talk: IPv6 and its Security Issues, 5:30 Mon. 4/22

IPv6 and its Security Issues
Neal Ziring, National Security Agency
5:30-6:45 Monday 22 April 2019, Math/Psych 101
CMSC 626 Guest Lecture — all are welcome to attend
In this talk, we will introduce the basics of IPv6 and some of the security issues associated with it. Specifically, we discuss the motivations, history and adoption of IPv6, and current status in the global Internet. We then detail the structure of an IPv6 address and the types of addresses used, and the conceptual model for address assignment in IPv6. The modes of deployment of IPv6, and understanding of how dual-stack mode works, is then provided. We then discuss the basic model for IPv6 control protocols, ICMPv6, and how they support low-level network operations. We then identify IPv6’s place in the network stack, and explain how that does, and does not, affect security. Several basic threats to IPv6 devices and networks will be identified as well as how common network security posture/hygiene can be affected by dual stack operation. Lastly, we identify some key concepts in secure use of IPv6, and discuss the concept of NAT and its use in IPv4 and why IPv6 does not use it.
Mr. Neal Ziring is the Technical Director for the National Security Agency’s Capabilities Directorate, serving as a technical advisor to the Capabilities Director, Deputy Director, and other senior leadership. Mr. Ziring is responsible for setting the technical direction across many parts of the capabilities mission space, including in cyber-security. Mr. Ziring tracks technical activities, promotes technical health of the staff, and acts as liaison to various industry, intelligence, academic, and government partners. Prior to the formation of the Capabilities Directorate, Mr. Ziring served five years as Technical Director of the Information Assurance Directorate. His personal expertise areas include security automation, IPv6, cloud computing, cross-domain information exchange, and data access control, and cyber defense. Prior to coming to NSA in 1988, Neal worked at AT&T Bell Labs. He has BS degrees in Computer Science and Electrical Engineering, and an MS degree in Computer Science, all from Washington University in St. Louis.
The post talk: IPv6 and its Security Issues, 5:30 Mon. 4/22 appeared first on Department of Computer Science and Electrical Engineering.
]]>
IPv6 and its Security Issues Neal Ziring, National Security Agency 5:30-6:45 Monday 22 April 2019, Math/Psych 101 CMSC 626 Guest Lecture — all are welcome to attend In this talk,...
https://www.csee.umbc.edu/2019/04/ipv6-and-its-security-issues-talk-umbc/
https://beta.my.umbc.edu/api/v0/pixel/news/83782/guest@my.umbc.edu/bca50fee3866dcf313e619bbd4ced531/api/pixel
cybersecurity
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Mon, 15 Apr 2019 20:29:34 -0400
Mon, 15 Apr 2019 20:29:34 -0400
talk: Why are memory-corruption bugs still a thing?, 10:30am Mon 4/8, ITE325
Why are memory-corruption bugs still a thing?
The challenges of securing software at an assembly level
Doug Britton
CTO, RunSafe Security Inc.
10:30-11:30 Monday, 8 April 2019, ITE346
Methods to chip away at the danger of memory-corruption bugs have been available for some time. Why has the going-price of memory-corruption-based exploits not spiked? If the methods were have a broad-based result in mitigating exploit vectors, there would be a reduction in supply, causing an increase in prices. Also, there would be a reduction in the pool of people qualified to develop zero-days, allowing them to push the prices up. The data suggest that prices have remained generally stable and attackers are able to move with impunity. What are the challenges to large-scale adoption of memory-corruption based mitigation methods.
Doug Britton serves as Chief Technology Officer and Director of RunSafe Security, Inc. Mr. Britton Co-founded Kaprica Security, Inc., in 2011 and serves as its Chief Executive Officer. Prior to his leadership role in Kaprica, Mr. Britton was a cyber-security focused research and development manager at Lockheed Martin. He has an MBA and MS from University of Maryland and a BS in Computer Science from the University of Illinois.
