NSA highlights strong partnership with UMBC through Featured School campaign

NSA highlights strong partnership with UMBC in Featured School campaign
Over the past two decades, UMBC and the National Security Agency (NSA) have developed a strong relationship, which has led to research, internship, and career opportunities for faculty, students, and alumni. UMBC is the first institution to be highlighted in NSA’s Featured School Series, which launched on September 4.
“UMBC’s long-standing partnership with NSA has provided valuable experiences for our students, faculty, and alumni to pursue internships, careers, and collaborative research opportunities,” said President Freeman Hrabowski. “Through this work we are helping to address the need for well-trained cyber professionals by creating a network of talented people to protect the state, nation, and world.”
More than 1100 NSA employees are UMBC alumni, including Darniet Jennings ‘98, M.S. ‘99, Ph.D. ‘03, information systems management. Jennings continued his dissertation research when he took a job at NSA, where he developed a system to manage big data effectively, which was patented in 2010.
The opportunities at NSA include careers in a broad range of disciplines including cybersecurity, engineering, computer science, language, and biological and chemical sciences. Regina Hambleton ‘87, mathematics, has held a number of positions at NSA and is currently the Agency’s deputy director of Engagement and Policy. She began working at NSA while she was a student at UMBC, and participated in a program that allowed her to spend a semester at UMBC taking courses followed by a semester working at NSA.
The partnership between NSA and UMBC also helps prepare an increasing number of graduates for careers in cybersecurity-related fields, to protect the nation from cyber threats.
Charles Nicholas, professor of computer science and electrical engineering, is also highlighted in the Featured School Series campaign. He has spent two sabbaticals at NSA during his time at UMBC, and has mentored students who completed NSA internships, in addition to students who went on to pursue careers at NSA. Nicholas is interested in the intersection of cybersecurity and data science, and the tools that are used to compare malware specimens.
“There are so many opportunities in the intelligence community, including at NSA,” Nicholas says. “It is important for students interested in those careers to develop technical ability, as well as critical and creative thinking, and I enjoy the chance to help them grow those skills.”
For more information about the partnership, and a few UMBC alumni who work at NSA, visit the UMBC page on the NSA website.
Adapted from a UMBC News article by Megan Hanks. Banner image by Marlayna Demond for UMBC.
The post NSA highlights strong partnership with UMBC through Featured School campaign appeared first on Department of Computer Science and Electrical Engineering.
]]>
NSA highlights strong partnership with UMBC in Featured School campaign Over the past two decades, UMBC and the National Security Agency (NSA) have developed a strong relationship, which has...
https://www.csee.umbc.edu/2018/09/nsa-highlights-strong-partnership-with-umbc-through-featured-school-campaign/
https://beta.my.umbc.edu/api/v0/pixel/news/78345/guest@my.umbc.edu/937bbb0918436a7c5bf367c07f1e6516/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
electrical-engineering
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
true
Wed, 05 Sep 2018 09:12:55 -0400
Wed, 05 Sep 2018 09:12:55 -0400
talk: Robot Governance – Institutions and Issues, 10:30 Tue 7/24, ITR346
Robot Governance – Institutions and Issues
Dr. Aaron Mannes, ISHPI Information Technologies
10:30-11:30 Tuesday, 24 July 2018, ITE 346
Inexpensive sensors and information storage and processing have enabled the large-scale production of robots: autonomous systems capable of acting on the world. These systems represent an enormous technological and economic opportunity that will change society in countless and unpredictable ways. They will also bring new policy challenges. This presentation examines the missions the government will need to undertake to address the challenges raised by this new technology, identifies critical gaps the government faces in carrying out these missions, and discusses institutional options to address these gaps.
Dr. Aaron Mannes is the Senior Policy Advisor at ISHPI Information Technologies, where he supports the Apex Data Analytics Engine (DA-E) at the Department of Homeland Security Science and Technology Directorate. In supporting DA-E, Dr. Mannes collaborates on big data projects that support the Homeland Security Enterprise and researches technology policy. He started at DHS as an American Association for the Advancement of Science Policy Fellow in September 2015. From 2004 to 2015, Dr. Mannes was a researcher at the University of Maryland Institute for Advanced Computer Studies (UMIACS) where he was the subject matter expert on terrorism and international affairs collaborating with a team of inter-disciplinary scientists to build computational tools to support decision-makers facing 21st century security and development problems. Dr. Mannes earned his Ph.D. at the University of Maryland’s School of Public Policy in 2014. His dissertation topic was the evolving national security role of the vice president.
