UMBC redesignated a National Center of Academic Excellence in Cyber Defense

UMBC redesignated a National Center of Academic Excellence in Cyber Defense
UMBC has been redesignated as a National Center of Academic Excellence in Cyber Defense (CAE-CD) through the academic year 2028.
The CAE-CD designation indicates that UMBC is helping reduce threats to our national infrastructure by promoting higher education and research in cyber defense and providing the nation with a pipeline of qualified cybersecurity professionals. UMBC is also designated as a Center of Academic Excellence in Cyber Research (CAE-R), which signifies that UMBC increases the understanding of robust cyber defense technology, policy, and practices that will enable our Nation to prevent and respond to a catastrophic event.
The National Centers of Academic Excellence in Cybersecurity (NCAE-C) program is managed by the National Cryptologic School at the National Security Agency. Federal Partners include the Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), the National Institute of Standards and Technology (NIST)/National Initiative on Cybersecurity Education (NICE), the National Science Foundation (NSF), the Department of Defense Office of the Chief Information Officer (DoD-CIO), and US Cyber Command (CYBERCOM).
The NCAE-C program’s mission is to create and manage a collaborative cybersecurity educational program with community colleges, colleges, and universities that
- Establishes standards for cybersecurity curriculum and academic excellence,
- Includes competency development among students and faculty,
- Values community outreach and leadership in professional development,
- Integrates cybersecurity practice within the institution across academic disciplines,
- Actively engages in solutions to challenges facing cybersecurity education.
UMBC offers courses, a track, and concentrations focused on cybersecurity in its Computer Science and Information Systems programs at the undergraduate and graduate levels. In addition, UMBC has several major cybersecurity-oriented scholarship programs to prepare the next generation of cybersecurity professionals in an increasingly digital age, focusing on increasing the participation of women and other underrepresented groups in this fast-growing field. These include the UMBC Cyber Scholars program, CyberCorps: Scholarships For Service (SFS) program, and DOD Cyber Scholarship Program (CySP). Applications for SFS cybersecurity scholarships to begin in Fall 2022 are due via Scholarship Retriever by 12noon November 15, 2021.
UMBC also has professional cybersecurity programs that include certificate programs as well as a Master’s of Professional Studies (MPS) degree at its campuses in Catonsville (UMBC main campus) and Rockville (UMBC at the Universities at Shady Grove). UMBC Training Centers offers cybersecurity courses for both individuals and organizations.
Cybersecurity research at UMBC occurs in many of its laboratories and in the UMBC Center for Cybersecurity (UCYBR), which recently merged with UMBC’s original cybersecurity center, the UMBC Center for Information Security and Assurance (CISA).
The post UMBC redesignated a National Center of Academic Excellence in Cyber Defense appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC redesignated a National Center of Academic Excellence in Cyber Defense UMBC has been redesignated as a National Center of Academic Excellence in Cyber Defense (CAE-CD) through the academic...
https://www.csee.umbc.edu/2021/08/umbc-redesignated-a-national-center-of-academic-excellence-in-cyber-defense/
https://beta.my.umbc.edu/api/v0/pixel/news/111686/guest@my.umbc.edu/b8874785ca9f862a6e3868a7b1c08931/api/pixel
coeit
csee
cyberscholars
cybersecurity
education
information-systems
research
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Fri, 20 Aug 2021 17:18:35 -0400
Fri, 20 Aug 2021 17:18:35 -0400
Six UMBC faculty, incuding three in CSEE, receive MIPS research awards
 Anupam Joshi (left, photo by Marlayna Demond’ 11) and Tina Williams-Koroma, ’02 computer science (right, photo courtesy of Williams-Koroma)
Anupam Joshi (left, photo by Marlayna Demond’ 11) and Tina Williams-Koroma, ’02 computer science (right, photo courtesy of Williams-Koroma)
Three CSEE faculty receive MIPS research awards
This post is adapted from a UMBC News article UMBC faculty, alumni entrepreneurs receive record-number of MIPS awards for tech collaborations written by Adriana Fraser.
Six UMBC faculty members have just received grants from the Maryland Industrial Partnerships (MIPS) program to develop new technologies with potential to grow the state’s economy. This is UMBC’s largest number of winning proposals within a single proposal round since MIPS began in 1987. The program connects University System of Maryland (USM) faculty and students with Maryland businesses. UMBC’s latest MIPS grantees include computer science and electrical engineering faculty Tim Oates, Chein-I Chang, and Anupam Joshi; Soobum Lee, mechanical engineering; Dipanjan Pan, chemical, biochemical, and environmental engineering; and Vikram Vakharia, marine biotechnology. Among their industry partners are UMBC alumni entrepreneurs who are building businesses in Maryland.
