Cybersecurity CTF competition starts 1pm Friday 4/29
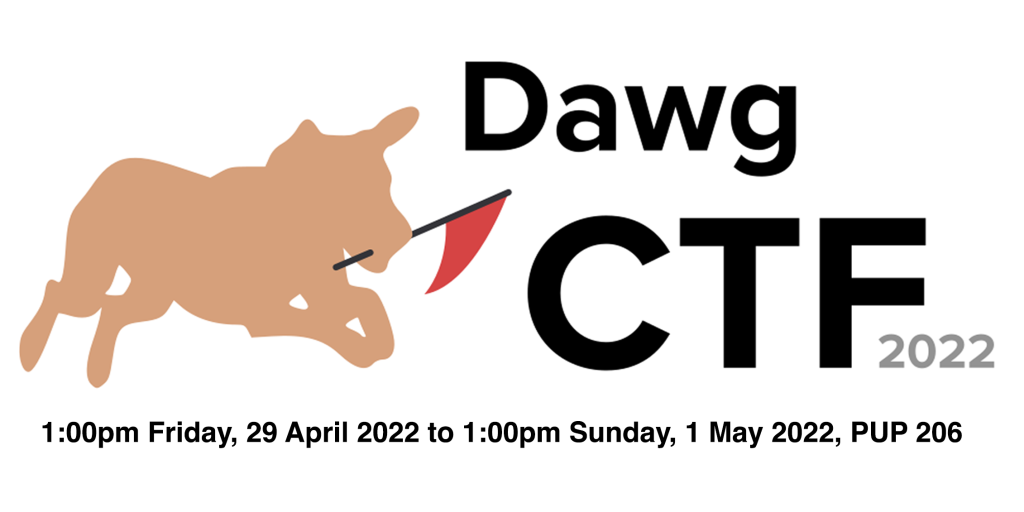
The UMBC Cyberdawgs will host a 48-hour Jeopardy-style Capture The Flag cybersecurity competition, online and in person for UMBC participants.
DawgCTF 2022 will be a Jeopardy-style CTF, so things are pretty simple. Players register online, either in teams or alone. At 1300 EDT on April 29, 2022, the competition will open. Players will have access to a board of challenges, ranging from easy to nigh-impossible, and scored appropriately. Whoever earns the most points by solving challenges wins! The in-person part of the event will take place in room 206 of the Public Policy Building.
The CTF will begin at 1:00 PM EDT on Friday, April 29, 2022, and end at 1:00 PM EDT on Sunday, May 1, 2022, for a total runtime of 48 hours. The maximum team size is four. There will be an in-person component for UMBC participants only.
At 8:00 PM on Friday, April 29th (7 hours after the start), we will give out some prizes to UMBC competitors, depending on their current position on the scoreboard at 8:00 PM. Only UMBC competitors will be eligible for these prizes. Don’t worry, they’ll be small prizes, mostly just for fun, and the clout and CTFtime credit will go to the “official” winners at competition closing time (1 pm on Sunday).
See the Dawg CTF 2022 site to register, get more information, and join the Discord server.
The post Cybersecurity CTF competition starts 1pm Friday 4/29 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyberdawgs will host a 48-hour Jeopardy-style Capture The Flag cybersecurity competition, online and in person for UMBC participants. DawgCTF 2022 will be a Jeopardy-style CTF, so things...
https://redirect.cs.umbc.edu/2022/04/cybersecurity-ctf-competition-starts-1pm-friday-4-29/
https://beta.my.umbc.edu/api/v0/pixel/news/129853/guest@my.umbc.edu/0822de8c309dd82c5655432c00695220/api/pixel
cybersecurity
events
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Tue, 26 Apr 2022 22:47:03 -0400
Tue, 26 Apr 2022 22:47:03 -0400
Cybersecurity CTF competition starts 1pm Friday 4/29
The UMBC Cyberdawgs will host a 48-hour Jeopardy-style Capture The Flag cybersecurity competition, online and in person for UMBC participants.
DawgCTF 2022 will be a Jeopardy-style CTF, so things are pretty simple. Players register online, either in teams or alone. At 1300 EDT on April 29, 2022, the competition will open. Players will have access to a board of challenges, ranging from easy to nigh-impossible, and scored appropriately. Whoever earns the most points by solving challenges wins! The in-person part of the event will take place in room 206 of the Public Policy Building.
The CTF will begin at 1:00 PM EDT on Friday, April 29, 2022, and end at 1:00 PM EDT on Sunday, May 1, 2022, for a total runtime of 48 hours. The maximum team size is four. There will be an in-person component for UMBC participants only.
At 8:00 PM on Friday, April 29th (7 hours after the start), we will give out some prizes to UMBC competitors, depending on their current position on the scoreboard at 8:00 PM. Only UMBC competitors will be eligible for these prizes. Don’t worry, they’ll be small prizes, mostly just for fun, and the clout and CTFtime credit will go to the “official” winners at competition closing time (1 pm on Sunday).
