talk: More holes than cheese: Vulnerabilities of the e-voting system used in the 2022 French presidential election
 The Neovote e-voting system was used for three of the five primaries in the French 2022 presidential election
The Neovote e-voting system was used for three of the five primaries in the French 2022 presidential electionThe UMBC Cyber Defense Lab presents
More holes than cheese:
Vulnerabilities of the e-voting system
used in the 2022 French presidential election
CNRS, Laboratory of Industrial and Human Automation, Mechanics and Computer Science, Université Polytechnique Hauts-de-France, and CNRS Center for Internet and Society
12–1 pm ET Friday, 13 May 2022 via WebEx
(joint work with Antoine Gallais, Emmanuel Leblond, Djohar Sidhoum-Rahal, and Juliette Walter)
This talk will present the first security and privacy analysis of the Neovote e-voting system, which was used for three of the five primaries in the French 2022 presidential election. Based on information gathered by a whistle-blower (now a member of the team) and analyses made by our team during the last online vote in January 2022, I will show that the demands of transparency, verifiability, and security set by French governmental organizations were not met. I will then propose multiple attacks against the system targeting both the breach of voters’ privacy and the manipulation of the tally. I will also show how inconsistencies in the verification system allow the publication of erroneous tallies and document how this arrived in practice during one of the primary elections. Finally, I will discuss the complex institutional and legal frameworks as well as the social considerations that allow systems like this one to flourish.
Dr. Enka Blanchard is a transdisciplinary permanent researcher working for the French National Centre for Scientific Research. A significant fraction of their work concerns the social and psychological aspects of security, especially when it comes to voting systems, on which they frequently collaborate with Ted Selker and Alan Sherman of UMBC. Prior to this, they were a post-doctoral fellow in the Digitrust Project of the University of Lorraine. Their research and contact information is available on their website: koliaza.com
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1 pm. All meetings are open to the public. CDL meetings will resume in fall 2022.
The post talk: More holes than cheese: Vulnerabilities of the e-voting system used in the 2022 French presidential election appeared first on Department of Computer Science and Electrical Engineering.
]]>
The Neovote e-voting system was used for three of the five primaries in the French 2022 presidential election The UMBC Cyber Defense Lab presents More holes than cheese: Vulnerabilities of the...
https://www.csee.umbc.edu/2022/05/talk-more-holes-than-cheese-vulnerabilities-of-the-e-voting-system-used-in-the-2022-french-presidential-election/
https://beta.my.umbc.edu/api/v0/pixel/news/119318/guest@my.umbc.edu/d22e070605c2fe2a0a7aa029ab1cf78c/api/pixel
cybersecurity
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Mon, 09 May 2022 21:12:33 -0400
Mon, 09 May 2022 21:12:33 -0400
talk: More holes than cheese: Vulnerabilities of the e-voting system used in the 2022 French presidential election
 The Neovote e-voting system was used for three of the five primaries in the French 2022 presidential election
The Neovote e-voting system was used for three of the five primaries in the French 2022 presidential electionThe UMBC Cyber Defense Lab presents
More holes than cheese:
Vulnerabilities of the e-voting system
used in the 2022 French presidential election
CNRS, Laboratory of Industrial and Human Automation, Mechanics and Computer Science, Université Polytechnique Hauts-de-France, and CNRS Center for Internet and Society
12–1 pm ET Friday, 13 May 2022 via WebEx
(joint work with Antoine Gallais, Emmanuel Leblond, Djohar Sidhoum-Rahal, and Juliette Walter)
This talk will present the first security and privacy analysis of the Neovote e-voting system, which was used for three of the five primaries in the French 2022 presidential election. Based on information gathered by a whistle-blower (now a member of the team) and analyses made by our team during the last online vote in January 2022, I will show that the demands of transparency, verifiability, and security set by French governmental organizations were not met. I will then propose multiple attacks against the system targeting both the breach of voters’ privacy and the manipulation of the tally. I will also show how inconsistencies in the verification system allow the publication of erroneous tallies and document how this arrived in practice during one of the primary elections. Finally, I will discuss the complex institutional and legal frameworks as well as the social considerations that allow systems like this one to flourish.
