talk: Matt Green on Privacy-Preserving Cryptographic Protocols, 12-1 EDT Fri. 9/4, online
The UMBC Cyber Defense Lab presents
Privacy-Preserving Cryptographic Protocols
Professor Matthew Green
Johns Hopkins University
We investigate the problem of automating the development of adaptive chosen-ciphertext attacks on systems that contain vulnerable format oracles. Rather than simply automate the execution of known attacks, we consider a more challenging problem: to programmatically derive a novel attack strategy, given only a machine-readable description of the plaintext verification function and the malleability characteristics of the encryption scheme. We present a new set of algorithms that use SAT and SMT solvers to reason deeply over the design of the system, producing an automated attack strategy that can decrypt protected messages entirely.
Matthew Green is an Associate Professor at the Johns Hopkins Information Security Institute. His research includes techniques for privacy-enhanced information storage, anonymous payment systems, and bilinear map- based cryptography. He is one of the creators of the Zerocash protocol, which is used by the Zcash cryptocurrency, and a founder of an encryption startup Zeutro. He was formerly a partner in Independent Security Evaluators, a custom security evaluation and design consultancy, and currently consults independently. From 1999-2003, he served as a senior technical staff member at AT&T Laboratories/Research in Florham Park, NJ. email: *protected email* Dr. Green writes a popular blog on applied cryptography, A Few Thoughts on Cryptographic Engineering, A Few Thoughts on Cryptographic Engineering
Host: Alan T. Sherman,, *protected email* Support for this event was provided in part by the NSF under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL Meetings:
- The Cyber Defense Lab hosts biweekly talks on Fridays 12-1pm.
The post talk: Matt Green on Privacy-Preserving Cryptographic Protocols, 12-1 EDT Fri. 9/4, online appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Privacy-Preserving Cryptographic Protocols Professor Matthew Green Johns Hopkins University 12:00-1:00 pm Friday, 4 September 2020...
https://www.csee.umbc.edu/2020/09/talk-matt-green-on-privacy-preserving-cryptographic-protocols/
https://beta.my.umbc.edu/api/v0/pixel/news/95450/guest@my.umbc.edu/3f30b5b4cc036e2cb3b597c9c394a3ac/api/pixel
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Thu, 03 Sep 2020 23:03:53 -0400
Thu, 03 Sep 2020 23:03:53 -0400
online talk: Opal Hard Drives for Ransomware Resilience

The UMBC Cyber Defense Lab presents
Opal Hard Drives for Ransomware Resilience
Russ Fink, Ph.D.
Senior Staff, the Johns Hopkins University / Applied Physics Laboratory
Ransomware is crippling industry and government alike. Paying the ransom doesn’t guarantee you’ll get your files back, but it funds the criminals who will continue on. Restoring from traditional network backups takes time, and never gets you back to the system you had before the attack. In response, we have developed a resilient, local malware restore and recovery capability, capable of quickly restoring OS images onto “bare metal” after an attack or misconfiguration, useful for many applications.
I will discuss the technical details, including a description of the Opal hard drive specification, the Trusted Computing Group’s Trusted Platform Module (TPM), and how we secure secrets needed for WUBU – Wake-Up-Back-Up. I’ll talk through some of the open-source technologies that we used to build our solution. WebEx willing, I will give a live demonstration of a ShinoLocker ransomware infection, followed by an “as if nothing ever happened” recovery that takes only ten minutes.
Russ Fink is a senior staff member at the Johns Hopkins University / Applied Physics Laboratory. His research interests include computational private information retrieval, trusted computing applications, applied cryptography, and enterprise and mission cyber resiliency techniques. He earned a Ph.D. in computer science from UMBC in 2010 working with Dr. Alan Sherman. email: *protected email*
Host: Alan T. Sherman, *protected email*. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL Meetings:
- Apr 24, Lance Hoffman (GWU), policy
- May 8, Jason Wells (UMBC SFS scholar), law enforcement
- May 22, Spring SFS Meeting at UMBC, 9:30am-2pm, ITE 456
The post online talk: Opal Hard Drives for Ransomware Resilience appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Opal Hard Drives for Ransomware Resilience Russ Fink, Ph.D. Senior Staff, the Johns Hopkins University / Applied Physics Laboratory 12:00–1 pm, Friday, 10...
https://www.csee.umbc.edu/2020/04/online-talk-opal-hard-drives-for-ransomware-resilience/
https://beta.my.umbc.edu/api/v0/pixel/news/92012/guest@my.umbc.edu/f3fa76f5ca100a5158da1e1a80870c9e/api/pixel
computer-science
cybersecurity
news
research
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Thu, 09 Apr 2020 11:33:17 -0400
Thu, 09 Apr 2020 11:33:17 -0400
Online Talks Double Feature: Blockchain and Network Defense, 12-2 Fri 3/27, UMBC
UMBC will hold a double feature with two online security-oriented talks from 12:00 pm to 2:00 pm EDT on Friday, March 27. Both talks will be shared via Webex.

