Talk: Lance Hoffman (GWU) Cyber Policy Challenges, 12-1pm 4/24 online

The UMBC Cyber Defense Lab presents
Cyber Policy Challenges
Lance J. Hoffman
Distinguished Professor, George Washington University
12–1:00 pm, Friday, 24 April 2020
System attackers and defenders operate on a constantly changing battlefield, and some of the more serious conflicts involving nation-states could be considered acts of war, though we are still in the early stages of defining war in cyberspace. Policies for security and privacy can vary wildly, and have important personal, national, and global consequences for privacy, free speech, censorship, and other issues. Things get even more complicated with the advent of the Internet of Things, where (mostly unsophisticated) users may think they have more control than they actually do and can make bad mistakes. Various ethical issues related to the development of these systems, including bias in artificial intelligence and what harm to choose when harm is unavoidable have only started to be examined. This talk will provide both historical context and some discussion of topical issues such as Zoombombing and the security of electronic voting systems as compared to mail ballots and traditional voting.
Professor Lance J. Hoffman is the author or editor of numerous articles and five books on computer security and privacy. He developed the first regularly offered course on computer security at the University of California, Berkeley in 1970. A Fellow of the Association for Computing Machinery and a member of the Cyber Security Hall of Fame, Dr. Hoffman institutionalized the ACM Conference on Computers, Freedom, and Privacy. He has served on a number of Advisory Committees including those of Federal Trade Commission and the Department of Homeland Security and has testified before Congress on security and privacy-related issues. He is the principal investigator of the CyberCorps program at GWU. Dr. Hoffman earned his Ph. D. in Computer Science from Stanford University, after a B.S. in Mathematics from Carnegie Mellon University.
Host: Alan T. Sherman, *protected email* Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming CDL meetings: May 8, Jason Wells (UMBC SFS scholar) law enforcement; May 22, Spring SFS Meeting at UMBC, 9:30am-2pm, ITE456
The post Talk: Lance Hoffman (GWU) Cyber Policy Challenges, 12-1pm 4/24 online appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Cyber Policy Challenges Lance J. Hoffman Distinguished Professor, George Washington University 12–1:00 pm, Friday, 24 April 2020 remotely via WebEx...
https://www.csee.umbc.edu/2020/04/talk-lance-hoffman-gwu-cyber-policy-challenges/
https://beta.my.umbc.edu/api/v0/pixel/news/92101/guest@my.umbc.edu/82505162580cdf42c92f5a6e2c15d321/api/pixel
cybersecurity
news
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Sat, 11 Apr 2020 12:15:46 -0400
Sat, 11 Apr 2020 12:15:46 -0400
Online Talks Double Feature: Blockchain and Network Defense, 12-2 Fri 3/27, UMBC
UMBC will hold a double feature with two online security-oriented talks from 12:00 pm to 2:00 pm EDT on Friday, March 27. Both talks will be shared via Webex.

From 1:00-2:00 pm, Professor Dr. John Mitchell of Stanford University will give a Lockheed Martin Distinguished lecture on “Will Blockchain Change Everything“. Join the presentation online at 1:00 pm EDT at https://umbc.webex.com/meet/joshi.
Far from serving only as a foundation for cryptocurrency, blockchain technology provides a general framework for trusted distributed ledgers. Over the past few years, their popularity has grown tremendously, as shown by the number of companies and efforts associated with the Linux Foundation’s Hyperledger project, for example. From a technical standpoint, a blockchain combines a storage layer, networking protocols, a consensus layer, and a programmable transaction layer, leveraging cryptographic operations. The distributed state machine paradigm provides atomicity and transaction rollback, while consensus supports distributed availability as well as certain forms of fair access. From an applications perspective, blockchains appeal to distributed networks of independent agents, as arise in supply chain, credentialing, and decentralized financial services. The talk will look at the potential for radical change as well as specific technical challenges associated with verifiable consensus protocols and trustworthy smart contracts.

From 12:00-1:00 pm EDT Col. Dan Yaroslaski, a former operations officer at the Marine Forces Cyberspace Command will talk on “Hard-Learned Lesson in Defense of a Network“. You can join the presentation online at 12:00 pm at https://umbc.webex.com/meet/sherman.
