Learn about Grad Degrees in Cybersecurity

Interested in breaking into the burgeoning field of Cybersecurity? Come to a Graduate Information Session on Wednesday, May 2 in ITE 104 at Noon to learn about UMBC's Master's programs in Cybersecurity.
Headed by program director Richard Forno, UMBC offers both a Master's in Professional Studies: Cybersecurity, a ten-course master’s degree that incorporates courses in cybersecurity strategy, policy, and management with more technical, hands-on cybersecurity courses, and a Graduate Certificate in Professional Studies: Cybersecurity Strategy & Policy, a four-course program that can be completed in a year.
To RSVP for next Wednesday's session, click here. In the meantime, take a look at the program brochure, fact-sheet, and website for more information.
]]>
Interested in breaking into the burgeoning field of Cybersecurity? Come to a Graduate Information Session on Wednesday, May 2 in ITE 104 at Noon to learn about UMBC's Master's programs in...
http://www.csee.umbc.edu/2012/04/learn-about-grad-degrees-in-cybersecurity/
https://beta.my.umbc.edu/api/v0/pixel/news/14431/guest@my.umbc.edu/691c5bffe0cd9c122813bb871c69b623/api/pixel
events
graduate
news
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 24 Apr 2012 09:36:48 -0400
Sat, 28 Apr 2012 19:36:48 -0400
MS defense: Distributed Model Consensus for Models of Locally Biased Measurements in Wireless Sensor Networks
MS Thesis Defense
Distributed Model Consensus for Models of Locally
Biased Measurements in Wireless Sensor Networks
Jacob Thompson
4:00pm Wednesday, 25 April 2012, ITE 325B, UMBC
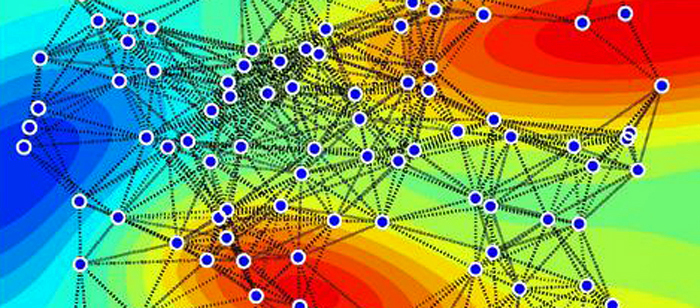
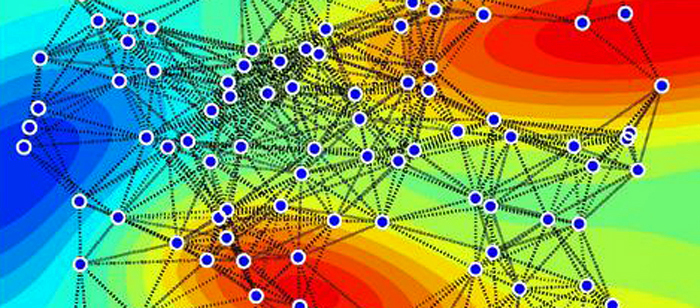
Wireless sensor networks (WSNs) consist of interconnected microsensors, each of which collects measurements from its local environment, which are often used in monitoring and control applications. These applications make inferences about the global and local states of the deployment environment. However, due to the limited communication and energy resources at the sensors, gathering all the raw data at a central fusion/control point is impractical.
Hence, it is essential to have distributed learning and inference in WSNs, such as learning a consensus model from the locally learned models. Consensus is challenging due to the limited resources of the sensors and the inherent bias of the individual sensor models learned from their local sensing environments. Two leading approaches for this problem are the approach by Zheng et al which uses loopy belief propagation on a certain graphical model based on the WSN topology and the local models, and the approach by Xiao et al which relies on gossip averaging of the parameters of the local models.
We focus on multivariate linear regression models, such as Bayesian, Ridge, and Lasso regression models. We analyze and extend the loopy Gaussian belief propagation (GaBP) approach to model consensus, and compare its performance to the gossip averaging approach. We experimentally find that GaBP tends to converge much faster than gossip averaging, but to a less accurate estimated consensus model (especially in the presence of multiple cycles in its corresponding graphical model). We also find that gossip averaging along paths in the WSN, tends to provide much faster convergence to more accurate estimated consensus models as compared to GaBP.