Dr. Enka Blanchard is a transdisciplinary permanent researcher working for the French National Centre for Scientific Research. A significant fraction of their work concerns the social and psychological aspects of security, especially when it comes to voting systems, on which they frequently collaborate with Ted Selker and Alan Sherman of UMBC. Prior to this, they were a post-doctoral fellow in the Digitrust Project of the University of Lorraine. Their research and contact information is available on their website: koliaza.com
Host: Alan T. Sherman, sherman@umbc.edu. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1 pm. All meetings are open to the public. CDL meetings will resume in fall 2022.
The post talk: More holes than cheese: Vulnerabilities of the e-voting system used in the 2022 French presidential election appeared first on Department of Computer Science and Electrical Engineering.
]]>
The Neovote e-voting system was used for three of the five primaries in the French 2022 presidential election The UMBC Cyber Defense Lab presents More holes than cheese: Vulnerabilities of the...
https://redirect.cs.umbc.edu/2022/05/talk-more-holes-than-cheese-vulnerabilities-of-the-e-voting-system-used-in-the-2022-french-presidential-election/
https://beta.my.umbc.edu/api/v0/pixel/news/129850/guest@my.umbc.edu/d257b8507ff3e35c560c263743befc73/api/pixel
cybersecurity
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Mon, 09 May 2022 21:12:33 -0400
Mon, 09 May 2022 21:12:33 -0400
talk: Model Validation for DARPA DPRIVE
The UMBC Cyber Defense Lab presents
Model Validation for DARPA DPRIVE
Ian Blumenfeld
UMBC and Two Six Technologies
(joint work with Eric Bond, William Harrison, Chris Hathhorn, Paul Li, Matthew Torrence, and Jared Ziegler)
12–1 pm ET, Friday 6 May 2022, via WebEx
Commodity hardware description languages (HDLs) like VHDL and Verilog present a challenge from a high assurance point of view because they lack formalized semantics: when a team of hardware engineers produces a circuit design in a commodity HDL and claims that it correctly implements a pseudocode algorithm, on what basis can that claim be evaluated? A formalized model of the circuit design may be painstakingly created (e.g., in the logic of a theorem prover), but how are the accuracy and faithfulness of that model then established? The distance between the widely adopted commodity HDLs and formal models of hardware has been a well-recognized and persistent impediment to driving formal methods into hardware development.
This talk presents a technique developed at Two Six Technologies, called model validation, that formally connects hardware design and its formal model via a functional, high-level synthesis language called ReWire. Model validation introduces a “model” program to bridge the gap between the hardware design and algorithm by establishing 1) the equivalence of the algorithm to the model and 2) the equivalence of the model to the circuit design. Equivalence between the algorithm and the ReWire model is verified with a ReWire semantics formalized in Isabelle. Equivalence between the ReWire model and the circuit design is established by producing binary circuits from each (using commodity synthesis tools and the ReWire compiler rwc) and then applying an automated binary equivalence checker.
This talk describes our experience applying model validation as part of the DARPA Data Protection in Virtual Environments (DPRIVE) program. DPRIVE aims to develop a novel hardware accelerator to ease computational challenges preventing widespread use of fully homomorphic encryption (FHE) that began with Gentry’s discovery and was improved upon in the PROCEED program. To this end, DPRIVE’s purpose is to design hardware accelerators to improve upon the existing algorithmic gains to FHE. Model validation through ReWire moves formal methods into the practical world, empowering hardware designers to reason about the correctness, safety, and security properties of their designs. In addition, we expect our pipeline to protect hardware supply chains by allowing for a full formal analysis of RTL implementations before tape out.
Ian Blumenfeld is the Research Director for Mathematics at Two Six Technologies. In that role, he is a principal investigator on multiple DARPA programs, spanning the areas of formal methods, modern cryptography, and applied category theory. Prior to his work at Two Six, Ian was a formal verification engineer at Apple, where he verified cryptographic properties of the iPhone secure enclave processor. Ian has worked in roles in and around the federal research space for more than a decade, including five years as an applied research mathematician at the National Security Agency. Ian is currently enrolled as a part-time Ph.D. student in the UMBC computer science department, working with Dr. Alan Sherman and Dr. Don Engel. Email: itblumenfeld@umbc.edu
Host: Alan T. Sherman, sherman@umbc.edu. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public. Upcoming CDL Meeting: May 13, Enka Blanchard (Digitrust Loria, France)
The post talk: Model Validation for DARPA DPRIVE appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Model Validation for DARPA DPRIVE Ian Blumenfeld UMBC and Two Six Technologies (joint work with Eric Bond, William Harrison, Chris Hathhorn, Paul Li, Matthew...