Joshi, professor and chair of computer science and electrical engineering, received a MIPS grant for a cybersecurity collaboration with the startup CyDeploy. They are developing a platform that automates the quality assurance process for cybersecurity updates made to IT and “internet of things” (IoT) devices like Amazon Alexa, Google Home, and health and medical devices. CyDeploy CEO Tina Williams-Koroma ’02, computer science, presented Joshi with the idea to develop a “cybersecurity-driven change management system.” The technology is based on and leverages the use of artificial intelligence and machine learning to create a cloud-based replica of a company’s systems.
Williams-Koroma and Joshi’s group at UMBC developed a conceptual prototype. It shows the infrastructure and technology that would make the system feasible, combining off-the-shelf tools with novel research. “Increasingly, the government is now beginning to mandate security requirements around IoT devices. The longer-term vision that CyDeploy has is capturing the state of these systems, virtually recreating them and then running the security changes against virtual versions to see how the changes would affect those systems,” Joshi adds.
Williams-Koroma, who is also an adjunct instructor at UMBC, projects that the initial development of the platform will be complete in late spring 2021. They anticipate launching a free pilot version for businesses to test their IT systems. IoT pilots will come in a later phase.
Read more about these awards in the UMBC News article UMBC faculty, alumni entrepreneurs receive record-number of MIPS awards for tech collaborations.
The post Six UMBC faculty, incuding three in CSEE, receive MIPS research awards appeared first on Department of Computer Science and Electrical Engineering.
]]>
Anupam Joshi (left, photo by Marlayna Demond’ 11) and Tina Williams-Koroma, ’02 computer science (right, photo courtesy of Williams-Koroma) Three CSEE faculty receive MIPS research awards This...
https://www.csee.umbc.edu/2021/02/six-umbc-faculty-incuding-three-in-csee-receive-mips-research-awards/
https://beta.my.umbc.edu/api/v0/pixel/news/99277/guest@my.umbc.edu/be762a3ecac75c981fea346f57be054f/api/pixel
computer-science
csee
cybersecurity
electrical-engineering
news
research
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sat, 13 Feb 2021 12:27:43 -0500
talk: Dr. Richard Carback on Startup Lessons Learned, 12-1 Fri 2/12

The UMBC Cyber Defense Lab presents
Startup Lessons Learned
Richard Carback (Ph.D. UMBC CS 2010)
xx network
This talk will explore the technology and lessons learned by UMBC alumnus Richard Carback from his experience co-founding and closing the security startup Lexumo, which provided the only automated service that continuously monitors IoT software platforms for the latest public vulnerabilities. In addition to covering some of the hard problems and Lexumo’s technical approach for monitoring all the world’s open-source software to assist companies in managing their vulnerabilities, Dr. Carback will discuss the mistakes and complexities of getting funded, delivering a product, and finding customers.
Dr. Richard Carback is a UMBC Alumnus (CS Ph.D., 2010) who is an entrepreneur who currently runs a private consultancy for computer security, computer forensics, cryptography, and smart contracts. He is a privacy-preserving systems expert with a background in elections and anonymity networks. While the group leader for the embedded systems security group at Charles Stark Draper Laboratories, he spun out an IoT vulnerability startup called Lexumo that provided the only automated service that continuously monitored IoT software platforms for the latest public vulnerabilities. At UMBC, he worked with Alan Sherman on secure elections and was the primary researcher behind Takoma Park’s deployment of the Scantegrity voting system, the first usage of voter-verifiable end-to-end election technology in a municipal election. email: *protected email*
Host: Alan T. Sherman, *protected email*. Support for this event was provided in part by the NSF under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1 pm. All meetings are open to the public. Upcoming CDL Meetings:
- Feb 26, Vahid Heydari (Rowan University)
- Mar 12, Chao Liu (UMBC), Efficient asynchronous BFT with adaptive security
- Mar 26, Jeremy Clark (Concordia)
- April 9, (UMBC), MeetingMayhem: A network adversarial thinking game
- April 23, Peter Peterson (University of Minnesota Duluth), Adversarial thinking
- May 7, Farid Javani (UMBC), Anonymization by oblivious transfer
The post talk: Dr. Richard Carback on Startup Lessons Learned, 12-1 Fri 2/12 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Startup Lessons Learned Richard Carback (Ph.D. UMBC CS 2010) xx network 12:00–1:00pm ET, Friday,12 February 12 2021 WebEx:...