Committee: Professors Kostas Kalpakis (chair), Tim Oates and Yun Peng
]]>
MS Thesis Defense Distributed Model Consensus for Models of Locally Biased Measurements in Wireless Sensor Networks Jacob Thompson 4:00pm Wednesday, 25 April 2012, ITE 325B, UMBC...
http://www.csee.umbc.edu/2012/04/ms-defense-distributed-model-consensus-for-models-of-locally-biased-measurements-in-wireless-sensor-networks/
https://beta.my.umbc.edu/api/v0/pixel/news/14357/guest@my.umbc.edu/b49884a4df67ec8555195bf290cd5aa0/api/pixel
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
7
0
true
Mon, 23 Apr 2012 17:49:08 -0400
CSEE Students Take Part in 34th Annual Graduate Research Conference
 photo courtesy www.umbc.edu/gsa
photo courtesy www.umbc.edu/gsa
More than two-dozen Computer Science and Electrical Engineering graduate students are slated to present at the Graduate Student Association's annual Graduate Research Conference (GRC). The GRC will be held this Friday, April 27 and features a keynote presentation from Dr. Michael I. Nishimura, a UMBC alumnus who now works at Loyola University Chicago as a professor in the Department of Surgery, the Associate Director of the Oncology institute, the Associate Director of the Cancer Center Translations Research, and as Program Director of Immunologic Therapeutics.
This year, the CSEE presence at the GRC is even stronger than it was last year, when three CSEE students were awarded for outstanding presentations. The honorees were Varish Mulwad who received an award for an outstanding oral presentation on his dissertation research entitled "Generating Knowledge from Tables," Kavita Krishnaswamy who received an award for an outstanding oral presentation on her thesis research entitled "Path planning a roboticarm efficiently," and Akshya Iyengar who received an award for an outstanding poster presentation for her thesis research entitled "Estimating Temporal Boundaries of Events using Social Media Data".
Take a look at the list below, which includes the 27 CSEE graduate students who will present at the GRC this year.
Check out some photos from last year's conference.
Click here for a printable list of CSEE presenters.
Oral Presentations
Location: Sondheim 203
“Noise Reduction in AIRS Infared Earth Observing Radiance Grids using the Obscov Algorithm”
David Chapman, Milton Halem, Phuong Nguyen, and Jeff Avery
Time: 9:00 a.m.
“Heart Disease Prediction Model: A Data Mining Approach”
Soma Das
Time: 9:15 a.m.
“Measuring the Pulse Duration of Ultrafast Lasers”
Jared Dixon
Time: 9:30 a.m.
“Using Deceptive Packets to Increase Base-Station Anonymity in Wireless Sensor Network”
Yousef Ebrahimi and Mohamed Younis
Time: 9:45 a.m.
“SmartRate: A Rating Interpretation Mechanism for Agents in Smart Grid Markets”
Yasaman Haghpanah
Time: 10:00 a.m.
“Visualizing Changes to Directory Structure to Support Digital Forensics”
Timothy Leschke
Time: 10:15 a.m.
“Extracting Semantic Linked Data from Tables”
Varish Mulwad
Time: 10:30 a.m.
“Automatic Identification of Prescription Drugs Using Shape, Imprint, and Color”
Adrian Rosebrock
Time: 11:00 a.m.
“An Optical Sensor for a Ceramic Water Filtration System for the Detection of E.Coli Using a Microfluidic Chip”
Serina Woods
Time: 11:15 a.m.
Poster Presentations
Location: Albin O. Kuhn Library: 7th Floor
“Witness-based Saboteur Detection in Multi-agent Systems”
Petr Babkin
Time: 11:00 a.m.
“Entity Linking and Disambiguation for Smartphone Platforms”
Anurag Korde
Time: 11:00 a.m.
“Third-order Quadratically Converging, Quasi-Newton Optimization”
Rory Mulvaney
Time: 11:00 a.m.
“Supervised Learning Techniques for Predicting Risk of Breast Cancer using Genetic Information”
Aniket Bochare
Time: 11:12 a.m.
“Prostate Cancer Prognosis using Genomic Data”
Rohit Kugaonkar
Time: 11:12 a.m.
“Using Supervised Techniques for Classification of Conventional Data Items”
Nikhil Puranik
Time: 11:12 a.m.
“Surface Emitting Quantum Cascade Laser Array”
Xing Chen, Liwei Cheng, Dingkai Guo, and Fow-Sen Choa
Time: 11:24 a.m.
“Learning Sensitive to Multiple Sources of Costs”
Zachary Kurtz
Time: 11:24 a.m.