From 1:00-2:00 pm, Professor Dr. John Mitchell of Stanford University will give a Lockheed Martin Distinguished lecture on “Will Blockchain Change Everything“. Join the presentation online at 1:00 pm EDT at https://umbc.webex.com/meet/joshi.
Far from serving only as a foundation for cryptocurrency, blockchain technology provides a general framework for trusted distributed ledgers. Over the past few years, their popularity has grown tremendously, as shown by the number of companies and efforts associated with the Linux Foundation’s Hyperledger project, for example. From a technical standpoint, a blockchain combines a storage layer, networking protocols, a consensus layer, and a programmable transaction layer, leveraging cryptographic operations. The distributed state machine paradigm provides atomicity and transaction rollback, while consensus supports distributed availability as well as certain forms of fair access. From an applications perspective, blockchains appeal to distributed networks of independent agents, as arise in supply chain, credentialing, and decentralized financial services. The talk will look at the potential for radical change as well as specific technical challenges associated with verifiable consensus protocols and trustworthy smart contracts.

From 12:00-1:00 pm EDT Col. Dan Yaroslaski, a former operations officer at the Marine Forces Cyberspace Command will talk on “Hard-Learned Lesson in Defense of a Network“. You can join the presentation online at 12:00 pm at https://umbc.webex.com/meet/sherman.
Often network defenders fail to take into account organizational culture when attempting to provide a secure, reliable, and usable enterprise network. Users and process leaders often fall victim to the false allure of the value of networked systems, without asking the question, “Should this be networked?” Collectively, organizations also forget that networks are a combination of the humans who use the network, the personas we all have to form to gain access to this manmade domain, and the interplay of logical and physical network architecture manifested in geographical locations. The value of some simple military principles—including defense-in-depth, mission focus, redundancy, and resiliency versus efficiency—can help a network defender better advise everyone from the “C Suite” decision-makers to the average network user, on how to have a secure network while accepting reasonable limitations.
The post Online Talks Double Feature: Blockchain and Network Defense, 12-2 Fri 3/27, UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC will hold a double feature with two online security-oriented talks from 12:00 pm to 2:00 pm EDT on Friday, March 27. Both talks will be shared via Webex. From 1:00-2:00 pm,...
https://www.csee.umbc.edu/2020/03/online-talks-double-feature-blockchain-and-network-defense-12-2-fri-3-27-umbc/
https://beta.my.umbc.edu/api/v0/pixel/news/91615/guest@my.umbc.edu/02d72add2655694ae942c1b404c60363/api/pixel
computer-science
cybersecurity
news
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Thu, 26 Mar 2020 22:50:30 -0400
Webex talk: John Mitchell: Will Blockchain Change Everything? Fri 3/27 1-2pm

Lockheed Martin Distinguished Speaker Series
Will Blockchain Change Everything?
Dr. John Mitchell
Mary and Gordon Crary Family Professor
Departments of Computer Science & Electrical Engineering
Stanford University
1:00-2:00pm EST, Friday, 27 March 2020
Webex meeting hosted by Anupam Joshi
https://umbc.webex.com/meet/joshi
Far from serving only as a foundation for cryptocurrency, blockchain technology provides a general framework for trusted distributed ledgers. Over the past few years, their popularity has grown tremendously, as shown by the number of companies and efforts associated with the Linux Foundation’s Hyperledger project, for example. From a technical standpoint, a blockchain combines a storage layer, networking protocols, a consensus layer, and a programmable transaction layer, leveraging cryptographic operations. The distributed state machine paradigm provides atomicity and transaction rollback, while consensus supports distributed availability as well as certain forms of fair access. From an applications perspective, blockchains appeal to distributed networks of independent agents, as arise in supply chain, credentialing, and decentralized financial services. The talk will look at the potential for radical change as well as specific technical challenges associated with verifiable consensus protocols and trustworthy smart contracts.
