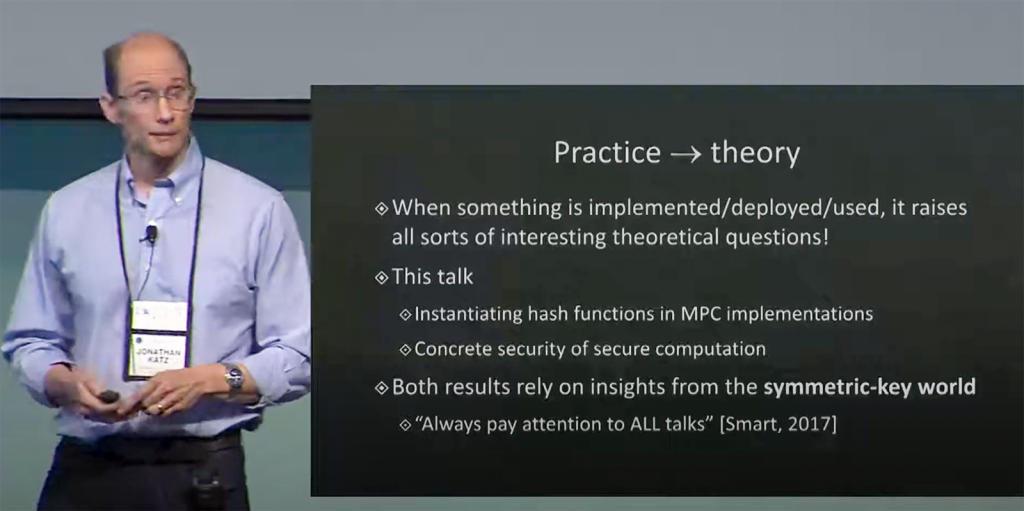
talk: Secure Computation: From Theory to Practice, 12-1pm Oct 30
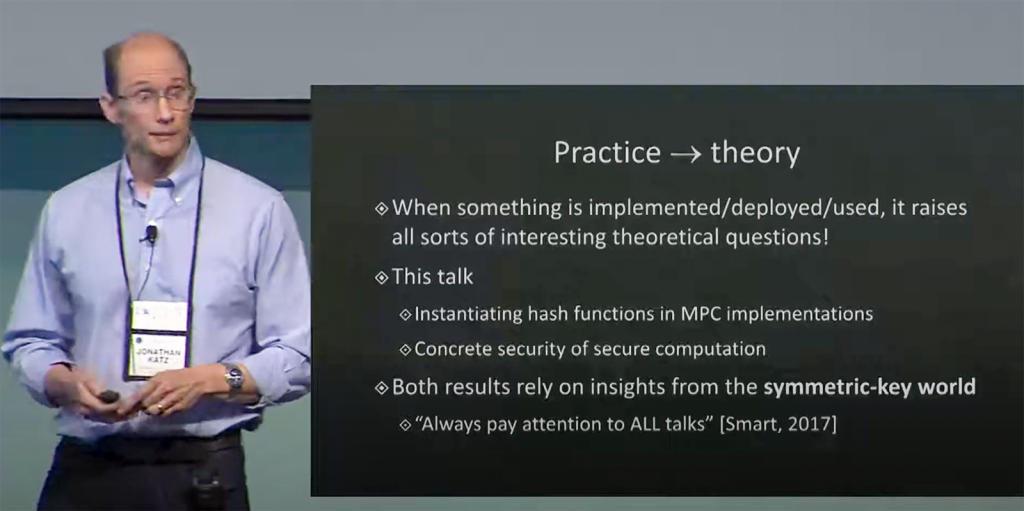
UMBC Cyber Defense Lab presents
Secure Computation: From Theory to Practice
Jonathan Katz
Computer Science Department
University of Maryland, College Park
12:00–1:00 pm EDT, Friday, 30 October 2020
Online via Webex
Protocols for secure multi-party computation (MPC) allow a collection of mutually distrusting parties to compute a function of their private inputs without revealing anything else about their inputs to each other. Secure computation was shown to be feasible 35 years ago, but only in the past decade has its efficiency been improved to the point where it has been implemented and, more recently, begun to be used. This real-world deployment of secure computation suggests new applications and raises new questions.
