Account data breach: Nitro
Digital Document Service Breached
In September 2020, a Portable Document Format(PDF) file and digital document service, Nitro, suffered a data breach. This breach contained data for approximately 78 million customers and was exposed online. The customer information included names, passwords and the titles of documents. No financial information was leaked.
1,440 UMBC accounts were victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a Nitro account, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach, visit: https://haveibeenpwned.com/.
More about Nitro data breach:
https://infosec.berry.edu/2021/01/19/data-breach-notification-nitro-pdf/#:~:text=In%20September%20of%202020%20there%20was%20a%20breach,or%20vikings.berry.edu%20email%20address%20 included%20in%20the%20 breach.
If you have any questions or concerns, email us at: security@umbc.edu.
Information about this breach was provided to us by Have I Been Pwned(HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
In September 2020, a Portable Document Format(PDF) file and digital document service, Nitro, suffered a data breach. This breach contained data for approximately 78 million customers and was...
https://beta.my.umbc.edu/api/v0/pixel/news/112310/guest@my.umbc.edu/b015eeb17b697f9414e770c24f4ad2a9/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776949508
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1776949508
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776949508
IT Security - DoIT
0
0
true
Tue, 14 Sep 2021 16:04:20 -0400
Tue, 14 Sep 2021 16:05:04 -0400
Account data breach: Romwe
Online Fashion Site Breached
In June 2018, an online fashion website, Romwe, suffered a data breach. This breach has data for approximately 20 million customers. The data was sold online. The customer information includes names, email addresses, IP addresses, physical addresses, phone numbers, and passwords. No financial information was leaked.
229 UMBC accounts were potential victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a Romwe account, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach visit:https://haveibeenpwned.com/.
More about Romwe data breach:
https://us.romwe.com/datasecurityFAQs-a-1039.html?SASSource=cjunction&affiliateID=100357191_5250933&url_from=cj.com&cjevent=dd0a33c1077f11ec804300290a82b82d
If you have any questions or concerns, email us at:security@umbc.edu.
Information about this breach was provided to us by Have I Been Pwned(HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
In June 2018, an online fashion website, Romwe, suffered a data breach. This breach has data for approximately 20 million customers. The data was sold online. The customer information includes...
https://beta.my.umbc.edu/api/v0/pixel/news/112308/guest@my.umbc.edu/685d281e225088a2a9a529d5cdcfb79b/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776949508
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1776949508
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776949508
IT Security - DoIT
0
0
true
Tue, 14 Sep 2021 16:00:50 -0400
Vendor Breaches and Account Compromises
Password Stopped Working? This Might Be Why.
Vendor Breaches and Account Compromises
Internet vendors will, at times, suffer data breaches. Sometimes the service will attempt to contact it’s account holders and other times it won’t. Often, after some time has passed, the malicious actors who stole the original data or others who have acquired it in the meantime will release it publicly. UMBC’s Division of Information Technology (DoIT) subscribes to a service called HaveIBeenPwned which looks for such public releases and searches them for email addresses ending in @umbc.edu.
For example, if you registered for a member’s discount card with Giant Food or signed-up for online banking and entered your email address as myname@umbc.edu, DoIT may receive notification if a publicly released breach included that email address. This does NOT automatically mean that your UMBC account was compromised. If you use a different password on your Giant account than you use on your UMBC account, then your UMBC account is still secure.
If DoIT determines that your UMBC account has been compromised (or if we are unable to determine that it hasn’t), your password will be replaced with a random string of text. You will also receive email in your Password Reset Email account (not your primary UMBC account) notifying you of the password change.