John Mitchell is the Mary and Gordon Crary Family Professor in the School of Engineering, Professor of Computer Science, co-director of the Stanford Computer Security Lab, and Professor (by courtesy) of Education. He was Vice Provost at Stanford University from 2012 to 2018. Mitchell’s research focusses on programming languages, computer, and network security, privacy, and education. He has published over 200 research papers, served as editor of eleven journals, including Editor-in-Chief of the Journal of Computer Security, and written two books. He has led research projects funded by numerous organizations and served as advisor and consultant to successful small and large companies. His first research project in online learning started in 2009 when he and six undergraduate students built Stanford CourseWare, an innovative platform that served as the foundation for initial flipped classroom experiments at Stanford and helped inspire the first massive open online courses (MOOCs) from Stanford. Professor Mitchell currently serves as Chair of the Stanford Department of Computer Science.
The post Webex talk: John Mitchell: Will Blockchain Change Everything? Fri 3/27 1-2pm appeared first on Department of Computer Science and Electrical Engineering.
]]>
Lockheed Martin Distinguished Speaker Series Will Blockchain Change Everything? Dr. John Mitchell Mary and Gordon Crary Family Professor Departments of Computer Science &...
https://www.csee.umbc.edu/2020/03/webex-talk-john-mitchell-will-blockchain-change-everything-fri-3-27-1-2pm/
https://beta.my.umbc.edu/api/v0/pixel/news/91356/guest@my.umbc.edu/98a6a027f52a1e7e10d749e5648e138a/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sun, 15 Mar 2020 17:27:52 -0400
Webex Talk: Hard-Learned Lesson in Defense of a Network, 12-1 Fri 3/27

The UMBC Cyber Defense Lab presents
Hard-Learned Lesson in Defense of a Network
Dan Yaroslaski
Former Operations Officer at Marine Forces Cyberspace Command, Colonel, USMC
Often network defenders fail to take into account organizational culture when attempting to provide a secure, reliable, and usable enterprise network. Users and process leaders often fall victim to the false allure of the value of networked systems, without asking the question, “Should this be networked?” Collectively, organizations also forget that networks are a combination of the humans who use the network, the personas we all have to form to gain access to this manmade domain, and the interplay of logical and physical network architecture manifested in geographical locations. The value of some simple military principles—including defense-in-depth, mission focus, redundancy, and resiliency versus efficiency—can help a network defender better advise everyone from the “C Suite” decision-makers to the average network user, on how to have a secure network while accepting reasonable limitations.
Colonel Dan Yaroslaski is a career Marine with over 30 years of service to the nation. He started as an enlisted anti-armor missileman, who then became an Assault Amphibian Vehicle Officer (AAV’s are 27 Ton armored amphibious descendants of the WW II vehicles used from Tarawa to Iwo Jima). He has made a career of integrating technology and human beings to form cohesive combat organizations. Dan’s diverse career placed him at the forefront of high-end, top-secret compartmentalized planning and execution, to the extremely human act of advising an Afghan National Army Kandak (Battalion). During his five-year tenure at Marine Forces Cyberspace Command, he successfully architected new techniques that took advantage of boundary defenses, to new and innovative ways to integrate traditional warfare methods with cyberspace operations, as highlighted in a recent NPR story about USCYBERCOM’s Operation GLOWING SYMPHONY. Dan also spent time creating effective policy directing network operations and defense, to include an extremely frustrating year negotiating the interplay of network operations, operations in the information environment, and Marine Corps culture. Dan and his wife are now empty nesters, so they spend an enormous amount of time nurturing two dogs to fill the void left by their children. As the Rolling Stones point out, “What a drag it is getting old.”
Host: Alan T. Sherman, *protected email*
Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL Meetings:
- Apr 10, Russ Fink (APL), ransomware
- Apr 24, Lance Hoffman (GWU), policy
- May 8, Jason Wells (UMBC SFS scholar), law enforcement
- May 22, Spring SFS Meeting at UMBC, 9:30am-2pm, ITE 456
The post Webex Talk: Hard-Learned Lesson in Defense of a Network, 12-1 Fri 3/27 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Hard-Learned Lesson in Defense of a Network Dan Yaroslaski Former Operations Officer at Marine Forces Cyberspace Command, Colonel, USMC...