https://www.csee.umbc.edu/2021/02/talk-dr-richard-carback-on-startup-lessons-learned-12-1-fri-2-12/
https://beta.my.umbc.edu/api/v0/pixel/news/99052/guest@my.umbc.edu/afa1dc13cc981b15aed9bf7eccba5300/api/pixel
alumni
csee
cybersecurity
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Sun, 07 Feb 2021 21:30:34 -0500
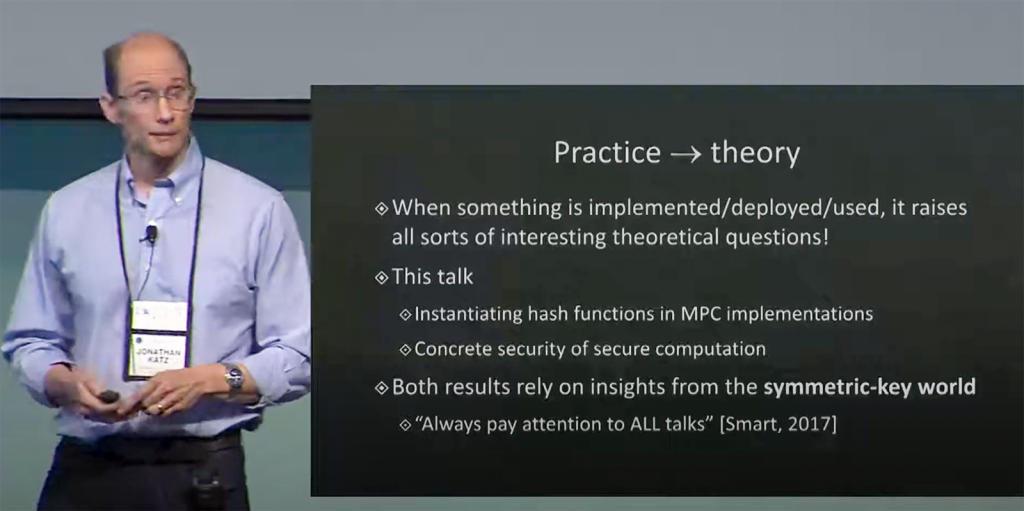
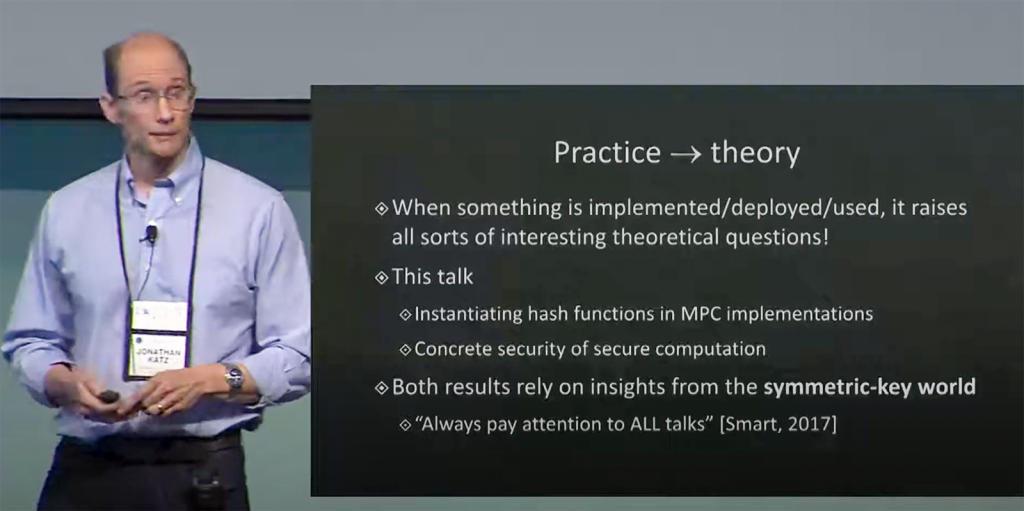
talk: Secure Computation: From Theory to Practice, 12-1pm Oct 30
UMBC Cyber Defense Lab presents
Secure Computation: From Theory to Practice
Jonathan Katz
Computer Science Department
University of Maryland, College Park
12:00–1:00 pm EDT, Friday, 30 October 2020
Online via Webex
Protocols for secure multi-party computation (MPC) allow a collection of mutually distrusting parties to compute a function of their private inputs without revealing anything else about their inputs to each other. Secure computation was shown to be feasible 35 years ago, but only in the past decade has its efficiency been improved to the point where it has been implemented and, more recently, begun to be used. This real-world deployment of secure computation suggests new applications and raises new questions.
This talk will survey some recent work at the intersection of the theory and practice of MPC, focusing on a surprising application to the construction of Picnic, a “post-quantum” signature scheme currently under consideration by NIST for standardization.
Jonathan Katz is a faculty member in the department of computer science at the University of Maryland, College Park, where he formerly served as director of the Maryland Cybersecurity Center for over five years. He is an IACR Fellow, was named a University of Maryland distinguished scholar-teacher in 2017-2018, and received the ACM SIGSAC Outstanding Contribution Award in 2019.
