talk: Hardware Security Kernel for Managing Memory and Instruction Execution, 12pm Fri 2/28
The UMBC Cyber Defense Lab presents
Hardware Security Kernel for Managing Memory and Instruction Execution
Patrick Jungwirth, PhD
Computational and Information Sciences Directorate
Army Research Lab, Aberdeen Proving Ground, USA
12–1 pm Friday, 28 February 2020, ITE 227, UMBC
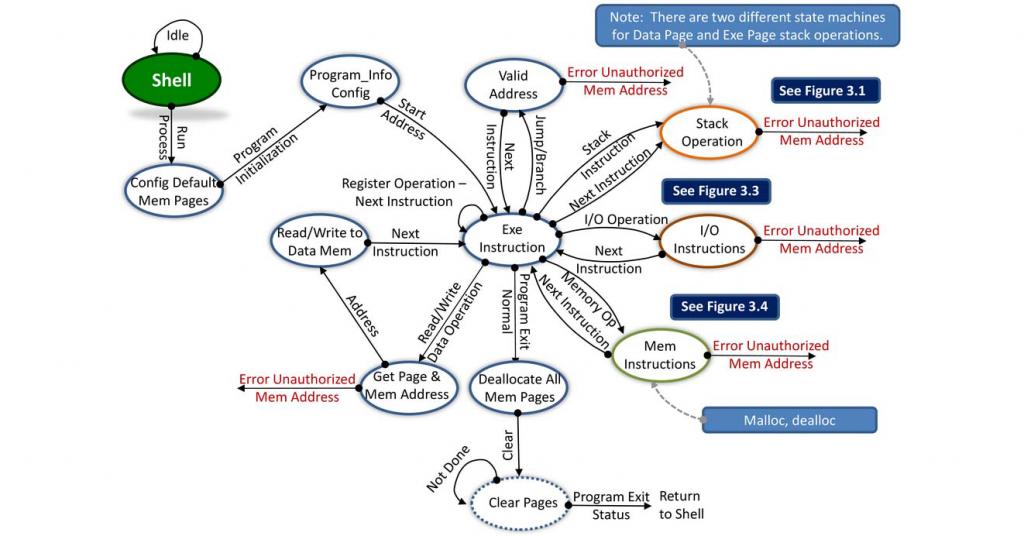
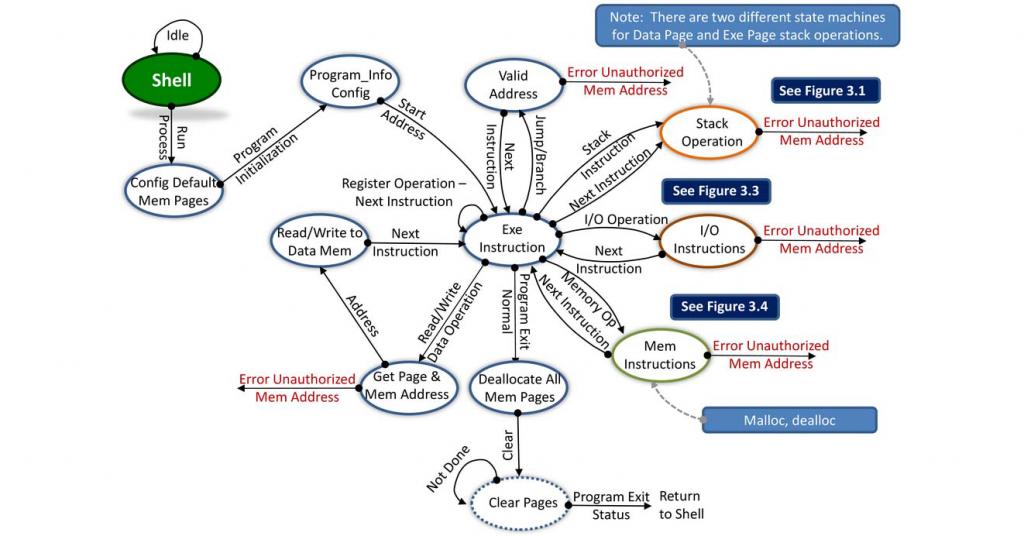
The cybersecurity world faces multiple attack vectors from hardware-level exploits, including cache bank malicious operations, rowhammer, Spectre, Meltdown, and Foreshadow attacks, and software-based attacks including buffer-overflows, et al. Hardware-level exploits bypass protections provided by software-based separation kernels. Current microprocessor execution pipelines are not designed to understand security: they treat malicious instructions, software bugs, and harmless code the same. This presentation explores adding a hardware-level security monitor below the execution pipeline [1,2,3].