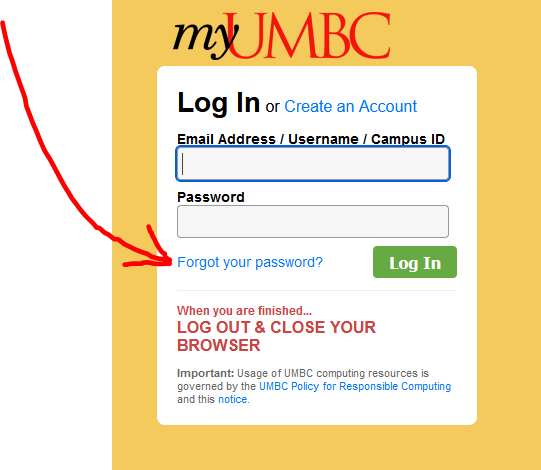
DoIT has no way of knowing what the new randomized password is, but you can recover access to your account by going to the MyUMBC login page and selecting “Forgot your password?” (see image below). You will then need to answer the security questions you set up for your account. After answering correctly, a link will be sent to your designated Password Reset Email account. If you have trouble with this, the Technology Support Center (https://doit.umbc.edu/tsc/, 410-455-3838) can assist you.
]]>
Vendor Breaches and Account Compromises Internet vendors will, at times, suffer data breaches. Sometimes the service will attempt to contact it’s account holders and other times it won’t. ...
https://beta.my.umbc.edu/api/v0/pixel/news/112307/guest@my.umbc.edu/40987f9cf2e4f4b975569be2b32010ef/api/pixel
learn
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776949508
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1776949508
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776949508
IT Security - DoIT
0
0
true
Tue, 14 Sep 2021 15:54:43 -0400
Mon, 01 Nov 2021 16:44:36 -0400
Hybrid Workplace Training Series: Docusign
Working remotely during the
pandemic required the workforce to constantly adapt work processes and
procedures and we all learned a great deal in this process. With a gradual
return to campus and hybrid work we will need to continue to upskill in order
to evolve as the nature of our work and our workplace evolves. The Hybrid
Workplace series offers staff training in the available productivity and
collaboration tools that will help contribute to individual and shared success
in our new normal.
TRAINING VIDEO: Docusign Session - Hybrid Workplace Training Series
Docusign is a tool that allows employees to
initiate a document to collect relevant data, digitally sign and follow a
workflow that replaces paper form completion and routing. There is no
need to print or scan and it is mobile friendly.
Course objectives:
·
Docusign uses (Single Use &
Templates)
·
Docusign framework (Webform,
Docusign Dashboard & Email Notifications)
·
Docusign portal as a dashboard
(Quick views & filters, docusign status and form review)
·
Docusign Do’s and Don’ts (Finish
Later, Decline to sign, Corrections, etc.)
·
Initiate a DocuSign document
·
Download a DocuSign document
·
Advanced Features Overview
(Overview for a future session)
Check out additional sessions from the Hybrid Workplace Training Series on demand
Foundations of the Hybrid Workplace. The series includes the
following sessions:
· Webex: Messaging and Calling
·
Webex Meetings
·
Gmail & Calendar
·
Google Docs
·
Google Sheets
·
Google Slides
Strategic Planning for the Hybrid Workplace. The series includes the following sessions:
·
Webex: Messaging and Calling
·
Webex Meetings
·
Facilitating Hybrid Meetings
·
Leading Hybrid Teams
·
Surveys with Google Forms/Qualtrics
·
Docusign
]]>
Working remotely during the pandemic required the workforce to constantly adapt work processes and procedures and we all learned a great deal in this process. With a gradual return to campus and...
https://beta.my.umbc.edu/api/v0/pixel/news/112272/guest@my.umbc.edu/50088af0581e8ecf327282ec4b097ae2/api/pixel
DocuSign
https://beta.my.umbc.edu/groups/docusign
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/319/63ea969223a3dc6eec7c5f3699d43f31/xsmall.png?1720464532
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/001/319/63ea969223a3dc6eec7c5f3699d43f31/original.png?1720464532
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/001/319/63ea969223a3dc6eec7c5f3699d43f31/xxlarge.png?1720464532
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/319/63ea969223a3dc6eec7c5f3699d43f31/xlarge.png?1720464532
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/001/319/63ea969223a3dc6eec7c5f3699d43f31/large.png?1720464532
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/319/63ea969223a3dc6eec7c5f3699d43f31/medium.png?1720464532
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/319/63ea969223a3dc6eec7c5f3699d43f31/small.png?1720464532
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/319/63ea969223a3dc6eec7c5f3699d43f31/xsmall.png?1720464532
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/319/63ea969223a3dc6eec7c5f3699d43f31/xxsmall.png?1720464532
DocuSign
0
0
false
Tue, 14 Sep 2021 09:12:45 -0400
Tue, 14 Sep 2021 09:15:45 -0400
Phishing Alert: President Freeman A. Hrabowski impersonator
This Is Not Dr. Hrabowski!