Dr. Mannes is the author or co-author of four books on terrorism and has written scores of articles, papers, and book chapters on an array of topics including Middle East affairs, terrorism, technology, and other international security issues for popular and scholarly publications including Politico, Policy Review, The Wall Street Journal, Foreign Policy, The Journal of International Security Affairs, The Huffington Post, The National Interest, The Jerusalem Post, and The Guardian.
This research was conducted with the support of the Apex Data Analytics Engine in the Department of Homeland Security (DHS) Science and Technology Directorate (S&T). In no way should anything stated in this seminar be construed as representing the official position of DHS S&T or any other component of DHS. Opinions and findings expressed in this seminar, as well as any errors and omissions, are the responsibility of the presenter alone.
The post talk: Robot Governance – Institutions and Issues, 10:30 Tue 7/24, ITR346 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Robot Governance – Institutions and Issues Dr. Aaron Mannes, ISHPI Information Technologies 10:30-11:30 Tuesday, 24 July 2018, ITE 346 Inexpensive sensors and information storage...
https://www.csee.umbc.edu/2018/07/talk-robot-governance-institutions-and-issues-1030-tue-7-24-itr346/
https://beta.my.umbc.edu/api/v0/pixel/news/77606/guest@my.umbc.edu/eb929b4718ba6f9af0b285ec85f5cf78/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Mon, 23 Jul 2018 17:27:32 -0400
UMBC launches cybersecurity research collaboration with Japanese and UK partners
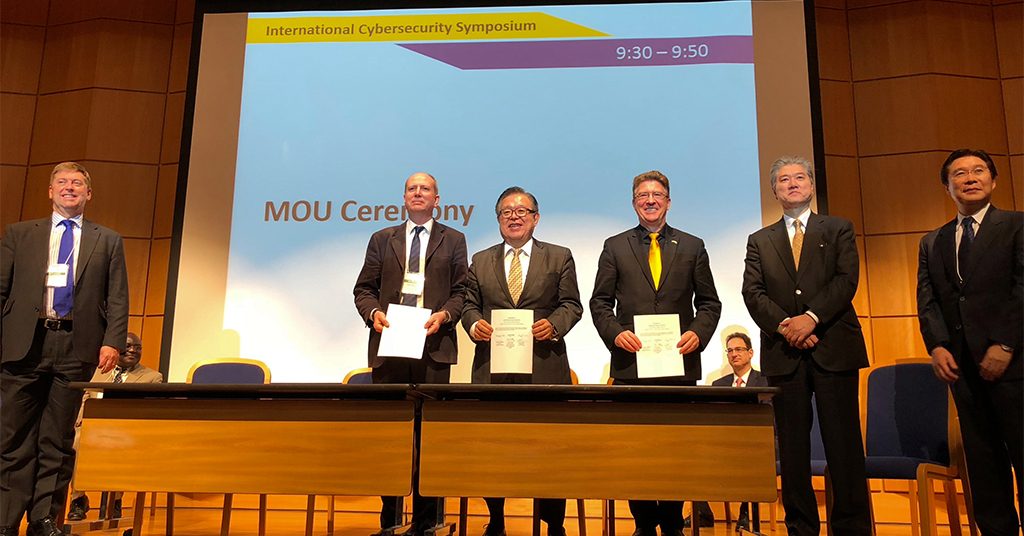 University leaders, including Karl V. Steiner, third from right, signed the three-nation agreement in a ceremony at the sixth International Cybersecurity Symposium in Japan. Photo courtesy of Karl V. Steiner
University leaders, including Karl V. Steiner, third from right, signed the three-nation agreement in a ceremony at the sixth International Cybersecurity Symposium in Japan. Photo courtesy of Karl V. Steiner
UMBC launches infrastructure-focused cybersecurity research collaboration with Japanese and UK partners
UMBC is one of three leading academic institutions collaborating on a new research initiative focused on cybersecurity for critical national infrastructures, including information technology, public transit, and financial services. University leaders signed the three-nation agreement in a ceremony at the sixth International Cybersecurity Symposium in Japan.
