Training on Respondus LockDown Browser & Respondus Monitor
Learn to Deliver Online Assessments using these tools
| LockDown Browser is a custom browser that prevents digital cheating during an online exam. Respondus Monitor is a companion application for LockDown Browser that deters cheating when students take online exams in non-proctored environments. Students use their own computers with a standard webcam to record assessment sessions. |
This comprehensive training webinar is intended for instructors who plan to use LockDown Browser and/or Respondus Monitor with online exams. The session provides a detailed demonstration of both applications, including enhancements that make Respondus Monitor even more effective and easy to use. Click on one of the dates/times provided below to register for a webinar or visit https://web.respondus.com/webinars/ to register:
- Tuesday, August 25 at 1 pm ET / 10 am PT
- Thursday, August 27 at 2 pm ET / 11 am PT
- Tuesday, September 1 at 3 pm ET / 12 pm PT
- Wednesday, September 2 at 2 pm ET / 11 am PT
- Tuesday, September 8 at 12 pm ET / 9 am PT
- Wednesday, September 9 at 4 pm ET / 1 pm PT
- Tuesday, September 15 at 1 pm ET / 10 am PT
- Thursday, September 17 at 3 pm ET / 12 pm PT
- Wednesday, September 23 at 2 pm ET / 11 am PT
- Tuesday, September 29 at 12 pm ET / 9 am PT
USM OnTrack has added additional Quality Matters workshops in high-demand topics for the Fall term!
NEW - Quality Matters Fall Workshops
We are excited to announce that we have added a new set of Quality Matters workshops starting the week of September 14, targeted at providing just-in-time support for faculty teaching this fall. Topics include active learning strategies, assessment, accessibility, and increasing engagement. Please encourage faculty to register now to secure their spot.
There is no cost for any USM faculty or staff member to attend these workshops, but each workshop does have a 30-person limit, so we encourage you to promote these as soon as possible. We will be monitoring registrations as will add additional sessions if we see high demand.
Week of August 24 |
Wednesday August 26, 2020 | 1:00-3:00 | Creating Accessible Word Docs |
Thursday, August 27, 2020 | 9:00-11:00 | Providing Accessible Web Content |
Week of September 14 |
Tuesday, September 15, 2020 | 9:00-11:00 | Rethinking Assessments for Application & Engagement |
Tuesday, September 15, 2020 | 1:00-3:00 | Connecting LOs & Assessments |
Wednesday, September 16, 2020 | 9:00-11:00 | Active Learning Strategies |
Wednesday, September 16, 2020 | 1:00-3:00 | Increasing Learning Engagement with Web 2.0 Tools |
Thursday, September 17, 2020 | 9:00-11:00 | Helping Learners Track Their Progress |
Thursday, September 17, 2020 | 1:00-3:00 | Creating Rubrics |
Week of September 21 |
Tuesday, September 22, 2020 | 9:00-11:00 | Captioning Videos |
Tuesday, September 22, 2020 | 1:00-3:00 | Rethinking Assessments for Application & Engagement |
Wednesday, September 23, 2020 | 9:00-11:00 | Connecting LOs & Assessments |
Wednesday, September 23, 2020 | 1:00-3:00 | Active Learning Strategies |
Thursday, September 24, 2020 | 9:00-11:00 | Increasing Learning Engagement with Web 2.0 Tools |
Thursday, September 24, 2020 | 1:00-3:00 | Helping Learners Track Their Progress |
Week of September 28 |
Tuesday, September 29, 2020 | 9:00-11:00 | Creating Rubrics |
Tuesday, September 29, 2020 | 1:00-3:00 | Captioning Videos |
Wednesday, September 30, 2020 | 9:00-11:00 | Rethinking Assessments for Application & Engagement |
Wednesday, September 30, 2020 | 1:00-3:00 | Connecting LOs & Assessments |
Thursday, October 1, 2020 | 9:00-11:00 | Active Learning Strategies |
Thursday, October 1, 2020 | 1:00-3:00 | Increasing Learning Engagement with Web 2.0 Tools |
2-Step Instructions for Self-Registering for USM OnTrack QM Workshops
There is no cost for any USM faculty or staff member to attend these workshops, but each workshop does have a 30-person limit, so please sign up as soon as possible!