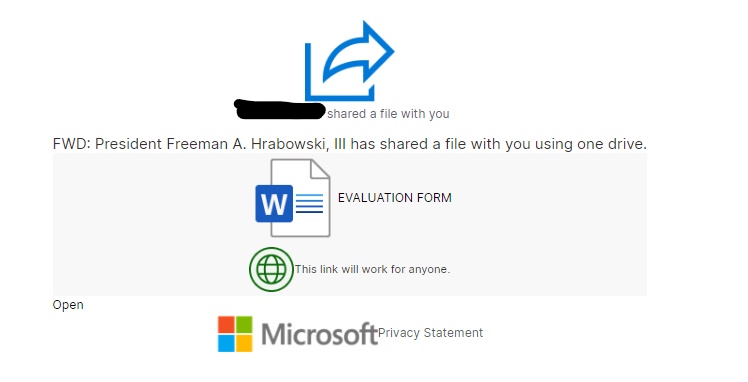
Recently, DOIT received an email from a compromised account at North Central Kansas Technical College(NCKTC) impersonating Dr Hrabowski. The email consisted of a Microsoft word document titled “EVALUATION FORM.” Below is a copy of the email. We removed the name of the NCKTC user and the To field for privacy reasons.
From: NCKTC member’s name <userID@ncktc.edu> Date: Wed, Aug 25, 2021 at 12:00 PM Subject: NCKTC member name shared "EVALUATION FORM" with you. To:
|
The link for the email will take you to the EVALUATION FORM document. See below to look inside the Word docs.
This link will ask you to sign in to your Microsoft account to view a file/form that the compromised account shared on One Drive. DO NOT CLICK ON ANY OF THE LINKS IN THE EMAIL OR THE DOCS. However, if you have done so already, please contact us immediately atsecurity@umbc.edu.
A lot of phishing emails contain a link that asks the recipients to sign into their accounts. Whenever you receive such emails, always try and verify with the senders on an entirely different email if you know them. Feel free to always send the message to us to validate the email.
For more information about phishing, visit:https://itsecurity.umbc.edu/critical/?id=98136.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Recently, DOIT received an email from a compromised account at North Central Kansas Technical College(NCKTC) impersonating Dr Hrabowski. The email consisted of a Microsoft word document titled...
https://beta.my.umbc.edu/api/v0/pixel/news/112267/guest@my.umbc.edu/5d2ed9704c24bfcbe9a7381192490342/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776949508
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1776949508
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776949508
IT Security - DoIT
0
0
true
Mon, 13 Sep 2021 18:28:49 -0400
Email marketing and the User-Agent-String
When What Looks Like Phishing Is Just Spam
Recently, DOIT received multiple reports of suspicious messages about student loans from email addresses with the format <emails@alert###.info>. The recipients of these messages marked them as phishing, but on careful investigation, we realised that these were legitimate. We therefore classified these messages as spam instead of phishing.
According to Phishing.org, “[p]hishing is a cybercrime in which a target or targets are contacted by email, telephone or text message by someone posing as a legitimate institution to lure individuals into providing sensitive data such as personally identifiable information, banking and credit card details, and passwords.” A third party company, CollegeLoans, sent these messages on behalf of these loan companies. Therefore, they are not malicious or criminal; instead, they are commercial.
Nonetheless, you might not have subscribed to receive these messages; hence they are spam. According to Cisco.com, “[s]pam is unsolicited and unwanted junk email sent out in bulk to an indiscriminate recipient list. Typically, ...sent for commercial purposes.” These emails are advertisements. They target university students since people in this demographic may need help covering tuition costs.