See the Dawg CTF 2022 site to register, get more information, and join the Discord server.
The post Cybersecurity CTF competition starts 1pm Friday 4/29 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyberdawgs will host a 48-hour Jeopardy-style Capture The Flag cybersecurity competition, online and in person for UMBC participants. DawgCTF 2022 will be a Jeopardy-style CTF, so things...
https://www.csee.umbc.edu/2022/04/cybersecurity-ctf-competition-starts-1pm-friday-4-29/
https://beta.my.umbc.edu/api/v0/pixel/news/118961/guest@my.umbc.edu/d778738d7a814069f2cb98ffc80417c0/api/pixel
cybersecurity
events
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Tue, 26 Apr 2022 22:47:03 -0400
Tue, 26 Apr 2022 22:47:03 -0400
2021 NSA Codebreaker Challenge Now Open
“The Codebreaker Challenge closely mirrors the real-world scenarios we deal with every day at NSA,” said challenge creator Eric Bryant. “It gives students the opportunity to test their knowledge, build new skills, and develop experience in areas typically not covered by course curricula in cybersecurity.”
NSA Codebreaker Challenge 2021 Now Open
NSA’s annual Codebreaker Challenge offers students a closer look at the type of work done at NSA and provides the opportunity to develop skills needed to achieve the Agency’s national security mission. The problems touch on skills like software reverse engineering, cryptanalysis, exploit development, blockchain analysis, and more. It gives students a hands-on opportunity to develop their reverse-engineering/low-level code analysis skills while working on a realistic problem set centered around the NSA’s mission.
The Challenge is open now and will run until a date late in December. Anyone with an email address from a recognized U.S. school or university may participate. While the challenge is intended for students, faculty are encouraged to participate as well. Furthermore, the site was designed to make it easy for those faculty interested in incorporating the challenge into their courses to do so (see the additional FAQ entries below.)
The 2021 Codebreaker Challenge consists of a series of tasks that are worth a varying amount of points based upon their difficulty. Schools will be ranked according to the total number of points accumulated by their students with the current ranking shown on a leaderboard. Solutions may be submitted at any time for the duration of the Challenge.
While not required, it is recommend that you solve tasks in order, since they flow with the storyline. Later tasks may rely on artifacts / inputs from earlier tasks. Each task in the 2021 challenge will require a range of skills. You will need to call upon all of your technical expertise, your intuition, and your common sense.
NSA provides some helpful resources to get you on the right track with the 2021 Challenge. The list as a starting point. It’s not exhaustive, and you’ll definitely need to do additional research on your own. There are things in this list that aren’t actually part of this year’s challenge. Once you register, you will be able to join the Community of Practice Discord server for the 2021 Codebreaker Challenge. NSA will also hold two technical talks this Fall, giving you a chance to hear from some of NSA’s experts.
The post 2021 NSA Codebreaker Challenge Now Open appeared first on Department of Computer Science and Electrical Engineering.
]]>
“The Codebreaker Challenge closely mirrors the real-world scenarios we deal with every day at NSA,” said challenge creator Eric Bryant. “It gives students the opportunity to test their knowledge,...
https://www.csee.umbc.edu/2021/08/2010-nsa-codebreaker-challenge-now-open/
https://beta.my.umbc.edu/api/v0/pixel/news/111553/guest@my.umbc.edu/25f07029a0a15396ab509af2bc16f860/api/pixel
cyberscholars
cybersecurity
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Sun, 15 Aug 2021 22:15:22 -0400
Sun, 15 Aug 2021 22:15:22 -0400
UMBC Cyber Dawgs win 2021 Mid-Atlantic Collegiate Cyber Defense Competition
 Photo by Marlayna Demond ’11 for UMBC
Photo by Marlayna Demond ’11 for UMBC
Congratulation to the UMBC Cyber Dawgs team, which took first place in the 2021 Mid-Atlantic Collegiate Cyber Defense Competition (MACCDC) finals. UMBC’s team was one of eight teams out of an initial 23 that qualified for the final competition. UMBC’s Cyber Dawgs will move on to compete in the National Collegiate Cyber Defense Competition (NCCDC), which will be held April 23-25, 2021.
The 2021 MACCDC regional final took place online April 1-3 and had teams fighting to protect their networks efficiently and effectively from simulated cyber threats and attacks using a scenario based on the COVID-19 global pandemic for its competition events.
The National Emergency Response Division (N.E.R.D.) is a data science-focused group within the Big Time Health Organization (BTHO), a multinational entity headquartered in Bethesda, Maryland. N.E.R.D. employees have been exceptionally busy dealing with the global health pandemic. As such, they have had to not only shift to work from home, but also expand the number of employees to support the inordinate amounts of data that is flooding each of its eight geographic locations throughout the U.S. Protecting the integrity of the data is critical, but when the data affects the delivery of health services to the public, the job of N.E.R.D. becomes even more mission critical.
