowledge management and introducing lean thinking into engineering and manufacturing organizations.
Mr. Reynolds has served as industry liaison for the Lean Aerospace/ Advancement initiatives at MIT since its inception in 1992. He also serves as the chairman and/or member of numerous engineering Advisory Boards for major universities, and is the past Chairman of the Aerospace Industries Associations Engineering Management Committee. Mr. Reynolds was selected as National Black Engineer of the Year for Professional Achievement in Industry in 1991, and Black Engineer of the Year for Corporate Support of Engineering Education in 2008. He is one of three people in the nation to receive two of these awards. In 2001, he was awarded the Distinguished Black Marylander Award.
Mr. Reynolds holds a B.S. in Engineering from Howard University, an M.S. in Engineering Administration from George Washington University, and is a graduate of the Program for Management Development at Harvard School of Business. He is also a Johns Hopkins Fellow in the Management of Change. He holds a black belt in Six Sigma and is an expert in Lean Thinking. Mr. Reynolds holds a commercial pilots license with multi-engine and jet ratings.
Host: Prof. Joel M. Morris
]]>
EE Graduate Seminar From Backpack to Briefcase: Transition from the Academic World to Corporate Culture George W. Reynolds Director, Industry and University Initiatives Northrop Grumman...
http://www.csee.umbc.edu/2012/03/talk-transition-from-the-academic-world-to-corporate-culture-1130-fri-316/
https://beta.my.umbc.edu/api/v0/pixel/news/12981/guest@my.umbc.edu/3deb6b2f313565d24a90ec725a59f5c1/api/pixel
electrical-engineering
news
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 14 Mar 2012 11:40:43 -0400
Wed, 14 Mar 2012 11:40:43 -0400
talk: Ram Sriram on Cyber-Physical Social Systems April 6

Cyber-Physical Social Systems: Research Challenges
Ram D. Sriram
Chief, Software and Systems Division
Information Technology Laboratory
National Institute of Standards and Technology
1:00pm 6 April 2012, ITE325 UMBC
We are witnessing a new revolution in computing and communication. The Internet, which has spanned several networks in a wide variety of domains, is having a significant impact on every aspect of our lives. The next generation of networks will utilize a wide variety of resources with significant sensing capabilities. Such networks will extend beyond physically linked computers to include multimodal information from biological, cognitive, semantic, and social networks. This paradigm shift will involve symbiotic networks of people (social networks), intelligent devices, and mobile personal computing and communication devices (mPCDs), that will form net-centric societies (NCS) or cyber-physical social systems (CPSS). mPCDs are already equipped with myriad sensors, with regular updates of additional sensing capabilities. Additionally, we are witnessing the emergence of “intelligent devices,” such as smart meters, smart cars, etc., with considerable sensing and networking capabilities. Hence, these devices – and the network — will be constantly sensing, monitoring, and interpreting the environment; this is sometimes referred to as the Internet of Things (IOT). The symbiosis of IOT and social networks will have significant implications for both the market for advanced computing and communication infrastructure and the future markets – for nearly 4.5 billion people — that CPSS will create. In this seminar, I will provide an overview of the Software and Systems Division at NIST, followed by a discussion of research challenges for CPSS with a specific focus on smart healthcare.
Dr. Ram D. Sriram is currently the chief of the Software and Systems Division, Information Technology Laboratory, at the National Institute of Standards and Technology. Before joining the Software and Systems Division, Sriram was the leader of the Design and Process group in the Manufacturing Systems Integration Division, Manufacturing Engineering Laboratory, where he conducted research on standards for interoperability of computer-aided design systems. He was also the manager of the Sustainable Manufacturing Program. Prior to joining NIST, he was on the engineering faculty (1986-1994) at the Massachusetts Institute of Technology (MIT) and was instrumental in setting up the Intelligent Engineering Systems Laboratory. Sriram has co-authored or authored nearly 250 publications, including several books. Sriram was a founding co-editor of the International Journal for AI in Engineering. In 1989, he was awarded a Presidential Young Investigator Award from the National Science Foundation. In 2011, Sriram received the ASME Design Automation Award for his work on computer-supported collaborative design. Sriram is a Fellow of ASME and AAAS, a member (life) of ACM, a Senior Member of the IEEE, and a member (life) of AAAI. Sriram has a B.Tech. from IIT, Madras, India, and an M.S. and a Ph.D. from Carnegie Mellon University, Pittsburgh, USA.