As mentioned earlier, these loan messages or advertisements originated from the third party company, CollegeLoan. This company is located in Puerto Rico. When you click on the link in the email, they will earn a commission whether or not you apply for the loans. It is business. It’s email marketing.
CollegeLoans sends out links on behalf of the following companies:
We were also suspicious because clicking the link might take the reader to Amazon.com rather than the advertised site. Among the information webservers can collect when you click is something called a User-Agent-String. This string helps the website determine the version of the browser you are using in order to avoid trying to perform advanced functions on old browsers. Bad actors may use this feature to hide from browsers commonly used to analyze malicious sites. However, we determined that the link is not malicious.
We are not sure of the reason that CollegeLoans chose to use browser detection. However, it is not uncommon for developers/companies to add this feature to their code/applications. According to MDN web Docs, using a browser detection would depend on one of the following:
If you are trying to work around a specific bug in some version of a browser.
If you are trying to check for the existence of a particular feature.
If you want to provide different HTML depending on which browser.
When you receive messages like this
, plese mark them as spam or phishing and continue to report them to us at: security@umbc.edu.
Source:
https://www.phishing.org/what-is-phishing
https://www.cisco.com/c/en/us/products/security/email-security/what-is-spam.html#:~:text=Spam%20email%20is%20unsolicited%20and,botnets%2C%20networks%20of%20infected%20computers.
To read more about user agents, visit https://towardsdatascience.com/the-user-agent-that-crazy-string-underpinning-a-bunch-of-analytics-86507ef632f0.
https://developer.mozilla.org/en-US/docs/Web/HTTP/Browser_detection_using_the_user_agent
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Recently, DOIT received multiple reports of suspicious messages about student loans from email addresses with the format <emails@alert###.info>. The recipients of these messages marked them...
https://beta.my.umbc.edu/api/v0/pixel/news/112255/guest@my.umbc.edu/96ad3039ef3fff9a72053358bbb5565d/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776949508
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1776949508
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776949508
IT Security - DoIT
0
0
true
Mon, 13 Sep 2021 14:45:05 -0400
Synchronize Bb groups in Collab breakout groups coming soon!
Maintain student learning between course & live sessions
Breakout groups are a powerful engagement tool for active learning in a synchronous session, providing private audio, video, whiteboard, application sharing, and chat for small group collaboration. Instructors can
distribute files with breakout groups, and
pull those files back into the main room for sharing with the entire class.
In Collaborate, breakout groups were
typically created with random student placements to the groups or manual placements by the instructor with an optional setting to allow students to switch groups.
With this new integration, however, instructors will be able to use their existing groups in their Blackboard courses to quickly create and launch breakout groups in Collaborate. As needed, instructors can adjust groups while maintaining the original placements.

The Collaborate and Blackboard Learn groups integration applies to both Original and Ultra courses, but will require the use of group sets rather than individually created groups in the course.
The Collaborate and Blackboard Learn groups integration is scheduled for gradual release in mid-September. As soon we have additional information, we will update the FAQs with how-to documentation and related resources. UPDATE: New FAQ is available.
Additionally, with this release, Collaborate will proactively inform users about outdated browser use and encourage them to upgrade to a supported browser. Users will still be allowed to join a session, but the experience may not be the same.
As always, if you have any questions about teaching, learning, and technology at UMBC, please consider the following options:
]]>
Breakout groups are a powerful engagement tool for active learning in a synchronous session, providing private audio, video, whiteboard, application sharing, and chat for small group...