“Exploring Hidden Markov Model for Semantic Activity Prediction”
Amey Sane
Time: 11: 24 a.m.
“Calculating Representatives of Geographic Sites across the World”
Ashwinkumar Ganesan
Time: 11:36 a.m.
“Older Adults Interactions with a Touch Table Top Display Space”
Galina Madjaroff
Time: 11:36 a.m.
“Rendering of Smoke and Fire in a 3D Volume with Multiple Scattering”
Taekyu Shin
Time: 11:36 a.m.
“Chronic Disease Prediction: An Experimental Analysis Using the K-nearest Neighbor Algorithm”
Matthew Gately
Time: 11:48 a.m.
“Situation Aware Intrusion Detection Model”
Sumit S. More
Time: 11:48 a.m.
“Unsupervised Coreference Resolution for FOAF Instances”
Jennifer Sleeman
Time: 11:48 a.m.
“Towards an Intuitive Query System for DBpedia”
Lushan Han
Time: 12:00 p.m.
“Link Prediction Using Frequent Subgraphs”
Maksym Morawski
Time: 12:00 p.m.
“Modeling Motheye Antireflective Structures for Increased Coupling through As2S3 Optical Fibers”
Robert J. Weiblen
Time: 12:00 p.m.
]]>
photo courtesy www.umbc.edu/gsa More than two-dozen Computer Science and Electrical Engineering graduate students are slated to present at the Graduate Student Association's annual Graduate...
http://www.csee.umbc.edu/2012/04/csee-students-take-part-in-34th-annual-graduate-research-conference/
https://beta.my.umbc.edu/api/v0/pixel/news/14313/guest@my.umbc.edu/61be701cc406a1d1fe9535fd6e1b0fa7/api/pixel
alumni
events
graduate
news
research
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Mon, 23 Apr 2012 11:28:29 -0400
Tue, 24 Apr 2012 06:28:29 -0400
URCAD: Analyzing Social Media Data
Analyzing Social Media Data
Morgan Madeira
Junior, Computer Science
Social media has increasingly become an outlet for expression for a large part of our society. Literature suggests that analyzing data from these sites can lead to improvements in areas such as health-care and search-ad targeting. Users of these sites often associate with many other users described as “friends,” even if they do not have a strong connection, or what would be described as friendship in daily life. It is valuable to determine the strength of relationships between users and to identify communities within social networks. These communities represent people with similar characteristics, which are used by applications to solve many real-world problems. For instance, it is useful to identify groups that are interested in a specific movie genre. Information about these groups can be used to target movie advertisements towards the people most interested in that genre. These types of problems have similar characteristics to identifying close friends. We have created a system to collect and analyze the data about user characteristics, while being respectful of privacy concerns. The system is composed of a front end Facebook application and a back end machine-learning based tool. The front end component gathers data about a user and their friends. The back end uses the collected data and machine-learning techniques to determine relationships between users.
To learn more about the project, check out an interview with Morgan.
![]()
Catch Morgan's poster presentation at URCAD this Wednesday, April 25 in the University Center Ballroom from 10:00 a.m. to 12:30 p.m.
]]>
Analyzing Social Media Data Morgan Madeira Junior, Computer Science Social media has increasingly become an outlet for expression for a large part of our society. Literature suggests that...
http://www.csee.umbc.edu/2012/04/urcad-analyzing-social-media-data/
https://beta.my.umbc.edu/api/v0/pixel/news/14290/guest@my.umbc.edu/17f5124cac089fc48be8391a5b1c1942/api/pixel
events
news
research
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Mon, 23 Apr 2012 08:37:49 -0400
URCAD: Multiclass Datasets, Their Predictions, and Their Visualization

Multiclass Datasets, Their Predictions, and Their Visualization
Wallace Brown and Alexander Morrow with Kevin Winner
Senior, Computer Science
Sophomore, Computer Science
Many datasets contain a wealth of information. For example, a person may be described by their race, age, gender, income, marital status, nationality, level of education, etc. By analyzing this data, we can form educated and accurate predictions about individuals. We can, for instance, determine that a person with a particular race, age, nationality, and income is likely to be a college undergraduate. Our goal is to develop ways to visualize these predictions and the uncertainty associated with the predictions. Displaying data in a scatterplot is a standard means of describing two-dimensional information. However, displaying high-dimensional data (i.e., data that includes many attributes, such as age, race, and income) is significantly more challenging. We present a means of visualizing high-dimensional data sets and the predictive models derived from the data, using existing dimension reduction techniques and novel glyph-based displays.