The student teams will stand on the front lines of technology, alongside various healthcare providers. The main task at hand will be to ensure that pandemic-related data from state departments of health are accurate and delivered quickly. Information on outbreak locations, promising interventions, efficacy of testing, mortality rates, and other related statistics are critical so physicians, public health officials, and government entities can make informed decisions about resource allocations. Loss or inaccurate information can lead to tragic consequences. Vigilance is a must – be smart, be strong, be safe.
These regional and national competitions attract leading collegiate cybersecurity teams from across the nation. They put teams in situations that mimic scenarios they might encounter working to secure and protect online systems for government agencies and companies. Throughout each challenge, teammates work together to protect their systems from hackers and cyber attacks. At the same time, they keep their networks accessible to the users relying on them.
The UMBC Cyber Dawgs team won the MACCDC regionals last year and were national champions in 2017. In this year’s MACCDC, George Mason placed second and Liberty University third. Good luck to the Cyber Dawgs as they compete with the winners of nine other regional competitions in the National Collegiate Cyber Defense Competition later this month.
The post UMBC Cyber Dawgs win 2021 Mid-Atlantic Collegiate Cyber Defense Competition appeared first on Department of Computer Science and Electrical Engineering.
]]>
Photo by Marlayna Demond ’11 for UMBC Congratulation to the UMBC Cyber Dawgs team, which took first place in the 2021 Mid-Atlantic Collegiate Cyber Defense Competition (MACCDC) finals. UMBC’s...
https://www.csee.umbc.edu/2021/04/umbc-cyber-dawgs-win-2021-mid-atlantic-collegiate-cyber-defense-competition/
https://beta.my.umbc.edu/api/v0/pixel/news/100543/guest@my.umbc.edu/ffe2780cdfd7eea3e6ba57291000831f/api/pixel
cybersecurity
news
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
false
Sat, 03 Apr 2021 22:52:33 -0400
Sat, 03 Apr 2021 22:52:33 -0400
talk: EIPC: Efficient Asynchronous BFT with Adaptive Security, 12-1 Fri 3/12

The UMBC Cyber Defense Lab presents
EIPC: Efficient Asynchronous BFT with Adaptive Security
Chao Liu, CSEE, UMBC
12:00–1:00 pm ET, Friday, 12 March 2021
via WebEx
We present EPIC, a novel and efficient asynchronous Byzantine fault-tolerant (BFT) protocol with adaptive security. We characterize efficient BFT protocols using adaptive vs. static corruptions corruption models. EPIC takes a new approach to adaptively secure asynchronous BFT. It uses the adaptively secure threshold pseudorandom function (PRF) scheme for coin tossing and uses the Cobalt asynchronous binary agreement (ABA) protocol, which resolves the liveness issue of HoneyBadgerBFT and BEAT. As our new protocol modifies almost all building blocks for asynchronous BFT (including ABA, threshold PRF, and threshold encryption but not Byzantine reliable broadcast (RBC)), evaluating which component dominates the performance bottleneck is a difficult task. We mix and match different building blocks to implement four asynchronous BFT protocols and evaluate their performance. Via a five-continent deployment on Amazon EC2, we show that EPIC is slightly slower for small and medium-sized networks than the most efficient asynchronous BFT protocols with static security. We also find when the number of replicas less than 46, EPIC’s throughput is stable, achieving a peak throughput of 8,000–12,500 tx/sec using t2.medium VMs. When the network size grows larger, EPIC is not as efficient as those with static security, with a throughput of 4,000–6,300 tx/sec.
BFT state machine replication is the only known software solution for masking arbitrary failures and malicious attacks. BFT has been regarded as the model for building permissioned blockchains, where the distributed ledgers (i.e., replicas) know each other’s identities but may not trust each other.
Asynchronous protocols are inherently more robust against timing and denial-of-service (DoS) attacks. Two recent asynchronous BFT systems—HoneyBadgerBFT proposed by Miller et al. in CCS’16 and BEAT by Duan et al. in CCS’18—have comparable performance as partially synchronous BFT protocols and can scale to 100 replicas. The protocols, however, achieve static security, where the adversary needs to choose the set of corrupted replicas before protocol execution. This security property is weaker than that for many existing BFT protocols (e.g., PBFT), which achieve adaptive security, where the adversary can choose to corrupt replicas at any moment during the execution of the protocol.
Chao Liu is a Ph.D. candidate in computer science at UMBC, working with Alan Sherman. His research interests focus on cryptography, cybersecurity, and distributed systems.
