Professional Graduate Programs Open House, Sat. 10/20 (CYBR, DATA, …)

Professional Graduate Programs Open House, Sat. 10/20
The Fall Open House for UMBC’s Professional Programs (Main Campus offerings) takes place on Saturday, October 20 in the first floor of PAHB from 9:30-11:30am. Students interested in exploring and/or pursuing these graduate programs (degrees and/or certificates) or just want to learn more about these fields are encouraged to register and attend. CSEE students interested in pursuing a BS/MPS option for selected programs (such as CYBR or Data Science) are especially welcome.
Programs represented include
Faculty program directors will be presenting in individual breakout sessions and relevant support staff will be on-hand to provide administrative overviews, answer questions, and mingle. Refreshments will be provided.
If you are interested, please RSVP at https://openhouse.umbc.edu/. If you have questions contact: *protected email*
The post Professional Graduate Programs Open House, Sat. 10/20 (CYBR, DATA, …) appeared first on Department of Computer Science and Electrical Engineering.
]]>
Professional Graduate Programs Open House, Sat. 10/20 The Fall Open House for UMBC’s Professional Programs (Main Campus offerings) takes place on Saturday, October 20 in the first floor of PAHB...
https://www.csee.umbc.edu/2018/10/professional-graduate-programs-open-house-sat-10-20-cybr-data/
https://beta.my.umbc.edu/api/v0/pixel/news/79464/guest@my.umbc.edu/a7478305bcb2d96e34dc23e14d28a5dd/api/pixel
cybersecurity
data-science
engineering-management
events
news
systems-engineering
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Mon, 15 Oct 2018 13:41:41 -0400
MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library
MD-AI Meetup holds 1st event at UMBC
6-8pm Wed 10/3, 7th floor library
A new Maryland-based meetup interest group has been established for Artificial Intelligence (MD-AI Meetup) and will have its first meeting at UMBC this coming Wednesday (Oct 3) from 6:00-8:00pm in the 7th floor of the library. The first meeting will feature a talk by UMCP Professor Phil Resnik on the state of NLP and an AI research agenda. Refreshments will be provided. The meetup is organized by Seth Grimes and supported by TEDCO, local AI startup RedShred, and the Maryland Tech Council.
If you are interested in attending this and possibly future meetings (which will probably be monthly), go to the Meetup site and join (it’s free) and RSVP to attend this meeting (if there’s still room). If you join the meetup and RSVP, you can see who’s registered to attend.
These meetups are good opportunities to meet and network with people in the area who share interests. It’s a great opportunity for students who are will be looking for internships or jobs in the coming year.
The post MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library appeared first on Department of Computer Science and Electrical Engineering.
]]>
MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library A new Maryland-based meetup interest group has been established for Artificial Intelligence (MD-AI Meetup) and will...
https://www.csee.umbc.edu/2018/09/md-ai-meetup-holds-1st-event-at-umbc-6-8pm-wed-10-3-7th-floor-library/
https://beta.my.umbc.edu/api/v0/pixel/news/78988/guest@my.umbc.edu/9f971bc6300fd641f11e4a00be96e2fb/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
events
nlp
robotics
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Sat, 29 Sep 2018 23:50:53 -0400
Sat, 29 Sep 2018 23:50:53 -0400
Machine learning and AI for cybersecurity: a technical chat with DISA

The UMBC Cyber Defense Lab
Machine Learning and Artificial Intelligence: A Technical Chat with the Defense Information Systems Agency
James Curry
Lead Engineer–DoD Cyber Security Range
Defense Information Systems Agency (DISA)
12:00–1:00pm Friday, 28 September 2018, ITE 227, UMBC
A broad reaching brief on the scope and scale of the DISA Mission, followed by a dive into DISA’s efforts to develop Machine Learning and Artificial Intelligence to help defend the nation’s cyber infrastructure. Attendees are highly encouraged to ask questions.
James Curry is the Lead Engineer of the DoD Cyber Security Range (CSR). The CSR’s mission is to replicate the DoD Information Network (DODIN) environment at lab scale, while maintaining high-fidelity realism. As Lead Engineer, Mr. Curry led the design, acquisition, and implementation of two first-of-its-kind technologies: a Virtual Internet Access Point (vIAP) and a Virtual Joint Regional Security Stack (vJRSS). These technologies enable the DoD Workforce to train in an IaaS-on-demand environment that realistically matches DISA’s core infrastructure. Mr. Curry is a Scholarship for Service (SFS) recipient (2008-2009) and received his masters and bachelors of science in computer science from New Mexico Tech. Email: *protected email*
Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming meetings for Fall 2018 include the following.