This talk will survey some recent work at the intersection of the theory and practice of MPC, focusing on a surprising application to the construction of Picnic, a “post-quantum” signature scheme currently under consideration by NIST for standardization.
Jonathan Katz is a faculty member in the department of computer science at the University of Maryland, College Park, where he formerly served as director of the Maryland Cybersecurity Center for over five years. He is an IACR Fellow, was named a University of Maryland distinguished scholar-teacher in 2017-2018, and received the ACM SIGSAC Outstanding Contribution Award in 2019.
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public.
Upcoming CDL Meetings: Nov. 13, TBA, [possibly: David R Imbordino (NSA), Security of the 2020 presidential election]; Dec. 11, TBA, [possibly: Peter A. H. Peterson (Univ. of Minnesota Duluth), Adversarial Thinking]
The post talk: Secure Computation: From Theory to Practice, 12-1pm Oct 30 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Defense Lab presents Secure Computation: From Theory to Practice Jonathan Katz Computer Science Department University of Maryland, College Park 12:00–1:00 pm EDT, Friday, 30...
https://www.csee.umbc.edu/2020/10/talk-secure-computation-from-theory-to-practice-12-1pm-oct-30/
https://beta.my.umbc.edu/api/v0/pixel/news/96902/guest@my.umbc.edu/d095dd467d54d3508b78e08059ead114/api/pixel
csee
cybersecurity
events
news
quantum-computing
research
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sat, 24 Oct 2020 13:33:48 -0400
Sat, 10 Oct 2020 13:33:00 -0400
talk: BVOT, Self-Tallying Boardroom Voting with Oblivious Transfer; 12-1pm 11/6

BVOT is a self-tallying boardroom voting protocol with ballot secrecy, fairness (no tally info. available before polls close), and dispute-freeness (voters can see that all voters followed the protocol).
UMBC Cyber Defense Lab
BVOT: Self-Tallying Boardroom Voting with Oblivious Transfer
Farid Javani, CSEE, UMBC
12:00–1:00pm, Friday, 6 November 2020
(Joint work with Alan T. Sherman)
A boardroom election is an election with a small number of voters carried out with public communications. We present BVOT, a self-tallying boardroom voting protocol with ballot secrecy, fairness (no tally information is available before the polls close), and dispute-freeness (voters can observe that all voters correctly followed the protocol).
BVOT works by using a multiparty threshold homomorphic encryption system in which each candidate is associated with a masked unique prime. Each voter engages in an oblivious transfer with an untrusted distributor: the voter selects the index of a prime associated with a candidate and receives the selected prime in a masked form. The voter then casts their vote by encrypting their masked prime and broadcasting it to everyone. The distributor does not learn the voter’s choice, and no one learns the mapping between primes and candidates until the audit phase. By hiding the mapping between primes and candidates, BVOT provides voters with insufficient information to carry out effective cheating. The threshold feature prevents anyone from computing any partial tally—until everyone has voted. Multiplying all votes, their decryption shares, and the unmasking factor yields a product of the primes each raised to the number of votes received.
In contrast to some existing boardroom voting protocols, BVOT does not rely on any zero-knowledge proof; instead, it uses oblivious transfer to assure ballot secrecy and correct vote casting. Also, BVOT can handle multiple candidates in one election. BVOT prevents cheating by hiding crucial information: an attempt to increase the tally of one candidate might increase the tally of another candidate. After all votes are cast, any party can tally the votes.
Farid Javani is a Ph.D. candidate in computer science at UMBC, working with Alan Sherman. His research interests include algorithms, security, applied cryptography, and distributed systems. He is the manager of the Enterprise Architecture team at CCC Information Services in Chicago. email: *protected email*
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1:00 pm. All meetings are open to the public. Upcoming CDL Meetings: Oct. 30, Jonathan Katz (UMCP), [possibly on secure distributed computation]; Nov. 13, TBA, [possibly: David R Imbordino (NSA), Security of the 2020 presidential election]; and Dec. 11, TBA, [possibly: Peter A. H. Peterson (Univ. of Minnesota Duluth), Adversarial Thinking]
The post talk: BVOT, Self-Tallying Boardroom Voting with Oblivious Transfer; 12-1pm 11/6 appeared first on Department of Computer Science and Electrical Engineering.