https://my3.my.umbc.edu/groups/instructional-technology/posts/111913
https://beta.my.umbc.edu/api/v0/pixel/news/111913/guest@my.umbc.edu/b2f1689c1c04219624acc0f3a3bb8064/api/pixel
active-learning
breakout-groups
collaborate
fa2021
online-learning
ultra-update
Instructional Technology
https://beta.my.umbc.edu/groups/instructional-technology
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xsmall.png?1446126703
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/original.png?1446126703
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xxlarge.png?1446126703
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xlarge.png?1446126703
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/large.png?1446126703
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/medium.png?1446126703
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/small.png?1446126703
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xsmall.png?1446126703
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xxsmall.png?1446126703
Instructional Technology
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/913/13771dc0bfbc18b7486895087f95d15f/xxlarge.jpg?1630501227
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/913/13771dc0bfbc18b7486895087f95d15f/xlarge.jpg?1630501227
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/913/13771dc0bfbc18b7486895087f95d15f/large.jpg?1630501227
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/913/13771dc0bfbc18b7486895087f95d15f/medium.jpg?1630501227
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/913/13771dc0bfbc18b7486895087f95d15f/small.jpg?1630501227
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/913/13771dc0bfbc18b7486895087f95d15f/xsmall.jpg?1630501227
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/913/13771dc0bfbc18b7486895087f95d15f/xxsmall.jpg?1630501227
1
0
true
Tue, 07 Sep 2021 11:59:08 -0400
Mon, 13 Sep 2021 10:54:43 -0400
Free Training for Respondus Lockdown Browser & Monitor
Join an upcoming webinar to see the latest features
Join an upcoming training webinar from Respondus to see the latest features and integrations for LockDown Browser and Monitor. Learn how these applications are used with a range of online testing environments, virtual proctoring and Blackboard.
Instructor Training: LockDown Browser & Respondus Monitor
This comprehensive 45-minute training is intended for instructors who plan to use LockDown Browser and/or Respondus Monitor to protect academic integrity and ensure student identity during online testing. The training will cover:
- How to use LockDown Browser to prevent digital cheating in proctored testing environments
- How to use Respondus Monitor in non-proctored environments, to protect exam integrity and confirm student identity
- The student perspective using each application
- Efficient review of the assessment data collected, including the Review Priority system, timeline, and milestone features
- Best practices and tips for success with both applications
Pick your date/time and register directly with Respondus:
All attendees will receive a link to a recording after the session.
About Respondus Lockdown Browser
RLDB is a custom browser that locks down the testing environment within Blackboard. Students are unable to copy, print, access other applications, or visit other websites during an online exam. For additional information, please review
our FAQ collection.
NOTE: Students should not register for any instructor training session but instead, contact use the Respondus support tools embedded in RLDB, or
review this FAQ for further help.
]]>
Join an upcoming training webinar from Respondus to see the latest features and integrations for LockDown Browser and Monitor. Learn how these applications are used with a range of online testing...
https://my3.my.umbc.edu/groups/instructional-technology/posts/111939
https://beta.my.umbc.edu/api/v0/pixel/news/111939/guest@my.umbc.edu/c1e119d883cebce043b350ec39ac600e/api/pixel
respondus-lockdown-browser
respondus-monitor
rldb
training
webinar
Instructional Technology
https://beta.my.umbc.edu/groups/instructional-technology
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xsmall.png?1446126703
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/original.png?1446126703
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xxlarge.png?1446126703
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xlarge.png?1446126703
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/large.png?1446126703
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/medium.png?1446126703
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/small.png?1446126703
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xsmall.png?1446126703
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xxsmall.png?1446126703
Instructional Technology
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/939/3eaec6d8dd6be57d0d27fa0ef7b2a483/xxlarge.jpg?1630519917
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/939/3eaec6d8dd6be57d0d27fa0ef7b2a483/xlarge.jpg?1630519917
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/939/3eaec6d8dd6be57d0d27fa0ef7b2a483/large.jpg?1630519917
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/939/3eaec6d8dd6be57d0d27fa0ef7b2a483/medium.jpg?1630519917
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/939/3eaec6d8dd6be57d0d27fa0ef7b2a483/small.jpg?1630519917
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/939/3eaec6d8dd6be57d0d27fa0ef7b2a483/xsmall.jpg?1630519917
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/111/939/3eaec6d8dd6be57d0d27fa0ef7b2a483/xxsmall.jpg?1630519917
0
0
true
Wed, 01 Sep 2021 14:19:47 -0400
SCAM: University of Maryland Personnel Retirement Support
Retirement Phishing Scam
During the past week, the Division of Technology(DOIT) has received phishing reports of scammers impersonating state-licensed retirement support representatives. Below is an example of such a message. The reporter’s name and email have been removed to protect their privacy.