- Oct 12 Enis Golaszewski, The 2018 UMBC SFS study
- Oct 26 Enis Golaszewski, Using tools in the formal analysis of cryptographic protocols
- Nov 9 Razvan Mintesu, Legal aspects privacy
- Dec 7 Tim Finin, A knowledge graph for cyber threat intelligence
The post Machine learning and AI for cybersecurity: a technical chat with DISA appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab Machine Learning and Artificial Intelligence: A Technical Chat with the Defense Information Systems Agency James Curry Lead Engineer–DoD Cyber Security Range...
https://www.csee.umbc.edu/2018/09/machine-learning-and-ai-for-cybersecurity-a-technical-chat-with-disa/
https://beta.my.umbc.edu/api/v0/pixel/news/78945/guest@my.umbc.edu/1d7e79c959c784379822047cd7dd1737/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
machine-learning
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Thu, 27 Sep 2018 12:49:08 -0400
NSA highlights strong partnership with UMBC through Featured School campaign

NSA highlights strong partnership with UMBC in Featured School campaign
Over the past two decades, UMBC and the National Security Agency (NSA) have developed a strong relationship, which has led to research, internship, and career opportunities for faculty, students, and alumni. UMBC is the first institution to be highlighted in NSA’s Featured School Series, which launched on September 4.
“UMBC’s long-standing partnership with NSA has provided valuable experiences for our students, faculty, and alumni to pursue internships, careers, and collaborative research opportunities,” said President Freeman Hrabowski. “Through this work we are helping to address the need for well-trained cyber professionals by creating a network of talented people to protect the state, nation, and world.”
More than 1100 NSA employees are UMBC alumni, including Darniet Jennings ‘98, M.S. ‘99, Ph.D. ‘03, information systems management. Jennings continued his dissertation research when he took a job at NSA, where he developed a system to manage big data effectively, which was patented in 2010.
The opportunities at NSA include careers in a broad range of disciplines including cybersecurity, engineering, computer science, language, and biological and chemical sciences. Regina Hambleton ‘87, mathematics, has held a number of positions at NSA and is currently the Agency’s deputy director of Engagement and Policy. She began working at NSA while she was a student at UMBC, and participated in a program that allowed her to spend a semester at UMBC taking courses followed by a semester working at NSA.
The partnership between NSA and UMBC also helps prepare an increasing number of graduates for careers in cybersecurity-related fields, to protect the nation from cyber threats.
Charles Nicholas, professor of computer science and electrical engineering, is also highlighted in the Featured School Series campaign. He has spent two sabbaticals at NSA during his time at UMBC, and has mentored students who completed NSA internships, in addition to students who went on to pursue careers at NSA. Nicholas is interested in the intersection of cybersecurity and data science, and the tools that are used to compare malware specimens.
“There are so many opportunities in the intelligence community, including at NSA,” Nicholas says. “It is important for students interested in those careers to develop technical ability, as well as critical and creative thinking, and I enjoy the chance to help them grow those skills.”
For more information about the partnership, and a few UMBC alumni who work at NSA, visit the UMBC page on the NSA website.
Adapted from a UMBC News article by Megan Hanks. Banner image by Marlayna Demond for UMBC.
The post NSA highlights strong partnership with UMBC through Featured School campaign appeared first on Department of Computer Science and Electrical Engineering.
]]>
NSA highlights strong partnership with UMBC in Featured School campaign Over the past two decades, UMBC and the National Security Agency (NSA) have developed a strong relationship, which has...
https://www.csee.umbc.edu/2018/09/nsa-highlights-strong-partnership-with-umbc-through-featured-school-campaign/
https://beta.my.umbc.edu/api/v0/pixel/news/78345/guest@my.umbc.edu/937bbb0918436a7c5bf367c07f1e6516/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
electrical-engineering
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
true
Wed, 05 Sep 2018 09:12:55 -0400
Wed, 05 Sep 2018 09:12:55 -0400
talk: Big Data, Security and Privacy, 11am Wed 5/16

Big Data, Security and Privacy
Prof. Bhavani Thuraisingham, University of Texas at Dallas
11:00-12:00 Wednesday, 16 May 2018, ITE 459, UMBC
The collection, storage, manipulation and retention of massive amounts of data have resulted in serious security and privacy considerations. Various regulations are being proposed to handle big data so that the privacy of the individuals is not violated. For example, even if personally identifiable information is removed from the data, when data is combined with other data, an individual can be identified. This is essentially the inference and aggregation problem that data security researchers have been exploring for the past four decades. This problem is exacerbated with the management of big data as different sources of data now exist that are related to various individuals.