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public.
Upcoming CDL Meetings: Nov. 13, TBA, [possibly: David R Imbordino (NSA), Security of the 2020 presidential election]; Dec. 11, TBA, [possibly: Peter A. H. Peterson (Univ. of Minnesota Duluth), Adversarial Thinking]
The post talk: Secure Computation: From Theory to Practice, 12-1pm Oct 30 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Defense Lab presents Secure Computation: From Theory to Practice Jonathan Katz Computer Science Department University of Maryland, College Park 12:00–1:00 pm EDT, Friday, 30...
https://www.csee.umbc.edu/2020/10/talk-secure-computation-from-theory-to-practice-12-1pm-oct-30/
https://beta.my.umbc.edu/api/v0/pixel/news/96902/guest@my.umbc.edu/d095dd467d54d3508b78e08059ead114/api/pixel
csee
cybersecurity
events
news
quantum-computing
research
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sat, 24 Oct 2020 13:33:48 -0400
Sat, 10 Oct 2020 13:33:00 -0400
UMBC Cyber Dawgs are named CyberForce national champions
 The Cyber Dawgs at the CyberForce competition. From left, Charles Nicholas, Anna Staats, Drew Barrett, Grant Spencer, Cyrus Bonyadi, and Seamus Burke. Photo courtesy of Argonne National Lab.
The Cyber Dawgs at the CyberForce competition. From left, Charles Nicholas, Anna Staats, Drew Barrett, Grant Spencer, Cyrus Bonyadi, and Seamus Burke. Photo courtesy of Argonne National Lab.
UMBC Cyber Dawgs are named CyberForce national champions
UMBC’s Cyber Defense Team, known as the Cyber Dawgs, has emerged the national champion team in the U.S. Department of Energy’s fifth annual CyberForce Competition. The Cyber Dawgs earned first place overall out of more than 100 teams from universities across the country.
Ten national laboratories hosted competing teams this year, November 15 – 16. UMBC competed at the Argonne National Laboratory near Chicago, Illinois, while other teams traveled to sites like the Pacific Northwest National Laboratory in Washington state and Oak Ridge National Laboratory in Tennessee. Competing teams hailed from a broad range of institutions, including Virginia Tech, Carnegie Mellon, Georgia Tech, Texas A&M and the U.S. Air Force Academy.
The competition tasks students with defending critical energy infrastructure during simulated cyberattacks. The scenarios are designed to be realistic, focused on water and power systems and including real-world constraints, such as insufficient budget for system upkeep and limited information on system needs. During the competition, “red teams,” including industry professionals, attack the system, while the students work to ensure that the infrastructure is available to their customers, or “green teams,” who test system usability.
The teams receive points based on how successfully they address attacks, while still allowing users to access the infrastructure they need. The teams are also awarded points for innovative defense tactics and ideas. This year’s competition saw several leading teams with neck-and-neck scores until the final round, when UMBC’s Cyber Dawgs pulled ahead for the victory.
The competition offers students a unique opportunity to develop their cybersecurity skills in relation to critical infrastructure, and have hands-on experience in a realistic cyberattack situation.
“The CyberForce competition is the most unique of our annual events, allowing us to experiment with network configurations to defend an industrial control system against adversaries while playing the roles of an IT organization,” explains RJ Joyce ’18, M.S. ’20, computer science, a member of the winning team. “The hard work, dedication, and creativity that each member brought to the team lifted us from a regional win last year to a national win this year.”
In addition to Joyce, last weekend’s winning team included Anna Staats ’20, computer science; Drew Barrett ’20, computer science; Grant Spencer ’20, computer science; Cyrus Bonyadi, Ph.D. ’23, computer science; and Seamus Burke ’20, computer science.
“The team’s second national championship in three years shows the enthusiasm, grit, and tenacity of our students in demonstrating their technical cyber expertise in a competitive arena,” says Rick Forno, senior lecturer of computer science and assistant director of UMBC’s Center for Cybersecurity.
Forno advises the Cyber Dawgs with Charles Nicholas, professor of computer science and electrical engineering. “It’s an awesome thing not just for the team and university,” he says, “but for each competitor individually, as they prepare to enter the cybersecurity workforce after graduation.”
UMBC students have a strong record in state and national competition. In 2018, UMBC computer science and information systems students won the top prize at the Maryland Cyber Challenge. A year earlier, the UMBC Cyber Dawgs won the National Collegiate Cyber Defense Competition.
Adapted from a UMBC News article by Megan Hanks.
The post UMBC Cyber Dawgs are named CyberForce national champions appeared first on Department of Computer Science and Electrical Engineering.