Often network defenders fail to take into account organizational culture when attempting to provide a secure, reliable, and usable enterprise network. Users and process leaders often fall victim to the false allure of the value of networked systems, without asking the question, “Should this be networked?” Collectively, organizations also forget that networks are a combination of the humans who use the network, the personas we all have to form to gain access to this manmade domain, and the interplay of logical and physical network architecture manifested in geographical locations. The value of some simple military principles—including defense-in-depth, mission focus, redundancy, and resiliency versus efficiency—can help a network defender better advise everyone from the “C Suite” decision-makers to the average network user, on how to have a secure network while accepting reasonable limitations.
The post Online Talks Double Feature: Blockchain and Network Defense, 12-2 Fri 3/27, UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC will hold a double feature with two online security-oriented talks from 12:00 pm to 2:00 pm EDT on Friday, March 27. Both talks will be shared via Webex. From 1:00-2:00 pm,...
https://www.csee.umbc.edu/2020/03/online-talks-double-feature-blockchain-and-network-defense-12-2-fri-3-27-umbc/
https://beta.my.umbc.edu/api/v0/pixel/news/91615/guest@my.umbc.edu/02d72add2655694ae942c1b404c60363/api/pixel
computer-science
cybersecurity
news
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Thu, 26 Mar 2020 22:50:30 -0400
JHU/APL CIRCUIT internship program information session, 3pm Fri 1/31
JHU/APL CIRCUIT internship program information session
3:00-4:00 pm Friday, 31 January 2020
ITE 459, UMBC
There will be a special information session on the JHU/APL CIRCUIT internship program from 3:00 pm to 4:30 pm on Friday, 31 January 2020 in room ITE 459.
This session is for undergraduates who want to spend their summer (June through August) getting paid to do mentored research at the Johns Hopkins University Applied Physics Lab. The research areas include AI, data science, cybersecurity, precision medicine, and planetary exploration.
Interns selected for the program will do mission-oriented research on-site at JHU/APL in Laurel MD mentored by STEM professionals. There will also be year-round opportunities for engagement and enrichment. The selection for an internship will be based on a combination of potential, need and commitment.
Email *protected email* or *protected email* with questions.
The post JHU/APL CIRCUIT internship program information session, 3pm Fri 1/31 appeared first on Department of Computer Science and Electrical Engineering.
]]>
JHU/APL CIRCUIT internship program information session 3:00-4:00 pm Friday, 31 January 2020 ITE 459, UMBC There will be a special information session on the JHU/APL CIRCUIT...
https://www.csee.umbc.edu/2020/01/jhu-apl-circuit-internship-program-information-session-3pm-fri-1-31/
https://beta.my.umbc.edu/api/v0/pixel/news/89804/guest@my.umbc.edu/78328c3f0e19647545384211b4aa76f6/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
machine-learning
news
research
students
uncategorized
undergraduate
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Wed, 22 Jan 2020 16:05:36 -0500
Wed, 01 Jan 2020 16:05:36 -0500
UMBC Cyberdawgs win first place in the 2019 DOE CyberForce Competition
 UMBC’s CyberDawgs win first place in the 2019 DOE Cyberforce Competition
UMBC’s CyberDawgs win first place in the 2019 DOE Cyberforce CompetitionCyberdawgs place first out of 105 teams in DOE’s 5th CyberForce Competition
Congratulations to the UMBC CyberDawgs team for their first place finish in a field of 105 collegiate teams in the U.S. Department of Energy’s Fifth Annual CyberForce Competition. The distributed event was held at ten of the DOE’s National Laboratories and challenged 105 teams to defend a simulated energy infrastructure from cyber-attacks.
The took place on November 15 and 16 with the goal of bolstering the U.S. cybersecurity workforce by extending skill-building opportunities for students, offering memorable hands-on experiences and highlighting the crucial role this field plays in preserving national energy security. The Cyberdawgs participated at the Argonne National Laboratory site in Illinois.
During the competition, teams competed to defend their simulated infrastructure from attacks by adversarial “red teams” composed of industry professionals, all while maintaining service for their “green team” customers, played by volunteers. The scenarios included simulated industrial control system components, real-world anomalies and constraints, and interaction with users of the systems.
Teams were scored on their success in protecting the infrastructure against attacks while ensuring the usability of the system, with additional points awarded for innovative ideas and defenses.
The team that competed in this year’s competition was chosen from members of the CyberDawgs student group, composed of students from a variety of majors who share a common interest in computer and network security. No prior experience is required to join and any UMBC students who want to learn more about cybersecurity and learn new skills in the field are encouraged to subscribe to its mailing list and attend meetings.