Host: Yelena Yesha
]]>
Cyber-Physical Social Systems: Research Challenges Ram D. Sriram Chief, Software and Systems Division Information Technology Laboratory National Institute of Standards and Technology...
http://www.csee.umbc.edu/2012/03/talk-ram-sriram-on-cyber-physical-social-systems-april-6/
https://beta.my.umbc.edu/api/v0/pixel/news/12970/guest@my.umbc.edu/d50de9c1bad88dcf76e8846d9a53da29/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 14 Mar 2012 08:08:50 -0400
Fri, 30 Mar 2012 00:40:50 -0400
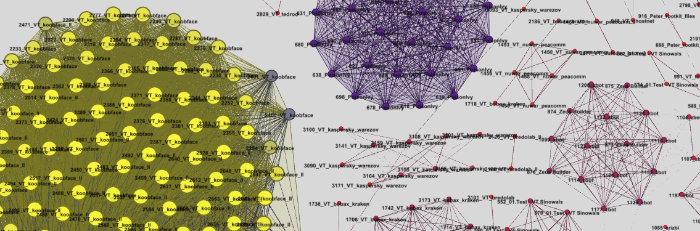
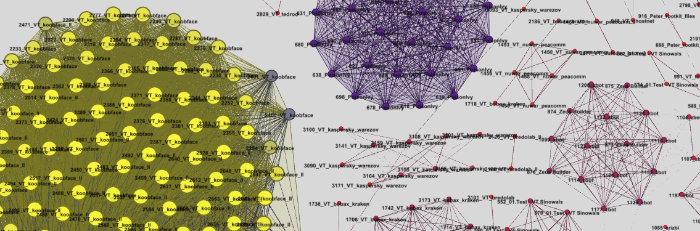
PhD Defense: Clustering and Visualization Techniques for Aggregate Trajectory Analysis
Ph.D. Dissertation Defense
Clustering and Visualization Techniques
for Aggregate Trajectory Analysis
David Trimm
1:00pm Thursday 15 March 15th 2012, ITE 365
Analyzing large trajectory sets enables deeper insights into multiple real-world problems. For example, animal migration data, multi-agent analysis, and virtual entertainment can all benefit from deriving conclusions from large sets of trajectory data. However, the analysis is complicated by several factors when using traditional analytic techniques. For example, directly visualizing the trajectory set results in a multitude of lines that cannot be easily understood. Statistical analysis methods and non-direct visualization techniques (e.g., parallel coordinates) produce conclusions that are non-intuitive and difficult to understand. By using two complementary processes—clustering and visualization—a new approach is developed to analyzing large trajectory sets. First, clustering techniques are developed and refined to group related trajectories together. From these similar sets, a trajectory composition visualization is created and implemented that clearly depicts the cluster characteristics including application-specific attributes. The effectiveness of the approach is demonstrated on two separate and unique data sets resulting in actionable conclusions. The first application, multi-agent analysis, represents a rich, spatial data that, when analyzed using this approach, shows ways to improve the underlying artificial intelligence algorithms. Student course-grade history analysis, the second application, requires tailoring the approach for a non-spatial data set. However, the results enable a clear understanding of which courses are most critical in a student's career and which student groups require assistance to succeed. In summary, this research contributes to methods for trajectory clustering, techniques for large-scale visualization of trajectory data, and processes for analyzing student data.
Committee
- Dr. Penny Rheingans (chair)
- Dr. Marie desJardins
- Dr. Anupam Joshi
- Dr. Marc Olano
- Dr. Sreedevi Sampath
]]>
Ph.D. Dissertation Defense Clustering and Visualization Techniques for Aggregate Trajectory Analysis David Trimm 1:00pm Thursday 15 March 15th 2012, ITE 365 Analyzing large trajectory...
http://www.csee.umbc.edu/2012/03/pfd-defense-clustering-and-visualization-techniques-for-aggregate-trajectory-analysis/
https://beta.my.umbc.edu/api/v0/pixel/news/12965/guest@my.umbc.edu/f7ad251362e248bf74a57da962a02490/api/pixel
computer-science
graduate
news
research
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 13 Mar 2012 23:30:09 -0400
Tue, 13 Mar 2012 23:30:09 -0400
Dr. Hillol Kargupta to speak at VERGE
 Dr. Hillol Kargupta will be one of over 80 speakers at GreenBiz's VERGE conference in Washinton D.C., which takes place this Wednesay, March 14–16.
Dr. Hillol Kargupta will be one of over 80 speakers at GreenBiz's VERGE conference in Washinton D.C., which takes place this Wednesay, March 14–16.