]]>
BVOT is a self-tallying boardroom voting protocol with ballot secrecy, fairness (no tally info. available before polls close), and dispute-freeness (voters can see that all voters followed the...
https://www.csee.umbc.edu/2020/10/talk-bvot-self-tallying-boardroom-voting-with-oblivious-transfer-12-1pm-11-6/
https://beta.my.umbc.edu/api/v0/pixel/news/96548/guest@my.umbc.edu/ca88798fe3c6bb9e5e3e69188b2b1c80/api/pixel
computer-science
cybersecurity
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Sun, 11 Oct 2020 17:46:41 -0400
Mon, 19 Oct 2020 17:46:00 -0400
talk: Tracking Hacking: The Disturbing Proliferation of Commercial Spyware, 1pm Oct. 23

Distinguished Speaker Series
The UMBC Center for Cybersecurity and
Dept. of Computer Science & Electrical Engineering
Tracking Hacking: The Disturbing Proliferation of Commercial Spyware
Ronald J. Deibert, Ph.D.
Prof. of Political Science, Director of Citizen Lab
Munk School of Global Affairs and Public Policy, University of Toronto
1–2:00 pm Friday, 23 October 2020
Webex, Mtg. #: 120 360 5372 Password: 4ExV8dCM3J2
Political struggles in and through the global Internet and related technologies are entering into a particularly dangerous phase for openness, security, and human rights. A growing number of governments and private companies have turned to “offensive” operations, with means ranging from sophisticated and expensive to homegrown and cheap. A large and largely unregulated market for commercial surveillance technology is finding willing clientele among the world’s least accountable regimes. Powerful spyware tools are used to infiltrate civil society networks, targeting the devices of journalists, human rights defenders, minority movements, and political opposition, often with lethal consequences. Drawing from the last decade of research at the University of Toronto’s Citizen Lab, I will provide an overview of these disturbing trends and discuss some pathways to repairing and restoring the Internet as a sphere that supports, rather than diminishes, human rights.
Ronald J. Deibert is Professor of Political Science and Director of the Citizen Lab at the Munk School of Global Affairs and Public Policy, University of Toronto. The Citizen Lab undertakes interdisciplinary research at the intersection of global security, ICTs, and human rights. The research outputs of the Citizen Lab are routinely covered in global media, including over two dozen reports receiving front-page coverage in the New York Times, Washington Post, and other media over the last decade. Deibert is the author of Black Code: Surveillance, Privacy, and the Dark Side of the Internet (Random House: 2013) Reset: Reclaiming the Internet for Civil Society (House of Anansi: 2020) as well as numerous books, chapters, articles, and reports on Internet censorship, surveillance, and cybersecurity. In 2013, he was appointed to the Order of Ontario and awarded the Queen Elizabeth II Diamond Jubilee medal, for being “among the first to recognize and take measures to mitigate growing threats to communications rights, openness and security worldwide.”
The post talk: Tracking Hacking: The Disturbing Proliferation of Commercial Spyware, 1pm Oct. 23 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Distinguished Speaker Series The UMBC Center for Cybersecurity and Dept. of Computer Science & Electrical Engineering Tracking Hacking: The Disturbing Proliferation of Commercial Spyware...
https://www.csee.umbc.edu/2020/10/tracking-hacking-the-disturbing-proliferation-of-commercial-spyware/
https://beta.my.umbc.edu/api/v0/pixel/news/96462/guest@my.umbc.edu/6441a83676b8d7d7b866889079311d73/api/pixel
cybersecurity
research
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Wed, 07 Oct 2020 15:13:47 -0400
talk: Exploding Blockchain Myths, 5:30pm Tue 10/13
UMBC Data Science Meetup Talk
Exploding Blockchain Myths
Maria Vachino and Dr. James P. Howard
5:30-7:00pm Tuesday, 13 October 2020
In this talk, Maria Vachino from Easy Dynamics and Dr. James P. Howard from APL will provide an overview of what blockchain is and isn’t, focusing on non-cryptocurrency use cases, will explain the results of their research for the DHS S&T Cybersecurity Directorate, and will provide insight into the value (or lack therefore) of the technology.