The CyberDawgs group is advised by CSEE faculty Charles Nicholas and Richard Forno.
The post UMBC Cyberdawgs win first place in the 2019 DOE CyberForce Competition appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC’s CyberDawgs win first place in the 2019 DOE Cyberforce Competition Cyberdawgs place first out of 105 teams in DOE’s 5th CyberForce Competition Congratulations to the UMBC CyberDawgs...
https://www.csee.umbc.edu/2019/11/umbc-cyberdawgs-win-first-place-2019-doe-cyberforce-competition-argonne-cybersecurity-security/
https://beta.my.umbc.edu/api/v0/pixel/news/88544/guest@my.umbc.edu/ee7b8df122690fe7ad2794a05a16674d/api/pixel
csee
cybersecurity
news
students
uncategorized
undergraduate
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
8
0
false
Sun, 17 Nov 2019 17:25:26 -0500
talk: Analysis of the Secure Remote Password (SRP) Protocol Using CPSA

The UMBC Cyber Defense Lab presents
Analysis of the Secure Remote Password (SRP) Protocol Using CPSA
Erin Lanus, UMBC Cyber Defense Lab
12:00–1:00pm, Friday, 6 September 2019, ITE 227, UMBC
Joint work with Alan Sherman, Richard Chang, Enis Golaszewski, Ryan Wnuk-Fink, Cyrus Bonyadi, Mario Costa, Moses Liskov, and Edward Zieglar
Secure Remote Password (SRP) is a widely deployed password authenticated key exchange (PAKE) protocol used in products such as 1Password and iCloud Keychain. As with other PAKE protocols, the two participants in SRP use knowledge of a pre-shared password to authenticate each other and establish a session key. I will explain the SRP protocol and security goals it seeks to achieve. I will demonstrate how to model the protocol using the Cryptographic Protocol Shapes Analyzer (CPSA) tool and present my analysis of the shapes produced by CPSA.
Erin Lanus earned her Ph.D. in computer science in May 2019 from Arizona State University. Dr. Lanus is currently conducting research with Professor Sherman’s Protocol Analysis Lab at UMBC. Her previous results include how to use state to enable CPSA to reason about time in forced-latency protocols. Her research also explored algorithmic approaches to constructing combinatorial arrays employed in interaction testing and the creation of a new type of array for attribute distribution to achieve anonymous authorization in attribute-based systems. In October she will begin as a research assistant professor at Virginia Tech’s Hume Center in Northern Virginia. email: *protected email*
Support for this research was provided in part by grants to CISA from the Department of Defense, CySP grants H98230-17-1-0387 and H98230-18-0321.
The post talk: Analysis of the Secure Remote Password (SRP) Protocol Using CPSA appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Analysis of the Secure Remote Password (SRP) Protocol Using CPSA Erin Lanus, UMBC Cyber Defense Lab 12:00–1:00pm, Friday, 6 September 2019, ITE...
https://www.csee.umbc.edu/2019/09/talk-analysis-of-secure-remote-password-srp-protocol-using-cpsa-umbc-cybersecurity/
https://beta.my.umbc.edu/api/v0/pixel/news/86326/guest@my.umbc.edu/fa69f8ed49100aecdbfa8e0cfc867b00/api/pixel
cybersecurity
news
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Tue, 03 Sep 2019 22:21:17 -0400
Tue, 03 Sep 2019 22:21:17 -0400
CSEE faculty Ben Shariati co-author of NIST guide on mobile device security and privacy
Dr. Ben Shariati co-author of NIST guide on mobile device security and privacy
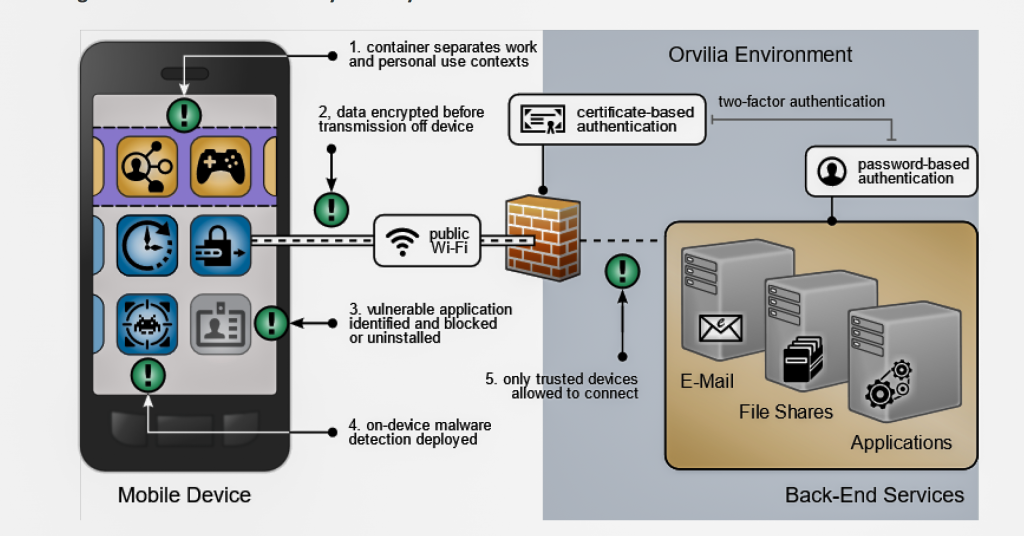
Dr. Behnam Shariati, Assistant Director of the UMBC Graduate Cybersecurity Program, is one of the authors of a new NIST Cybersecurity Practice Guide guide on how organizations can use standards-based, commercially available products to help meet their mobile device security and privacy needs. Dr. Shariati is also a lecturer in Cybersecurity graduate program and oversees its operations at the Universities at Shady Grove in Rockville, MD.