UMBC, Keio Research Institute (KRIS) in Japan, and Royal Holloway University of London (RHUL) in the UK will partner to investigate the use of common system simulation tools for modeling critical national infrastructure. This partnership is part of a broader international collaboration, the International Cybersecurity Center of Excellence (INCS-COE). It will also involve Hitachi, an international operator in power systems, telecommunication, railways, and other core infrastructure areas.
Because cybersecurity attacks may not be limited to national borders, this collaboration argues that defense against such attacks should not be siloed either.
“Cybersecurity can no longer be treated as a national issue,” emphasizes Karl V. Steiner, vice president for research at UMBC. “Long-term and productive international collaborations are needed to make significant progress.”
Jun Murai, professor of environment and information studies at Keio University, notes, “We look forward to working with our research colleagues in the UK and U.S. to help address the increasingly challenging cyber threats to the security of our respective critical national infrastructures.”
Working with a common toolset will enable mixed nationality teams to run simulations together. This will help cybersecurity experts learn how to more effectively address human factors, including cultural differences, in predicting how attacks and responses to those attacks might play out across different geographies.
“We are excited to participate in this new research collaboration with our colleagues in Japan and the UK to help us better understand and address some of the key cybersecurity challenges that our nations face from increasingly aggressive international adversaries,” says Anupam Joshi, director of UMBC’s Center for Cybersecurity.
The partners in this research see the modeling of system security as increasingly vital for industry and government, for both training purposes and vulnerability analysis.
“This initiative creates many future opportunities including, for example, the opportunity to address the impact on critical national infrastructure security of the exponential growth of the internet of things, and for potential exchanges of expert staff and students,” explains Keith Mayes, head of the Information Security Group (ISG) at Royal Holloway University.
Steiner shares Mayes’s excitement about expanding opportunities for both established and emerging researchers in this growing field. Thanks to leading academic programs in cybersecurity, the bwtech@UMBC Cyber Incubator, and UMBC’s internationally-known Center for Cybersecurity, he says, “UMBC is uniquely positioned in Maryland to become a major global force for research in cybersecurity.”
“This partnership,” says Steiner, “builds important connections to move this essential work forward.”
Adapted from a UMBC News article written by Megan Hanks. Photo by Marlayna Demond ’11 for UMBC.
The post UMBC launches cybersecurity research collaboration with Japanese and UK partners appeared first on Department of Computer Science and Electrical Engineering.
]]>
University leaders, including Karl V. Steiner, third from right, signed the three-nation agreement in a ceremony at the sixth International Cybersecurity Symposium in Japan. Photo courtesy of Karl...
https://www.csee.umbc.edu/2018/07/umbc-cybersecurity-research-collaboration-japanese-uk-partners/
https://beta.my.umbc.edu/api/v0/pixel/news/77417/guest@my.umbc.edu/fb69bb7ce9baa05f22981b1dd26cee4d/api/pixel
computer-engineering
computer-science
cybersecurity
research
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Sun, 08 Jul 2018 09:06:00 -0400
UMBC Cyber Dawgs Capture The Flag Cybersecurity Competition, Sunday March 11
UMBC Cyber Dawgs
Capture The Flag Cybersecurity Competition
The national champion UMBC Cyber Dawgs will hold the second annual computer security Capture The Flag (CTF) competition on Sunday, March 11th from 11am-7pm in the UC Ballroom. This CTF event is a Jeopardy-style competition where teams of four people use their laptops to discover answers to questions about cybersecurity, including network forensics, reverse engineering, reconnaissance, and cryptography. Each question has a point value based upon its difficulty and whichever team has the most points at the end wins!
The competition is open to all current UMBC students and student from a few other nearby schools. Both beginners and experts are welcome to participate.
Prizes will be awarded to the top teams. There will also be door prizes for randomly selected participants as well as T-Shirts for everyone. Some prizes from last year include Raspberry Pis, a Wireless Pineapple Nano, a YARD Stick One, and a Chromebook! Lunch and dinner (Lima’s Chicken) will be provided for everyone.