To learn more about the project, check out an interview with Wallace and Alexander.


Catch Wallace and Alexander's presentation at URCAD this Wednesday, April 25 in the University Center 312 from 1:15 to 1:30 p.m.
]]>
Multiclass Datasets, Their Predictions, and Their Visualization Wallace Brown and Alexander Morrow with Kevin Winner Senior, Computer Science Sophomore, Computer Science Many datasets...
http://www.csee.umbc.edu/2012/04/urcad-multiclass-datasets-their-predictions-and-their-visualization/
https://beta.my.umbc.edu/api/v0/pixel/news/14291/guest@my.umbc.edu/597b313b850b38d0667feb420069878d/api/pixel
events
news
research
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Mon, 23 Apr 2012 08:32:54 -0400
MS Defense: Shamit Patel on a Working Theory of the Learning Rule for Dendritic Integration
MS Thesis Defense
Towards Implementation of a Pattern Recognition System based on
a Working Theory of the Learning Rule for Dendritic Integration
Shamit Patel
4:00pm Monday 23 April 2012, ITE 346, UMBC
My goal is to develop a working theory of the learning rule for dendritic integration, and to then implement a pattern recognition system based on that learning algorithm so that the algorithm can be evaluated for its generalization ability. In this regard, this thesis presents an implementation of Jeff Hawkins and Dileep George's Hierarchical Temporal Memory (HTM) pattern recognition system that's based on an existing theory of the learning rule for dendritic integration – spike-timing-dependent synaptic plasticity (STDP). The integration of this learning rule is the novel contribution of this thesis. I found that the STDP HTM system achieved much higher probabilistic classification accuracy and better generalization ability than the non-STDP HTM system. Probabilistic classification accuracy is a way of measuring classification accuracy in which a testing pattern is classified correctly if its label appears in the group of labels output by the top-level node of the HTM network.
Committee: Professors Tim Oates (Chair), Yun Peng and Tim Finin
]]>
MS Thesis Defense Towards Implementation of a Pattern Recognition System based on a Working Theory of the Learning Rule for Dendritic Integration Shamit Patel 4:00pm Monday 23 April 2012,...
http://www.csee.umbc.edu/2012/04/shamit-patel-dendritic-integration-pattern-recognition-machine-learning/
https://beta.my.umbc.edu/api/v0/pixel/news/14217/guest@my.umbc.edu/05ba953355971455f0b5d71ed6cb4a6a/api/pixel
computer-science
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 22 Apr 2012 11:39:41 -0400
PhD defense: DiffServ Assured Forwarded and Robust Header Compression: Performance Analysis
Ph.D. Dissertation Defense
DiffServ Assured Forwarded and Robust
Header Compression: Performance Analysis
Houcheng Lee
12:30pm Monday, 23 April 2012, ITE 201b
Performance analysis of network architecture and protocols can be done by using modeling and simulation or using emulation techniques. Modeling and simulation can be used to obtain qualitative results about a network protocol through building models of protocols under drastic abstractions. One major concern of the modeling approach is the fidelity of the results from a model simulation.
This dissertation presents detailed performance analyses of two major Internet standards using emulation techniques. The standards investigated are Differentiated Services (DiffServ) architecture and Robust Compression (ROHC) standard.
The DiffServ architecture was proposed to support quality of services (QoS) implementation in TCP/IP networks. In the first part of dissertation, a new and scalable approach to performance analysis of DiffServ architecture, based on fluid flow modeling approximation to TCP/UDP based traffic flows, is used to emulate millions of competing TCP and UDP flows across networks of various sizes, complexities and link speeds. The emulation involved real-world network constraints, including traffic prioritizations, limited buffers in routers, link congestion, active queue management (AQM) and packet drop policies on congested links. The results provided first quantitative understanding of the interactions of traffic with different drop precedencies in AF1 class traffic in a congested network.
The Robust Header Compression (ROHC) is proposed to implement efficient IP header compression on bandwidth constrained links in TCP/IP networks. In the second part of dissertation, an emulation tool, called CORE, developed at NRL is used to analyze the performance of ROHC. ROHC compresses packet headers at a sender side, and decompresses them at the receiver side to increase efficiency of a communication link. The results provided quantitative understanding of compression gains from using ROHC standard for compressing IPv4/UDP and IPv6/UDP traffic on links.