References:
• https://ieeexplore.ieee.org/document/8965252/
• http://jitm.ubalt.edu/XXX-3/article3.pdf
Maria Vachino is the Director of Digital Identity at Easy Dynamics where she is focused on Identity Credential & Access Management (ICAM) technologies, policies, & standards, Cybersecurity, and IT modernization for the US Federal Government. She started investigating applications for blockchain technology in 2015 as the Technical and Government Engagement Lead for the DHS S&T Cyber Security Directorate’s Identity Management Research & Development Program while a member of the Senior Professional Staff at the Johns Hopkins Applied Physics Lab. Maria has a BS in Computer Science from UMBC and an MS in Cybersecurity.
Dr. James P. Howard, II (UMBC Ph.D. ’14) is a scientist at the Johns Hopkins Applied Physics Laboratory. Previously, he was a consultant to numerous government agencies, including the Securities and Exchange Commission, the Executive Office of the President, and the United States Department of Homeland Security, and worked for the Board of Governors of the Federal Reserve System as an internal consultant on scientific computing. He is a passionate educator, teaching mathematics and statistics at the University of Maryland Global Campus since 2010 and has taught public management at Central Michigan University, Penn State, and the University of Baltimore. His most recent work has modeled the spread of infectious respiratory diseases and Ebolavirus, predicted global disruptive events, researched using blockchain for government services, and created devices for rescuing victims of building collapse. He is the author of two books.
The post talk: Exploding Blockchain Myths, 5:30pm Tue 10/13 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Data Science Meetup Talk Exploding Blockchain Myths Maria Vachino and Dr. James P. Howard 5:30-7:00pm Tuesday, 13 October 2020 In this talk, Maria Vachino from Easy Dynamics and Dr....
https://www.csee.umbc.edu/2020/10/talk-exploding-blockchain-myths-530pm-tue-10-13/
https://beta.my.umbc.edu/api/v0/pixel/news/96415/guest@my.umbc.edu/097b844dc5ba2983199d05604cc47309/api/pixel
alumni
computer-science
cybersecurity
data-science
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Tue, 06 Oct 2020 20:58:09 -0400
Tue, 06 Oct 2020 20:58:09 -0400
talk: Psychometric Evaluation of the Cybersecurity Concept Inventory, 12-1 Fri 9/18

The UMBC Cyber Defense Lab presents
Psychometric Evaluation of the Cybersecurity Concept Inventory
Seth Poulsen
Computer Science
University of Illinois at Urbana-Champaign
12:00noon–1pm, Friday, September 18, 2020
https://umbc.webex.com/meet/sherman
Joint work with Geoffrey Herman, Alan Sherman, Linda Oliva, Peter Peterson, Enis Golaszewski, Travis Scheponik, and Akshita Gorti.
We present a psychometric evaluation of a revised version of the Cybersecurity Concept Inventory (CCI) completed by 355 students from 29 colleges and universities. The CCI is a conceptual test of understanding created to enable research on instruction quality in cybersecurity education. This work extends previous expert review and small-scale pilot testing of the CCI. Results show that the CCI aligns with a curriculum many instructors expect from an introductory cybersecurity course, and that it is a valid and reliable tool for assessing what cybersecurity conceptual knowledge students learned.