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL Meetings include Mar 26, Jeremy Clark (Concordia); April 9, (UMBC), MeetingMayhem: A network adversarial thinking game; April 23, Peter Peterson (University of Minnesota Duluth), Adversarial thinking; and May 7, Farid Javani (UMBC), Anonymization by oblivious transfer
The post talk: EIPC: Efficient Asynchronous BFT with Adaptive Security, 12-1 Fri 3/12 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents EIPC: Efficient Asynchronous BFT with Adaptive Security Chao Liu, CSEE, UMBC 12:00–1:00 pm ET, Friday, 12 March 2021 via WebEx We present EPIC, a novel...
https://www.csee.umbc.edu/2021/03/talk-eipc-efficient-asynchronous-bft-with-adaptive-security-12-1-fri-3-12/
https://beta.my.umbc.edu/api/v0/pixel/news/99829/guest@my.umbc.edu/84382550ee5147b2c2a3c3aa7b60ce2b/api/pixel
computer-science
cybersecurity
news
research
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Sat, 06 Mar 2021 21:07:51 -0500
Sat, 06 Mar 2021 21:07:51 -0500
talk: 2021 SFS Research Study: Vulnerabilities in UMBC’s Incident Management System, 12-1 Jan. 29
The 2021 SFS Research Study: Vulnerabilities in UMBC’s Incident Management System
Cyrus Bonyadi and Enis Golaszewski
CSEE Department, UMBC
12:00noon–1pm Friday, 29 January 2021
remotely via WebEx
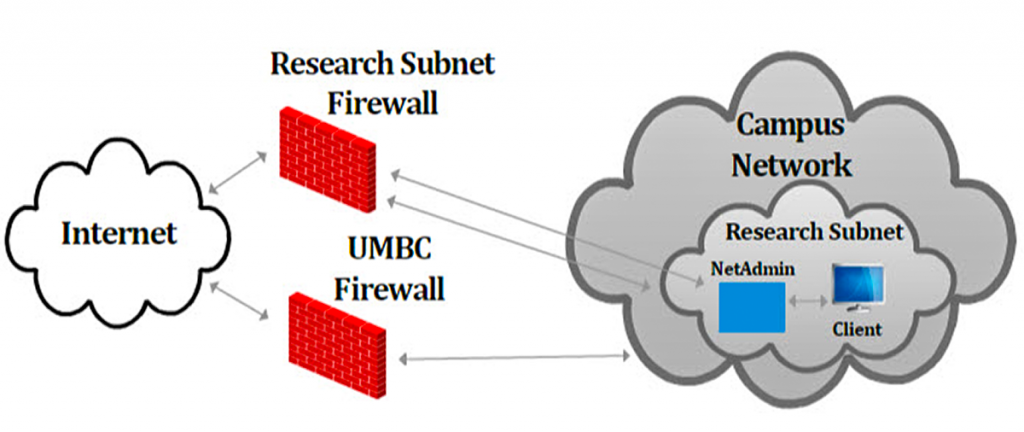
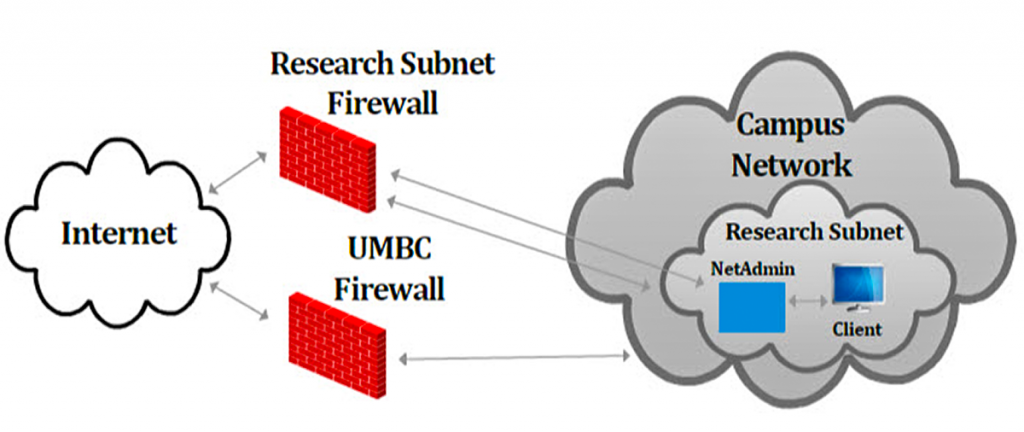
January 11–15, 2020, UMBC scholars in the CyberCorps: Scholarship for Service (SFS) and the DoD Cybersecurity Scholarship (CySP) programs collaboratively analyzed the security of UMBC’s Incident Management System (IMS). Students found numerous serious issues, including race conditions, code-injection, and cross-site scripting attacks, improper API implementation, and denial-of-service attacks. We present findings, recommendations, and details of these vulnerabilities.
UMBC’s Incident Management System (IMS) is a web application under development by UMBC’s DoIT to supplement their RequestTracker (RT). IMS allows DoIT security staff to supplement the information in RT by linking IMS incidents to RT tickets. IMS incidents store additional information and files regarding existing and potential security campaigns. Using the information in IMS and RT, DoIT generates executive reports, which can influence decisions related to budget, training, and other security concerns. Our study is helping to improve the architecture and implementation of IMS.
Participants comprised BS, MS, MPS, and Ph.D. students studying computer science, computer engineering, information systems, and cybersecurity, including SFS scholars who transferred from Montgomery College (MC) and Prince George’s Community College (PGCC) to complete their four-year degrees at UMBC.