Committee:
- Dr. Deepinder Sidhu
- Dr. Yelena Yesha
- Dr. Konstantinos Kalpakis
- Dr. Ted M. Foster
- Dr. Edward Zieglar
]]>
Ph.D. Dissertation Defense DiffServ Assured Forwarded and Robust Header Compression: Performance Analysis Houcheng Lee 12:30pm Monday, 23 April 2012, ITE 201b Performance analysis...
http://www.csee.umbc.edu/2012/04/phd-defense-diffserv-assured-forwarded-and-robust-header-compression-performance-analysis/
https://beta.my.umbc.edu/api/v0/pixel/news/14049/guest@my.umbc.edu/8f5c5de540d5a96633cc1a92aee77364/api/pixel
computer-science
graduate
news
research
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 19 Apr 2012 23:18:52 -0400
Chat with Graphics Engineer Joshua Barczak
Find out what it's like to work in the game industry

]]>
http://www.csee.umbc.edu/2012/04/chat-with-graphics-engineer-joshua-barczak/
https://beta.my.umbc.edu/api/v0/pixel/news/14027/guest@my.umbc.edu/109d3e2a46e4a1de005864d4bca52071/api/pixel
home-page
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 19 Apr 2012 15:56:07 -0400
Thu, 19 Apr 2012 17:31:05 -0400
CSEE Students Secure Undergraduate Research Awards (URA)
Congratulations to our Computer Science and Electrical Engineering undergraduate students who have recently been selected as Undergraduate Research Award (URA)Scholars. The URA provides undergraduates with up to $1,500 to fund their original research projects. The work is done in conjunction with a faculty mentor, and is then presented at UMBC's Undergraduate Research and Creative Achievement Day (URCAD) in April. This year, these students and their faculty advisors will be recognized at URCAD on Wednesday, April 25 at noon in the University Center, Room 312.
David Eisen
Computer Engineering, Senior
Faculty Advisor: Fow-Sen Choa
David’s research focuses on the study of cultured neuron inhibition and excitation via optical stimuli from mid-IR (MIR) quantum cascade lasers (QCL).
“It was very exciting news to hear my URA proposal was accepted. This is my first research experience and proposal, so I believe this award will give me the confidence to pursue other opportunities in the future. The URA will give me a hands-on learning experience in the field of photonics research by working alongside Professor Choa as well as graduate students. Not only does this look good on a resume, but it gives me a chance to really get a taste for what real world challenges and rewards await after graduation.”
Julian Field
Computer Engineering, Junior
Faculty Advisor: Tinoosh Mohsenin
Julian will be doing research in UMBC's Energy Efficient and High Performance Computing Lab. His task will be the development and mapping of a many-core processor for the purpose of performing ultrasound imaging applications. Many cores on the processor will improve performance and reduce the running time of the processes. The processor will be designed using the Verilog hardware description language (HDL) and will be implemented by programming the design into a Field-Programmable Gate Array (FPGA). Using an FPGA not only reduces the cost of the design, but it also speeds up implementation.
"I felt very honored to receive the award, and I believe that it is going to help me in several ways. It allows me to get paid for doing research in a field that fascinates me and in which I hope to work in the future. Besides the obvious financial benefit, the award adds weight to my research when I list it on my resume, and this should be of great value when I apply to graduate school and for Computer Engineering jobs and internships in the future."
Thomas A Hervey
Information Systems/ Geography, Sophomore
Aneep Bindra
Computer Science, Sophomore
Zachary Hullihen
Computer Science, Junior
Faculty Advisor: Marc Olano
"Lights, Camera, Motion, Action: The Dance Application of Microsoft's Kinect and Intelligent Stage Lighting."
"Receiving this award has given me a stronger incentive to work my hardest and apply myself beyond [the] academic realm. This award will be beneficial because it will provide necessary funds for unusual but necessary research tools. I look forward to strengthening my presentation skills at URCAD next year as well as refining my organizational skills through planned documentation and procedures during the actual experimentation. The award overall certainly creates a sense of confidence within the research community. I find it likely that students that are not active in research will hear about the award and benefits through their friends' experiences, and current URA scholars will continue research through new projects." -Thomas A. Hervey
Alex Morrow
Computer Science, Sophomore
Faculty Advisor: Marie desJardins
"Quantitative Evaluation of Dimension Reduction for Visualization and Analysis."