Seth Poulsen is a PhD candidate in computer science at the University of Illinois at Urbana-Champaign. I’m interested in Computing Education, Programming Language design and implementation, Math Education, and any interesting intersections of the above. Previously, he was a Software Engineer at Amazon.com, working on Kindle Web Rendering and the Kindle Lite Android app. email: *protected email*,
Support for this research was provided in part by the U.S. Department of Defense under CAE-R grants H98230-15-1-0294, H98230-15-1-0273, H98230-17-1-0349, H98230-17-1-0347; and by the National Science Foundation under UMBC SFS grants DGE-1241576, 1753681, and SFS Capacity Grants DGE-1819521, 1820531. For more on the educational Cybersecurity Assessment Tools (CATS) Project: https://arxiv.org/pdf/2004.05248.pdf
Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public. Upcoming CDL Meetings:
- Oct. 2, TBA [possibly: security of payment infrastructure]
- Oct. 16, TBA [possibly: Jonathan Katz (GMU)]
- Oct. 30, TBA
- Nov. 13, TBA, [possibly: David R Imbordino (NSA), Security of the 2020 presidential election]
- Dec. 11, TBA, [possibly: Peter A. H. Peterson (Univ. of Minnesota Duluth), Adversarial Thinking]
The post talk: Psychometric Evaluation of the Cybersecurity Concept Inventory, 12-1 Fri 9/18 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Psychometric Evaluation of the Cybersecurity Concept Inventory Seth Poulsen Computer Science University of Illinois at Urbana-Champaign 12:00noon–1pm,...
https://www.csee.umbc.edu/2020/09/talk-psychometric-evaluation-of-the-cybersecurity-concept-inventory-12-1-fri-9-18/
https://beta.my.umbc.edu/api/v0/pixel/news/95860/guest@my.umbc.edu/e7176914894654fe973ff4ba27514c1a/api/pixel
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Wed, 16 Sep 2020 18:51:11 -0400
talk: Matt Green on Privacy-Preserving Cryptographic Protocols, 12-1 EDT Fri. 9/4, online
The UMBC Cyber Defense Lab presents
Privacy-Preserving Cryptographic Protocols
Professor Matthew Green
Johns Hopkins University
We investigate the problem of automating the development of adaptive chosen-ciphertext attacks on systems that contain vulnerable format oracles. Rather than simply automate the execution of known attacks, we consider a more challenging problem: to programmatically derive a novel attack strategy, given only a machine-readable description of the plaintext verification function and the malleability characteristics of the encryption scheme. We present a new set of algorithms that use SAT and SMT solvers to reason deeply over the design of the system, producing an automated attack strategy that can decrypt protected messages entirely.
Matthew Green is an Associate Professor at the Johns Hopkins Information Security Institute. His research includes techniques for privacy-enhanced information storage, anonymous payment systems, and bilinear map- based cryptography. He is one of the creators of the Zerocash protocol, which is used by the Zcash cryptocurrency, and a founder of an encryption startup Zeutro. He was formerly a partner in Independent Security Evaluators, a custom security evaluation and design consultancy, and currently consults independently. From 1999-2003, he served as a senior technical staff member at AT&T Laboratories/Research in Florham Park, NJ. email: *protected email* Dr. Green writes a popular blog on applied cryptography, A Few Thoughts on Cryptographic Engineering, A Few Thoughts on Cryptographic Engineering
Host: Alan T. Sherman,, *protected email* Support for this event was provided in part by the NSF under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL Meetings:
- The Cyber Defense Lab hosts biweekly talks on Fridays 12-1pm.
The post talk: Matt Green on Privacy-Preserving Cryptographic Protocols, 12-1 EDT Fri. 9/4, online appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Privacy-Preserving Cryptographic Protocols Professor Matthew Green Johns Hopkins University 12:00-1:00 pm Friday, 4 September 2020...