https://www.csee.umbc.edu/2020/03/webex-talk-hard-learned-lesson-in-defense-of-a-network-12-1-fri-3-27/
https://beta.my.umbc.edu/api/v0/pixel/news/91355/guest@my.umbc.edu/74d59cee6e5929961f6c25d66d715cd0/api/pixel
computer-science
cybersecurity
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sun, 15 Mar 2020 14:42:11 -0400
talk: Autonomous Agents, Deep Learning, and Graphs for Cyber Defense, 12-1 Fri. 3/13
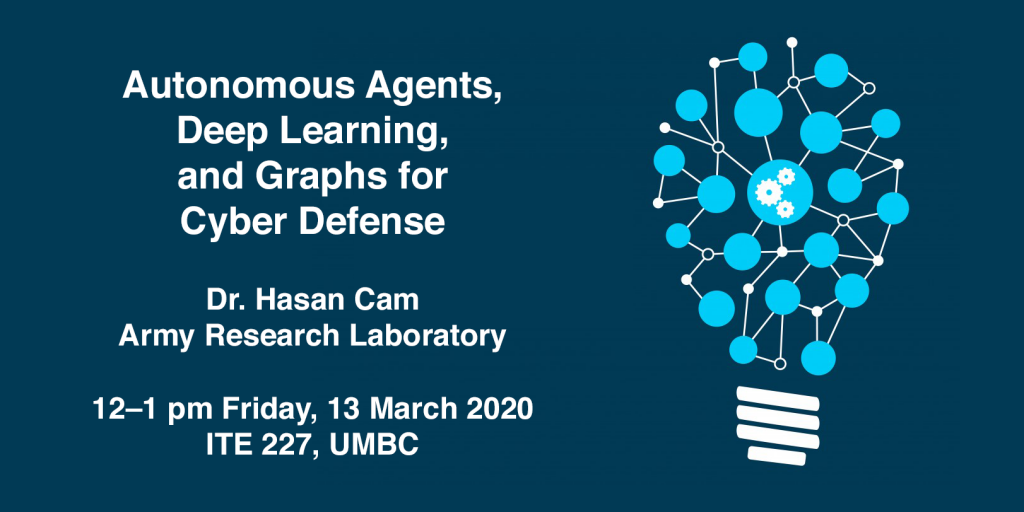
The UMBC Cyber Defense Lab presents
Autonomous Agents, Deep Learning,
and Graphs for Cyber Defense
Dr. Hasan Cam
Army Research Laboratory
12–1 pm Friday, 13 March 2020, ITE 227, UMBC
Cyber resilience usually refers to the ability of an entity to detect, respond to, and recover from cybersecurity attacks to the extent that the entity can continuously deliver the intended outcome despite their presence. Cybersecurity tools such as intrusion detection and prevention systems usually generate far too many alerts, indicators or log data, many of which do not have obvious security implications unless their correlations and temporal causality relationships are determined. In this talk, I will present methods to first estimate the infected and exploited assets and then take recovery and preventive actions using autonomous agents, deep learning, and graphs. Autonomous adversary and defender agents are designed such that the adversary agent can infer the adversary activities and intentions, based on cybersecurity observations and measurements, while the defender agent aims at estimating the best reactive and pro-active actions to protect assets and mitigate the adversary activities. The graph thinking and causality analysis of cyber infection and exploitation helps predict the infection states of some assets. This prediction data of infections is taken as input data by deep reinforcement learning to train agents for determining effective actions. This talk will discuss some preliminary results from the development of building an automated system of autonomous agents to provide cyber resiliency over networks.
Hasan Cam is a Computer Scientist at US Army Research Laboratory. He currently works on the projects involved with autonomous agents, active malware defense, cyber resiliency, and risk assessment over wired, mobile, and tactical networks. His research interests include cybersecurity, machine learning, data analytics, networks, algorithms, and parallel processing. He served as the government lead for the Risk area in Cyber Collaborative Research Alliance. He has previously worked as a faculty member in academia and a senior research scientist in the industry. He has served as an editorial member of two journals, a guest editor of two special issues of journals, an organizer of symposiums and workshops, and a Technical Program Committee Member in numerous conferences. He received a Ph.D. degree in electrical and computer engineering from Purdue University, and an M.S. degree in computer science from Polytechnic University, New York. He is a Senior Member of IEEE.