The conference foucses on sustainability by exploring technological advances that deal with energy, information, buildings, and transportation.
Speakers include the likes of AOL Co-founder, Steve Case, Robin Chase, founder of carsharing revolution, Zipcar, textbook publishing mogul Tim O'Reilly, and other executives working at the intersection of technology and enivronmental awareness.
The VERGE website credits Dr. Kargupta as a "Guru" for Data Mining for M2M Applications. He is the president of Agnik, a data analytics company for distributed, mobile, and embedded environments that has been developing vehicle performance monitoring software.
On Thursday, March 15 at 1:30 p.m., Dr. Kargupta will discuss "Connected Cars and Beyond" with Shelby Clark Founder & Chief Community Officer of RelayRides, Tim Johnson Strategic Opportunity Manager of Sprint, Nick Pudar Vice President of Planning and Business Development at OnStar, and Marc Gunther Senior Writer at the GreenBiz Group. Register at the VERGE website to watch a live stream of Dr. Kargupta's and other presentations for free.
]]>
Dr. Hillol Kargupta will be one of over 80 speakers at GreenBiz's VERGE conference in Washinton D.C., which takes place this Wednesay, March 14–16. The conference foucses on sustainability by...
http://www.csee.umbc.edu/2012/03/dr-hillol-kargupta-to-speak-at-verge/
https://beta.my.umbc.edu/api/v0/pixel/news/12938/guest@my.umbc.edu/d1f1becb303f242194a8e588df5c4611/api/pixel
faculty-and-staff
news
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 13 Mar 2012 13:37:05 -0400
Cyberdawgs make it to CyberWatch regional competition

Photo courtesy www.midatlanticccdc.org
This weekend, UMBC’s Cyber Defense club, the Cyberdawgs, will be one of eight schools vying for the win at the CyberWatch Mid-Atlantic Collegiate Cyber Defense Competition (CCDC) Regional Finals. The competition, the first of its kind to focus on the operational aspects of protecting and managing an existing “commercial” network infrastructure, will take place at the Johns Hopkins University Applied Physics Lab from March 14–18, according to the CCDC website.
“I always get excited for these types of competitions,” says Marc Warfield, president of the Cyberdawgs. A Junior Information Systems major, Warfield hopes to eventually pursue a career in software development with a focus in network and computer security. “I enjoy the field because it’s so dynamic and keeps everyone on their toes.”
In late February, Warfield and his teammates competed against twenty-five schools during a three-hour virtual qualifying round. “We had to secure five different virtual machines and complete tasks that they assigned us during the three hours of scoring,” he explains.
Now only eight schools from the region are left; among them Towson University, Capitol College, and Howard County Community College. Warfield and seven of his teammates will represent UMBC. “We sadly didn’t make it to regionals last year, so it feels good to make it there this year,” he says. “I’m excited to meet people that are already working in the field and considered to be “rockstars” in the computer security discipline.”
Conceived in 2006, the CCDC is funded by CyberWatch, an Advanced Technological Education (ATE) Center. Since then, the center’s mission has been to “improve the quantity and quality of the nation’s information assurance (IA) workforce,” says the website.This year, the competition’s theme is “Healthcare IT.” During the competition, the teams must “ensure the systems supply the specified services while under attack from a volunteer Red Team" and “satisfy periodic “injects” that simulate business activities IT staff must deal with in the real world.”
Warfield explains that his preparation strategy includes “Redbull and long weekend nights.” “We practice securing machines and setting up web applications along with learning to configure them,” he says.
This year’s CCDC is the first to include a Speaker Symposium that’s free and open to the public. Kicking off Wednesday morning, the symposium features founder and CEO of Oculis Labs, Bill Anderson with a speech entitled “Causes of Data Breaches in Healthcare? Just Look Around,” and Larry Pesce and Darren Wigley, members of the PaulDotCom Security Weekly podcast, whose presentation is called “MEDIC! Building and Rules of the 2012 Badges.”
If Warfield and his teammates place in the competition this weekend, they will make it to the National competition which will take place in San Antonio, Texas in mid-April. Schools currently slated to compete in the Nationals include the University of Alaska Fairbanks, the Air Force Academy, UNC Charlotte, Rochester Institute of Technology, and Texas A&M University.