https://www.csee.umbc.edu/2020/09/talk-matt-green-on-privacy-preserving-cryptographic-protocols/
https://beta.my.umbc.edu/api/v0/pixel/news/95450/guest@my.umbc.edu/3f30b5b4cc036e2cb3b597c9c394a3ac/api/pixel
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Thu, 03 Sep 2020 23:03:53 -0400
Thu, 03 Sep 2020 23:03:53 -0400
talk: Identifying and Addressing Concerning Behavior in the Digital Age, 12-1 Fri 5/8

The UMBC Cyber Defense Lab presents
Identifying and Addressing Concerning
Behavior in the Digital Age
Jason W. Wells
Graduate Student, Cybersecurity MPS
University of Maryland, Baltimore County
12:00–1pm Friday, 8 May 2020, webex
The United States Secret Service (USSS) is widely known as the premier law enforcement agency that is charged with protecting some of the most important political figures in the world. Some of these protectees include the President of the United States, the Vice-President, the First Family and Second Family, and Heads of State visiting the United States, to name a few. A major part of the protective mission of the USSS is focused around “protective intelligence,” where agents are trained to identify concerning and threatening behavioral indicators in others, and then to address those issues in a proactive and positive manner and ensure that the community is safe from harm. This proactive methodology has been researched and applied for decades and has a very high rate of success. Now, other law enforcement agencies throughout the country have started to apply this training to their agents and officers. Can these methodologies be used and/or modified to recognize threats in cyberspace as well?
Jason Wells is a former special agent with the United States Secret Service, where he served for nine years from 2005 – 2014. During that time, Mr. Wells was extensively trained in identifying and addressing threat-related and concerning behavioral indicators, and how to address those behaviors in a positive and proactive manner. In 2016, Mr. Wells published his first book Our Path to Safety: A U.S. Secret Service Agent’s Guide to Creating Safe Communities (ISBN-13: 978-0-9982488-0-6) on how the community can identify these behavioral conditions in the same way that federal law enforcement does every day. Mr. Wells earned his undergraduate degree from the Virginia Military Institute and his first graduate degree from Henley-Putnam University in Strategic Security and Protection Management in 2014. Additionally, Mr. Wells has published 11 editorial articles in print media on improving safety and security methodologies in schools and businesses. Currently, he is an SFS scholarship graduate student at UMBC with plans to complete his degree in spring 2020. He and his wife, Blythe, have two children and have lived in Baltimore County since 2008.
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL Meetings: May 22, Spring SFS Meeting at UMBC, 9:30am-2pm, via WebEx.
The post talk: Identifying and Addressing Concerning Behavior in the Digital Age, 12-1 Fri 5/8 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Identifying and Addressing Concerning Behavior in the Digital Age Jason W. Wells Graduate Student, Cybersecurity MPS University of Maryland, Baltimore...
https://www.csee.umbc.edu/2020/05/talk-identifying-and-addressing-concerning-behavior-in-the-digital-age-12-1-fri-5-8/
https://beta.my.umbc.edu/api/v0/pixel/news/92799/guest@my.umbc.edu/c57f1df02979ddc3394e4b7f0292a546/api/pixel
cybersecurity
events
news
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
false
Sun, 03 May 2020 20:41:58 -0400
Sun, 03 May 2020 20:41:58 -0400
talk: Cybersecurity during COVID-19 and other emergencies, 12-1 Tue May 5
The UMBC Center for Cybersecurity (UCYBR) Presents
Cybersecurity during COVID-19 and other emergencies
Dr. Richard Forno
Senior Lecturer, Computer Science & Electrical Engineering
Director, UMBC Graduate Cybersecurity Program & Assistant Director, UMBC Center for Cybersecurity
12–1 pm Tuesday, 5 May 2020
online via webex
‘Cyber’ touches many, if not all, parts of society and organizations. However, even in 2020, cybersecurity often still is seen as exclusively a function of IT and not a function of enterprise mission assurance or operational resiliency. Accordingly, operational performance can be compromised by a failure to consider, if not embrace, cybersecurity principles and concerns during crisis planning – which can significantly impede effective crisis response and incident management during actual events and make a bad situation even worse. This talk will discuss the role of cybersecurity and cybersecurity thinking within crisis management and incident handling, with a particular emphasis on maintaining operational resiliency and mission assurance during the ongoing COVID-19 pandemic.
Dr. Richard Forno is a Senior Lecturer in the UMBC Department of Computer Science and Electrical Engineering, where he directs the UMBC Graduate Cybersecurity Program and serves as the Assistant Director of UMBC’s Center for Cybersecurity. Prior to joining UMBC in 2010, his twenty-year career in operational cybersecurity spanned the government, military, and private sector, including helping build a formal cybersecurity program for the US House of Representatives, serving as the first Chief Security Officer for Network Solutions (then, the global center of the internet DNS system), consulting to Fortune 100 companies, and more. From 2005-12 he was a Visiting Scientist at the Software Engineering Institute at Carnegie Mellon University, where he taught courses on incident handling for the CERT Coordination Center (CERT/CC).