QM Coordinator information:
Dr. Sherri Braxton - University of Maryland-Baltimore County
]]>
USM OnTrack has added additional Quality Matters workshops in high-demand topics for the Fall term! NEW - Quality Matters Fall Workshops We are excited to announce that we have added a...
https://www.usmd.edu/cai/register-qm-workshops
Document
https://assets3-beta.my.umbc.edu/system/shared/attachments/ebe6073bdbd86da9914b32684e2176af/69ec1def/news/000/095/113/f56fd81299f45d30fae410987983d000/OnlineSessionSelfRegistrationInstructionsDedicated.pdf?1598303574
https://beta.my.umbc.edu/api/v0/pixel/news/95113/guest@my.umbc.edu/a07f520e20764d330c41f78220d7b517/api/pixel
online-learning
professional-development
qm
quality-matters
usm
Instructional Technology
https://beta.my.umbc.edu/groups/instructional-technology
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xsmall.png?1446126703
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/original.png?1446126703
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xxlarge.png?1446126703
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xlarge.png?1446126703
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/large.png?1446126703
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/medium.png?1446126703
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/small.png?1446126703
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xsmall.png?1446126703
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/001/164/dec3b026b81ee6d890a8f82f75c94a2e/xxsmall.png?1446126703
Instructional Technology
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/113/a875020a9280c7db69e73eb15d3755e4/xxlarge.jpg?1598303574
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/113/a875020a9280c7db69e73eb15d3755e4/xlarge.jpg?1598303574
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/113/a875020a9280c7db69e73eb15d3755e4/large.jpg?1598303574
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/113/a875020a9280c7db69e73eb15d3755e4/medium.jpg?1598303574
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/113/a875020a9280c7db69e73eb15d3755e4/small.jpg?1598303574
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/113/a875020a9280c7db69e73eb15d3755e4/xsmall.jpg?1598303574
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/113/a875020a9280c7db69e73eb15d3755e4/xxsmall.jpg?1598303574
2
0
false
Mon, 24 Aug 2020 17:14:47 -0400
Phishing Email from Fake UMBC IT Desk
Phsihing Attack Sent To Over 1000 UMBC Accounts
A compromised UMBC account was used to send phishing emails to over 1200 other UMBC accounts today. These malicious emails, claiming to be from the “UMBC IT Desk,” contained a link to a fake myUMBC login page, potentially allowing the malicious actors to steal any passwords entered on the site. To prevent further malicious activity, DoIT Security has scrambled the password of the account used to send the emails.
From: <name removed>
Date: Mon, Aug 24, 2020 at 10:40 AM
Subject: COVID-19 Update
To:
This is the UMBC IT Desk. Kindly Update your details to avoid beinglocked out of your email account.