Host: Alan T. Sherman, *protected email*
Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL Meetings:
- Mar 27, Dan Yaroslaski, cybercommand
- Apr 10, Russ Fink (APL), ransomware
- Apr 24, Lance Hoffman (GWU), policy
- May 8, Jason Wells, law enforcement
- May 22, Spring SFS Meeting at UMBC, 9:30-2, ITE 456
The post talk: Autonomous Agents, Deep Learning, and Graphs for Cyber Defense, 12-1 Fri. 3/13 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Autonomous Agents, Deep Learning, and Graphs for Cyber Defense Dr. Hasan Cam Army Research Laboratory 12–1 pm Friday, 13 March 2020, ITE...
https://www.csee.umbc.edu/2020/03/talk-autonomous-agents-deep-learning-and-graphs-for-cyber-defense-12-1-fri-3-13/
https://beta.my.umbc.edu/api/v0/pixel/news/91103/guest@my.umbc.edu/4cdbd1c2dfd69476b76f6d340e202dc6/api/pixel
computer-engineering
computer-science
cybersecurity
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sun, 08 Mar 2020 13:06:35 -0400
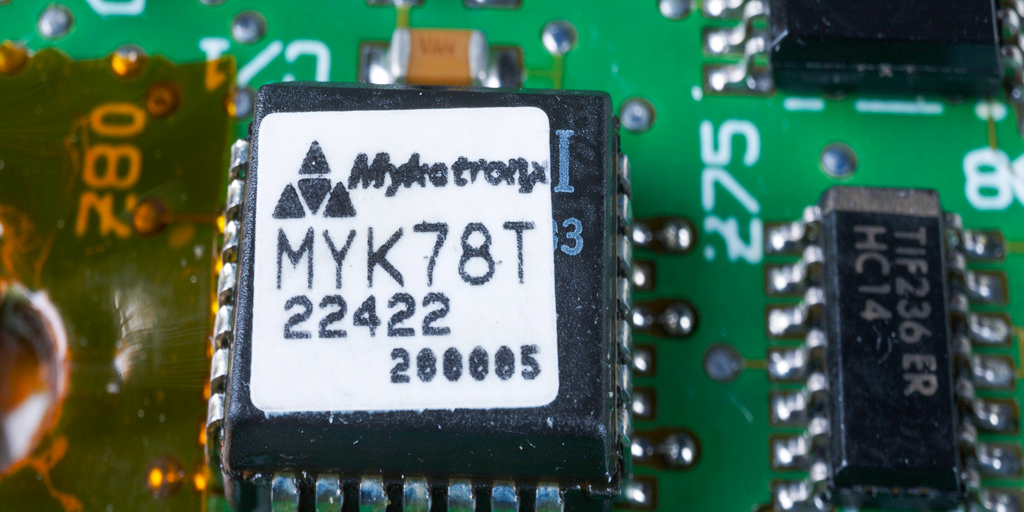
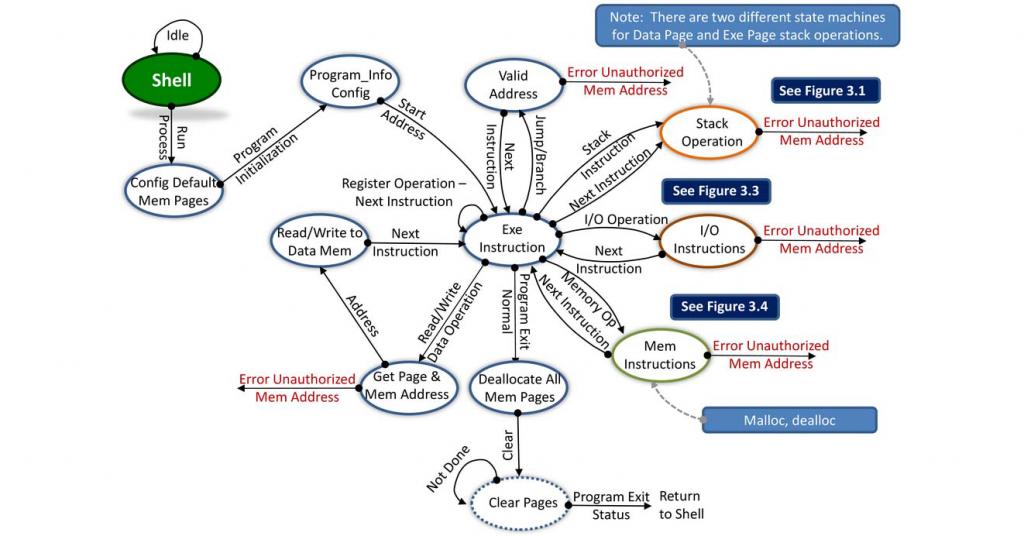
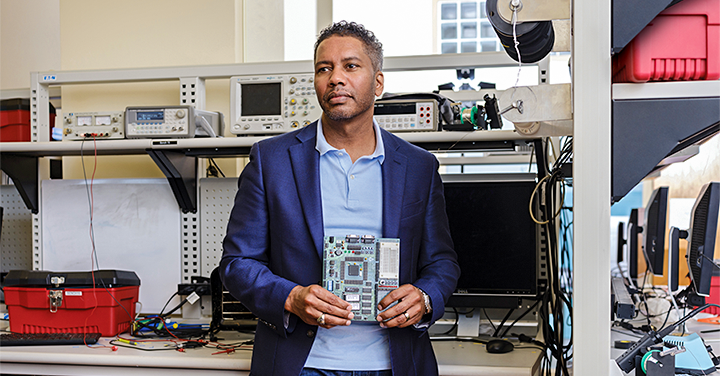
talk: Hardware Security Kernel for Managing Memory and Instruction Execution, 12pm Fri 2/28
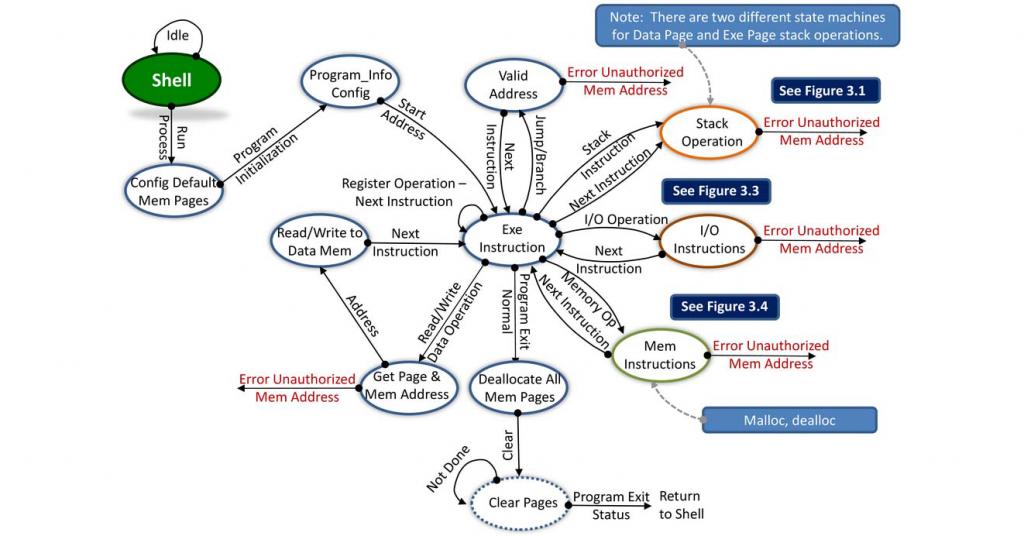
The UMBC Cyber Defense Lab presents