The post talk: Why are memory-corruption bugs still a thing?, 10:30am Mon 4/8, ITE325 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Why are memory-corruption bugs still a thing? The challenges of securing software at an assembly level Doug Britton CTO, RunSafe Security Inc. 10:30-11:30 Monday, 8 April 2019, ITE346...
https://www.csee.umbc.edu/2019/04/talk-why-are-memory-corruption-bugs-still-a-thing-umbc-cybersecurity/
https://beta.my.umbc.edu/api/v0/pixel/news/83516/guest@my.umbc.edu/52431b447531c3ba39864f7200ff8c47/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Sun, 07 Apr 2019 11:00:05 -0400
talk and demo: Exploiting IoT Vulnerabilities, 11:45-1:00pm Mon 2/18

Exploiting IoT Vulnerabilities
Dr. Yatish Joshi, Senior Engineer, Cisco Systems
11:45am-1:00pm Monday, 18 February 2019, ITE 325-B
The past decade has seen explosive growth in the use and deployment of IoT (Internet of Things) devices. According to Gartner there will be about 20.8 billion IoT devices in use by 2020. These devices are seeing wide spread adoption as they are cheap, easy to use and require little to no maintenance. In most cases, setup simply requires using a web or phone app to configure Wi-Fi credentials. Digital home assistants, security cameras, smart locks, home appliances, smart switches, toys, vacuum cleaners, thermostats, leakage sensors etc are examples of IoT devices that are widely used and deployed in home and enterprise environments.

The threat landscape is constantly evolving and threat actors are always on the prowl for new vulnerabilities they can exploit. With traditional attack methods yielding fewer exploits due to the increased focus on security testing, frequent patches, increased user awareness, Threat actors have turned their attention on IoT devices and are exploiting inherent vulnerabilities in these devices. The vulnerabilities, always ON nature, and autonomous mode of operation allow attackers to spy on users, spoof data, or leverage them as botnet infrastructure to launch devastating attacks on third parties. Mirai, a well known IoT malware utilized hundreds and thousands of enslaved IoT devices to launch DDoS attacks on Dyn affecting access to Netflix, Twitter, Github and many other websites. With the release of the Mirai source code numerous variants of the malware are infecting IoT devices across the world and using them to carry out attacks.
These attacks are made possible because the devices are manufactured without security in mind!. In this talk I will demonstrate how one can hack a widely available off-the-shelf IP Camera and router by exploiting the vulnerabilities present in these devices to get on the network, steal personal data, spy on a user, disrupt operation etc. We will also look at what can be done to mitigate the dangers posed by IOT devices.
So attend hack & defend!
Dr. Yatish Joshi is a software engineer in the Firepower division at Cisco Systems where he works on developing new features for Cisco’s security offerings. Yatish has a PhD in Computer Engineering from UMBC. Prior to Cisco Yatish worked as a lecturer at UMBC, and was a senior software engineer developing TV software at Samsung Electronics. When not working, he enjoys reading spy thrillers and fantasy novels.
The post talk and demo: Exploiting IoT Vulnerabilities, 11:45-1:00pm Mon 2/18 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Exploiting IoT Vulnerabilities Dr. Yatish Joshi, Senior Engineer, Cisco Systems 11:45am-1:00pm Monday, 18 February 2019, ITE 325-B The past decade has seen explosive growth in the use and...