Follow the URLbelow to proceed to setup umbc.edu/cas-web/login/Update
IT DeskUMBC
The link leads to this fake login page:
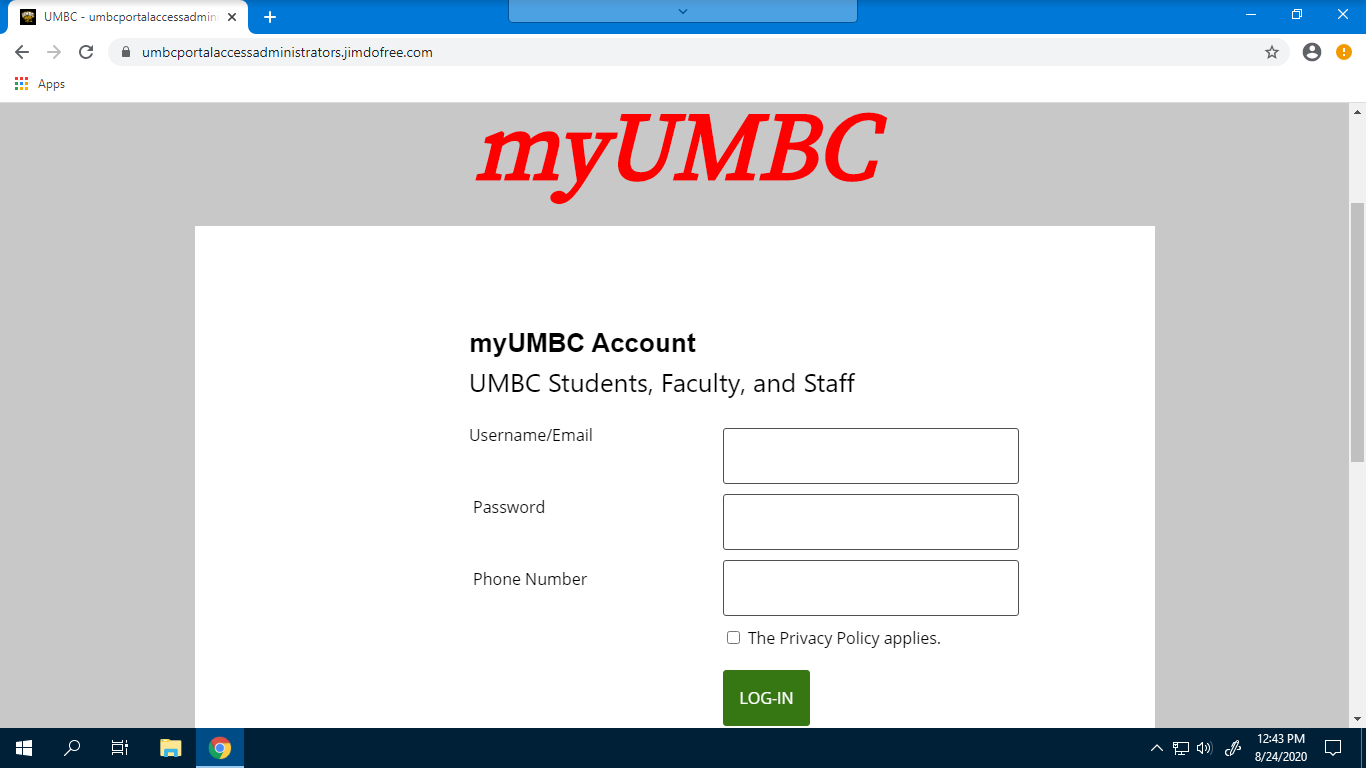
Always check the URL before entering credentials online. Notice that this site is not in the umbc.edu domain, despite claiming to be myUMBC. In addition, you can compare it to the real login page by navigating to myUMBC without using a link to see that it does not match.
As of this writing, approximately 150 people have clicked this link. If you have entered your UMBC password after clicking the link in this phishing email, please change it to something substantively different as soon as possible. Instructions for doing so can be found here:https://wiki.umbc.edu/pages/viewpage.action?pageId=1867939.
If you do receive any email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
]]>
A compromised UMBC account was used to send phishing emails to over 1200 other UMBC accounts today. These malicious emails, claiming to be from the “UMBC IT Desk,” contained a link to a fake...
https://beta.my.umbc.edu/api/v0/pixel/news/95109/guest@my.umbc.edu/76a7aa4617da4d330558aa3e1cf11818/api/pixel
covid19
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777059166
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 16:00:48 -0400
Blackboard Predict to be Sunset
And rolling out a new model that helps students earlier!
Blackboard Predict (BB Predict) is a subscription-based predictive model designed to identify students at risk of receiving a grade of D or F in a course. UMBC has a long partnership with Blackboard and had an active advisory role in the development of this tool. While the product produced was high quality, it has been lightly used (although more recently DoIT has partnered with individual faculty and staff to explore ways to use it as part of our student success efforts and as a complement to our First Year Intervention Alert Program).