Hardware Security Kernel for Managing Memory and Instruction Execution
Patrick Jungwirth, PhD
Computational and Information Sciences Directorate
Army Research Lab, Aberdeen Proving Ground, USA
12–1 pm Friday, 28 February 2020, ITE 227, UMBC
The cybersecurity world faces multiple attack vectors from hardware-level exploits, including cache bank malicious operations, rowhammer, Spectre, Meltdown, and Foreshadow attacks, and software-based attacks including buffer-overflows, et al. Hardware-level exploits bypass protections provided by software-based separation kernels. Current microprocessor execution pipelines are not designed to understand security: they treat malicious instructions, software bugs, and harmless code the same. This presentation explores adding a hardware-level security monitor below the execution pipeline [1,2,3].
[1] P. Jungwirth, et al.: “Hardware security kernel for cyber-defense,” Proc. SPIE 11013, Disruptive Technologies in Information Sciences II, 110130J, Baltimore 10 May 2019); https://doi.org/10.1117/12.2513224
[2] P. Jungwirth, and J. Ross: “Security Tag Fields and Control Flow Management,” IEEE SouthEastCon 2019, Huntsville, AL, April 2019.
[3] P. Jungwirth and D. Hahs: “Transfer Entropy Quantifies Information Leakage,” IEEE SouthEastCon 2019, Huntsville, AL, April 2019.