About the Speakers. Cyrus Jian Bonyadi is a Ph.D. Student at UMBC working on distributed computing consensus theory. He is an alumnus of the varsity CyberDawgs team. email: *protected email* Enis Golaszewski is a Ph.D. Student at UMBC working on protocol analysis. He is a leading member of the Protocol Analysis Lab under Dr. Sherman. email: *protected email*,
Host: Alan T. Sherman, *protected email*. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1 pm. All meetings are open to the public. Upcoming CDL Meetings:
- Feb 12, Richard Carback (xxnetwork), Startup lessons learned
- Feb 26, Vahid Heydari (Rowan University)
- Mar 12, Chao Liu (UMBC), Efficient asynchronous BFT with adaptive security
- Mar 26, Jeremy Clark (Concordia)
- April 9, (UMBC), MeetingMayhem: A network adversarial thinking game
- April 23, Peter Peterson (University of Minnesota Duluth), Adversarial thinking
- May 7, Farid Javani (UMBC), Anonymization by oblivious transfer
The post talk: 2021 SFS Research Study: Vulnerabilities in UMBC’s Incident Management System, 12-1 Jan. 29 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The 2021 SFS Research Study: Vulnerabilities in UMBC’s Incident Management System Cyrus Bonyadi and Enis Golaszewski CSEE Department, UMBC 12:00noon–1pm Friday, 29 January 2021 remotely via...
https://www.csee.umbc.edu/2021/01/talk-2021-sfs-research-study-vulnerabilities-in-umbcs-incident-management-system-12-1-jan-29/
https://beta.my.umbc.edu/api/v0/pixel/news/98823/guest@my.umbc.edu/e1c770981082bf24494dd3e617b48316/api/pixel
cybersecurity
students
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Fri, 29 Jan 2021 09:30:31 -0500
event: UMBC INSuRE Research Projects from Fall 2020, 12-1:30 ET 12/18

UMBC’s Cyber Defense Lab presents
Presentations of the UMBC INSuRE Research Projects from Fall 2020
12:00noon–1:30pm, Friday, 18 December 2020
The Information Security Research and Education (INSuRE) research collaborative is a network of National Centers of Academic Excellence in Cyber Defense Research (CAE-Rs) universities that cooperate to engage students in solving applied cybersecurity research problems. Since fall 2012, INSuRE has fielded a multi-institutional cybersecurity research course in which BS, MS, and Ph.D. students work in small groups to solve unclassified problems proposed by the National Security Agency (NSA) and by other government and private organizations and laboratories.
Schedule
12:00-12:15pm poster presentations
12:15-12:40pm Detecting Web-Based Cryptomining Malware by Mining Open-Source Repositories
12:40-1:05pm Meeting Mayhem: A Network Adversary Game
1:05-1:30pm Analysis of the 5G AKA protocol with Comparison to 4G AKA
Detecting Web-Based Cryptomining Malware by Mining Open-Source Repositories
Naomi Albert, Elias Enamorado, Benjamin Padgette, Anshika Patel
Technical Director: William J. La Cholter (APL)
UMBC Expert: Charles Nicholas
With the ever-increasing popularity of browser-based cryptomining it is now more important than ever to detect malicious cryptojacking code. This paper serves to identify reliable indicators of injected cryptomining code in open-source repositories using static source code analysis techniques. We analyze static source code features of a curated set of cryptomining projects and innocuous codebases that are available as open-source projects on GitHub. Through this analysis we show that a novel Normalized Halstead Difficulty metric can be an important indicator of the presence of cryptomining software. Specifically, the Normalized Halstead complexity is significantly higher for cryptomining source code files as compared to the sampled non-miners. Using this newfound knowledge of the complexity of browser-based JavaScript cryptominers, supply-chain cryptojacking injection attacks in open-source repositories may be easier to identify through automated code review techniques.
Meeting Mayhem: A Network Adversary Game
Richard Baldwin, Trenton Foster
Technical Director: Edward Zieglar (NSA)
UMBC Experts: Marc Olano, Linda Oliva
Meeting Mayhem, a web-based educational game, teaches adversarial thinking through the Dolev-Yao security model. Meeting Mayhem is based on the paper-and-pencil “Protocol Analysis Game,” introduced by Edward Zieglar and adapted by UMBC PhD student Enis Golaszewski. Two or more users try to arrange a meeting time and place by sending messages through an insecure network controlled by an adversary. Through self discovery, players learn the dangers of network communications and the value of sound protocols supported by encryption, hashing, and digital signatures.