Given current usage and financial constraints, we have made the decision to sunset BB Predict and will not renew our subscription.
One factor that limited the usefulness of BB Predict to improve student success through better early alerts is simple. The model’s predictions only become precise enough to use with confidence at the semester's midpoint and are not “early enough.” Recognizing that the earlier at-risk students can be identified with precision, the more time we have to help them and the greater the likelihood of their success, the Data Science Team within DoIT and supported by the Provost’s office constructed our own model, now called UMBC Predict. The team’s goal was to increase the precision of the model’s estimates earlier in the semester, in this case, four weeks from the first day of classes, to allow for greater opportunities for students to seek assistance or change their approach to the class, and for these changes or assistance to have an impact.
UMBC Predict does not attempt to replicate the model and platform of our vendor partner. The strategy employed by the Data Science Team was to focus on fewer courses in the initial stages of the work. In particular, the team focused on courses with elevated DFW rates, large numbers of students, and importantly, courses where instructors make relatively heavy use of our learning management system (Blackboard) to engage students and to record assignments and grades throughout the semester. It has always been true that instructors’ use of the learning management system provides valuable information to students about their progress in the course, but it is also the case that these interactions provide important information that the predictive model can use to sharpen predictions at an earlier point in the semester.
A second important factor underlying our decision to sunset BB Predict is pragmatic and necessary. With the current pandemic and its associated negative effects upon the state budget, reducing our expenditure on a subscription-based model in favor of an internal model with equivalent or better performance for certain courses allows us to maintain our support for students while freeing up resources to support people and programs.
UMBC Predict is already being integrated into department-level enhanced early alert programs on a pilot basis. This term, faculty in the Mathematics and Statistics Department and the Dean’s Office in the College of Mathematical and Natural Sciences plan to partner with DoIT and the Analytics and Business Intelligence Group to use targeted communications to students who may be at risk after four weeks. The communication, delivered over the course instructor’s signature, encourages students to take advantage of their office hours along with other tips developed by the Academic Success Center to improve students’ chances of success both in the course and at UMBC.
]]>
Blackboard Predict (BB Predict) is a subscription-based predictive model designed to identify students at risk of receiving a grade of D or F in a course. UMBC has a long partnership with...
https://doit.umbc.edu/Analytics/
https://beta.my.umbc.edu/api/v0/pixel/news/95096/guest@my.umbc.edu/3c818c79de1545627e54d5378c7cfca9/api/pixel
analytics
Division of Information Technology (DoIT)
https://beta.my.umbc.edu/groups/doit
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/021/d27760c5de12c74b73faec8d0e631acf/xsmall.png?1727453227
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/021/d27760c5de12c74b73faec8d0e631acf/original.JPG?1727453227
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/021/d27760c5de12c74b73faec8d0e631acf/xxlarge.png?1727453227
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/021/d27760c5de12c74b73faec8d0e631acf/xlarge.png?1727453227
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/021/d27760c5de12c74b73faec8d0e631acf/large.png?1727453227
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/021/d27760c5de12c74b73faec8d0e631acf/medium.png?1727453227
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/021/d27760c5de12c74b73faec8d0e631acf/small.png?1727453227
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/021/d27760c5de12c74b73faec8d0e631acf/xsmall.png?1727453227
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/021/d27760c5de12c74b73faec8d0e631acf/xxsmall.png?1727453227
Division of Information Technology (DoIT)
https://assets3-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/096/631da9a10d488745677cc1bf1b321960/xxlarge.jpg?1598291938
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/096/631da9a10d488745677cc1bf1b321960/xlarge.jpg?1598291938
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/096/631da9a10d488745677cc1bf1b321960/large.jpg?1598291938
https://assets2-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/096/631da9a10d488745677cc1bf1b321960/medium.jpg?1598291938
https://assets4-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/096/631da9a10d488745677cc1bf1b321960/small.jpg?1598291938
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/096/631da9a10d488745677cc1bf1b321960/xsmall.jpg?1598291938
https://assets1-beta.my.umbc.edu/system/shared/thumbnails/news/000/095/096/631da9a10d488745677cc1bf1b321960/xxsmall.jpg?1598291938
4
0
true
Mon, 24 Aug 2020 13:59:56 -0400
Account data breach: Zoosk (2020)
Credentials Breach Report
In January 2020, Zoosk 2020, an online dating service, suffered a data breach. This breach contained 24 million users data that was posted online. The user information includes dates of birth, drinking habits, education levels, email addresses, ethnicities, family structure, genders, geographic locations, income levels, names, nicknames, physical attributes, political views, relationship statuses, religions, sexual orientations,and smoking habits. While the passwords posted were not valid for access to UMBC accounts, we suggest you change your UMBC password as a safety precaution.