[1] P. Jungwirth, et al.: “Hardware security kernel for cyber-defense,” Proc. SPIE 11013, Disruptive Technologies in Information Sciences II, 110130J, Baltimore 10 May 2019); https://doi.org/10.1117/12.2513224
[2] P. Jungwirth, and J. Ross: “Security Tag Fields and Control Flow Management,” IEEE SouthEastCon 2019, Huntsville, AL, April 2019.
[3] P. Jungwirth and D. Hahs: “Transfer Entropy Quantifies Information Leakage,” IEEE SouthEastCon 2019, Huntsville, AL, April 2019.
About the Speaker. Dr. Jungwirth is a computer architecture researcher at the Army Research Lab. Previously he worked for the Aviation and Missile, RDEC in Huntsville, AL. Currently, he is researching hardware state machines to provide simple operating system support (monitor) and control flow integrity in hardware. Dr. Jungwirth is co-inventor of the OS Friendly Microprocessor Architecture, US Patent 9122610. The OS Friendly Microprocessor Architecture includes hardware security features for an operating system and supports near single-cycle context switches in hardware. Email: *protected email*
Host: Alan T. Sherman, *protected email*
Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681.
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public.
Upcoming CDL Meetings:
Mar 13, Hasan Cam, autonomous agents
Mar 27, Dan Yaroslaski, cybercommand
Apr 10, Russ Fink (APL), ransomware
Apr 24, TBA
May 8, Jason Wells, law enforcement
May 22, Spring SFS Meeting at UMBC, 9:30am-2pm, ITE 456
The post talk: Hardware Security Kernel for Managing Memory and Instruction Execution, 12pm Fri 2/28 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Hardware Security Kernel for Managing Memory and Instruction Execution Patrick Jungwirth, PhD Computational and Information Sciences Directorate...
https://www.csee.umbc.edu/2020/02/talk-hardware-security-kernel-for-managing-memory-and-instruction-execution-12pm-fri-2-28/
https://beta.my.umbc.edu/api/v0/pixel/news/90623/guest@my.umbc.edu/73a2ef9aadd73410c584e89816bb8157/api/pixel
computer-engineering
computer-science
cybersecurity
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Thu, 20 Feb 2020 11:57:26 -0500
Lockheed Martin Distinguished Speaker Series
Designing Secure Hardware Systems
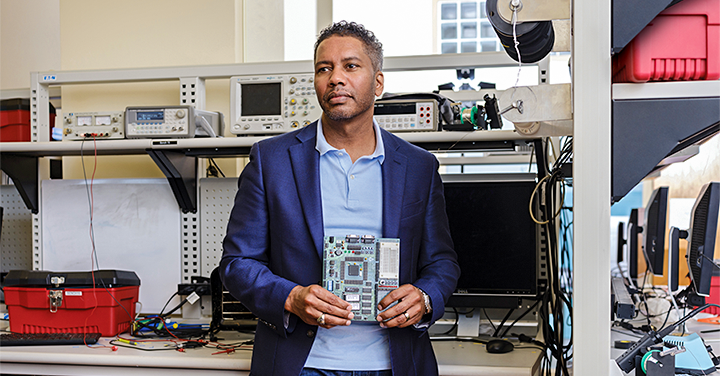
Shawn Blanton
Trustee Professor, Electrical and Computer Engineering
Carnegie Mellon University
1:00-2:00pm Friday 7 Feb. 2020
Commons 329, UMBC
University Center Ballroom
On October 29, 2018, DARPA issued an RFI that stated: “This Request for Information (RFI) from the Defense Advanced Research Projects Agency’s (DARPA) Microsystems Technology Office (MTO) seeks information on technology, concepts, and approaches to support the integration of security capabilities directly into System on Chip (SoC) system design and to enable the autonomous integration and assembly of SoCs.