Formal Methods Analysis of the 5G AKA protocol, with Comparison to 4G AKA
Prajna Bhandary, Ryan Jahnige, Jason Schneck
Technical Director: Edward Zieglar (NSA)
We analyze the Fifth Generation (5G) Authentication and Key Agreement (AKA) protocol and the Fourth Generation (4G) Evolved Packet System Authentication and Key Agreement (EPS-AKA) protocol for possible structural faults using the Cryptographic Protocol Shapes Analyzer (CPSA). It is fundamental to provide authentication and key management in the security of cellular networks. 5G AKA provides mutual authentication between subscribers and the network, by providing the keys to protect both signaling and user plane data. 4G defines an authentication method, EPS-AKA, whereas 5G offers several different authentication techniques: 5G AKA, 5G EAP-AKA, and 5G EAP-TLS. In addition to our formal method analysis of 5G AKA and 4G EPS-AKA, we also analyze the differences in security properties between the 4G EPS-AKA protocol, and 5G AKA protocol. We verify that the upgrades made to 4G EPS-AKA improves control of the Home Network (HN) in 5G AKA. Additionally, we found that the ambiguous nature of the documentation regarding the channel between Serving Network (SN) and HN results in authentication concerns and we propose a solution.
Course Instructor: Alan T. Sherman
Support for this event is provided in part by the NSF under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public. Upcoming CDL meetings:
Biweekly CDL talks will resume in the spring 2021 semester.
The 2021 UMBC SFS/CySP Research Study will take place remotely in January (likely January 11-15).
The post event: UMBC INSuRE Research Projects from Fall 2020, 12-1:30 ET 12/18 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC’s Cyber Defense Lab presents Presentations of the UMBC INSuRE Research Projects from Fall 2020 12:00noon–1:30pm, Friday, 18 December 2020 via WebEx The Information Security Research...
https://www.csee.umbc.edu/2020/12/event-umbc-insure-research-projects-from-fall-2020-12-130-et-12-18/
https://beta.my.umbc.edu/api/v0/pixel/news/98052/guest@my.umbc.edu/a7f293a2362640ad181a5fa3ae035606/api/pixel
computer-science
cybersecurity
education
news
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sat, 12 Dec 2020 10:11:12 -0500
CyberCorps SFS Spring Meeting at UMBC
 The Scholarship for Service (SFS) Program is designed to recruit and train the next generation of cybersecurity professionals to meet the needs of Federal, State, local, and tribal government.
The Scholarship for Service (SFS) Program is designed to recruit and train the next generation of cybersecurity professionals to meet the needs of Federal, State, local, and tribal government.
CyberCorps SFS Spring Meeting at UMBC
10:00am-2:00pm Friday, 22 May 2020
Open to the public
via: https://umbc.webex.com/meet/sherman
UMBC’s Spring CyberCorps Scholarship for Service meeting will take place from 10 am to 2 pm on Friday, 22 May 2020. It will feature a discussion with Dr. Dan Guernsey (NSA) on Ghidra, Software Reverse Engineering, and Cybersecurity Careers at NSA, presentations by SFS students, and a hands-on Capture the Flag exercise.
10:00-10:30 Student presentations
Scholarship for Service (SFS) students from UMBC, Montgomery College (MC), and Prince George’s Community College (PGCC) will present their results solving IT security problems for their universities, county governments, and local companies. This activity is part of a pioneering program centered at UMBC to extend SFS scholarships to community college students. In January 2020, all SFS scholars at UMBC, PGCC, and MC worked collaboratively to analyze the security of a custom shadow-IT software application to query research grant information
10:30-11:30 Discussion with Dr. Dan Guernsey (NSA)
Learn about Ghidra, software reverse engineering, and cybersecurity careers at NSA. Ghidra is a software reverse engineering framework developed by NSA’s Research Directorate for NSA’s cybersecurity mission. It helps analyze malicious code and malware like viruses, and can give cybersecurity professionals a better understanding of potential vulnerabilities in their networks and systems (GitHub).
11:30-12:30 Lunch and discussion among attendees
12:30-2:00 Hands-on cyber defense exercise
Sharpen your cybersecurity skills by participating in a hands-on Capture the Flag exercise developed by the UMBC Cyber Dawgs and Cyrus Bonyadi, an SFS scholar and a member of the Cyber Dawgs, whose cyberdefense team won first place at the Mid-Atlantic Collegiate Cyber Defense Competition (MACCDC) in April 2020 and is competing in the National Collegiate Cyber Defense Competition (NCCDC).
Participants and organizers
Dr. Dan Guernsey earned the Ph.D in Computer Science from the University of Tulsa. Since 2011, he worked at the Department of Defense as a Computer Scientist and Architectures Researcher. During his studies at Tulsa, Dr. Guernsey contracted with the DoD Office of the Inspector General, the U.S. Secret Service, and local law firms. He performed reverse engineering and authored software analysis tools for product evaluation and digital forensics. His work helped solve criminal cases and helped resolve civil disputes involving software copyrights. Dr. Guernsey is an Adjunct Instructor at UMBC in the graduate Cybersecurity Program.
Host Alan T. Sherman (*protected email*) is a professor of computer science and Director of the UMBC Center for Information Security and Assurance, which center is responsible for UMBC’s designation as a National Center of Academic Excellence in Cyber Defense Education and Cyber Defense Research.