While collecting massive amounts of data causes security and privacy concerns, big data analytics applications in cyber security is exploding. For example, an organization can outsource activities such as identity management, email filtering and intrusion detection to the cloud. This is because massive amounts of data are being collected for such applications and this data has to be analyzed. The question is, how can the developments in big data management and analytics techniques be used to solve security problems? These problems include malware detection, insider threat detection, and intrusion detection.
To address the challenges of big data security and privacy as well as big data analytics for cyber security applications, we organized a workshop sponsored by the National Science Foundation in September 2014 and presented the results in 2015 at an inter-agency workshop in Washington DC. Since then several developments have been reported on big data security and privacy as well as on big data analytics of cyber security. This presenting will summarize the findings of the workshop and discuss the developments and directions.
Dr. Bhavani Thuraisingham is the Louis A. Beecherl, Jr. Distinguished Professor in the Erik Jonsson School of Engineering and Computer Science at The University of Texas at Dallas (UTD) and the Executive Director of UTD’s Cyber Security Research and Education Institute since October 2004. She is also a Senior Research Fellow at Kings College, University of London (2015-2018) and a New America Cyber Security Policy Fellow (2017-2018). Her current research is on integrating cyber security and data science. Prior to joining UTD she worked at the MITRE Corporation for 16 years including a three-year stint as a Program Director at the NSF. She initiated the Data and Applications Security program at NSF and was a member of the Cyber Trust theme. While at MITRE she was a department head and was also a technical advisor to the DoD, the NSA, the CIA, and the IRS. Prior to that, she worked for the commercial industry for six years including at Honeywell, Inc. She is the recipient of numerous awards including the IEEE CS 1997 Technical Achievement Award, the IEEE ISI 2010 Research Leadership Award, ACM SIGSAC 2010 Outstanding Contributions Award, SDPS 2012 Transformative Achievement Gold Medal, 2013 IBM Faculty Award, ACM CODASPY 2017 Innovative and Lasting Research Contributions Award, IEEE CS Services Computing 2017 Research Innovation Award, and Dallas Business Journal 2017 Women in Technology Award. She is a 2003 Fellow of the IEEE and the AAAS and a 2005 Fellow of the British Computer Society. She has published over 120 journal articles, 250 conference papers, 15 books, has delivered over 130 keynote and featured addresses, and is the inventor of six US patents. She has chaired/co-chaired top tier conferences including the Women in Cyber Security (WiCyS) 2016, ACM CCS 2017, and is serving as the Program co-Chair for IEEE ICDM 2018. She also delivered a featured address at the Women in Data Science (WiDS) conference in 2018. She received her PhD at the University of Wales, Swansea, UK, and the earned higher doctorate (D. Eng) from the University of Bristol, England, UK for her published research in secure data management.
The post talk: Big Data, Security and Privacy, 11am Wed 5/16 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Big Data, Security and Privacy Prof. Bhavani Thuraisingham, University of Texas at Dallas 11:00-12:00 Wednesday, 16 May 2018, ITE 459, UMBC The collection, storage, manipulation and retention...
https://www.csee.umbc.edu/2018/05/talk-umbc-bhavani-thuraisingham-big-data-security-privacy-utd/
https://beta.my.umbc.edu/api/v0/pixel/news/76642/guest@my.umbc.edu/973c2409255673a40cf2a563d30a3181/api/pixel
cybersecurity
data-science
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Tue, 15 May 2018 08:44:32 -0400
Thu, 03 May 2018 08:44:32 -0400

The UMBC Cyber Defense Lab presents
Classifying Malware using Data Compression
Charles Nicholas, UMBC
12:00–1:00pm Friday, 20 April 2018, ITE 229
Comparing large binary objects can be tricky and expensive. We describe a method for comparing such strings, using ideas form data compression, that is both fast and effective. We present results from experiments applying this method, which we refer to as LZJD, to the areas of malware classification and digital forensics.