About the Speaker. Dr. Jungwirth is a computer architecture researcher at the Army Research Lab. Previously he worked for the Aviation and Missile, RDEC in Huntsville, AL. Currently, he is researching hardware state machines to provide simple operating system support (monitor) and control flow integrity in hardware. Dr. Jungwirth is co-inventor of the OS Friendly Microprocessor Architecture, US Patent 9122610. The OS Friendly Microprocessor Architecture includes hardware security features for an operating system and supports near single-cycle context switches in hardware. Email: *protected email*
Host: Alan T. Sherman, *protected email*
Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681.
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public.
Upcoming CDL Meetings:
Mar 13, Hasan Cam, autonomous agents
Mar 27, Dan Yaroslaski, cybercommand
Apr 10, Russ Fink (APL), ransomware
Apr 24, TBA
May 8, Jason Wells, law enforcement
May 22, Spring SFS Meeting at UMBC, 9:30am-2pm, ITE 456
The post talk: Hardware Security Kernel for Managing Memory and Instruction Execution, 12pm Fri 2/28 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Hardware Security Kernel for Managing Memory and Instruction Execution Patrick Jungwirth, PhD Computational and Information Sciences Directorate...
https://www.csee.umbc.edu/2020/02/talk-hardware-security-kernel-for-managing-memory-and-instruction-execution-12pm-fri-2-28/
https://beta.my.umbc.edu/api/v0/pixel/news/90623/guest@my.umbc.edu/73a2ef9aadd73410c584e89816bb8157/api/pixel
computer-engineering
computer-science
cybersecurity
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Thu, 20 Feb 2020 11:57:26 -0500
Lockheed Martin Distinguished Speaker Series
Designing Secure Hardware Systems
Shawn Blanton
Trustee Professor, Electrical and Computer Engineering
Carnegie Mellon University
1:00-2:00pm Friday 7 Feb. 2020
Commons 329, UMBC
University Center Ballroom
On October 29, 2018, DARPA issued an RFI that stated: “This Request for Information (RFI) from the Defense Advanced Research Projects Agency’s (DARPA) Microsystems Technology Office (MTO) seeks information on technology, concepts, and approaches to support the integration of security capabilities directly into System on Chip (SoC) system design and to enable the autonomous integration and assembly of SoCs.
This RFI and the tens of millions of dollars that the US government has already invested in hardware security research and development is based on the fact that the fabrication of state-of-the-art electronics is now mostly overseas. With the recent announcement that GLOBALFOUNDRIES is going to stop all 7nm development, there is now only one company in the US that continues to pursue advanced semiconductors (Intel). Unfortunately, Intel does not have the same experience of making chips for third parties as does Samsung and (most importantly) TSMC (Taiwan Semiconductor Manufacturing Corporation). As a result, the US government believes it will be forced to fabricate advanced, sensitive electronics overseas in untrusted fabrication facilities. As a result, there is keen interest in design methodologies that mitigate reverse engineering, tampering, counterfeiting, etc.
In this talk, an overview of hardware security will be presented followed by a discussion on a concept called logic locking. This approach will be described and the “back and forth” that is now occurring in the research community involving: (i) vulnerability discovery and (ii) logic locking improvement.
Shawn Blanton is a professor in the Electrical and Computer Engineering Department at Carnegie Mellon University and Associate Director of the SYSU-CMU Joint Institute of Engineering (JIE). In 1995 he received his Ph.D. in Electrical Engineering and Computer Science from the University of Michigan, Ann Arbor. His research interests include various aspects of integrated system tests, testable design, and test methodology development. He has consulted for various companies and is the founder of TestWorks, a Carnegie Mellon University spinout focused on information extraction from IC test data. He is a Fellow of the IEEE and Senior Member of the ACM and served as the program chair for the 2011 International Test Conference.
The post 🔴 talk: Shawn Blanton (CMU); Designing Secure Hardware Systems, 1pm Fri 2/7; Commons 329 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Lockheed Martin Distinguished Speaker Series Designing Secure Hardware Systems Shawn Blanton Trustee Professor, Electrical and Computer Engineering Carnegie Mellon University...
https://www.csee.umbc.edu/2020/02/talk-shawn-blanton-cmu-on-designing-secure-hardware-systems-1pm-fri-2-7/
https://beta.my.umbc.edu/api/v0/pixel/news/90162/guest@my.umbc.edu/8136f036ce8ed4c55bc786ea98ddc9df/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
electrical-engineering
events
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Wed, 05 Feb 2020 09:56:00 -0500
Wed, 05 Feb 2020 09:56:00 -0500
JHU/APL CIRCUIT internship program information session, 3pm Fri 1/31
JHU/APL CIRCUIT internship program information session
3:00-4:00 pm Friday, 31 January 2020
ITE 459, UMBC
There will be a special information session on the JHU/APL CIRCUIT internship program from 3:00 pm to 4:30 pm on Friday, 31 January 2020 in room ITE 459.