]]>
Photo courtesy www.midatlanticccdc.org This weekend, UMBC’s Cyber Defense club, the Cyberdawgs, will be one of eight schools vying for the win at the CyberWatch Mid-Atlantic Collegiate Cyber...
http://www.csee.umbc.edu/2012/03/cyberdawgs-make-it-to-cyberwatch-regional-competition/
https://beta.my.umbc.edu/api/v0/pixel/news/12934/guest@my.umbc.edu/21045978d289714d351cc9f401203352/api/pixel
news
students
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
6
0
true
Tue, 13 Mar 2012 09:35:40 -0400
Tue, 13 Mar 2012 09:35:40 -0400
New T-SITE scholarship program targets tech transfer students
 Next fall, a new scholarship program geared toward transfer students majoring in technology fields will offer ten students the support—both financial and otherwise—that they need. It’s called T-SITE (Transfer-Scholarships in Information Technology and Engineering), and similar to the previous SITE (Scholars in Information Technology and Engineering) program, is supported by an NSF S-STEM grant.
Next fall, a new scholarship program geared toward transfer students majoring in technology fields will offer ten students the support—both financial and otherwise—that they need. It’s called T-SITE (Transfer-Scholarships in Information Technology and Engineering), and similar to the previous SITE (Scholars in Information Technology and Engineering) program, is supported by an NSF S-STEM grant.
The program is the brainchild of a team of seven women sprinkled throughout IT and Engineering departments in the College of Engineering and Information Technology at UMBC. Dr. Penny Rheingans, Director of the Center for Women in Technology (CWIT) and a professor of Computer Science and Electrical Engineering, is the Principal Investigator for the project. Five professors will  serve as faculty mentors for the future scholars: Dr. Marie desJardins (Computer Science), Dr. Gymama Slaughter (Computer Engineering), Dr. Anne Spence (Mechanical Engineering), Dr. Taryn Bayles (Chemical, Biochemical, and Environmental Engineering), and Dr. Carolyn Seaman (Information Systems). Dr. Susan Martin, the Associate Director of CWIT, has been reaching out to Maryland community colleges and will teach a transfer student seminar for the selected scholars. “I don’t think any of us could do it without the others,” says Dr. Rheingans of her team of dedicated collaborators.
serve as faculty mentors for the future scholars: Dr. Marie desJardins (Computer Science), Dr. Gymama Slaughter (Computer Engineering), Dr. Anne Spence (Mechanical Engineering), Dr. Taryn Bayles (Chemical, Biochemical, and Environmental Engineering), and Dr. Carolyn Seaman (Information Systems). Dr. Susan Martin, the Associate Director of CWIT, has been reaching out to Maryland community colleges and will teach a transfer student seminar for the selected scholars. “I don’t think any of us could do it without the others,” says Dr. Rheingans of her team of dedicated collaborators.
“It’s particularly hard for transfer students to really become an integrated part of the community,” says Dr. Penny Rheingans. Transfer students often are at a disadvantage because they miss out on all the orientating activities showered on freshman, she explains. As a result, they’re less aware of campus  resources and tend to feel disconnected from the campus community. T-SITE aims to change all that.
resources and tend to feel disconnected from the campus community. T-SITE aims to change all that.
Starting in the fall of 2012, the grant will award ten financially needy transfer students with partial scholarships: $6,700 each, capped by an individual student's financial need. Eligible students must intend to major in one of the five IT or Engineering majors: Computer Science, Computer Engineering, Mechanical Engineering, Chemical and Biochemical Engineering, and Information Systems. In addition to financial support, future T-SITE scholars will be warmly integrated into the CWIT Scholars community, where they can take advantage of its outpouring of resources and community events.
“We are leveraging CWIT to make this work and we’re taking advantage of CWIT infrastructure. It’s an  extension of CWIT in that we’re looking at it as a vehicle for increasing diversity in these fields,” says Dr. Rheingans. “Not just gender,” she adds, “but gender’s what we’re particularly good at.”
extension of CWIT in that we’re looking at it as a vehicle for increasing diversity in these fields,” says Dr. Rheingans. “Not just gender,” she adds, “but gender’s what we’re particularly good at.”
Like the CWIT program, T-SITE won’t limit the scholarship pool by gender. “We would want men that we bring in as part of the T-SITE program to be supportive of increasing gender diversity,” says Dr. Rheingans. “Having allies that believe in the mission is part of what makes it work.”
Dr. Rheingans’ experience with the successes of the CWIT and SITE programs makes her confident that the T-SITE programs will give its scholars a leg up. “The support network makes a huge difference,” says Dr. Rheingans, who explains that the CWIT and SITE programs had nearly 90%  retention in the major compared to the nationwide statistic of around 50%.
retention in the major compared to the nationwide statistic of around 50%.