Charles Nicholas (*protected email*) earned his B.S. in Computer Science from the University of Michigan – Flint in 1979, and the M.S. and Ph.D. degrees in Computer Science from Ohio State University in 1982 and 1988, respectively. He joined the Computer Science Department at UMBC in 1988. His research interests include electronic document processing, intelligent information systems, and software engineering. In recent years he has focused on the problems of storing and retrieving information from large collections of documents. Intelligent software agents are an important aspect of this work. Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public.
The post 🗣 talk: Classifying Malware using Data Compression, 12-1 Fri 4/20, ITE229 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Classifying Malware using Data Compression Charles Nicholas, UMBC 12:00–1:00pm Friday, 20 April 2018, ITE 229 Comparing large binary objects can be...
https://www.csee.umbc.edu/2018/04/talk-classifying-malware-using-data-compression-umbc-nicholas-cybersecurity/
https://beta.my.umbc.edu/api/v0/pixel/news/75698/guest@my.umbc.edu/af742b2d5bd0e690e50299c23c102811/api/pixel
ai
cybersecurity
data-science
machine-learning
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Sun, 15 Apr 2018 18:08:07 -0400
Sun, 15 Apr 2018 18:08:07 -0400

Global Impact, Promise & Perils of Blockchain
UMBC Professors Haibin Zhang (Computer Science and Electrical Engineering) and Karuna Joshi (Information Systems) will be panelists for an event focused on the impact, promise and perils of blockchain technologies at the bwtech@UMBC Research & Technology Park. The event will take place from 8:15 to 11:15am on Tuesday, March 20 2018 at and will include breakfast and time for networking. They will be joined on the panel by Marcus Edwards, from Northrop Grumman’s Cyber & Intelligence Mission Solutions, Steve Cook of Verizon Enterprise Solutions, Sean Manion of Science Distributed and moderator Razvan Miutescu of Whiteford, Taylor & Preston, LLP. For more information and tickets are available on eventbrite.
8:15 – 11:15 Tuesday, March 20, 2018
bwtech@UMBC Research & Technology Park
5520 Research Park Drive, Baltimore, MD 21228
Cryptocurrency market capitalizations have soared over the past year and new innovative blockchain applications are continuing to emerge seemingly by the day. However, the average end-user is left to singularly make sense of a vast and global marketplace that is rapidly converging the core tenets of economics and technology development. The future prospects of traditional business and financial models is uncertain as blockchain technology leaves key decision makers in an untenable position to either adopt and adapt or simply be left behind. Industry and academic experts in the field will discuss the pros and cons and opportunities and challenges of this disruptive technology movement.
The post 🗣️ CyberInnovation Briefing: Global Impact, Promise & Perils of Blockchain appeared first on Department of Computer Science and Electrical Engineering.
]]>
Global Impact, Promise & Perils of Blockchain UMBC Professors Haibin Zhang (Computer Science and Electrical Engineering) and Karuna Joshi (Information Systems) will be panelists for an event...
https://www.csee.umbc.edu/2018/03/umbc-cyberinnovation-briefing-global-impact-promise-perils-of-blockchain/
https://beta.my.umbc.edu/api/v0/pixel/news/74886/guest@my.umbc.edu/071b57ec9d7f66fc52ec392277325cb1/api/pixel
computer-science
cybersecurity
data-science
events
faculty-and-staff
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Fri, 16 Mar 2018 08:34:37 -0400
Fri, 16 Mar 2018 08:34:37 -0400
UMBC Cyber Dawgs Capture The Flag Cybersecurity Competition, Sunday March 11
UMBC Cyber Dawgs
Capture The Flag Cybersecurity Competition
The national champion UMBC Cyber Dawgs will hold the second annual computer security Capture The Flag (CTF) competition on Sunday, March 11th from 11am-7pm in the UC Ballroom. This CTF event is a Jeopardy-style competition where teams of four people use their laptops to discover answers to questions about cybersecurity, including network forensics, reverse engineering, reconnaissance, and cryptography. Each question has a point value based upon its difficulty and whichever team has the most points at the end wins!