https://www.csee.umbc.edu/2019/02/umbc-talk-exploiting-iot-vulnerabilities-security-internet-of-things/
https://beta.my.umbc.edu/api/v0/pixel/news/81984/guest@my.umbc.edu/9dfa6538945e4c821638d88994576150/api/pixel
computer-engineering
computer-science
cybersecurity
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Fri, 08 Feb 2019 22:21:57 -0500
Sun, 17 Feb 2019 16:00:57 -0500
talk: Using Deep Learning in Identifying Network Intrusions, 10:30am Mon 2/11, UMBC

Using Deep Learning in Identifying Network Intrusions
Dr. Rajeev Agrawal
Information Technology Laboratory
US Army Engineer Research and Development Center
10:30-11:30 Monday, February 11, 2019, ITE325
Deep Learning algorithms have been very successful in computer vision, natural language processing, and speech recognition. However, there is a big challenge in applying it in cyber security domain due to non‐availability of ‘real’ cybersecurity data. Many researchers have tried using synthetic data such as KDD‐NSL or newer UNSW-NB15 network intrusion datasets, however, it is difficult to determine the performance of the proposed research on a dataset captured from an enterprise network. The DoD’s High Performance Computing Modernization Program (HPCMP) operates Defense Research Engineering network (DREN), which has multiple security software and hardware tools installed across the network. A variety of cybersecurity logs are captured using these tools. We use a TensorFlow based framework to analyze DREN’s Bro alert data generated under Cybersecurity Environment for Detection, Analysis and Reporting (CEDAR) project. These alerts are marked as bad or normal by the cybersecurity analysts and used as ground truths. This labeled data is used to measure the performance of our approach in identifying network intrusions. We are able to achieve high level accuracy by tuning hyper-parameters used in any deep learning approach. In this presentation, we will discuss the results of our approach which harnesses the power of HPC systems to train our proposed model.
Dr. Rajeev Agrawal joined Cyber Engineering and Analysis branch (CEAB), Information Technology Laboratory in 2016. He is the Data Science lead of the High Performance Computing Architecture (HPC) for Cyber Situational Awareness (HACSAW) Project. The goal of this project is to analyze the cybersecurity data captured across Defense Research and Engineering Network (DREN). He is also a member of the HPC-based deep learning project team and exploring deep learning applicability in cybersecurity domain. Dr. Agrawal received his Ph.D. in Computer Science with minor in Engineering from Wayne State University in 2009. Prior to joining ITL, he was an Associate Professor in the Department of Computer Systems Technology at North Carolina A&T State University. Dr. Agrawal’s research interests include Deep Learning, Cyber Security, SCADA/ICS, Machine Learning and Pattern Recognition. He has published more than 80 technical papers and book chapters in refereed conferences and journals in these areas. He was selected a Data Science Fellow by the National Consortium of Data Science (NCDS) in 2014. His research has been funded by NSF, US Army, John Deere, ACM, RedHat, National Consortium of Data Science and Michigan State University.
The post talk: Using Deep Learning in Identifying Network Intrusions, 10:30am Mon 2/11, UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
Using Deep Learning in Identifying Network Intrusions Dr. Rajeev Agrawal Information Technology Laboratory US Army Engineer Research and Development Center 10:30-11:30 Monday, February...
https://www.csee.umbc.edu/2019/01/talk-using-deep-learning-in-identifying-network-intrusions-1030am-mon-2-11-umbc/
https://beta.my.umbc.edu/api/v0/pixel/news/81612/guest@my.umbc.edu/e67516e735d4bb31c91bfecf68c17168/api/pixel
computer-science
cybersecurity
data-science
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
true
Thu, 24 Jan 2019 15:58:15 -0500
Thu, 24 Jan 2019 15:58:15 -0500
talk: Legal Aspects of Privacy and Data Protection, 12-1 Fri 11/9

The UMBC Cyber Defense Lab presents
Legal Aspects of Privacy and Data Protection
Razvan Miutescu
Privacy Counsel, Whiteford, Taylor & Preston
12:00–1:00pm Friday, 9 November 2018, ITE 227, UMBC
Privacy and data security continue to be topics of interest for organizations of all sizes. In addition to being concerned about cyber crimes and data breaches occurring more frequently and with higher operational impact, consumers and regulators around the world are focusing on privacy. Individuals are becoming increasingly aware of the value and the use of the information that identifies them or analyzes their conduct and behavior. Privacy laws around the world are becoming stricter. The European Union’s General Data Protection Regulation (GDPR) is viewed as a flagship law that imposes data protection requirements well beyond the borders of the European Economic Area. California recently passed its Consumer Privacy Act, which borrows concepts from the GDPR, leaving no doubt that privacy laws in the United States are also on track to become more complex. In this context, we will discuss practical legal approaches to an organization’s privacy and data security program.