Students who are interested must register online in advance and bring a laptop to the event. Please note any dietary restrictions on the registration form as well as your T-Shirt size. See the event website for more information
The post UMBC Cyber Dawgs Capture The Flag Cybersecurity Competition, Sunday March 11 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Dawgs Capture The Flag Cybersecurity Competition The national champion UMBC Cyber Dawgs will hold the second annual computer security Capture The Flag (CTF) competition on Sunday,...
https://www.csee.umbc.edu/2018/02/umbc-cyber-dawgs-capture-flag-cybersecurity-competition-sunday-march-11-2018/
https://beta.my.umbc.edu/api/v0/pixel/news/74319/guest@my.umbc.edu/2e5232853dad24355b1c4efb82961c8a/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Mon, 26 Feb 2018 23:53:40 -0500
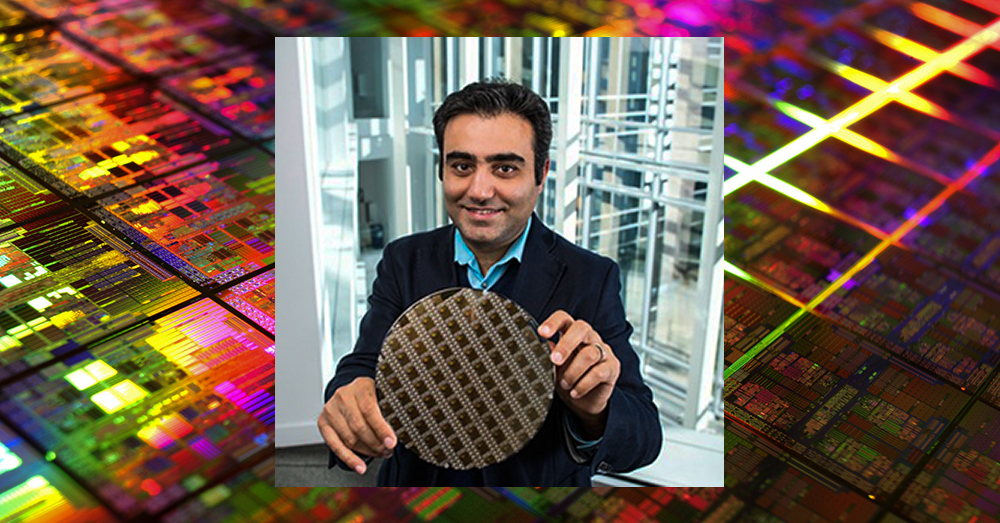
talk: Towards Hardware Cybersecurity, 11am Tue 2/20, ITE325, UMBC
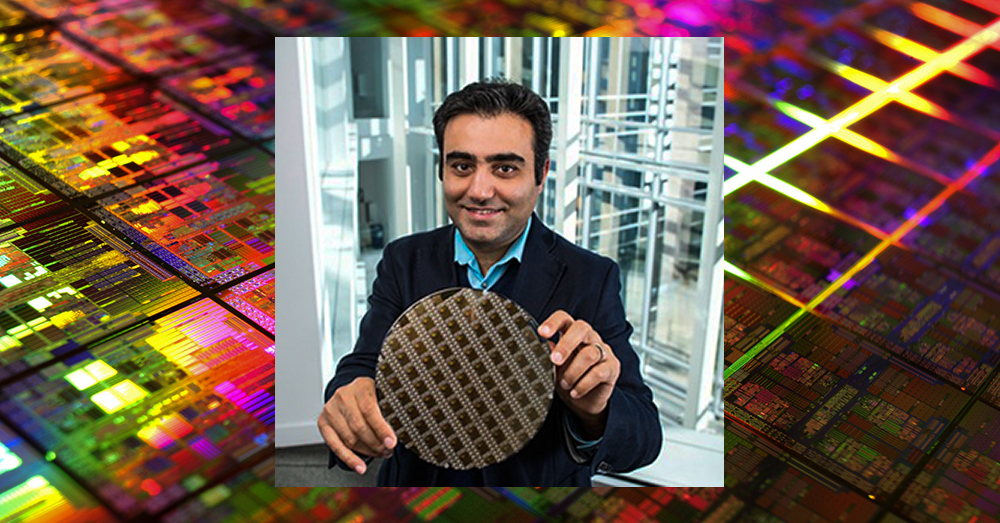
Towards Hardware Cybersecurity
11:00am-12:00pm Tuesday, 20 Febuary 2018, ITE 325, UMBC
Electronic system security, trust and reliability has become an increasingly critical area of concern for modern society. Secure hardware systems, platforms, as well as supply chains are critical to industry and government sectors such as national defense, healthcare, transportation, and finance.