This RFI and the tens of millions of dollars that the US government has already invested in hardware security research and development is based on the fact that the fabrication of state-of-the-art electronics is now mostly overseas. With the recent announcement that GLOBALFOUNDRIES is going to stop all 7nm development, there is now only one company in the US that continues to pursue advanced semiconductors (Intel). Unfortunately, Intel does not have the same experience of making chips for third parties as does Samsung and (most importantly) TSMC (Taiwan Semiconductor Manufacturing Corporation). As a result, the US government believes it will be forced to fabricate advanced, sensitive electronics overseas in untrusted fabrication facilities. As a result, there is keen interest in design methodologies that mitigate reverse engineering, tampering, counterfeiting, etc.
In this talk, an overview of hardware security will be presented followed by a discussion on a concept called logic locking. This approach will be described and the “back and forth” that is now occurring in the research community involving: (i) vulnerability discovery and (ii) logic locking improvement.
Shawn Blanton is a professor in the Electrical and Computer Engineering Department at Carnegie Mellon University and Associate Director of the SYSU-CMU Joint Institute of Engineering (JIE). In 1995 he received his Ph.D. in Electrical Engineering and Computer Science from the University of Michigan, Ann Arbor. His research interests include various aspects of integrated system tests, testable design, and test methodology development. He has consulted for various companies and is the founder of TestWorks, a Carnegie Mellon University spinout focused on information extraction from IC test data. He is a Fellow of the IEEE and Senior Member of the ACM and served as the program chair for the 2011 International Test Conference.
The post 🔴 talk: Shawn Blanton (CMU); Designing Secure Hardware Systems, 1pm Fri 2/7; Commons 329 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Lockheed Martin Distinguished Speaker Series Designing Secure Hardware Systems Shawn Blanton Trustee Professor, Electrical and Computer Engineering Carnegie Mellon University...
https://www.csee.umbc.edu/2020/02/talk-shawn-blanton-cmu-on-designing-secure-hardware-systems-1pm-fri-2-7/
https://beta.my.umbc.edu/api/v0/pixel/news/90162/guest@my.umbc.edu/8136f036ce8ed4c55bc786ea98ddc9df/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
electrical-engineering
events
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Wed, 05 Feb 2020 09:56:00 -0500
Wed, 05 Feb 2020 09:56:00 -0500
JHU/APL CIRCUIT internship program information session, 3pm Fri 1/31
JHU/APL CIRCUIT internship program information session
3:00-4:00 pm Friday, 31 January 2020
ITE 459, UMBC
There will be a special information session on the JHU/APL CIRCUIT internship program from 3:00 pm to 4:30 pm on Friday, 31 January 2020 in room ITE 459.
This session is for undergraduates who want to spend their summer (June through August) getting paid to do mentored research at the Johns Hopkins University Applied Physics Lab. The research areas include AI, data science, cybersecurity, precision medicine, and planetary exploration.
Interns selected for the program will do mission-oriented research on-site at JHU/APL in Laurel MD mentored by STEM professionals. There will also be year-round opportunities for engagement and enrichment. The selection for an internship will be based on a combination of potential, need and commitment.
Email *protected email* or *protected email* with questions.
The post JHU/APL CIRCUIT internship program information session, 3pm Fri 1/31 appeared first on Department of Computer Science and Electrical Engineering.
]]>
JHU/APL CIRCUIT internship program information session 3:00-4:00 pm Friday, 31 January 2020 ITE 459, UMBC There will be a special information session on the JHU/APL CIRCUIT...