Razvan Miutescu is a technology and information governance attorney with Whiteford, Taylor & Preston. His practice focuses on privacy and data security, information technology transactions and licensing, intellectual property, and data management, including data broker transactions, cloud services, distributed ledgers/blockchain, and related regulatory and compliance matters. Email: *protected email*
Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public.
The post talk: Legal Aspects of Privacy and Data Protection, 12-1 Fri 11/9 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Legal Aspects of Privacy and Data Protection Razvan Miutescu Privacy Counsel, Whiteford, Taylor & Preston 12:00–1:00pm Friday, 9 November 2018, ITE...
https://www.csee.umbc.edu/2018/11/talk-legal-aspects-of-privacy-and-data-protection-12-1-fri-11-9/
https://beta.my.umbc.edu/api/v0/pixel/news/80114/guest@my.umbc.edu/e8a22fb19468481f39cdcfa024b0c615/api/pixel
computer-science
cybersecurity
data-science
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Tue, 06 Nov 2018 12:26:47 -0500
Tue, 06 Nov 2018 12:26:47 -0500
talk: Results of a student study of UMBC computer systems security

The UMBC Cyber Defense Lab presents
Results from the January 2018 SFS Research Study at UMBC
Enis Golaszewski, CSEE, UMBC
12:00-1:00pm Friday, 12 October 2018, ITE 227
January 22-26, 2018, UMBC SFS scholars worked collaboratively to analyze the security of a targeted aspect of the UMBC computer system. The focus of this year’s study was the WebAdmin module that enables users to perform various functions on their accounts, including changing the password. Students identified vulnerabilities involving failure to sanitize user input properly and suggested mitigations. Participants comprised BS, MS, MPS, and PhD students studying computer science, computer engineering, information systems, and cybersecurity, including SFS scholars who transferred from Montgomery College (MC) and Prince George’s Community College (PGCC) to complete their four-year degrees at UMBC. We hope that other universities can benefit from our motivational and educational strategy of cooperating with the university’s IT staff to engage students in active project-based learning centering on focused questions about the university computer system.
Enis Golaszewski is a PhD student and SFS scholar in computer science working with Dr. Sherman on blockchain, protocol analysis, and the security of software-defined networks.
This project was supported in part by the National Science Foundation under SFS grant 1241576.
Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public.
The post talk: Results of a student study of UMBC computer systems security appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Results from the January 2018 SFS Research Study at UMBC Enis Golaszewski, CSEE, UMBC 12:00-1:00pm Friday, 12 October 2018, ITE 227 January 22-26,...
https://www.csee.umbc.edu/2018/10/talk-results-of-a-student-study-of-umbc-computer-systems-security/
https://beta.my.umbc.edu/api/v0/pixel/news/79376/guest@my.umbc.edu/6d0ccf28223fa07d9b9e974e1d9d28cb/api/pixel
computer-science
cybersecurity
students
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Thu, 11 Oct 2018 10:25:13 -0400
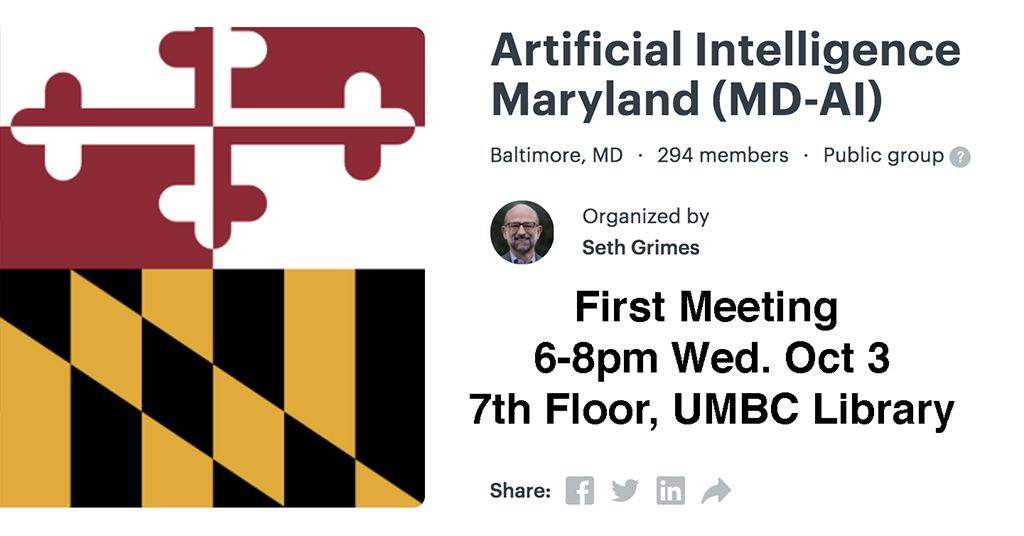
MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library
MD-AI Meetup holds 1st event at UMBC
6-8pm Wed 10/3, 7th floor library
A new Maryland-based meetup interest group has been established for Artificial Intelligence (MD-AI Meetup) and will have its first meeting at UMBC this coming Wednesday (Oct 3) from 6:00-8:00pm in the 7th floor of the library. The first meeting will feature a talk by UMCP Professor Phil Resnik on the state of NLP and an AI research agenda. Refreshments will be provided. The meetup is organized by Seth Grimes and supported by TEDCO, local AI startup RedShred, and the Maryland Tech Council.