The post talk: Cybersecurity during COVID-19 and other emergencies, 12-1 Tue May 5 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Center for Cybersecurity (UCYBR) Presents Cybersecurity during COVID-19 and other emergencies Dr. Richard Forno Senior Lecturer, Computer Science & Electrical Engineering Director,...
https://www.csee.umbc.edu/2020/04/talk-cybersecurity-during-covid-19-and-other-emergencies/
https://beta.my.umbc.edu/api/v0/pixel/news/92644/guest@my.umbc.edu/4dedfebfbd0eb9440f728609f77e20f9/api/pixel
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Mon, 27 Apr 2020 18:13:32 -0400
Mon, 27 Apr 2020 18:13:32 -0400
Talk: Lance Hoffman (GWU) Cyber Policy Challenges, 12-1pm 4/24 online

The UMBC Cyber Defense Lab presents
Cyber Policy Challenges
Lance J. Hoffman
Distinguished Professor, George Washington University
12–1:00 pm, Friday, 24 April 2020
System attackers and defenders operate on a constantly changing battlefield, and some of the more serious conflicts involving nation-states could be considered acts of war, though we are still in the early stages of defining war in cyberspace. Policies for security and privacy can vary wildly, and have important personal, national, and global consequences for privacy, free speech, censorship, and other issues. Things get even more complicated with the advent of the Internet of Things, where (mostly unsophisticated) users may think they have more control than they actually do and can make bad mistakes. Various ethical issues related to the development of these systems, including bias in artificial intelligence and what harm to choose when harm is unavoidable have only started to be examined. This talk will provide both historical context and some discussion of topical issues such as Zoombombing and the security of electronic voting systems as compared to mail ballots and traditional voting.
Professor Lance J. Hoffman is the author or editor of numerous articles and five books on computer security and privacy. He developed the first regularly offered course on computer security at the University of California, Berkeley in 1970. A Fellow of the Association for Computing Machinery and a member of the Cyber Security Hall of Fame, Dr. Hoffman institutionalized the ACM Conference on Computers, Freedom, and Privacy. He has served on a number of Advisory Committees including those of Federal Trade Commission and the Department of Homeland Security and has testified before Congress on security and privacy-related issues. He is the principal investigator of the CyberCorps program at GWU. Dr. Hoffman earned his Ph. D. in Computer Science from Stanford University, after a B.S. in Mathematics from Carnegie Mellon University.
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL meetings: May 8, Jason Wells (UMBC SFS scholar) law enforcement; May 22, Spring SFS Meeting at UMBC, 9:30am-2pm, ITE456
The post Talk: Lance Hoffman (GWU) Cyber Policy Challenges, 12-1pm 4/24 online appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Cyber Policy Challenges Lance J. Hoffman Distinguished Professor, George Washington University 12–1:00 pm, Friday, 24 April 2020 remotely via WebEx...