]]>
The Cyber Dawgs at the CyberForce competition. From left, Charles Nicholas, Anna Staats, Drew Barrett, Grant Spencer, Cyrus Bonyadi, and Seamus Burke. Photo courtesy of Argonne National Lab. UMBC...
https://www.csee.umbc.edu/2019/11/umbc-cyber-dawgs-are-named-cyberforce-national-champions/
https://beta.my.umbc.edu/api/v0/pixel/news/88626/guest@my.umbc.edu/c932c805fd9921bb2a7c6733824198ca/api/pixel
csee
cybersecurity
news
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
false
Tue, 19 Nov 2019 15:38:07 -0500
UMBC Cyberdawgs win first place in the 2019 DOE CyberForce Competition
 UMBC’s CyberDawgs win first place in the 2019 DOE Cyberforce Competition
UMBC’s CyberDawgs win first place in the 2019 DOE Cyberforce CompetitionCyberdawgs place first out of 105 teams in DOE’s 5th CyberForce Competition
Congratulations to the UMBC CyberDawgs team for their first place finish in a field of 105 collegiate teams in the U.S. Department of Energy’s Fifth Annual CyberForce Competition. The distributed event was held at ten of the DOE’s National Laboratories and challenged 105 teams to defend a simulated energy infrastructure from cyber-attacks.
The took place on November 15 and 16 with the goal of bolstering the U.S. cybersecurity workforce by extending skill-building opportunities for students, offering memorable hands-on experiences and highlighting the crucial role this field plays in preserving national energy security. The Cyberdawgs participated at the Argonne National Laboratory site in Illinois.
During the competition, teams competed to defend their simulated infrastructure from attacks by adversarial “red teams” composed of industry professionals, all while maintaining service for their “green team” customers, played by volunteers. The scenarios included simulated industrial control system components, real-world anomalies and constraints, and interaction with users of the systems.
Teams were scored on their success in protecting the infrastructure against attacks while ensuring the usability of the system, with additional points awarded for innovative ideas and defenses.
The team that competed in this year’s competition was chosen from members of the CyberDawgs student group, composed of students from a variety of majors who share a common interest in computer and network security. No prior experience is required to join and any UMBC students who want to learn more about cybersecurity and learn new skills in the field are encouraged to subscribe to its mailing list and attend meetings.
The CyberDawgs group is advised by CSEE faculty Charles Nicholas and Richard Forno.
The post UMBC Cyberdawgs win first place in the 2019 DOE CyberForce Competition appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC’s CyberDawgs win first place in the 2019 DOE Cyberforce Competition Cyberdawgs place first out of 105 teams in DOE’s 5th CyberForce Competition Congratulations to the UMBC CyberDawgs...
https://www.csee.umbc.edu/2019/11/umbc-cyberdawgs-win-first-place-2019-doe-cyberforce-competition-argonne-cybersecurity-security/
https://beta.my.umbc.edu/api/v0/pixel/news/88544/guest@my.umbc.edu/ee7b8df122690fe7ad2794a05a16674d/api/pixel
csee
cybersecurity
news
students
uncategorized
undergraduate
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
8
0
false
Sun, 17 Nov 2019 17:25:26 -0500
Richard Forno: Threats remain to US voting system – and voters’ perceptions of reality
 As Americans go to the polls, the voting process and the information environment are still not secure. AP Photo/David Goldman
As Americans go to the polls, the voting process and the information environment are still not secure. AP Photo/David Goldman
Threats remain to US voting system – and voters’ perceptions of reality
Richard Forno, University of Maryland, Baltimore County
As the 2018 midterms proceed, there are still significant risks to the integrity of the voting system – and information warfare continues to try to influence the American public’s choices when they cast their ballots.
On the day of the election, there were a number of early hitches in voting at individual polling places, such as polling places opening late and vote-counting machines not plugged in. But there seem not – at least not yet – to be major problems across the country.
However, not all the election-related news and information voters have been encountering in recent days and weeks is accurate, and some of it is deliberately misleading. As this election’s results come back, they will reveal whether the misinformation and propaganda campaigns conducted alongside the political ones were effective.
Securing election systems
America’s electoral process remains highly fragmented, because of the country’s cherished tradition of decentralized government and local control. While this may leave some individual communities’ voting equipment potentially vulnerable to attack, the nation’s voting process overall may be more trustworthy as a result of this fragmentation. With no unified government agency or office to provide, administer and protect election technologies, there’s not one central national element that could fail or be attacked.
Across the country, though, many districts’ voters will cast ballots with the help of machines that have long-standing security concerns. Fortunately, 45 states keep a paper record of each vote cast – whether for fear of threats to voting integrity or just budget constraints preventing purchase of newer gear. But that means five states – Louisiana, Georgia, South Carolina, New Jersey and Delaware – don’t keep paper records of their voters’ choices.