Richard Forno is a senior lecturer, Director of the UMBC Graduate Cybersecurity Program, and Assistant Director of the UMBC Center for Cybersecurity.
Casey W. O’Brien is Executive Director and Principal Investigator of the National CyberWatch Center, Prince George’s Community College.
Joe Roundy is the Cybersecurity Program Manager at Montgomery College, Germantown.
Support for this event is provided in part by the National Science Foundation under SFS grant DGE-1753681 and by the Department of Defense under CySP grant H98230-19-1-0308.
The post CyberCorps SFS Spring Meeting at UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
The Scholarship for Service (SFS) Program is designed to recruit and train the next generation of cybersecurity professionals to meet the needs of Federal, State, local, and tribal government....
https://www.csee.umbc.edu/2020/05/cybercorps-sfs-spring-meeting-at-umbc/
https://beta.my.umbc.edu/api/v0/pixel/news/93018/guest@my.umbc.edu/bb27d6581cff14ea903a83ad23c21eb5/api/pixel
cybersecurity
news
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
false
Sat, 09 May 2020 14:52:08 -0400
Sat, 09 May 2020 14:52:08 -0400
UMBC Cyber Dawgs rank #1 among university teams at annual Capture the Flag event

UMBC Cyber Dawgs #1 among university
teams at annual Capture the Flag event
The UMBC Cyber Dawgs ranked #1 among university teams in a challenging cybersecurity competition hosted virtually by the University of Maryland, College Park on April 18.
The Capture the Flag event was designed to test teams’ abilities to solve a variety of realistic cybersecurity problems. UMBC went head to head with more than 300 teams from both colleges and industry, placing third overall and #1 among the universities.
Charles Nicholas, professor of computer science and electrical engineering and a Cyber Dawgs faculty advisor, says that the team’s win shows how well-prepared UMBC students are for careers in cybersecurity, and how committed they are to excelling in intercollegiate competition. “It speaks volumes about our students, their enthusiasm, and their character,” he says.
Reflecting on the Cyber Dawgs’ #3 overall finish, Nicholas shares, “The teams that beat us are made up of experienced cyber professionals, who do this sort of work for a living.” To end the competition as the leading university team and trailing just two professional teams was quite a feat, he notes, saying, “Our faculty and our university are very proud of these students.”
The Cyber Dawgs recently won the Mid-Atlantic Collegiate Cyber Defense Competition. They are preparing for the National Collegiate Cyber Defense Competition, which will be held virtually in May.
Adapted from a UMBC News article written by Megan Hanks. Banner image: A person typing on a computer. Photo by Marlayna Demond ’11 for UMBC.
The post UMBC Cyber Dawgs rank #1 among university teams at annual Capture the Flag event appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Dawgs #1 among university teams at annual Capture the Flag event The UMBC Cyber Dawgs ranked #1 among university teams in a challenging cybersecurity competition hosted...
https://www.csee.umbc.edu/2020/04/umbc-cyber-dawgs-rank-1-among-university-teams-at-annual-capture-the-flag-event/
https://beta.my.umbc.edu/api/v0/pixel/news/92572/guest@my.umbc.edu/12762cf8000fbec29e409aa47a78ad34/api/pixel
cybersecurity
events
news
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Fri, 24 Apr 2020 16:00:35 -0400
Fri, 24 Apr 2020 16:00:35 -0400
UMBC Cyber Dawgs win Mid-Atlantic Collegiate Cyber Defense Competition
UMBC Cyber Dawgs win Mid-Atlantic Collegiate Cyber Defense Competition
Last weekend, the UMBC Cyber Dawgs took first place in the Mid-Atlantic Collegiate Cyber Defense Competition (MACCDC), which was held virtually. UMBC’s team was one of eight that participated in the competition, fighting to protect their networks efficiently and effectively from simulated cyber threats and attacks. The team topped Penn State; the University of Maryland, College Park; and University of Virginia, which won the national championship for the past two years.
UMBC’s Cyber Dawgs will move on to compete in the National Collegiate Cyber Defense Competition (NCCDC). Due to COVID-19, the competition will be held remotely this year.
How does the competition work?
These regional and national competitions attract leading collegiate cybersecurity teams from across the nation. They put teams in situations that mimic scenarios they might encounter working to secure and protect online systems for government agencies and companies. Throughout each challenge, teammates work together to protect their systems from hackers and cyber attacks. At the same time, they keep their networks accessible to the users relying on them.
Meet the team
The MACCDC was about 14 hours long, and was held over two days. During the competition, the teams were not permitted to interact with their coaches Charles Nicholas, professor of computer science and electrical engineering (CSEE), and Rick Forno, senior lecturer in CSEE.
The winning UMBC team included Anna Staats ‘20, computer science; RJ Joyce ‘18, M.S. ‘20, computer science; Cyrus Bonyadi, Ph.D. ‘23, computer science; Drew Barrett ‘20, computer science; Seamus Burke ‘20, computer science; Henry Budris ‘22, computer science; Chris Skane ‘21, computer science; and Nikola Bura ‘21, computer science.