https://www.csee.umbc.edu/2020/01/jhu-apl-circuit-internship-program-information-session-3pm-fri-1-31/
https://beta.my.umbc.edu/api/v0/pixel/news/89804/guest@my.umbc.edu/78328c3f0e19647545384211b4aa76f6/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
machine-learning
news
research
students
uncategorized
undergraduate
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Wed, 22 Jan 2020 16:05:36 -0500
Wed, 01 Jan 2020 16:05:36 -0500
talk: Security for Smart Cyber-Physical Systems, 12-1 5/3, ITE 227

UMBC Cyber Defense Lab
Security for Smart Cyber-Physical Systems
Prof. Anupam Joshi, UMBC
12:00–1:00pm, Friday, 3 May 2019, ITE 227
Smart Cyber-Physical Systems (CPS) are increasingly embedded in our everyday life. Security incidents involving them are often high-profile because of their ability to control critical infrastructure. Stuxnet and the Ukrainian power-grid attack are some notorious attacks reported against CPS which impacted governmental programs to ordinary users. In addition to the deliberate attacks, device malfunction and human error can also result in incidents with grave consequences. Hence the detection and mitigation of abnormal behaviors resulting from security incidents is imperative for the trustworthiness and broader acceptance of smart cyber-physical systems. We propose an automatic behavioral abstraction technique, ABATe, which automatically learns their typical behavior by finding the latent “context” space using available operational data and is used to discern anomalies. We evaluate our technique using two real-world datasets (a sewage water treatment plant dataset and an automotive dataset) to demonstrate the multi-domain adaptability and efficacy of our approach.
Anupam Joshi is the Oros Family Professor and Chair of Computer Science and Electrical Engineering Department at the University of Maryland, Baltimore County(UMBC). He is the Director of UMBC’s Center for Cybersecurity, and one of the USM leads for the National Cybersecurity FFRDC. He is a Fellow of IEEE. Dr. Joshi obtained a B.Tech degree from IIT Delhi in 1989, and a Masters and Ph.D. from Purdue University in 1991 and 1993 respectively. His research interests are in the broad area of networked computing and intelligent systems. His primary focus has been on data management and security/privacy in mobile/pervasive computing environments, and policy driven approaches to security and privacy. He is also interested in Semantic Web and Data/Text/Web Analytics, especially their applications to (cyber) security. He has published over 250 technical papers with an h-index of 79 and over 23,250 citations (per Google scholar), filed and been granted several patents, and has obtained research support from National Science Foundation (NSF), NASA, Defense Advanced Research Projects Agency (DARPA), US Dept of Defense (DoD), NIST, IBM, Microsoft, Qualcom, Northrop Grumman, and Lockheed Martin amongst others
The post talk: Security for Smart Cyber-Physical Systems, 12-1 5/3, ITE 227 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Defense Lab Security for Smart Cyber-Physical Systems Prof. Anupam Joshi, UMBC 12:00–1:00pm, Friday, 3 May 2019, ITE 227 Smart Cyber-Physical Systems (CPS) are...
https://www.csee.umbc.edu/2019/05/umbc-talk-cybersecurity-smart-cyber-physical-systems-cps/
https://beta.my.umbc.edu/api/v0/pixel/news/86106/guest@my.umbc.edu/2e4bbb97c805f4fd3d6ecbc7c7020288/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Wed, 01 May 2019 23:29:49 -0400
talk: The Evolution of Mobile Authentication, 1pm 4/30, ITE325, UMBC

The Evolution of Mobile Authentication
Prof. Keith Mayes, Royal Holloway University of London
1:00pm Tuesday 30 April 2019, ITE325, UMBC
Mobile communication is an essential part or modern life, however it is dependent on some fundamental security technologies. Critical amongst these technologies, is mobile authentication, the ability to identify valid users (and networks) and enable their secure usage of communication services. In the GSM standards and the 3GPP standards that evolved from them, the subscriber-side security has been founded on a removable, attack-resistant smart card known as a SIM (or USIM) card. The presentation explains how this situation came about, and how and why the protocols and algorithms have improved over time. It will cover some work by the author on a recent algorithm for 3GPP and then discuss how Machine-to-Machine and IoT considerations have led to new standards, which may herald the demise of the conventional removable SIM, in favour of an embedded eSIM.