https://redirect.cs.umbc.edu/2022/04/talk-model-validation-for-darpa-dprive/
https://beta.my.umbc.edu/api/v0/pixel/news/129852/guest@my.umbc.edu/7704c7d104dc778066f2ef8af899762e/api/pixel
computer-engineering
computer-science
cybersecurity
events
research
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Thu, 28 Apr 2022 09:57:22 -0400
Thu, 28 Apr 2022 09:57:22 -0400
talk: Model Validation for DARPA DPRIVE

The UMBC Cyber Defense Lab presents
Model Validation for DARPA DPRIVE
Ian Blumenfeld
UMBC and Two Six Technologies
(joint work with Eric Bond, William Harrison, Chris Hathhorn, Paul Li, Matthew Torrence, and Jared Ziegler)
12–1 pm ET, Friday 6 May 2022, via WebEx
Commodity hardware description languages (HDLs) like VHDL and Verilog present a challenge from a high assurance point of view because they lack formalized semantics: when a team of hardware engineers produces a circuit design in a commodity HDL and claims that it correctly implements a pseudocode algorithm, on what basis can that claim be evaluated? A formalized model of the circuit design may be painstakingly created (e.g., in the logic of a theorem prover), but how are the accuracy and faithfulness of that model then established? The distance between the widely adopted commodity HDLs and formal models of hardware has been a well-recognized and persistent impediment to driving formal methods into hardware development.
This talk presents a technique developed at Two Six Technologies, called model validation, that formally connects hardware design and its formal model via a functional, high-level synthesis language called ReWire. Model validation introduces a “model” program to bridge the gap between the hardware design and algorithm by establishing 1) the equivalence of the algorithm to the model and 2) the equivalence of the model to the circuit design. Equivalence between the algorithm and the ReWire model is verified with a ReWire semantics formalized in Isabelle. Equivalence between the ReWire model and the circuit design is established by producing binary circuits from each (using commodity synthesis tools and the ReWire compiler rwc) and then applying an automated binary equivalence checker.
This talk describes our experience applying model validation as part of the DARPA Data Protection in Virtual Environments (DPRIVE) program. DPRIVE aims to develop a novel hardware accelerator to ease computational challenges preventing widespread use of fully homomorphic encryption (FHE) that began with Gentry’s discovery and was improved upon in the PROCEED program. To this end, DPRIVE’s purpose is to design hardware accelerators to improve upon the existing algorithmic gains to FHE. Model validation through ReWire moves formal methods into the practical world, empowering hardware designers to reason about the correctness, safety, and security properties of their designs. In addition, we expect our pipeline to protect hardware supply chains by allowing for a full formal analysis of RTL implementations before tape out.
Ian Blumenfeld is the Research Director for Mathematics at Two Six Technologies. In that role, he is a principal investigator on multiple DARPA programs, spanning the areas of formal methods, modern cryptography, and applied category theory. Prior to his work at Two Six, Ian was a formal verification engineer at Apple, where he verified cryptographic properties of the iPhone secure enclave processor. Ian has worked in roles in and around the federal research space for more than a decade, including five years as an applied research mathematician at the National Security Agency. Ian is currently enrolled as a part-time Ph.D. student in the UMBC computer science department, working with Dr. Alan Sherman and Dr. Don Engel. Email: *protected email*
Host: Alan T. Sherman, *protected email*. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public. Upcoming CDL Meeting: May 13, Enka Blanchard (Digitrust Loria, France)
The post talk: Model Validation for DARPA DPRIVE appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Model Validation for DARPA DPRIVE Ian Blumenfeld UMBC and Two Six Technologies (joint work with Eric Bond, William Harrison, Chris Hathhorn, Paul Li, Matthew...