To address the challenge of securing mobile devices while managing risks, the National Cybersecurity Center of Excellence (NCCoE) at the National Institute of Standards and Technology (NIST) built a laboratory environment to explore how various mobile security technologies can be integrated within an enterprise’s network.
A draft version of the document is available as NIST SPECIAL PUBLICATION 1800-21A, Mobile Device Security, Corporate-Owned Personally-Enabled (COPE) and NIST solicits comments on it by September 23, 2019.
From the summary:
“The rapid pace at which mobile technologies evolve requires regular reevaluation of a mobility program to ensure it is accomplishing its security, privacy, and workplace functionality. Built-in mobile protections may not be enough to fully mitigate the security challenges associated with mobile information systems. Usability, privacy, and regulatory requirements each influence which mobile security technologies and security controls are going to be well-suited to meet the needs of an organization’s mobility program.
The goal of the Mobile Device Security: Corporate-Owned Personally-Enabled (COPE) project is to provide an example solution demonstrating how organizations can use a standards-based approach and commercially available technologies to meet their security needs for using mobile devices to access enterprise resources.
The sample solution details tools for an enterprise mobility management (EMM) capability located on-premises, mobile threat defense (MTD), mobile threat intelligence (MTI), application vetting, secure boot/image authentication, and virtual private network (VPN) services.”
This NCCoE project is the first in a series on Mobile Device Security for Enterprises. The next one, Mobile Device Security: Bring Your Own Device (BYOD), is under development.
The post CSEE faculty Ben Shariati co-author of NIST guide on mobile device security and privacy appeared first on Department of Computer Science and Electrical Engineering.
]]>
Dr. Ben Shariati co-author of NIST guide on mobile device security and privacy Dr. Behnam Shariati, Assistant Director of the UMBC Graduate Cybersecurity Program, is one of the authors of a...
https://www.csee.umbc.edu/2019/07/csee-faculty-ben-shariati-co-author-of-nist-guide-on-mobile-device-security-and-privacy/
https://beta.my.umbc.edu/api/v0/pixel/news/86104/guest@my.umbc.edu/275cd1fd959f945430fbd68099200067/api/pixel
cybersecurity
news
research
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Tue, 23 Jul 2019 15:41:46 -0400
UMBC partners with five universities in the US, UK, and Japan to launch International Cybersecurity Center of Excellence
 image: Representatives from the partnering institutions at UMBC. Photo by Marlayna Demond ’11 for UMBC.
image: Representatives from the partnering institutions at UMBC. Photo by Marlayna Demond ’11 for UMBC.UMBC partners with five universities in the US, UK, and Japan to launch International Cybersecurity Center of Excellence
UMBC has partnered to create a global university network dedicated to securing critical systems against cyber threats: the International Cybersecurity Center of Excellence (INCS-CoE).
The INCS-CoE has its foundations in a 2018 cybersecurity collaboration that included UMBC, Keio University in Japan, and Royal Holloway University of London. That initial group has now formally expanded to include Northeastern University, Kyushu University in Japan, and Imperial College London.