Traditionally, authenticity and integrity of data has been protected with various security protocol at the software level with the underlying hardware assumed to be secure, and reliable. This assumption however is no longer true with an increasing number of attacks reported on the hardware. Counterfeiting electronic components, inserting hardware trojans, and cloning integrated circuits are just few out of many malicious byproducts of hardware vulnerabilities, which need to be urgently addressed.
In the first part of this talk I will address the security and vulnerability challenges in the horizontal integrated hardware development process. I will then present the concept of hybrid spin-transfer torque CMOS look up table based design which is our latest effort on developing a cost-effective solution to prevent physical reverse engineering attacks.
In the second part of my talk I will present how information at the hardware level can be used to address some of the major challenges of software security vulnerabilities monitoring and detection methods. I will first discuss these challenges and will then show how the use of data at the hardware architecture level in combination with an effective machine learning based predictor helps protecting systems against various classes of hardware vulnerability attacks.
I will conclude the talk by emphasizing the importance of this emerging area and proposing a research agenda for the future.
Dr. Houman Homayoun is an Assistant Professor in the Department of Electrical and Computer Engineering at George Mason University. He also holds a courtesy appointment with the Department of Computer Science as well as Information Science and Technology Department. He is the director of GMU’s Accelerated, Secure, and Energy-Efficient Computing Laboratory (ASEEC). Prior to joining GMU, Houman spent two years at the University of California, San Diego, as NSF Computing Innovation (CI) Fellow awarded by the CRA-CCC. Houman graduated in 2010 from University of California, Irvine with a Ph.D. in Computer Science. He was a recipient of the four-year University of California, Irvine Computer Science Department chair fellowship. Houman received the MS degree in computer engineering in 2005 from University of Victoria and BS degree in electrical engineering in 2003 from Sharif University of Technology. Houman conducts research in hardware security and trust, big data computing, and heterogeneous computing, where he has published more than 80 technical papers in the prestigious conferences and journals on the subject. Since 2012 he leads ten research projects, a total of $7.2 million in funding, supported by DARPA, AFRL, NSF, NIST, and GM on the topics of hardware security and trust, big data computing, heterogeneous architectures, and biomedical computing. Houman received the 2016 GLSVLSI conference best paper award for developing a manycore accelerator for wearable biomedical computing. Since 2017 he has been serving as an Associate Editor of IEEE Transactions on VLSI. He is currently serving as technical program co-chair of 2018 GLSVLSI conference.
The post talk: Towards Hardware Cybersecurity, 11am Tue 2/20, ITE325, UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
Towards Hardware Cybersecurity Professor Houman Homayoun George Mason University 11:00am-12:00pm Tuesday, 20 Febuary 2018, ITE 325, UMBC Electronic system security, trust and reliability...
https://www.csee.umbc.edu/2018/02/talk-umbc-towards-hardware-cybersecurity-homayoun/
https://beta.my.umbc.edu/api/v0/pixel/news/73663/guest@my.umbc.edu/346faa5a3054d6e7d0b17a902843a9e0/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Sun, 04 Feb 2018 19:08:51 -0500
Sat, 17 Feb 2018 19:08:51 -0500
talk: An Introduction to Quantum Cryptography, Noon Friday 11/17, ITE231

The UMBC Cyber Defense Lab presents
An Introduction to Quantum Cryptography:
Or, How Alice Outwits Eve
Sam Lomonaco, CSEE, UMBC
12:00–1:00pm, Friday, 17 November 2017, ITE 231, UMBC
Alice and Bob wish to communicate without the archvillainess Eve eavesdropping on their conversation. Alice decides to take two college courses, one in cryptography, the other in quantum mechanics. During the courses, she discovers she can use what she has learned to devise a cryptographic communication system that automatically detects whether or not Eve is up to her villainous eavesdropping. Some of the topics discussed are Heisenberg’s Uncertainty Principle, the Vernam cipher, the BB84 and B92 cryptographic protocols. The talk ends with a discussion of some of Eve’s possible eavesdropping strategies, i.e., opaque eavesdropping, translucent eavesdropping, and translucent eavesdropping with entanglement.