https://www.csee.umbc.edu/2022/04/talk-model-validation-for-darpa-dprive/
https://beta.my.umbc.edu/api/v0/pixel/news/118993/guest@my.umbc.edu/a7bd1c976eabecaca996cf3cbe7c7efc/api/pixel
computer-engineering
computer-science
cybersecurity
events
research
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Thu, 28 Apr 2022 09:57:22 -0400
Thu, 28 Apr 2022 09:57:22 -0400
talk: Designing Quantum Resistant KeyExchange Protocols with CPSA, 12-1 Fri 4/15, online

With developments in quantum computers and algorithms, quantum-resistant key exchange protocols are needed to replace our existing vulnerable protocols
The UMBC Cyber Defense Lab presents
Designing Quantum Resistant Key
Exchange Protocols with CPSA
Dr. Edward Zieglar, CSEE, UMBC
12–1 pm, Friday, 15 April 2022
online via WebEx
With developments in quantum computers and algorithms, the public-key systems that we rely upon for secure network communication will become vulnerable to exploitation. Quantum-resistant key exchange protocols are needed to replace our existing vulnerable protocols. Much of the work has focused on developing new mathematical problems that are conjectured to be quantum-resistant as replacements for our current public-key algorithms. We took a different approach, looking to an old secret-key agreement protocol developed by Leighton and Micali at MIT for the Clipper Chip symmetric encryption system. We will present our analysis of the Leighton-Micali key agreement protocol, weaknesses we uncovered with the Cryptographic Protocol Shapes Analyzer (CPSA), and verification of a new protocol based on their ideas that corrects deficiencies in the original protocol.
Dr. Zieglar is an expert in protocol analysis and computer security at the National Security Agency. He is an adjunct faculty member at UMBC and a member of the UMBC Protocol Analysis Lab. Dr. Zieglar earned his Ph.D. in computer science from UMBC working under Dr. Sidhu. Email: eziegl1@umbc.edu
Host: Alan T. Sherman, sherman@umbc.edu. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1 pm. All meetings are open to the public. Upcoming CDL Meetings: April 29, Ian Blumenfeld (UMBC), May 13, Enka Blanchard (Digitrust Loria, France).
The post talk: Designing Quantum Resistant KeyExchange Protocols with CPSA, 12-1 Fri 4/15, online appeared first on Department of Computer Science and Electrical Engineering.
]]>
With developments in quantum computers and algorithms, quantum-resistant key exchange protocols are needed to replace our existing vulnerable protocols The UMBC Cyber Defense Lab presents...
https://redirect.cs.umbc.edu/2022/04/talk-designing-quantum-resistant-keyexchange-protocols-with-cpsa-12-1-fri-4-15-online/
https://beta.my.umbc.edu/api/v0/pixel/news/129855/guest@my.umbc.edu/74b27f1cfa2abf4a1e3e49e7f47ece4e/api/pixel
cybersecurity
events
quantum-computing
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Mon, 11 Apr 2022 15:30:28 -0400
Mon, 11 Apr 2022 15:30:28 -0400
talk: Designing Quantum Resistant KeyExchange Protocols with CPSA, 12-1 Fri 4/15, online

With developments in quantum computers and algorithms, quantum-resistant key exchange protocols are needed to replace our existing vulnerable protocols
The UMBC Cyber Defense Lab presents
Designing Quantum Resistant Key
Exchange Protocols with CPSA
Dr. Edward Zieglar, CSEE, UMBC
12–1 pm, Friday, 15 April 2022
online via WebEx
With developments in quantum computers and algorithms, the public-key systems that we rely upon for secure network communication will become vulnerable to exploitation. Quantum-resistant key exchange protocols are needed to replace our existing vulnerable protocols. Much of the work has focused on developing new mathematical problems that are conjectured to be quantum-resistant as replacements for our current public-key algorithms. We took a different approach, looking to an old secret-key agreement protocol developed by Leighton and Micali at MIT for the Clipper Chip symmetric encryption system. We will present our analysis of the Leighton-Micali key agreement protocol, weaknesses we uncovered with the Cryptographic Protocol Shapes Analyzer (CPSA), and verification of a new protocol based on their ideas that corrects deficiencies in the original protocol.
Dr. Zieglar is an expert in protocol analysis and computer security at the National Security Agency. He is an adjunct faculty member at UMBC and a member of the UMBC Protocol Analysis Lab. Dr. Zieglar earned his Ph.D. in computer science from UMBC working under Dr. Sidhu. Email: *protected email*
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1 pm. All meetings are open to the public. Upcoming CDL Meetings: April 29, Ian Blumenfeld (UMBC), May 13, Enka Blanchard (Digitrust Loria, France).
The post talk: Designing Quantum Resistant KeyExchange Protocols with CPSA, 12-1 Fri 4/15, online appeared first on Department of Computer Science and Electrical Engineering.