If you are interested in attending this and possibly future meetings (which will probably be monthly), go to the Meetup site and join (it’s free) and RSVP to attend this meeting (if there’s still room). If you join the meetup and RSVP, you can see who’s registered to attend.
These meetups are good opportunities to meet and network with people in the area who share interests. It’s a great opportunity for students who are will be looking for internships or jobs in the coming year.
The post MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library appeared first on Department of Computer Science and Electrical Engineering.
]]>
MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library A new Maryland-based meetup interest group has been established for Artificial Intelligence (MD-AI Meetup) and will...
https://www.csee.umbc.edu/2018/09/md-ai-meetup-holds-1st-event-at-umbc-6-8pm-wed-10-3-7th-floor-library/
https://beta.my.umbc.edu/api/v0/pixel/news/78988/guest@my.umbc.edu/9f971bc6300fd641f11e4a00be96e2fb/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
events
nlp
robotics
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Sat, 29 Sep 2018 23:50:53 -0400
Sat, 29 Sep 2018 23:50:53 -0400
talk: Phishing in an Academic Community, a Study of User Susceptibility and Behavior

The UMBC Cyber Defense Lab
Phishing in an Academic Community:
a Study of User Susceptibility and Behavior
Alejandra Diaz
University of Maryland, Baltimore County
12:00–1:00pm, Friday, 14 September 2018, ITE 227
(joint work with Alan T. Sherman Anupam Joshi)
We present an observational study on the relationship between demographic factors and phishing susceptibility at the University of Maryland, Baltimore County (UMBC). From March through May 2018, we performed three experiments that delivered phishing attacks to 450 randomly-selected students on three different days (1,350 students total) to examine user click rates and demographics within UMBC’s undergraduate student population. The participants were initially unaware of the study. We deployed the Billing Problem, Contest Winner, and Expiration Date phishing tactics. Experiment 1 impersonated banking authorities; Experiment 2 enticed users with monetary rewards; and Experiment 3 threatened users with account cancellation.
We found correlations resulting in lowered susceptibility based on college affiliation, academic year progression, cyber training, involvement in cyber clubs or cyber scholarship programs, amount of time spent on the computer, and age demographics. We found no significant correlation between gender and susceptibility. Contrary to our expectations, we observed an inverse correlation between phishing awareness and student resistance to clicking a phishing link. Students who identified themselves as understanding the definition of phishing had a higher susceptibility rate than did their peers who were merely aware of phishing attacks, with both groups of students having a higher susceptibility rate than those with no knowledge whatsoever. Overall, approximately 70% of the students who opened a phishing email clicked on it.
Alejandra Diaz (*protected email*) is a cyber software engineer at Northrop Grumman. She earned her BS in computer science from UMBC with a concentration in cybersecurity in May 2017, and her MS in computer science in August 2018. As a Cyber Scholar and a Society of Women Studying Information Security Scholar, she has a special interest in the human aspects of cybersecurity.