Samuel J. Lomonaco Jr. received his PhD in mathematics from Princeton University. He has been a full professor of computer science and electrical engineering at the University of Maryland, Baltimore County (UMBC) since 1985, serving as founding chair of the CS Department from 1985 to 1991. Representative Awards, Accomplishments, and Honors include: (1) He was a visiting key research scientist at the Mathematical Sciences Research Institute (MSRI) at the University of California at Berkley in 2004. (2) He was a senior LaGrange fellow at the Institute for Scientific Exchange in Torino, Italy in 2005. (3) For contributions made to the development of the programming language Ada, he received an award from the United States Under Secretary of Defense for Research and Engineering, Dr. Richard DeLauer. (4) He was the first to introduce quantum information science to the American Mathematical Society (AMS) by organizing and giving a two-day AMS short course on quantum computation at the Annual Meeting of the AMS in Washington, DC, in January 2000. (5) He published four books on quantum computation and information science. (6) He accepted an invitation to be a guest editor of the Journal of Quantum Information Processing for a special issue on topological quantum computation.
Host: Alan T. Sherman, *protected email*
The post talk: An Introduction to Quantum Cryptography, Noon Friday 11/17, ITE231 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents An Introduction to Quantum Cryptography: Or, How Alice Outwits Eve Sam Lomonaco, CSEE, UMBC 12:00–1:00pm, Friday, 17 November 2017, ITE 231, UMBC Alice...
https://www.csee.umbc.edu/2017/11/umbc-introduction-quantum-cryptography-lomonaco/
https://beta.my.umbc.edu/api/v0/pixel/news/72612/guest@my.umbc.edu/54e3ce4738d132a9095207c57d198708/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Wed, 15 Nov 2017 08:10:40 -0500
talk: A Practitioner’s Introduction to Deep Learning, 1pm Fri 11/17
ACM Tech Talk Series
A Practitioner’s Introduction to Deep Learning
Ashwin Kumar Ganesan, PhD student
1:00-2:00pm Friday, 17 November 2017, ITE325, UMBC
In recent years, Deep Neural Networks have been highly successful at performing a number of tasks in computer vision, natural language processing and artificial intelligence in general. The remarkable performance gains have led to universities and industries investing heavily in this space. This investment creates a thriving open source ecosystem of tools & libraries that aid the design of new architectures, algorithm research as well as data collection.
This talk (and hands-on session) introduce people to some of the basics of machine learning, neural networks and discusses some of the popular neural network architectures. We take a dive into one of the popular libraries, Tensorflow, and an associated abstraction library Keras.
To participate in the hands-on aspects of the workshop, bring a laptop computer with Python installed and install the following libraries using pip. For windows or (any other OS) consider doing an installation of anaconda that has all the necessary libraries.
- numpy, scipy & scikit-learn
- tensorflow / tensoflow-gpu (The first one is the GPU version)
- matplotlib for visualizations (if necessary)
- jupyter & ipython (We will use python2.7 in our experiments)
Following are helpful links:
Contact Nisha Pillai (NPillai1 at umbc.edu) with any questions regarding this event.
The post talk: A Practitioner’s Introduction to Deep Learning, 1pm Fri 11/17 appeared first on Department of Computer Science and Electrical Engineering.
]]>
ACM Tech Talk Series A Practitioner’s Introduction to Deep Learning Ashwin Kumar Ganesan, PhD student 1:00-2:00pm Friday, 17 November 2017, ITE325, UMBC In recent years, Deep Neural...
https://www.csee.umbc.edu/2017/11/practitioner-introduction-deep-learning-umbc-acm-teck-talk/
https://beta.my.umbc.edu/api/v0/pixel/news/72613/guest@my.umbc.edu/e6c0244a9107e67e192737ee9aca6200/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
graduate
news
research
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Tue, 14 Nov 2017 14:56:17 -0500
talk: Keith Mayes on Attacks on Smart Cards, RFIDs and Embedded System

Attacks on Smart Cards, RFIDs and Embedded Systems
Prof. Keith Mayes
Royal Holloway University of London
10-11:00am Tuesday, 10 October 2017, ITE 325, UMBC
Smart Cards and RFIDs exist with a range of capabilities and are used in their billions throughout the world. The simpler devices have poor security, however, for many years, high-end smart cards have successfully been used in a range of systems such as banking, passports, mobile communication, satellite TV etc. Fundamental to their success is a specialist design to offer remarkable resistance to a wide range of attacks, including physical, side-channel and fault. This talk describes a range of known attacks and the countermeasures that are employed to defeat them.