The INCS-CoE will support the efforts of the participating universities as they work together to address cybersecurity challenges facing society. The collaboration focuses on cybersecurity for critical national infrastructures including information technology, public transit, and financial services. Additionally, the Center of Excellence will include research, advocacy, and education components.
“Trust is one of the key pillars for a free and interconnected world, for commerce and for exchange of information, be it in the real world or in the digital world,” says Karl V. Steiner, UMBC’s vice president for research. “In order for machines to communicate well with each other, we need to put in place policies and technologies that establish a trust basis.”
He explains, “The INCS-CoE is built on a similar strong layer of trust among six institutions from three different continents. This first-of-its-kind global Center of Excellence will enable us to rapidly exchange ideas and find solutions to developing issues in an increasingly networked world.”
In the future, INCS-CoE may expand to include government and corporate partners, says Steiner.
“The challenges this first-of-its-kind partnership aims to solve span a complex set of cybersecurity issues,” said David Luzzi, senior vice provost for research at Northeastern.
Each academic institution has specific strengths and areas of expertise that they bring to the partnership. UMBC’s Center for Cybersecurity and Center for Accelerated Real Time Analytics will be instrumental in contributing to INCS-CoE’s goals for UMBC.
Learn more about the INCS-CoE.
Adapted from a UMBC News article by Megan Hanks, photo by Marlayna Demond ’11 for UMBC.
The post UMBC partners with five universities in the US, UK, and Japan to launch International Cybersecurity Center of Excellence appeared first on Department of Computer Science and Electrical Engineering.
]]>
image: Representatives from the partnering institutions at UMBC. Photo by Marlayna Demond ’11 for UMBC. UMBC partners with five universities in the US, UK, and Japan to launch International...
https://www.csee.umbc.edu/2019/07/umbc-partners-with-five-universities-in-the-us-uk-and-japan-to-launch-international-cybersecurity-center-of-excellence/
https://beta.my.umbc.edu/api/v0/pixel/news/86105/guest@my.umbc.edu/b33e12eacc045094d92a055df1614b80/api/pixel
cybersecurity
news
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Sun, 21 Jul 2019 13:22:14 -0400
talk: Using CPSA to Analyze Force-Latency Protocols, 12-1 4/19

Using CPSA to Analyze Force-Latency Protocols
Dr. Edward Zieglar, National Security Agency
12-1 Friday, 19 April 19, ITE 227
Several cryptographic protocols have been proposed to address the Man-in-the-Middle attack without the prior exchange of keys. This talk will describe a formal analysis of one such protocol proposed by Zooko Wilcox-O’Hearn, the forced-latency defense against the chess grandmaster attack. Using the Cryptographic Protocol Shapes Analyzer (CPSA), we validate the security properties of the protocol through the novel use of CPSA’s state features to represent time. We also describe a small message space attack that highlights how assumptions made in protocol design can affect the security of a protocol in use, even for a protocol with proven security properties.
Edward Zieglar is a security researcher in the Research Directorate of the National Security Agency, where he concentrates on formal analysis and verification of cryptographic protocols and network security. He is also an adjunct professor at UMBC where he teaches courses in networking and network security. He received his master’s and doctoral degrees in computer science from UMBC.
Host: Alan T. Sherman, *protected email*
The post talk: Using CPSA to Analyze Force-Latency Protocols, 12-1 4/19 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Defense Lab Using CPSA to Analyze Force-Latency Protocols Dr. Edward Zieglar, National Security Agency 12-1 Friday, 19 April 19, ITE 227 Several cryptographic protocols have...
https://www.csee.umbc.edu/2019/04/talk-using-cpsa-to-analyze-force-latency-protocols-12-1-4-19/
https://beta.my.umbc.edu/api/v0/pixel/news/83868/guest@my.umbc.edu/f354661fc2364d2b95d67f287e25fe8c/api/pixel
cybersecurity
news
talks
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Thu, 18 Apr 2019 12:34:38 -0400
Learn cybersecurity skills in NSA’s Codebreaker Challenge

Get hands-on cybersecurity and blockchain skills in NSA’s Codebreaker Challenge
NSA’s sixth annual Codebreaker Challenge is a hands-on, cybersecurity engineering challenge in which students work to complete mission-focused objectives and push their university to the top of the competition leaderboard.