This session is for undergraduates who want to spend their summer (June through August) getting paid to do mentored research at the Johns Hopkins University Applied Physics Lab. The research areas include AI, data science, cybersecurity, precision medicine, and planetary exploration.
Interns selected for the program will do mission-oriented research on-site at JHU/APL in Laurel MD mentored by STEM professionals. There will also be year-round opportunities for engagement and enrichment. The selection for an internship will be based on a combination of potential, need and commitment.
Email *protected email* or *protected email* with questions.
The post JHU/APL CIRCUIT internship program information session, 3pm Fri 1/31 appeared first on Department of Computer Science and Electrical Engineering.
]]>
JHU/APL CIRCUIT internship program information session 3:00-4:00 pm Friday, 31 January 2020 ITE 459, UMBC There will be a special information session on the JHU/APL CIRCUIT...
https://www.csee.umbc.edu/2020/01/jhu-apl-circuit-internship-program-information-session-3pm-fri-1-31/
https://beta.my.umbc.edu/api/v0/pixel/news/89804/guest@my.umbc.edu/78328c3f0e19647545384211b4aa76f6/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
machine-learning
news
research
students
uncategorized
undergraduate
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Wed, 22 Jan 2020 16:05:36 -0500
Wed, 01 Jan 2020 16:05:36 -0500
TALK: Reasoning About Time in a Crypto Protocol Analysis Tool

The UMBC Cyber Defense Lab presents
Reasoning About Time in a Crypto Protocol Analysis Tool
Dr. Catherine Meadows, Naval Research Laboratory
12:00–1:00pm Friday, 15 November 2019, ITE 227
The ability to guarantee timing properties, and in turn to use assumption about time to guarantee the security of protocols, is important to many of the applications we rely upon. For example, to compute locations, GPS depends on time synchronization between entities. Blockchain protocols require loose time synchronization to guarantee agreement on block timestamps. Distance-bounding protocols use the roundtrip time of an RF signal to enforce constraints on location. To analyze these types protocols formally, it is necessary to reason about time. This talk describes recent research in extending the Maude-NPA cryptographic protocol analysis tool to reason about cryptographic protocols that rely on or enforce timing properties. We describe the timing model we have created for the tool. We show how we we represent timing properties as constraints, whose solution is outsourced to an SMT solver. We also discuss our experimental results.
Catherine Meadows is a senior researcher in computer security at the Center for High Assurance Systems at the Naval Research Laboratory and heads that group’s Formal Methods Section. She was the principal developer of the NRL Protocol Analyzer (NPA), which was one of the first software tools to find previously undiscovered flaws in cryptographic protocols, and was used successfully in the analysis of a number of protocol standards. She is also leading, or has recently led, a number of projects related to the design and analysis of cryptographic protocols, including one focused the development of an analysis tool, Maude-NPA, that takes into account the the complex algebraic properties of cryptosystems, another that is focusing on the automatic generation of secure cryptosystems, and another devoted to formal methods for the design of cyber-physical systems with legacy components.
This work was supported by ONR 321 (*protected email*)
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant 175368. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL Events:
- December 6, Karl Henderson, Verisign
- 9am—5pm daily, January 13-17, UMBC SFS/CySP Research Study, ITE 456
- January 31, 2020, TBA, biweekly CDL talks resume
The post TALK: Reasoning About Time in a Crypto Protocol Analysis Tool appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Reasoning About Time in a Crypto Protocol Analysis Tool Dr. Catherine Meadows, Naval Research Laboratory 12:00–1:00pm Friday, 15 November 2019,...
https://www.csee.umbc.edu/2019/11/talk-reasoning-about-time-in-a-crypto-protocol-analysis-tool-catherine-meadows-naval-research-laboratory/
https://beta.my.umbc.edu/api/v0/pixel/news/88326/guest@my.umbc.edu/5ee2a03aa6c8d943d63ec889fe036f2e/api/pixel
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Sun, 10 Nov 2019 15:12:03 -0500