]]>
With developments in quantum computers and algorithms, quantum-resistant key exchange protocols are needed to replace our existing vulnerable protocols The UMBC Cyber Defense Lab presents...
https://www.csee.umbc.edu/2022/04/talk-designing-quantum-resistant-keyexchange-protocols-with-cpsa-12-1-fri-4-15-online/
https://beta.my.umbc.edu/api/v0/pixel/news/118396/guest@my.umbc.edu/9d16aa9a4995c46bfa5cf72d425c0ffb/api/pixel
cybersecurity
events
quantum-computing
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Mon, 11 Apr 2022 15:30:28 -0400
Mon, 11 Apr 2022 15:30:28 -0400
talk: Formal Methods Analysis of the Session Binding Proxy Protocol, 12-1 Fri 4/1
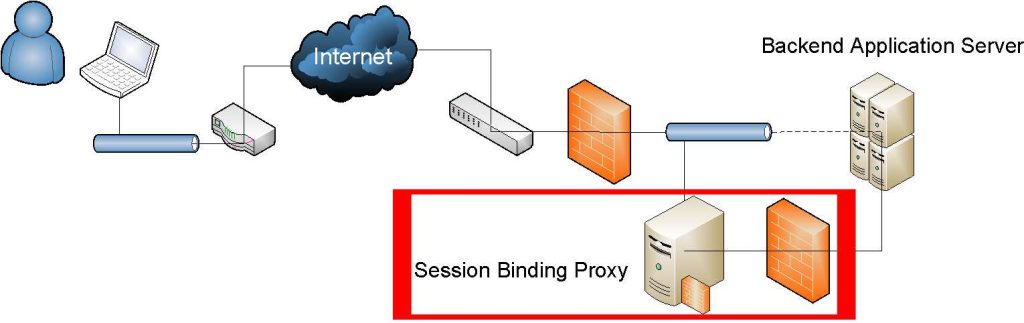
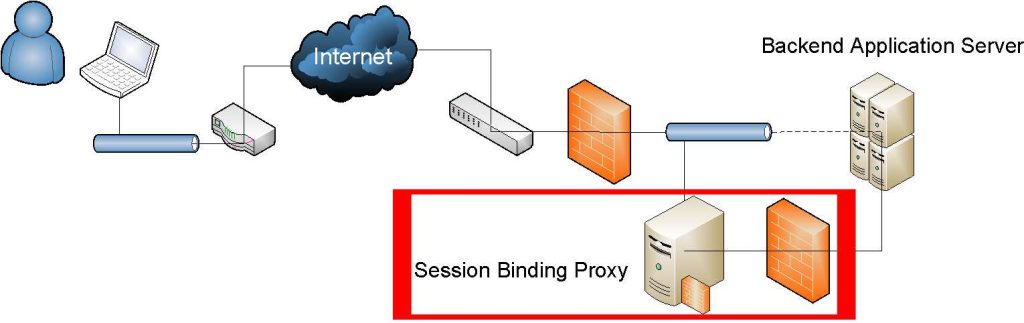
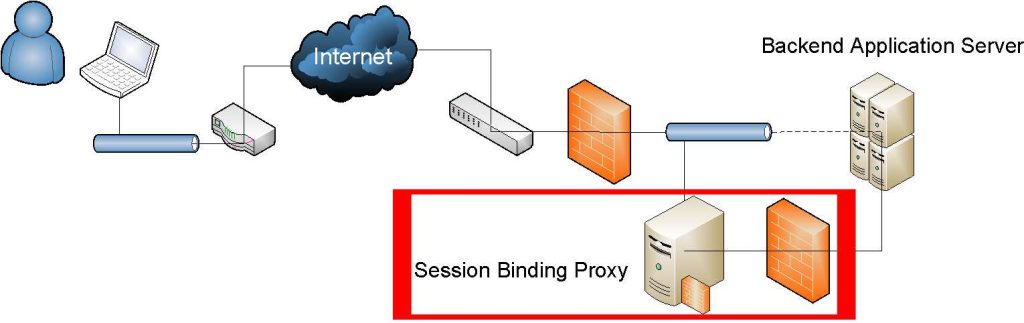
Session Binding Proxy protocol aims to prevent session hijacking by binding the application session to the underlying network session
The UMBC Cyber Defense Lab presents
A Formal Methods Analysis of the Session Binding Proxy Protocol
Kirellos N. Abou Elsaad, UMBC
12-1 pm, Friday, 1 April 2022, via WebEx
Proposed by Burgers, Verdult, and Eekelen in 2013, the Session Binding Proxy (SBP) protocol intends to prevent session hijacking by binding the application session to the underlying network session (i.e., binding the session token to the SSL/TLS shared key). We present a formal methods analysis of SBP using the Cryptographic Protocol Shapes Analyzer (CPSA). Our analysis reveals that SBP relies critically on the successful establishment of a secure SSL/TLS channel, which can be undermined using well-known attacks. Also, we find that SBP allows for the partial hijacking of a session using a tailgating attack. In this attack, the adversary uses the server to inject and execute malicious code inside the client’s browser to extract the session token and forge a valid state-changing request to the server. This attack is not neutralized by SBP because the request contains a valid session token and is sent over the client’s existing SSL/TLS channel.