From: Jennifer Flynn <support@publicemployeeretirement.com> Date: Tue, Jun 22, 2021 at 2:07 PM Subject: University of Maryland Personnel Retirement Support To: <YOUR UMBC EMAIL>
Employee <YOUR FIRSTNAME>, All University of Maryland employees are eligible to schedule an annual phone call or video conference with a licensed representative to answer your retirement benefit questions. During your initial consultation, you will be providing your basic financial and retirement data to the representative so they can begin to calculate your potential retirement income. They are then able to provide examples regarding how much longer you may need to work to reach your retirement income goals, your best ways to utilize your 401(a)/403(b), and how your social security benefits may be affected. Please don't forget to indicate in the notes section which type of appointment you prefer (phone call or video conference). Also, be sure to leave the best phone number you can be reached at during that time. These representatives work with all MD State/University employees so appointments fill up quickly. Be sure to click the link below to schedule your consultation. https://campus.publicemployeeretirement.com/pera Disclosure - Licensed representatives are not employees of the college, state, or direct representatives of your specific plan, however, they are independently licensed fiduciaries with the state. To opt-out of future mailings, click on the following link: unsubscribe
|
This message is not legitimate. If you have received this email, DO NOT CLICK THE LINK IN THE EMAIL. The link takes you to the website below. DO NOT FILL OUT THIS FORM.

If you have filled out this form, DO NOT JOIN THE APPOINTMENT.If you have joined the video conference or phone call and provided your financial information to the actors, immediately notify your bank. View our article on Identity Theft to help protect your identity: https://itsecurity.umbc.edu/critical/?id=102139
Forward this email with its headers immediately to security@umbc.edu. Instructions on how to find the email headers can be found below.
The HR Department advises that all valid retirement-related emails are sent from their approved retirement vendors
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
During the past week, the Division of Technology(DOIT) has received phishing reports of scammers impersonating state-licensed retirement support representatives. Below is an example of such a...
https://beta.my.umbc.edu/api/v0/pixel/news/111785/guest@my.umbc.edu/3ad213f6b8e2a6163ced429e7afab217/api/pixel
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/original.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1776949508
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/medium.png?1776949508
https://assets1-beta.my.umbc.edu/images/avatars/group/7/small.png?1776949508
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1776949508
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1776949508
IT Security - DoIT
0
0
true
Wed, 25 Aug 2021 18:15:13 -0400
taki downtime completed
To all taki users,
Our work bringing the taki cluster environment up-to-date has concluded. Please begin normal use of the cluster environment.
Please let us know if you have any questions or concerns by submitting a descriptive help request form found at the following link.
Roy Prouty
HPC System Administrator
]]>
To all taki users, Our work bringing the taki cluster environment up-to-date has concluded. Please begin normal use of the cluster environment. Please let us know if you have any questions...
https://beta.my.umbc.edu/api/v0/pixel/news/111763/guest@my.umbc.edu/0a5cb6583a1a2898f7828aa106495c87/api/pixel
HPCF
https://beta.my.umbc.edu/groups/hpcf
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/659/63ae3e64663572042ecdd0ef493c16e1/xsmall.png?1596736674
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/659/63ae3e64663572042ecdd0ef493c16e1/original.png?1596736674
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/001/659/63ae3e64663572042ecdd0ef493c16e1/xxlarge.png?1596736674
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/659/63ae3e64663572042ecdd0ef493c16e1/xlarge.png?1596736674
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/659/63ae3e64663572042ecdd0ef493c16e1/large.png?1596736674
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/659/63ae3e64663572042ecdd0ef493c16e1/medium.png?1596736674
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/659/63ae3e64663572042ecdd0ef493c16e1/small.png?1596736674
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/659/63ae3e64663572042ecdd0ef493c16e1/xsmall.png?1596736674
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/659/63ae3e64663572042ecdd0ef493c16e1/xxsmall.png?1596736674
HPCF
1
0
false
Tue, 24 Aug 2021 20:43:00 -0400