In addition to community support, the team has conceived a transfer student transition seminar to ensure that T-SITE scholars have the means to make a smooth transition. Taught by Dr. Martin, the seminar will have students connect with campus resources, identify and apply for internships, develop a career portfolio, learn about their own leadership styles, practice collaboration, and get insights from industry speakers. “The real purpose is to help them with the transition to UMBC and to address the professional development issues that are on the minds of transfer students,” says Dr. Martin.
Dr. Martin has been collaborating with UMBC’s Transfer Student Alliance to reach out to Montgomery College, the Community College of Baltimore County (CCBC), and Prince George’s Community College for help identifying qualified students. Application materials are available on the CWIT website and transfer students entering UMBC for the Fall 2012 semester must apply by April 20, 2012. The scholarship committee—made up of the band of five faculty mentors, Dr. Rheingans, and Dr. Martin—will then interview candidates to select the first cohort of ten T-SITE scholars.
 Though the current NSF grant will support the T-SITE program for three years (30 students in all), Dr. Rheingans hopes the program will extend well beyond that. “This is something for which the need will not go away,” she says about supporting transfer students. Though the renewal of the program into future years isn’t a certainty, chances are that when the time comes, the team will re-submit a proposal to seek further funding. “It’s hard to imagine not wanting to do that.”
Though the current NSF grant will support the T-SITE program for three years (30 students in all), Dr. Rheingans hopes the program will extend well beyond that. “This is something for which the need will not go away,” she says about supporting transfer students. Though the renewal of the program into future years isn’t a certainty, chances are that when the time comes, the team will re-submit a proposal to seek further funding. “It’s hard to imagine not wanting to do that.”
]]>
Next fall, a new scholarship program geared toward transfer students majoring in technology fields will offer ten students the support—both financial and otherwise—that they need. It’s called...
http://www.csee.umbc.edu/2012/03/new-t-site-scholarship-program-targets-tech-transfer-students/
https://beta.my.umbc.edu/api/v0/pixel/news/12930/guest@my.umbc.edu/1468fec4d5306cd7b227b2c97b1e6c46/api/pixel
faculty-and-staff
news
other
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 13 Mar 2012 08:50:43 -0400
Tue, 13 Mar 2012 08:50:43 -0400
Greater Baltimore Technology Council event calendar
If you are interested in entrepreneurship and the local startup community, especially in information technology, you should take a look at the Greater Baltimore Technology Council. This is a local organization of people devoted to "expanding the region’s technology community and supports technology companies with innovative programming, resources, links to capital markets and connections."
One useful new resource is the GBTC's event calendar, which lists technology events in and around Baltimore. If you have will be of interest to the GBTC community you can submit them easily via a simple form.
]]>
If you are interested in entrepreneurship and the local startup community, especially in information technology, you should take a look at the Greater Baltimore Technology Council. This is a local...
http://www.csee.umbc.edu/2012/03/greater-baltimore-technology-council-event-calendar/
https://beta.my.umbc.edu/api/v0/pixel/news/12879/guest@my.umbc.edu/c6503ed806879d639af8366c25116d0f/api/pixel
en
news
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
6
0
true
Sat, 10 Mar 2012 13:45:14 -0500
Thu, 08 Mar 2012 22:45:14 -0500
talk: Self-sustainable Cyber-physical System Design

Self-sustainable Cyber-physical System Design
Dr. Nilanjan Banerjee
University of Arkansas Fayetteville
1:00pm Tuesday 13 March 2012, ITE 325b UMBC
Renewable energy can enable diverse self-sustainable cyber-physical systems with applications ranging from healthcare to off-grid home energy management. However, there are several challenges that need to be addressed before such systems can be realized. For instance, how do we balance the small and often variable energy budgets imposed by renewables with system functionality? How can we design sensitive physical sensors and efficient harvesting circuits for mW energy sources such as sound and indoor light? For systems such as off-grid homes that interact with humans, how do we balance demand and supply while being cognizant to usability needs?
In this talk, I will present techniques that address these challenges. Specifically, I will propose a Hierarchical Power Management paradigm that combines platforms with varied energy needs to balance energy consumption and functionality, the design of an efficient harvester for sound scavenging, and sensitive ECG sensors. I will also present a measurement study that reveals the energy management challenges faced by off-grid home residents. Finally, I will conclude with the design of a solar replayer platform that allows immense flexibility in evaluating solar panel driven systems, and works for a wide range of panels.