Voting machine vendors have been reluctant to appear before Congress to explain their systems’ security practices – and shortcomings. However, federal agencies have helped some states reduce the likelihood of voting machines being hacked or physically tampered with.
Beyond voting machines
Election security is about much more than voting machines and vote-counting systems, though they are the most visible technologies at work on Election Day. State systems that track voter registrations, or allow users to register online, are enticing targets for hackers, too. Security firm Carbon Black reported that 81 million voter records from 20 states are available in online forums. This data, obtained by hacking various official and corporate databases, could be used to facilitate voter fraud or sow confusion at polling places on Election Day: How would you feel if you were told that someone using your name and address had already voted?
There are security concerns even in states like Oregon, where everyone votes on paper and mails in their ballots in advance of Election Day. That state’s election officials were targeted by hackers seeking to gain access to state email and database systems. With that access, attackers might be able to digitally impersonate a government official to send false or confusing emails, press releases or other notifications to citizens, journalists or poll workers.
Also at risk are public-facing official websites that carry election information. Merely changing the reported location of polling places or voting hours could prevent some people from voting. Also vulnerable are states’ methods of announcing preliminary election results. At a major internet security conference in August, children were able to compromise replicas of several states’ election-reporting systems. The most remarkable was that in just 10 minutes, an 11-year-old boy cracked the security on a copy of the Florida secretary of state’s website and was able to change the publicly announced vote totals for candidates. That could be enough to cast doubt on whatever was later reported as the official results – and the integrity of the system itself.
Managing information on social media
A more difficult threat to defend against is information warfare, which doesn’t attack voting machines or election officials’ computers. Rather, it targets voters’ perceptions and decisions, seeking to influence how they vote.
Long before the 2016 U.S. presidential election, information warfare was influencing elections around the world, including in Ukraine, Myanmar and Egypt. But after 2016, Facebook and Twitter came under intense scrutiny for their role in providing digital environments that facilitated the spread of misinformation to sow discontent, and special counsel Robert Mueller began investigating Russians’ influence efforts.
In the run-up to the 2018 midterms, Russians and others were still hard at work trying to influence Americans to vote in ways that help foreign interests. In October, the U.S. Department of Justice charged a Russian woman with creating thousands of fake social media accounts allegedly representing American citizens to “create and amplify divisive social media and political content” before the election.
This year, though, unlike two years ago, social media companies are taking action. Twitter and Facebook have both deleted thousands of accounts they identified as engaging in propaganda and influence-peddling. And they have made other efforts to identify and fight falsehoods on their platforms, too.
Nevertheless, online misinformation continues to thrive. More than 80 percent of the Twitter accounts that often shared links to false and misleading information in 2016 are still active today. And the amount of online misinformation is higher than it was two years ago.
Investigating alleged wrongdoing
U.S. intelligence and police agencies are concerned about the potential effects of misinformation on the American electorate. But large proportions of the country don’t trust those organizations to be politically independent. It doesn’t help that the White House continues to claim, without evidence, that voter fraud is a significant problem.
Mainstream news organizations can find themselves under scrutiny too, either for reporting falsehoods that appear to gain traction online or for failing to filter out or properly identify inaccurate information for their readers.
Looking ahead
Protecting democracy is a huge challenge. I’ve written before that it involves more than technical solutions to computer problems. The U.S. government, and the people it serves, must find the desire and the drive to establish secure and trustworthy procedures for running elections across the country. Education is also key, teaching people from an early age how to recognize propaganda and misinformation, and think critically about the information they encounter. Facts are not subject to alternative views; without widespread agreement on common objective realities, society and government cannot function well.
Technology continues to evolve, presenting challenges to individuals and society alike. Emerging “deepfake” technology is already helping create convincing videos of people appearing to say and do things they never said or did. In addition, intelligent social media bots are becoming more human-like, making identifying and blocking them much more difficult. That’s just some of the challenges that democracies will face in the future.
Many of these problems will not have a clearly defined fix, because they involve a nuanced balancing of individual rights and social necessities. Real and lasting solutions must come from civil discourse by rational and objectively informed people who have, above all, the actual honest desire to do it right.Richard Forno, Senior Lecturer, Cybersecurity & Internet Researcher, University of Maryland, Baltimore County
This article is republished from The Conversation under a Creative Commons license. Read the original article.
The post Richard Forno: Threats remain to US voting system – and voters’ perceptions of reality appeared first on Department of Computer Science and Electrical Engineering.