“We are so proud of our team, and their ability to work together as a team under such extraordinary conditions,” says Nicholas.
This is the third time in six years that the Cyber Dawgs have won the MACCDC. The UMBC team won the national championship in 2017.
Adapted from a UMBC News article by Megan Hanks. Banner image: Student using a computer. Photo by Marlayna Demond ’11 for UMBC.
The post UMBC Cyber Dawgs win Mid-Atlantic Collegiate Cyber Defense Competition appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Dawgs win Mid-Atlantic Collegiate Cyber Defense Competition Last weekend, the UMBC Cyber Dawgs took first place in the Mid-Atlantic Collegiate Cyber Defense Competition...
https://www.csee.umbc.edu/2020/04/umbc-cyber-dawgs-win-mid-atlantic-collegiate-cyber-defense-competition/
https://beta.my.umbc.edu/api/v0/pixel/news/92108/guest@my.umbc.edu/485f14121c68bc1bebb82c903f4cfa33/api/pixel
cybersecurity
events
news
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
4
0
false
Sun, 12 Apr 2020 16:33:39 -0400
Sun, 12 Apr 2020 16:33:39 -0400
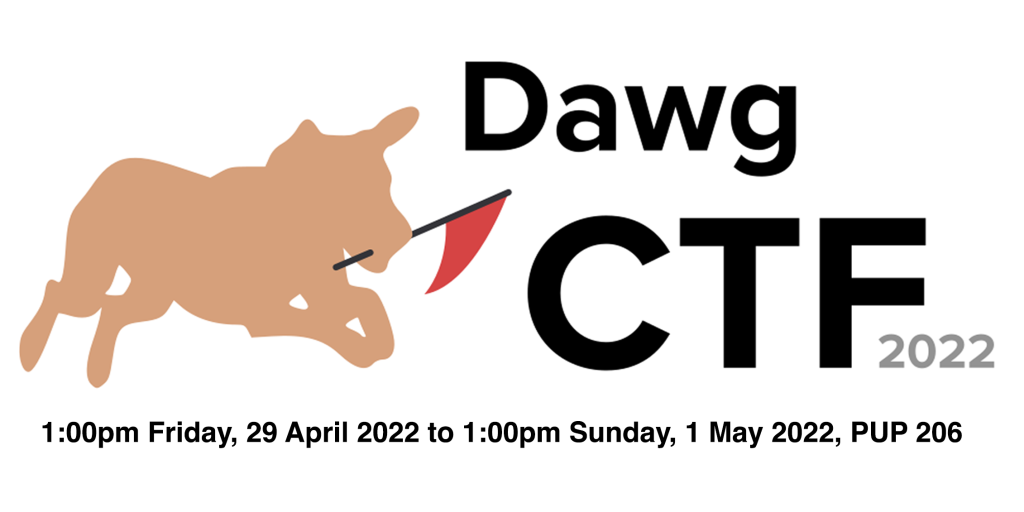
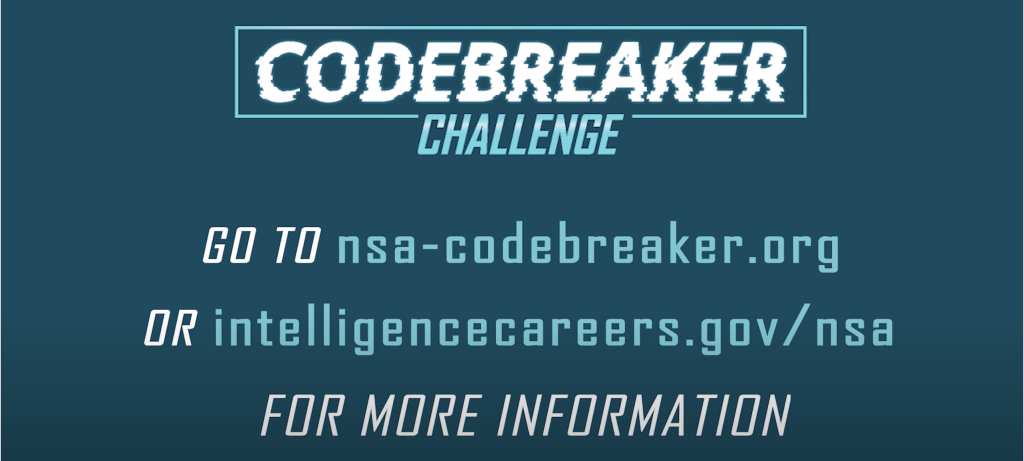
 Photo by Marlayna Demond ’11 for UMBC
Photo by Marlayna Demond ’11 for UMBC

 The Scholarship for Service (SFS) Program is designed to recruit and train the next generation of cybersecurity professionals to meet the needs of Federal, State, local, and tribal government.
The Scholarship for Service (SFS) Program is designed to recruit and train the next generation of cybersecurity professionals to meet the needs of Federal, State, local, and tribal government.