The competition is open to all current UMBC students and student from a few other nearby schools. Both beginners and experts are welcome to participate.
Prizes will be awarded to the top teams. There will also be door prizes for randomly selected participants as well as T-Shirts for everyone. Some prizes from last year include Raspberry Pis, a Wireless Pineapple Nano, a YARD Stick One, and a Chromebook! Lunch and dinner (Lima’s Chicken) will be provided for everyone.
Students who are interested must register online in advance and bring a laptop to the event. Please note any dietary restrictions on the registration form as well as your T-Shirt size. See the event website for more information
The post UMBC Cyber Dawgs Capture The Flag Cybersecurity Competition, Sunday March 11 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Dawgs Capture The Flag Cybersecurity Competition The national champion UMBC Cyber Dawgs will hold the second annual computer security Capture The Flag (CTF) competition on Sunday,...
https://www.csee.umbc.edu/2018/02/umbc-cyber-dawgs-capture-flag-cybersecurity-competition-sunday-march-11-2018/
https://beta.my.umbc.edu/api/v0/pixel/news/74319/guest@my.umbc.edu/2e5232853dad24355b1c4efb82961c8a/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Mon, 26 Feb 2018 23:53:40 -0500
talk: Towards Hardware Cybersecurity, 11am Tue 2/20, ITE325, UMBC
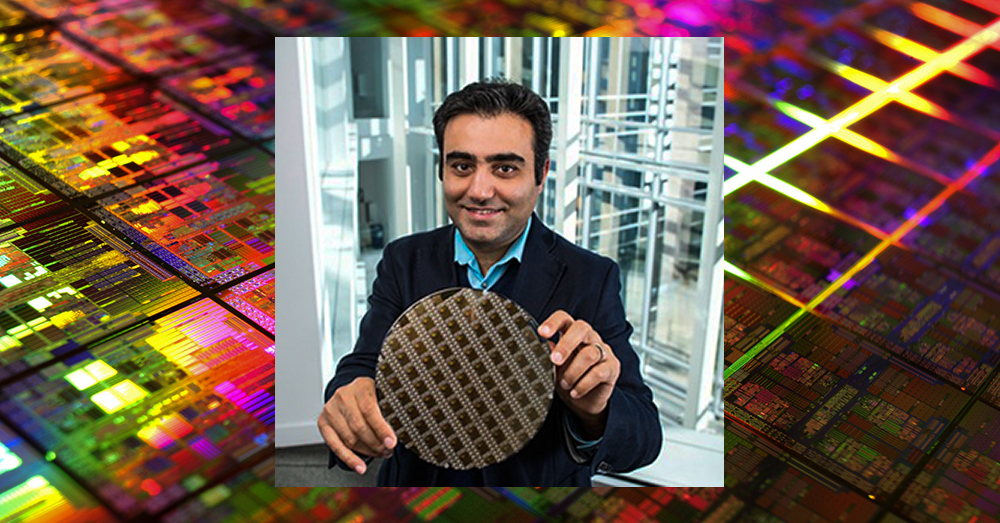
Towards Hardware Cybersecurity
11:00am-12:00pm Tuesday, 20 Febuary 2018, ITE 325, UMBC
Electronic system security, trust and reliability has become an increasingly critical area of concern for modern society. Secure hardware systems, platforms, as well as supply chains are critical to industry and government sectors such as national defense, healthcare, transportation, and finance.
Traditionally, authenticity and integrity of data has been protected with various security protocol at the software level with the underlying hardware assumed to be secure, and reliable. This assumption however is no longer true with an increasing number of attacks reported on the hardware. Counterfeiting electronic components, inserting hardware trojans, and cloning integrated circuits are just few out of many malicious byproducts of hardware vulnerabilities, which need to be urgently addressed.
In the first part of this talk I will address the security and vulnerability challenges in the horizontal integrated hardware development process. I will then present the concept of hybrid spin-transfer torque CMOS look up table based design which is our latest effort on developing a cost-effective solution to prevent physical reverse engineering attacks.
In the second part of my talk I will present how information at the hardware level can be used to address some of the major challenges of software security vulnerabilities monitoring and detection methods. I will first discuss these challenges and will then show how the use of data at the hardware architecture level in combination with an effective machine learning based predictor helps protecting systems against various classes of hardware vulnerability attacks.