]]>
As Americans go to the polls, the voting process and the information environment are still not secure. AP Photo/David Goldman Threats remain to US voting system – and voters’ perceptions of...
https://www.csee.umbc.edu/2018/11/richard-forno-threats-remain-to-us-voting-system-and-voters-perceptions-of-reality/
https://beta.my.umbc.edu/api/v0/pixel/news/80129/guest@my.umbc.edu/cfde4542edba58ca31cbea1ce67bb24d/api/pixel
computer-science
csee
cybersecurity
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Tue, 06 Nov 2018 15:03:32 -0500
Tue, 06 Nov 2018 15:03:32 -0500
Learn cybersecurity skills in NSA’s Codebreaker Challenge

Get hands-on cybersecurity and blockchain skills in NSA’s Codebreaker Challenge
NSA’s sixth annual Codebreaker Challenge is a hands-on, cybersecurity engineering challenge in which students work to complete mission-focused objectives and push their university to the top of the competition leaderboard.
The 2018 scenario involves ransomware and blockchain. A new strain of ransomware has managed to penetrate several critical government networks and NSA has been called upon to assist in remediating the infection to prevent massive data losses. For each infected machine, an encrypted copy of the key needed to decrypt the ransomed files has been stored in a smart contract on the Ethereum blockchain and is set to only be unlocked upon receipt of the ransom payment. Your mission is to ultimately (1) find a way to unlock the ransomware without giving in to the attacker’s demands and (2) figure out a way to recover all of the funds already paid by other victims. Are YOU up to the challenge?
UMBC students did well, both individually and as a group, in previous challenges. Let’s make it to the top of the leaderboard this year.
Feedback from previous iterations of the challenge showed that students were able to learn a great deal from participating. Each student receives a slightly different set of challenge binaries and associated files, so that one student’s solution won’t work for someone else. The binaries are similar enough so that students can work together to understand the problems and develop approaches to solutions and hen implement them independently and register their results.
The 2018 challenge consists of a series of tasks that are worth a varying amount of points based upon their difficulty. In previous years, tasks had to be solved in order to unlock the next task and rankings were based upon the quantity of solvers that progressed the furthest from each school. This way of ranking heavily weighted progression above participation and did not allow for skipping ahead if a particular task became a stumbling block. So to address these issues, all tasks will be available immediately upon registration and can be solved in any order. The point value associated with each task is based on relative difficulty and schools will be ranked according to total number of points accumulated by their students. It is still recommended to solve tasks in order since the tasks flow with the storyline, but that is no longer a requirement.
The post Learn cybersecurity skills in NSA’s Codebreaker Challenge appeared first on Department of Computer Science and Electrical Engineering.
]]>
Get hands-on cybersecurity and blockchain skills in NSA’s Codebreaker Challenge NSA’s sixth annual Codebreaker Challenge is a hands-on, cybersecurity engineering challenge in...
https://www.csee.umbc.edu/2018/09/learn-cybersecurity-skills-in-nsas-codebreaker-challenge/
https://beta.my.umbc.edu/api/v0/pixel/news/78824/guest@my.umbc.edu/b5c63a73e1d311c9178ad83678684ddf/api/pixel
csee
cybersecurity
students
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
3
0
true
Sun, 23 Sep 2018 09:45:05 -0400
talk: Cybersecurity as a Team Sport – Understanding Counsel’s Role, 6pm Wed 4/4

Allison Bender J.D.
6:00-8:00pm Wednesday, 4 April 2018
The Universities at Shady Grove
Building III (Camille Kendall Academic Center) Room 4230
9636 Gudelsky Drive, Rockville, Maryland 20850
Directions/Parking
In this presentation by seasoned incident response counsel, Allison Bender, you will gain a risk-informed perspective on the role of counsel in cybersecurity governance and incident response. Also, learn strategies for more effective communication and cooperation with other cybersecurity stakeholders (e.g., IT, IT Security, HR, Communications, business leaders, senior executives and the board); and take away practical tips for prioritizing efforts that help tame the chaos of cybersecurity incident response while maintaining privilege as appropriate.
Allison Bender counsels Fortune 50 companies and startups in a range of industries on cybersecurity and privacy matters in the U.S. and internationally. Drawing from her roots in government, national security, and R&D, she helps clients navigate legal issues associated with emerging technologies and aids clients in strategically managing legal, financial, and reputational cybersecurity risks. Allison translates technical, operational, legal, and policy issues to create practical solutions for clients’ legal challenges. Her cybersecurity and national security preparedness counseling is informed by over 80 incident response efforts. When drafting corporate policies and considering product design options, Allison’s advice is seasoned in the management of breaches involving personal data, intellectual property, payment card information, export controlled technical data, and other regulated information. Her experience also extends to counseling on cybersecurity and national security due diligence in mergers and acquisitions, vendor management, and transactions. From DHS, Allison brings experience in incident response as well as cybersecurity policy, information sharing, liability, and incentives. She was the primary operational legal counsel for the federal response to the Heartbleed vulnerability, the USIS-KeyPoint data breach, and the Healthcare.gov data breach.