Kirellos N. Abou Elsaad is a master’s student in computer science at UMBC working under Dr. Sherman and a member of the Protocol Analysis Lab (PAL). email: abou3@umbc.edu
Host: Alan T. Sherman, sherman@umbc.edu. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1 pm. All meetings are open to the public. Upcoming CDL Meetings: April 15, Edward Zieglar (NSA); April 29, Ian Blumenfeld (UMBC); May 13, Enka Blanchard (Digitrust Loria, France).
The post talk: Formal Methods Analysis of the Session Binding Proxy Protocol, 12-1 Fri 4/1 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Session Binding Proxy protocol aims to prevent session hijacking by binding the application session to the underlying network session The UMBC Cyber Defense Lab presents A Formal Methods...
https://redirect.cs.umbc.edu/2022/03/talk-formal-methods-analysis-of-the-session-binding-proxy-protocol-12-1-fri-4-1/
https://beta.my.umbc.edu/api/v0/pixel/news/129856/guest@my.umbc.edu/b130e6dfb565f94a7272a64c5f0ad7d5/api/pixel
computer-science
cybersecurity
events
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Sun, 27 Mar 2022 22:09:22 -0400
Sun, 27 Mar 2022 22:09:22 -0400
talk: Formal Methods Analysis of the Session Binding Proxy Protocol, 12-1 Fri 4/1
Session Binding Proxy protocol aims to prevent session hijacking by binding the application session to the underlying network session
The UMBC Cyber Defense Lab presents
A Formal Methods Analysis of the Session Binding Proxy Protocol
Kirellos N. Abou Elsaad, UMBC
12-1 pm, Friday, 1 April 2022, via WebEx
Proposed by Burgers, Verdult, and Eekelen in 2013, the Session Binding Proxy (SBP) protocol intends to prevent session hijacking by binding the application session to the underlying network session (i.e., binding the session token to the SSL/TLS shared key). We present a formal methods analysis of SBP using the Cryptographic Protocol Shapes Analyzer (CPSA). Our analysis reveals that SBP relies critically on the successful establishment of a secure SSL/TLS channel, which can be undermined using well-known attacks. Also, we find that SBP allows for the partial hijacking of a session using a tailgating attack. In this attack, the adversary uses the server to inject and execute malicious code inside the client’s browser to extract the session token and forge a valid state-changing request to the server. This attack is not neutralized by SBP because the request contains a valid session token and is sent over the client’s existing SSL/TLS channel.
Kirellos N. Abou Elsaad is a master’s student in computer science at UMBC working under Dr. Sherman and a member of the Protocol Analysis Lab (PAL). email: *protected email*
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1 pm. All meetings are open to the public. Upcoming CDL Meetings: April 15, Edward Zieglar (NSA); April 29, Ian Blumenfeld (UMBC); May 13, Enka Blanchard (Digitrust Loria, France).
The post talk: Formal Methods Analysis of the Session Binding Proxy Protocol, 12-1 Fri 4/1 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Session Binding Proxy protocol aims to prevent session hijacking by binding the application session to the underlying network session The UMBC Cyber Defense Lab presents A Formal Methods...