76 UMBC accounts were victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a Zoosk (2020) account, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach visit: https://haveibeenpwned.com/.
More about Zoosk(2020) data breach:
https://grahamcluley.com/zoosk-hacking/
https://www.justice4you.com/blog/zoosk-data-breach.html#:~:text=According%20to%20the%20notice%2C%20an%20unauthorized%20party%20breached,by%20email%2C%20including%20more%20than%20560%2C000%20California%20residents.
If you have any questions or concerns email us: security@umbc.edu
Information about this breach was provided to us by Have I Been Pwned(HIBP).
_____________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Need to set up a recovery email for your UMBC account?
Follow the instructions here: https://my3.my.umbc.edu/groups/itsecurity/posts/94776
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
In January 2020, Zoosk 2020, an online dating service, suffered a data breach. This breach contained 24 million users data that was posted online. The user information includes dates of birth,...
https://beta.my.umbc.edu/api/v0/pixel/news/95090/guest@my.umbc.edu/e19d02e85d33f6e43f12987559f2f8a4/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777059166
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 13:00:41 -0400
Account data breach: Drizly
Credentials Breach Report
In July 2020, an online alcohol delivery service, Drizly, suffered a data breach. This breach contained 2.5 million customers data that was sold online, and then posted on a hacking forum. The customer information includes names, email addresses, IP addresses, physical addresses, date of birth, phone numbers, and passwords. No financial information was leaked.
106 UMBC accounts were victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a Drizly account, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach visit: https://haveibeenpwned.com/.
More about Drizly data breach:
https://techcrunch.com/2020/07/28/drizly-data-breach/
https://www.forbes.com/sites/katedingwall/2020/07/29/alcohol-e-commerce-giant-drizly-hit-with-huge-data-breach/#63b0d40b5a96
If you have any questions or concerns email us: security@umbc.edu
Information about this breach was provided to us by Have I Been Pwned(HIBP).
_____________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Need to set up a recovery email for your UMBC account?
Follow the instructions here: https://my3.my.umbc.edu/groups/itsecurity/posts/94776
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
In July 2020, an online alcohol delivery service, Drizly, suffered a data breach. This breach contained 2.5 million customers data that was sold online, and then posted on a hacking forum. The...
https://beta.my.umbc.edu/api/v0/pixel/news/95089/guest@my.umbc.edu/89316cd852a70895cf563be575901740/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777059166
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 12:27:41 -0400
Account Data Breach: Havenly
Credentials Breach Report
In June 2020, Havenly, an interior design website, suffered a data breach. Approximately 1.4 million members' personal information was exposed. This data includes names, email, phone numbers, addresses and passwords stored as SHA-1 hashes. This information was shared on an online hacking community.
28 UMBC accounts were affected by this breach. The victims have been notified via their UMBC emails and/or their alternate emails. If you have a Havenly account, please contact them to see if you have been affected by this breach.
More about Heavenly data breach:
https://www.bleepingcomputer.com/news/security/hacker-leaks-386-million-user-records-from-18-companies-for-free/
If you have any questions or concerns email us: security@umbc.edu
Information about this breach was provided to us by Have I Been Pwned(HIBP).