Alex’s research branches off of his current research on visualization and analysis techniques to facilitate user understanding of the uncertainty associated with statistical models that have been learned from data. Alex will analyze and evaluate dimension reduction methods. Using a set of quantitative metrics compiled by his research advisors Dr. Marie desJardins and Dr. Penny Rheingans, Alex will compare the performance of several dimension reduction techniques in a number of different application domains.
Adam Page
Computer Engineering / Math
Faculty Advisor: Dr. Tinoosh Mohsenin
Adam’s research involves designing an energy efficient and high performance error correction Low Density Parity Check Decoder circuit for IEEE 802.11ad standard, the next generation of Wireless Local Arena Network (WLAN). The design will include an efficient architecture for the decoder using Verilog coding and VLSI implementation.
“I am both honored and excited to receive this award. I know the URA will give me the opportunity to apply knowledge I have gained from all of my courses into a real world application.”
Don’t forget to meet our URA scholars at URCAD next Wednesday, April 25 at noon in the University Center, Room 312.
]]>
Congratulations to our Computer Science and Electrical Engineering undergraduate students who have recently been selected as Undergraduate Research Award (URA)Scholars. The URA provides...
http://www.csee.umbc.edu/2012/04/csee-students-secure-undergraduate-research-awards-ura/
https://beta.my.umbc.edu/api/v0/pixel/news/13995/guest@my.umbc.edu/905687b090bcdb1fef2f59e1e5ab7f1e/api/pixel
news
other
research
students
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
7
0
true
Thu, 19 Apr 2012 10:09:52 -0400
MS defense: Heart Disease Prediction: A Data Mining Approach

Masters Thesis Defense
Heart Disease Prediction: A Data Mining Approach
Soma Das
2:00pm Monday, 23 April 2012, ITE 201B
Data mining is a field of computer science that combines statistical analysis and machine learning to detect hard-to-discern patterns from large amounts of data. It employs different algorithms to learn different patterns from training or experience and apply it to classify, predict or identify patterns. The healthcare environment is very information rich. There is a wealth of clinical data available within the healthcare systems. Also due to recent advancement of genomic research vast amount of genetic data are also available. Effective analysis tools are needed to discover hidden relationships and trends in these data. These tools are necessary to correctly diagnose people at risk of disease based on the derived knowledge from the data.
We used data mining techniques to evaluate the interaction between traditional risk factors and gene variants such as Single Nucleotide Polymorphisms (SNPs) towards Coronary Heart Disease (CHD) susceptibility in a prospective study of older population aged 65 and older. In our thesis we asked two questions whether we can predict CHD at birth or adding genetic information to traditional risk factors predict CHD better than traditional risk factors alone.We also analyzed two popular machine learning algorithms to determine the most efficient method on medical datasets mining. The evaluation is based on a set of performance metrics. We also applied a clustering method to identify different subgroups present in the selected datasets.
We chose eight traditional risk factors of CHD and 23 SNPs that had previously been reported to be associated with CHD. We then tested the association of these SNPs with CHD in cardiovascular Health Study (CHS). Based on previous studies, we pre specified a risk allele for each of 23 SNPs. We assigned coding values for homozygote, heterozygote, and the no risk homozygote SNPs and then combined these with traditional risk factors for each individual before feeding it to machine learning algorithms. We evaluated different classification algorithms using 10 fold cross validation test.
Receiver Operating Characteristic Curves (ROC) were plotted separately based on traditional risk factors alone and traditional risk factors plus SNPs. The increase in the Area Under Curve (AUC) was statistically significant for Whites and suggestive of improved CHD prediction for African American. We also found out that using only SNPs predicts CHD a little bit better than random guessing for only whites. The results gained from analysis suggest Naïve Bayes to be the best classifier for the given domain.
This study demonstrates the concept of using multiple SNPs as independent risk factors and indicates that it can improve prediction of incident CHD. Adding SNPs to traditional risk factors did not improve the prediction model dramatically as we expected but it was statistically significant.
Committee:
- Dr. Michael Grasso (co-chair)
- Dr. Anupam Joshi
- Dr. Yelena Yesha
]]>
Masters Thesis Defense Heart Disease Prediction: A Data Mining Approach Soma Das 2:00pm Monday, 23 April 2012, ITE 201B Data mining is a field of computer science that combines statistical...
http://www.csee.umbc.edu/2012/04/ms-defense-heart-disease-prediction-a-data-mining-approach/
https://beta.my.umbc.edu/api/v0/pixel/news/13996/guest@my.umbc.edu/0e3f11efb1128bb1935237c75a3d8e0a/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 19 Apr 2012 10:02:22 -0400