https://www.csee.umbc.edu/2022/03/talk-formal-methods-analysis-of-the-session-binding-proxy-protocol-12-1-fri-4-1/
https://beta.my.umbc.edu/api/v0/pixel/news/117941/guest@my.umbc.edu/861b4e6a10082187cd2eab14589cd84e/api/pixel
computer-science
cybersecurity
events
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sun, 27 Mar 2022 22:09:22 -0400
Sun, 27 Mar 2022 22:09:22 -0400
talk: CyMOT Cybersecurity Training for Operational Technology in Manufacturing, 12-1 Fri 3/18

The UMBC Cyber Defense Lab presents
CyMOT: Cybersecurity Training for
Operational Technology in Manufacturing
Nilanjan Banerjee, UMBC CSEE
12-1 pm Friday, 18 March 2022, via WebEx
The University of Maryland, Baltimore County (UMBC) and MxD Learn, the workforce arm of MxD, seeks to collaboratively build Phase I of CyMOT to address the need for cybersecurity for operational manufacturing technology (OT). Leveraging MxD Learn’s previous work identifying the skills and abilities needed in future manufacturing positions and the development and dissemination of training opportunities and career pathways, MxD Learn has partnered with UMBC, a leader in cybersecurity education, to create a curriculum that targets adult learners who are looking to increase their skills at the intersection of cybersecurity and manufacturing. The objective of the curriculum program is to provide current workers with learning opportunities that result in certification(s), giving them the tools necessary to execute careers in cybersecurity in manufacturing, and increasing the security of U.S. manufacturers from cyber attacks. This talk will describe the CyMOT Phase I pilot.
Dr. Nilanjan Banerjee is a professor of CSEE at UMBC. His area of expertise is in cybersecurity in manufacturing and physiological sensing.
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1 pm. All meetings are open to the public. Upcoming CDL Meetings: April 1, Kirellos Elsaad (UMBC); April 15, Edward Zieglar (NSA); April 29, Ian Blumenfeld (UMBC); May 13, Enka Blanchard (Digitrust Loria, France).
The post talk: CyMOT Cybersecurity Training for Operational Technology in Manufacturing, 12-1 Fri 3/18 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents CyMOT: Cybersecurity Training for Operational Technology in Manufacturing Nilanjan Banerjee, UMBC CSEE 12-1 pm Friday, 18 March 2022, via WebEx The...
https://www.csee.umbc.edu/2022/03/talk-cymot-cybersecurity-training-for-operational-technology-in-manufacturing-12-1-fri-3-18/
https://beta.my.umbc.edu/api/v0/pixel/news/117738/guest@my.umbc.edu/131dff771a479f4611509c8f1f94caa6/api/pixel
cybersecurity
events
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Tue, 15 Mar 2022 12:10:20 -0400
Tue, 15 Mar 2022 12:10:20 -0400
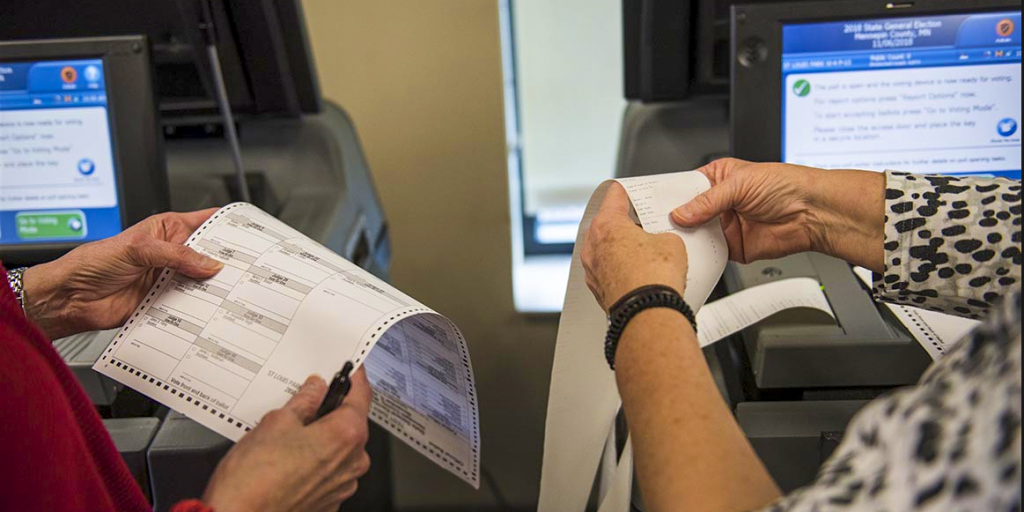
talk: Ted Selker on Voting Technology, 12-1, Fri 3/4
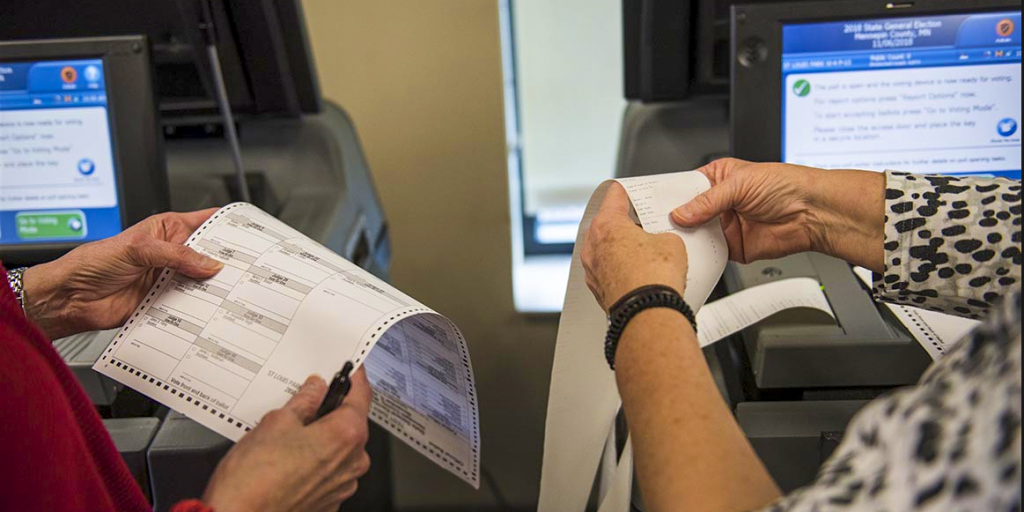
The UMBC Cyber Defense Lab presents