_____________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Need to set up a recovery email for your UMBC account?
Follow the instructions here: https://my3.my.umbc.edu/groups/itsecurity/posts/94776
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
In June 2020, Havenly, an interior design website, suffered a data breach. Approximately 1.4 million members' personal information was exposed. This data includes names, email, phone numbers,...
https://beta.my.umbc.edu/api/v0/pixel/news/95088/guest@my.umbc.edu/37cde20daa1e1e214e861b07e9f048a8/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777059166
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 12:25:16 -0400
Account Data Breach: Promo
Credentials Breach Report
In June 2020, a marketing video creator website, Promo, suffered a data breach. 22 million users' personal information was leaked on an online hacking forum. This data includes names, email, gender, IP addresses and passwords stored as SHA-256 hashes. This information was shared on an online hacking community.
34 UMBC accounts were affected by this breach. The victims have been notified via their UMBC emails and/or their alternate emails. If you have a Promo account, please contact them to see if you have been affected by this breach. Also visit https://haveibeenpwned.com/ to see if you were involved in any other breach.
More about Promo data breach:
https://support.promo.com/en/articles/4276475-promo-data-breach-faq
https://www.bleepingcomputer.com/news/security/promocom-discloses-data-breach-after-22m-user-records-leaked-online/#:~:text=Promo.com%2C%20an%20Israeli-based%20marketing%20video%20creation%20site%2C%20has,networks%20such%20as%20Facebook%2C%20Instagram%2C%20Twitter%2C%20and%20LinkedIn.
If you have any questions or concerns email us: security@umbc.edu
Information about this breach was provided to us by Have I Been Pwned(HIBP).
_____________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Need to set up a recovery email for your UMBC account?
Follow the instructions here: https://my3.my.umbc.edu/groups/itsecurity/posts/94776
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
In June 2020, a marketing video creator website, Promo, suffered a data breach. 22 million users' personal information was leaked on an online hacking forum. This data includes names, email,...
https://beta.my.umbc.edu/api/v0/pixel/news/95087/guest@my.umbc.edu/9b440e99fda3d256ddc3796c3a64a556/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777059166
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 12:24:27 -0400
Mon, 24 Aug 2020 12:25:39 -0400
Account Data breach: ProctorU
Credentials Breach Report
In June 2020, ProctorU, an online examination service, suffered a data breach. Over 444K user records were exposed and posted to an online hacking community. These records contain names, emails, physical addresses, phone numbers and passwords.
36UMBC accounts were affected by this breach. The victims have been notified via their UMBC emails and/or their alternate emails. If you have a ProctorU account, please contact them to see if you have been affected by this breach. To see if you were involved in any other breach visit: https://haveibeenpwned.com/.
More about ProctorU data breach:
https://www.smh.com.au/national/hackers-hit-university-online-exam-tool-20200806-p55j6h.html
https://www.bleepingcomputer.com/news/security/proctoru-confirms-data-breach-after-database-leaked-online/
If you have any questions or concerns email us: security@umbc.edu
Information about this breach was provided to us by Have I Been Pwned(HIBP).
_____________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. Instructions for doing so can be found at the UMBC support wiki: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Need to set up a recovery email for your UMBC account?
Follow the instructions here: https://my3.my.umbc.edu/groups/itsecurity/posts/94776
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity
]]>
In June 2020, ProctorU, an online examination service, suffered a data breach. Over 444K user records were exposed and posted to an online hacking community. These records contain names, emails,...
https://beta.my.umbc.edu/api/v0/pixel/news/95086/guest@my.umbc.edu/00f49b7a650a2111ae6eca31a0576d38/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777059166
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 12:21:59 -0400
Mon, 24 Aug 2020 12:26:02 -0400
Microsoft SharePoint Phishing Scam
A Scam Targeting Microsoft SharePoint Users
Malicious actors are using Covid-19 and current economic conditions to exploit victims with new phishing scams. The article linked below talks about two similar phishing scams. One scam claims to be giving the user a bonus while mimicking a Microsoft SharePoint notification. The other attempts to spoof a Microsoft Planner email notification. Both scams are trying to steal the user’s Microsoft login credentials.