The 2018 scenario involves ransomware and blockchain. A new strain of ransomware has managed to penetrate several critical government networks and NSA has been called upon to assist in remediating the infection to prevent massive data losses. For each infected machine, an encrypted copy of the key needed to decrypt the ransomed files has been stored in a smart contract on the Ethereum blockchain and is set to only be unlocked upon receipt of the ransom payment. Your mission is to ultimately (1) find a way to unlock the ransomware without giving in to the attacker’s demands and (2) figure out a way to recover all of the funds already paid by other victims. Are YOU up to the challenge?
UMBC students did well, both individually and as a group, in previous challenges. Let’s make it to the top of the leaderboard this year.
Feedback from previous iterations of the challenge showed that students were able to learn a great deal from participating. Each student receives a slightly different set of challenge binaries and associated files, so that one student’s solution won’t work for someone else. The binaries are similar enough so that students can work together to understand the problems and develop approaches to solutions and hen implement them independently and register their results.
The 2018 challenge consists of a series of tasks that are worth a varying amount of points based upon their difficulty. In previous years, tasks had to be solved in order to unlock the next task and rankings were based upon the quantity of solvers that progressed the furthest from each school. This way of ranking heavily weighted progression above participation and did not allow for skipping ahead if a particular task became a stumbling block. So to address these issues, all tasks will be available immediately upon registration and can be solved in any order. The point value associated with each task is based on relative difficulty and schools will be ranked according to total number of points accumulated by their students. It is still recommended to solve tasks in order since the tasks flow with the storyline, but that is no longer a requirement.
The post Learn cybersecurity skills in NSA’s Codebreaker Challenge appeared first on Department of Computer Science and Electrical Engineering.
]]>
Get hands-on cybersecurity and blockchain skills in NSA’s Codebreaker Challenge NSA’s sixth annual Codebreaker Challenge is a hands-on, cybersecurity engineering challenge in...
https://www.csee.umbc.edu/2018/09/learn-cybersecurity-skills-in-nsas-codebreaker-challenge/
https://beta.my.umbc.edu/api/v0/pixel/news/78824/guest@my.umbc.edu/b5c63a73e1d311c9178ad83678684ddf/api/pixel
csee
cybersecurity
students
uncategorized
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
3
0
true
Sun, 23 Sep 2018 09:45:05 -0400



 UMBC’s CyberDawgs win first place in the 2019 DOE Cyberforce Competition
UMBC’s CyberDawgs win first place in the 2019 DOE Cyberforce Competition
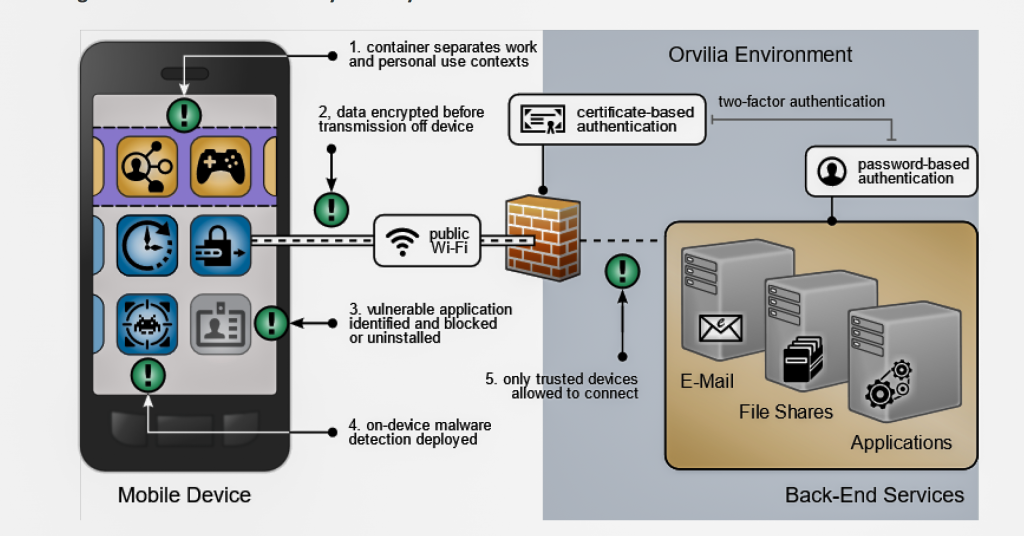
 image: Representatives from the partnering institutions at UMBC. Photo by Marlayna Demond ’11 for UMBC.
image: Representatives from the partnering institutions at UMBC. Photo by Marlayna Demond ’11 for UMBC.