Voting Technology
Ted Selker
Research Professor
UMBC CSEE Department
12–1 ET Friday, 4 March 2022 via WebEx
Traditionally most votes are lost in registration, voting ballot design problems, and polling place operations, causing long lines and possibly mail-in ballot fraud. This talk will describe voting-process problems and technological problems, and some possible solutions for voting improvement. Voting disenfranchisement is much higher for people with perceptual, physical, and cognitive disabilities. More than 14% of registered voters are in danger of increased errors due to dyslexia, and more than 6.5% due to short-term memory problems. We will describe and demonstrate technologies we are making that help disabled people and improve voting universally as well.
Dr. Ted Selker is an entrepreneur inventor who also mentors innovation. Ted spent five years as director of Considerate Systems research at Carnegie Mellon University Silicon Valley and in developing the campus’s research mission. Prior to that, Ted spent ten years as an associate professor at the MIT Media Laboratory, where he created the Context Aware Computing group, co-directed the Caltech/MIT Voting Technology Project, and directed the Industrial Design Intelligence future for product design project. Prior to that, his successes at targeted product creation and enhancement at IBM earned him the role of IBM Fellow. Ted’s work birthed successful products ranging from notebook computers to operating systems. It accumulated numerous awards, patents, and papers and has often been featured in the press. Ted is co-recipient of the Computer Science Policy Leader Award for Scientific American 50, the American Association for People with Disabilities Thomas Paine Award for his work on voting technology, and the Telluride Tech Fest Award.
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public. Upcoming CDL Meetings: March 18, Nilanjan Banerjee (UMBC); April 1, Kirellos Elsaad (UMBC); April 15, Edward Zieglar (NSA); April 29, Ian Blumenfeld (UMBC); May 13, Enka Blanchard (Digitrust Loria, France)
The post talk: Ted Selker on Voting Technology, 12-1, Fri 3/4 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Voting Technology Ted Selker Research Professor UMBC CSEE Department 12–1 ET Friday, 4 March 2022 via WebEx Traditionally most votes are lost in...
https://www.csee.umbc.edu/2022/03/talk-ted-selker-on-voting-technology-12-1-fri-3-4/
https://beta.my.umbc.edu/api/v0/pixel/news/117336/guest@my.umbc.edu/fb281d4e792d98468bd4ac5c35399e68/api/pixel
cybersecurity
events
research
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Tue, 01 Mar 2022 12:47:04 -0500
Tue, 01 Mar 2022 12:47:04 -0500
 The Neovote e-voting system was used for three of the five primaries in the French 2022 presidential election
The Neovote e-voting system was used for three of the five primaries in the French 2022 presidential election