Host: Alan T. Sherman, *protected email*
Support for this research was provided in part by the National Science Foundation under SFS grant 1241576, the U.S. Department of Defense under CAE grant H988230-17-1-0349, and IBM.
The post talk: Phishing in an Academic Community, a Study of User Susceptibility and Behavior appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab Phishing in an Academic Community: a Study of User Susceptibility and Behavior Alejandra Diaz University of Maryland, Baltimore County 12:00–1:00pm, Friday, 14...
https://www.csee.umbc.edu/2018/09/talk-phishing-in-an-academic-community-a-study-of-user-susceptibility-and-behavior/
https://beta.my.umbc.edu/api/v0/pixel/news/78459/guest@my.umbc.edu/239c541864336c1f8378903a30fe9277/api/pixel
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Sun, 09 Sep 2018 13:40:05 -0400
talk: Robot Governance – Institutions and Issues, 10:30 Tue 7/24, ITR346
Robot Governance – Institutions and Issues
Dr. Aaron Mannes, ISHPI Information Technologies
10:30-11:30 Tuesday, 24 July 2018, ITE 346
Inexpensive sensors and information storage and processing have enabled the large-scale production of robots: autonomous systems capable of acting on the world. These systems represent an enormous technological and economic opportunity that will change society in countless and unpredictable ways. They will also bring new policy challenges. This presentation examines the missions the government will need to undertake to address the challenges raised by this new technology, identifies critical gaps the government faces in carrying out these missions, and discusses institutional options to address these gaps.
Dr. Aaron Mannes is the Senior Policy Advisor at ISHPI Information Technologies, where he supports the Apex Data Analytics Engine (DA-E) at the Department of Homeland Security Science and Technology Directorate. In supporting DA-E, Dr. Mannes collaborates on big data projects that support the Homeland Security Enterprise and researches technology policy. He started at DHS as an American Association for the Advancement of Science Policy Fellow in September 2015. From 2004 to 2015, Dr. Mannes was a researcher at the University of Maryland Institute for Advanced Computer Studies (UMIACS) where he was the subject matter expert on terrorism and international affairs collaborating with a team of inter-disciplinary scientists to build computational tools to support decision-makers facing 21st century security and development problems. Dr. Mannes earned his Ph.D. at the University of Maryland’s School of Public Policy in 2014. His dissertation topic was the evolving national security role of the vice president.
Dr. Mannes is the author or co-author of four books on terrorism and has written scores of articles, papers, and book chapters on an array of topics including Middle East affairs, terrorism, technology, and other international security issues for popular and scholarly publications including Politico, Policy Review, The Wall Street Journal, Foreign Policy, The Journal of International Security Affairs, The Huffington Post, The National Interest, The Jerusalem Post, and The Guardian.
This research was conducted with the support of the Apex Data Analytics Engine in the Department of Homeland Security (DHS) Science and Technology Directorate (S&T). In no way should anything stated in this seminar be construed as representing the official position of DHS S&T or any other component of DHS. Opinions and findings expressed in this seminar, as well as any errors and omissions, are the responsibility of the presenter alone.
The post talk: Robot Governance – Institutions and Issues, 10:30 Tue 7/24, ITR346 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Robot Governance – Institutions and Issues Dr. Aaron Mannes, ISHPI Information Technologies 10:30-11:30 Tuesday, 24 July 2018, ITE 346 Inexpensive sensors and information storage...
https://www.csee.umbc.edu/2018/07/talk-robot-governance-institutions-and-issues-1030-tue-7-24-itr346/
https://beta.my.umbc.edu/api/v0/pixel/news/77606/guest@my.umbc.edu/eb929b4718ba6f9af0b285ec85f5cf78/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Mon, 23 Jul 2018 17:27:32 -0400
talk: Big Data, Security and Privacy, 11am Wed 5/16

Big Data, Security and Privacy
Prof. Bhavani Thuraisingham, University of Texas at Dallas
11:00-12:00 Wednesday, 16 May 2018, ITE 459, UMBC
The collection, storage, manipulation and retention of massive amounts of data have resulted in serious security and privacy considerations. Various regulations are being proposed to handle big data so that the privacy of the individuals is not violated. For example, even if personally identifiable information is removed from the data, when data is combined with other data, an individual can be identified. This is essentially the inference and aggregation problem that data security researchers have been exploring for the past four decades. This problem is exacerbated with the management of big data as different sources of data now exist that are related to various individuals.