Nilanjan Banerjee is an Assistant Professor in the department of Computer Science and Computer Engineering at University of Arkansas Fayetteville. He graduated with a M.S. and a Ph.D. from the University of Massachusetts at Amherst in 2009 and a BTech. (Hons.) from IIT Kharagpur in 2004. He has won the Yahoo! Outstanding dissertation award at UMass, a best undergraduate thesis award at IIT Kharagpur, and an Outstanding Researcher award at University of Arkansas. He is a 2011 NSF Career awardee and has won three other NSF awards (including the NSF I-Corp grant). His research interests span renewable energy driven systems, healthcare systems, and mobile systems.
Host: Anupam Joshi
See http://csee.umbc.edu/talks for more information
]]>
Self-sustainable Cyber-physical System Design Dr. Nilanjan Banerjee University of Arkansas Fayetteville 1:00pm Tuesday 13 March 2012, ITE 325b UMBC Renewable energy can enable diverse...
http://www.csee.umbc.edu/2012/03/talk-self-sustainable-cyber-physical-system-design/
https://beta.my.umbc.edu/api/v0/pixel/news/12874/guest@my.umbc.edu/649502cf0ae91475c5e9a7f9d4e7c4e0/api/pixel
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 10 Mar 2012 00:33:07 -0500
Sat, 10 Mar 2012 00:33:07 -0500
talk: Analytics for Detecting Web and Social Media Abuse
Analytics for Detecting Web and Social Media Abuse
Dr. Justin Ma, UC Berkeley
1:00pm Friday 16 March 2012, ITE 325, UMBC
The Web and online social media provide invaluable communication services to a global Internet user base. The tremendous success of these services, however, has also created valuable opportunities for criminals and other miscreants to abuse them for their own gain. As a result, it is both an important yet challenging problem to detect, monitor, and curtail this abuse. However, the large scale and diversity of these services, combined with the tactics used by attackers, make it difficult to discern one clear and robust signal for detecting abuse. One approach, relying on domain expertise, is to construct a small set of well-crafted heuristics, but such heuristics tend to rapidly become obsolete. In this talk, I will describe more robust approaches based on machine learning, statistical modeling, and large-scale analytics of large data sets.
First I will describe online learning approaches for detecting malicious Web sites (those involved in criminal scams) using lexical and host-based features of the associated URLs. This application is particularly appropriate for online algorithms as the size of the training data is larger than can be efficiently processed in batch and because the features that typify malicious URLs evolve continuously. Motivated by this application, we built a real-time system to gather URL features and analyze them against a source of labeled URLs from a large Web mail provider. Our system adapts in an online fashion to the evolving characteristics of malicious URLs, achieving daily classification accuracies up to 99% over a balanced data set.
Next I will describe our ongoing efforts for creating analytics for detecting social media abuse. Deciding on a universal definition of social media abuse is difficult, as abuse is often in the eye of the beholder. In light of this challenge, we explore a more formal definition based on information theory. In particular, we hypothesize that messages with low information content are likely to be abusive. From this, we develop a measure of content complexity to identify abusive users that shows promise in our early evaluations.
In addition to our own experiments in the lab, this work has found success in practice as well. Companies serving hundreds of millions of users have adopted these ideas to improve abuse detection within their own services.
Justin Ma is a postdoc in the UC Berkeley AMPLab. His primary research is in systems security, and his other interests include applications of machine learning to systems problems, systems for large-scale machine learning, and the impact of energy availability on computing. He received B.S. degrees in Computer Science and Mathematics from the University of Maryland in 2004, and he received his Ph.D. in Computer Science from UC San Diego in 2010.
Host: Anupam Joshi
See http://csee.umbc.edu/talks for more information
]]>
Analytics for Detecting Web and Social Media Abuse Dr. Justin Ma, UC Berkeley 1:00pm Friday 16 March 2012, ITE 325, UMBC The Web and online social media provide invaluable communication...
http://www.csee.umbc.edu/2012/03/talk-analytics-for-detecting-web-and-social-media-abuse-1pm-316/
https://beta.my.umbc.edu/api/v0/pixel/news/12876/guest@my.umbc.edu/6a06d76cfa8a670f2da3ca3d89138744/api/pixel
cybersecurity
news
research
security
social-media
talks
web
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 10 Mar 2012 00:01:06 -0500
Wed, 14 Mar 2012 00:01:06 -0400