I will conclude the talk by emphasizing the importance of this emerging area and proposing a research agenda for the future.
Dr. Houman Homayoun is an Assistant Professor in the Department of Electrical and Computer Engineering at George Mason University. He also holds a courtesy appointment with the Department of Computer Science as well as Information Science and Technology Department. He is the director of GMU’s Accelerated, Secure, and Energy-Efficient Computing Laboratory (ASEEC). Prior to joining GMU, Houman spent two years at the University of California, San Diego, as NSF Computing Innovation (CI) Fellow awarded by the CRA-CCC. Houman graduated in 2010 from University of California, Irvine with a Ph.D. in Computer Science. He was a recipient of the four-year University of California, Irvine Computer Science Department chair fellowship. Houman received the MS degree in computer engineering in 2005 from University of Victoria and BS degree in electrical engineering in 2003 from Sharif University of Technology. Houman conducts research in hardware security and trust, big data computing, and heterogeneous computing, where he has published more than 80 technical papers in the prestigious conferences and journals on the subject. Since 2012 he leads ten research projects, a total of $7.2 million in funding, supported by DARPA, AFRL, NSF, NIST, and GM on the topics of hardware security and trust, big data computing, heterogeneous architectures, and biomedical computing. Houman received the 2016 GLSVLSI conference best paper award for developing a manycore accelerator for wearable biomedical computing. Since 2017 he has been serving as an Associate Editor of IEEE Transactions on VLSI. He is currently serving as technical program co-chair of 2018 GLSVLSI conference.
The post talk: Towards Hardware Cybersecurity, 11am Tue 2/20, ITE325, UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
Towards Hardware Cybersecurity Professor Houman Homayoun George Mason University 11:00am-12:00pm Tuesday, 20 Febuary 2018, ITE 325, UMBC Electronic system security, trust and reliability...
https://www.csee.umbc.edu/2018/02/talk-umbc-towards-hardware-cybersecurity-homayoun/
https://beta.my.umbc.edu/api/v0/pixel/news/73663/guest@my.umbc.edu/346faa5a3054d6e7d0b17a902843a9e0/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Sun, 04 Feb 2018 19:08:51 -0500
Sat, 17 Feb 2018 19:08:51 -0500
talk: A Practitioner’s Introduction to Deep Learning, 1pm Fri 11/17
ACM Tech Talk Series
A Practitioner’s Introduction to Deep Learning
Ashwin Kumar Ganesan, PhD student
1:00-2:00pm Friday, 17 November 2017, ITE325, UMBC
In recent years, Deep Neural Networks have been highly successful at performing a number of tasks in computer vision, natural language processing and artificial intelligence in general. The remarkable performance gains have led to universities and industries investing heavily in this space. This investment creates a thriving open source ecosystem of tools & libraries that aid the design of new architectures, algorithm research as well as data collection.
This talk (and hands-on session) introduce people to some of the basics of machine learning, neural networks and discusses some of the popular neural network architectures. We take a dive into one of the popular libraries, Tensorflow, and an associated abstraction library Keras.
To participate in the hands-on aspects of the workshop, bring a laptop computer with Python installed and install the following libraries using pip. For windows or (any other OS) consider doing an installation of anaconda that has all the necessary libraries.
- numpy, scipy & scikit-learn
- tensorflow / tensoflow-gpu (The first one is the GPU version)
- matplotlib for visualizations (if necessary)
- jupyter & ipython (We will use python2.7 in our experiments)
Following are helpful links:
Contact Nisha Pillai (NPillai1 at umbc.edu) with any questions regarding this event.
The post talk: A Practitioner’s Introduction to Deep Learning, 1pm Fri 11/17 appeared first on Department of Computer Science and Electrical Engineering.
]]>
ACM Tech Talk Series A Practitioner’s Introduction to Deep Learning Ashwin Kumar Ganesan, PhD student 1:00-2:00pm Friday, 17 November 2017, ITE325, UMBC In recent years, Deep Neural...
https://www.csee.umbc.edu/2017/11/practitioner-introduction-deep-learning-umbc-acm-teck-talk/
https://beta.my.umbc.edu/api/v0/pixel/news/72613/guest@my.umbc.edu/e6c0244a9107e67e192737ee9aca6200/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
graduate
news
research
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Tue, 14 Nov 2017 14:56:17 -0500