Hosts: Dr. Behnam Shariati (*protected email*) and the UMBC Graduate Cybersecurity Association at USG
The UMBC Graduate Cybersecurity Association at USG is an organization created and managed by UMBC Cybersecurity graduate students at Shady Grove. The mission of Cybersecurity Association is to promote the study of Cybersecurity and to raise Cybersecurity awareness and knowledge in the community through panel discussions, conferences, and Cyber competitions. Also, the Cybersecurity Association aspires to create a supportive and positive learning environment in which every member has the opportunity to network, learn, and grow.
The post talk: Cybersecurity as a Team Sport – Understanding Counsel’s Role, 6pm Wed 4/4 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC at Shady Grove Cybersecurity Program Presents Cybersecurity as a Team Sport – Understanding Counsel’s Role Allison Bender J.D. 6:00-8:00pm Wednesday, 4 April 2018 The Universities...
https://www.csee.umbc.edu/2018/03/talk-cybersecurity-team-sport-understanding-counsels-role/
https://beta.my.umbc.edu/api/v0/pixel/news/75116/guest@my.umbc.edu/2f5b7b7cf26b697d3ec816f5139a17d5/api/pixel
csee
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
true
Tue, 27 Mar 2018 22:35:32 -0400
talk: Bill Fisher (NCCOE) on IoT Security @ USG 10/30 6-8PM

The UMBC Cybersecurity program at USG Speaker Series Presents
The Internet of Things (IoT)
With speaker
William (Bill) Fisher, NCCoE Security Engineer
Monday, October 30th 6:00-8:00 pm
The Internet of Things (IoT) is the inevitable result of years of Moore’s law – compact, cheap, chip platforms that can take ordinarily house hold items and make them data generating and collection devices that users can manage with their smart phone, web browser or their favorite automation platform. Physical proximity is no longer needed for things like cameras, door locks or thermostats. Instead users remotely access all of these “things” while on the go, even sharing some of their favorite things with friends and family, who need not own the thing, but simply be granted access through a web portal or mobile application. Like many technology trends before it, the IoT has brought great innovation but also great security challenges. These challenges go beyond standards and technology to economic and market forces that hinder security best practices, even for some of the most basic cyber hygiene. Join Bill Fisher of the National Cybersecurity Center of Excellence for a presentation on these challenges and basic mitigations organizations can put into place to help alleviate the risk that the IoT devices pose to consumers and the enterprise.
Speaker Bio:
Bill Fisher is a security engineer at the National Cybersecurity Center of Excellence (NCCoE). In this role, he is responsible for leading a team of engineers that work collaboratively with industry partners to address cybersecurity business challenges facing the nation. He leads the center’s Attribute Based Access Control (ABAC) project, Mobile Application Single Sign On (SSO) for the Public Safety and First Responder Sector, and is part of the ITL Cybersecurity for IoT program. Prior to his work at the NCCoE, Mr. Fisher was a program security advisor for the System High Corporation in support of the Network Security Deployment division at the Department of Homeland Security. He holds a bachelor’s degree in business administration from American University and a master’s degree in cybersecurity from Johns Hopkins University.
Host: Dr. Behnam Shariati (*protected email*) and UMBC Graduate Cybersecurity Association at USG
The post talk: Bill Fisher (NCCOE) on IoT Security @ USG 10/30 6-8PM appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cybersecurity program at USG Speaker Series Presents The Internet of Things (IoT) With speaker William (Bill) Fisher, NCCoE Security Engineer Building III – Room 4230...
https://www.csee.umbc.edu/2017/10/talk-bill-fisher-nccoe-iot-security-usg-1030-6-8pm/
https://beta.my.umbc.edu/api/v0/pixel/news/72617/guest@my.umbc.edu/85d6e62ef63ac2033b32c576bc185d28/api/pixel
computer-science
csee
cybersecurity
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Mon, 16 Oct 2017 11:47:51 -0400



 The Cyber Dawgs at the CyberForce competition. From left, Charles Nicholas, Anna Staats, Drew Barrett, Grant Spencer, Cyrus Bonyadi, and Seamus Burke. Photo courtesy of Argonne National Lab.
The Cyber Dawgs at the CyberForce competition. From left, Charles Nicholas, Anna Staats, Drew Barrett, Grant Spencer, Cyrus Bonyadi, and Seamus Burke. Photo courtesy of Argonne National Lab. As Americans go to the polls, the voting process and the information environment are still not secure.
As Americans go to the polls, the voting process and the information environment are still not secure. 