Prof. Keith Mayes is the Head of the School of Mathematics and Information Security at Royal Holloway University of London. He received his BSc (Hons) in Electronic Engineering in 1983 from the University of Bath, and his PhD degree in Digital Image Processing in 1987. He is an active researcher/author with 100+ publications in numerous conferences, books and journals. His interests include the design of secure protocols, communications architectures and security tokens as well as associated attacks/countermeasures. He is a Fellow of the Institution of Engineering and Technology, a Founder Associate Member of the Institute of Information Security Professionals, a Member of the Licensing Executives Society and a member of the editorial board of the Journal of Theoretical and Applied Electronic Commerce Research (JTAER).
The post talk: Keith Mayes on Attacks on Smart Cards, RFIDs and Embedded System appeared first on Department of Computer Science and Electrical Engineering.
]]>
Attacks on Smart Cards, RFIDs and Embedded Systems Prof. Keith Mayes Royal Holloway University of London 10-11:00am Tuesday, 10 October 2017, ITE 325, UMBC Smart Cards and RFIDs exist...
https://www.csee.umbc.edu/2017/10/talk-keith-mayes-attacks-smart-cards-rfids-embedded-system-cybersecurity-rfid/
https://beta.my.umbc.edu/api/v0/pixel/news/72618/guest@my.umbc.edu/f693b6777313d350fc774fad7d734ed2/api/pixel
computer-engineering
computer-science
cybersecurity
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Fri, 06 Oct 2017 21:46:20 -0400


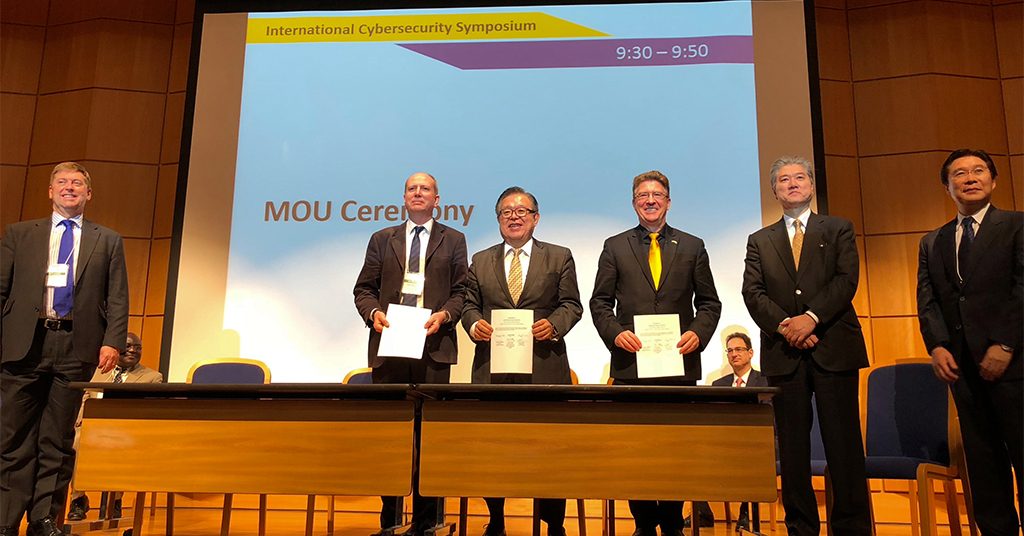 University leaders, including Karl V. Steiner, third from right, signed the three-nation agreement in a ceremony at the sixth International Cybersecurity Symposium in Japan. Photo courtesy of Karl V. Steiner
University leaders, including Karl V. Steiner, third from right, signed the three-nation agreement in a ceremony at the sixth International Cybersecurity Symposium in Japan. Photo courtesy of Karl V. Steiner