While collecting massive amounts of data causes security and privacy concerns, big data analytics applications in cyber security is exploding. For example, an organization can outsource activities such as identity management, email filtering and intrusion detection to the cloud. This is because massive amounts of data are being collected for such applications and this data has to be analyzed. The question is, how can the developments in big data management and analytics techniques be used to solve security problems? These problems include malware detection, insider threat detection, and intrusion detection.
To address the challenges of big data security and privacy as well as big data analytics for cyber security applications, we organized a workshop sponsored by the National Science Foundation in September 2014 and presented the results in 2015 at an inter-agency workshop in Washington DC. Since then several developments have been reported on big data security and privacy as well as on big data analytics of cyber security. This presenting will summarize the findings of the workshop and discuss the developments and directions.
Dr. Bhavani Thuraisingham is the Louis A. Beecherl, Jr. Distinguished Professor in the Erik Jonsson School of Engineering and Computer Science at The University of Texas at Dallas (UTD) and the Executive Director of UTD’s Cyber Security Research and Education Institute since October 2004. She is also a Senior Research Fellow at Kings College, University of London (2015-2018) and a New America Cyber Security Policy Fellow (2017-2018). Her current research is on integrating cyber security and data science. Prior to joining UTD she worked at the MITRE Corporation for 16 years including a three-year stint as a Program Director at the NSF. She initiated the Data and Applications Security program at NSF and was a member of the Cyber Trust theme. While at MITRE she was a department head and was also a technical advisor to the DoD, the NSA, the CIA, and the IRS. Prior to that, she worked for the commercial industry for six years including at Honeywell, Inc. She is the recipient of numerous awards including the IEEE CS 1997 Technical Achievement Award, the IEEE ISI 2010 Research Leadership Award, ACM SIGSAC 2010 Outstanding Contributions Award, SDPS 2012 Transformative Achievement Gold Medal, 2013 IBM Faculty Award, ACM CODASPY 2017 Innovative and Lasting Research Contributions Award, IEEE CS Services Computing 2017 Research Innovation Award, and Dallas Business Journal 2017 Women in Technology Award. She is a 2003 Fellow of the IEEE and the AAAS and a 2005 Fellow of the British Computer Society. She has published over 120 journal articles, 250 conference papers, 15 books, has delivered over 130 keynote and featured addresses, and is the inventor of six US patents. She has chaired/co-chaired top tier conferences including the Women in Cyber Security (WiCyS) 2016, ACM CCS 2017, and is serving as the Program co-Chair for IEEE ICDM 2018. She also delivered a featured address at the Women in Data Science (WiDS) conference in 2018. She received her PhD at the University of Wales, Swansea, UK, and the earned higher doctorate (D. Eng) from the University of Bristol, England, UK for her published research in secure data management.
The post talk: Big Data, Security and Privacy, 11am Wed 5/16 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Big Data, Security and Privacy Prof. Bhavani Thuraisingham, University of Texas at Dallas 11:00-12:00 Wednesday, 16 May 2018, ITE 459, UMBC The collection, storage, manipulation and retention...
https://www.csee.umbc.edu/2018/05/talk-umbc-bhavani-thuraisingham-big-data-security-privacy-utd/
https://beta.my.umbc.edu/api/v0/pixel/news/76642/guest@my.umbc.edu/973c2409255673a40cf2a563d30a3181/api/pixel
cybersecurity
data-science
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Tue, 15 May 2018 08:44:32 -0400
Thu, 03 May 2018 08:44:32 -0400