“Summer Bonus” Phishing Scam
The scammer sends an email that looks like a legitimate Microsoft SharePoint notification. The email offers what looks like a bonus for the month while also having an “open” button to display an explanatory file. An example of this email is shown below.
If the victim clicks on the “open” button they will be brought to a website that looks very similar to a Microsoft login page. A closer look reveals that this is not a link to a Microsoft login page but to an AppSpot site created by the scammers. Appspot.com is a cloud computing platform for developing and hosting web applications in Google-managed data centers.
If the victim enters their login credentials into the fake Microsoft login page, their account would be compromised.
Microsoft Planner Phishing Scam
Similar to the “Summer Bonus” scam, this Microsoft Planner Phishing Scam uses an email that tries to spoof a Microsoft Planner notification. As in the “Summer Bonus” scam, it has a button but this one says “Open in Microsoft Planner” and will take you to a fake Microsoft login page. An example of this email is shown below.
As with the previous scam, if the victim enters their login credentials into the fake Microsoft login page, their account would be compromised.
To avoid these scams, make sure the site you land on after clicking the button is really a Microsoft domain. If the site is a login for Microsoft then the URL should direct your browser to a legitimate Microsoft domain.
Even before clicking any buttons, look at the From address in the headers. The scammer’s display name makes it appear as if it belongs to the targeted company. The headers can show if the From email address itself is spoofed and who is actually sending the email to you.
Always remember that if it feels “too good to be true”, then it is probably too good to be true. It is also good practice to check with a supervisor before responding to any unsolicited requests for credentials or logins that appear to come from your employer.
If you do receive any email that you suspect is a scam, please do not click on any URL or reply. Either of those actions confirms to the sender that your email address is valid. Please forward the message (with the email headers) to security@umbc.edu.
How do I forward full email headers?
https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970
The images and the original article can be found here. Please check it out for more information:
https://www.area1security.com/blog/july-bonus-microsoft-spear-phishing/?utm_medium=email&utm_source=blast&utm_term=na&utm_content=na&utm_campaign=2020-Q3-Email-Blast-Spot-Campaign&mkt_tok=eyJpIjoiWVdKbE1HVXlOakkzWVRWaiIsInQiOiJFWnFFZVYxYXBuTFpcLytrc1hzNkFodUZ1XC9CbWRPcUROYmhMWlM0NisyZmo3K0cybFFyY0xmMnhYXC9lYUIzMit2UXZGYzFPTURmTSt2Z1cxRDkxOTladFUwVGl5Wmczd2FmZWFvSkRZZm9iN0FVZGh0TGs2b2FlazhaSFU0ZWhzbSJ9
To read more articles published by DoIT visit:
https://itsecurity.umbc.edu/critical/?tag=notice.
https://itsecurity.umbc.edu/home/covid-19-news/?tag=covid19
]]>
Malicious actors are using Covid-19 and current economic conditions to exploit victims with new phishing scams. The article linked below talks about two similar phishing scams. One scam claims to...
https://beta.my.umbc.edu/api/v0/pixel/news/95085/guest@my.umbc.edu/b71f97a748a34795397c539c4c6983f8/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://beta.my.umbc.edu/groups/itsecurity
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/original.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xxlarge.png?1777059166
https://assets3-beta.my.umbc.edu/images/avatars/group/7/xlarge.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/large.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/medium.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/small.png?1777059166
https://assets4-beta.my.umbc.edu/images/avatars/group/7/xsmall.png?1777059166
https://assets2-beta.my.umbc.edu/images/avatars/group/7/xxsmall.png?1777059166
IT Security - DoIT
0
0
true
Mon, 24 Aug 2020 12:20:48 -0400
Mon, 24 Aug 2020 12:26:24 -0400