https://www.csee.umbc.edu/2020/04/talk-lance-hoffman-gwu-cyber-policy-challenges/
https://beta.my.umbc.edu/api/v0/pixel/news/92101/guest@my.umbc.edu/82505162580cdf42c92f5a6e2c15d321/api/pixel
cybersecurity
news
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sat, 11 Apr 2020 12:15:46 -0400
Sat, 11 Apr 2020 12:15:46 -0400
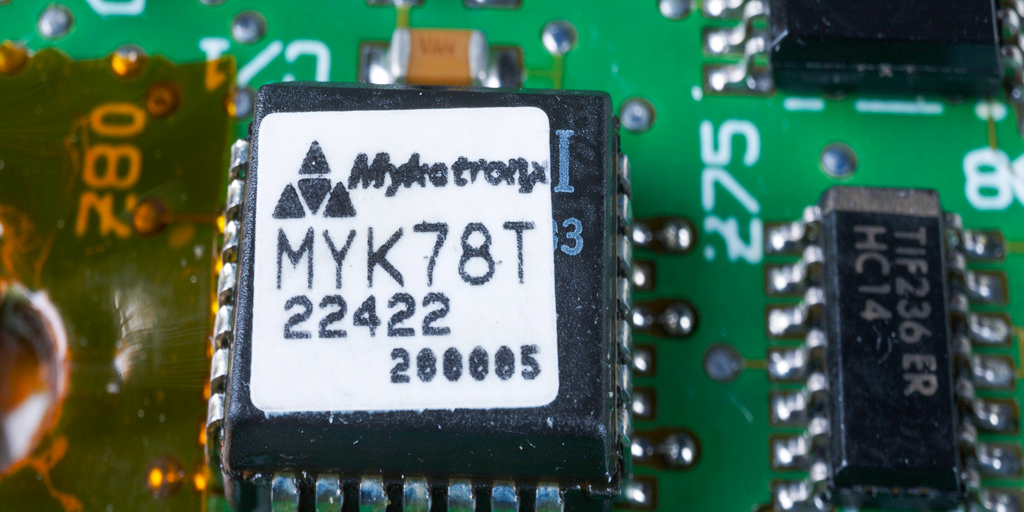
online talk: Opal Hard Drives for Ransomware Resilience

The UMBC Cyber Defense Lab presents
Opal Hard Drives for Ransomware Resilience
Russ Fink, Ph.D.
Senior Staff, the Johns Hopkins University / Applied Physics Laboratory
Ransomware is crippling industry and government alike. Paying the ransom doesn’t guarantee you’ll get your files back, but it funds the criminals who will continue on. Restoring from traditional network backups takes time, and never gets you back to the system you had before the attack. In response, we have developed a resilient, local malware restore and recovery capability, capable of quickly restoring OS images onto “bare metal” after an attack or misconfiguration, useful for many applications.
I will discuss the technical details, including a description of the Opal hard drive specification, the Trusted Computing Group’s Trusted Platform Module (TPM), and how we secure secrets needed for WUBU – Wake-Up-Back-Up. I’ll talk through some of the open-source technologies that we used to build our solution. WebEx willing, I will give a live demonstration of a ShinoLocker ransomware infection, followed by an “as if nothing ever happened” recovery that takes only ten minutes.
Russ Fink is a senior staff member at the Johns Hopkins University / Applied Physics Laboratory. His research interests include computational private information retrieval, trusted computing applications, applied cryptography, and enterprise and mission cyber resiliency techniques. He earned a Ph.D. in computer science from UMBC in 2010 working with Dr. Alan Sherman. email: *protected email*
Host: Alan T. Sherman, *protected email*. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL Meetings:
- Apr 24, Lance Hoffman (GWU), policy
- May 8, Jason Wells (UMBC SFS scholar), law enforcement
- May 22, Spring SFS Meeting at UMBC, 9:30am-2pm, ITE 456
The post online talk: Opal Hard Drives for Ransomware Resilience appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Opal Hard Drives for Ransomware Resilience Russ Fink, Ph.D. Senior Staff, the Johns Hopkins University / Applied Physics Laboratory 12:00–1 pm, Friday, 10...
https://www.csee.umbc.edu/2020/04/online-talk-opal-hard-drives-for-ransomware-resilience/
https://beta.my.umbc.edu/api/v0/pixel/news/92012/guest@my.umbc.edu/f3fa76f5ca100a5158da1e1a80870c9e/api/pixel
computer-science
cybersecurity
news
research
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Thu, 09 Apr 2020 11:33:17 -0400
Thu, 09 Apr 2020 11:33:17 -0400
 BVOT is a self-tallying boardroom voting protocol with ballot secrecy, fairness (no tally info. available before polls close), and dispute-freeness (voters can see that all voters followed the protocol).
BVOT is a self-tallying boardroom voting protocol with ballot secrecy, fairness (no tally info. available before polls close), and dispute-freeness (voters can see that all voters followed the protocol).