Professor Keith Mayes B.Sc. Ph.D. CEng FIET A.Inst.ISP, is a professor of information security within the Information Security Group (ISG) at Royal Holloway University of London. Prior to his sabbatical, he was the Director of the ISG and Head of the School of Mathematics and Information Security. He is an active researcher/author with 100+ publications in numerous conferences, books and journals. His current research interests are diverse, including, mobile communications, smart cards/RFIDS, the Internet of Things, and embedded systems. Keith joined the ISG in 2002, originally as the Founder Director of the ISG Smart Card Centre, following a career in industry working for Pye TVT, Honeywell Aerospace and Defence, Racal Research and Vodafone. Keith is a Chartered Engineer, a Fellow of the Institution of Engineering and Technology, a Founder Associate Member of the Institute of Information Security Professionals, a Member of the Licensing Executives Society and an experienced company director and consultant. He is active in the UK All Party Parliamentary Group (APPG) on Cyber Security and is an adjunct professor at UMBC.
The post talk: The Evolution of Mobile Authentication, 1pm 4/30, ITE325, UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
The Evolution of Mobile Authentication Prof. Keith Mayes, Royal Holloway University of London 1:00pm Tuesday 30 April 2019, ITE325, UMBC Mobile communication is an essential part or...
https://www.csee.umbc.edu/2019/04/talk-the-evolution-of-mobile-authentication-1pm-4-30-ite325-umbc-3gpp-esim/
https://beta.my.umbc.edu/api/v0/pixel/news/86107/guest@my.umbc.edu/f459a33f3816eb7fdefc2ff80cc3a4b5/api/pixel
computer-engineering
computer-science
cybersecurity
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
false
Mon, 29 Apr 2019 18:34:04 -0400
talk: Why are memory-corruption bugs still a thing?, 10:30am Mon 4/8, ITE325
Why are memory-corruption bugs still a thing?
The challenges of securing software at an assembly level
Doug Britton
CTO, RunSafe Security Inc.
10:30-11:30 Monday, 8 April 2019, ITE346
Methods to chip away at the danger of memory-corruption bugs have been available for some time. Why has the going-price of memory-corruption-based exploits not spiked? If the methods were have a broad-based result in mitigating exploit vectors, there would be a reduction in supply, causing an increase in prices. Also, there would be a reduction in the pool of people qualified to develop zero-days, allowing them to push the prices up. The data suggest that prices have remained generally stable and attackers are able to move with impunity. What are the challenges to large-scale adoption of memory-corruption based mitigation methods.
Doug Britton serves as Chief Technology Officer and Director of RunSafe Security, Inc. Mr. Britton Co-founded Kaprica Security, Inc., in 2011 and serves as its Chief Executive Officer. Prior to his leadership role in Kaprica, Mr. Britton was a cyber-security focused research and development manager at Lockheed Martin. He has an MBA and MS from University of Maryland and a BS in Computer Science from the University of Illinois.
The post talk: Why are memory-corruption bugs still a thing?, 10:30am Mon 4/8, ITE325 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Why are memory-corruption bugs still a thing? The challenges of securing software at an assembly level Doug Britton CTO, RunSafe Security Inc. 10:30-11:30 Monday, 8 April 2019, ITE346...
https://www.csee.umbc.edu/2019/04/talk-why-are-memory-corruption-bugs-still-a-thing-umbc-cybersecurity/
https://beta.my.umbc.edu/api/v0/pixel/news/83516/guest@my.umbc.edu/52431b447531c3ba39864f7200ff8c47/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Sun, 07 Apr 2019 11:00:05 -0400
talk and demo: Exploiting IoT Vulnerabilities, 11:45-1:00pm Mon 2/18

Exploiting IoT Vulnerabilities
Dr. Yatish Joshi, Senior Engineer, Cisco Systems
11:45am-1:00pm Monday, 18 February 2019, ITE 325-B
The past decade has seen explosive growth in the use and deployment of IoT (Internet of Things) devices. According to Gartner there will be about 20.8 billion IoT devices in use by 2020. These devices are seeing wide spread adoption as they are cheap, easy to use and require little to no maintenance. In most cases, setup simply requires using a web or phone app to configure Wi-Fi credentials. Digital home assistants, security cameras, smart locks, home appliances, smart switches, toys, vacuum cleaners, thermostats, leakage sensors etc are examples of IoT devices that are widely used and deployed in home and enterprise environments.

The threat landscape is constantly evolving and threat actors are always on the prowl for new vulnerabilities they can exploit. With traditional attack methods yielding fewer exploits due to the increased focus on security testing, frequent patches, increased user awareness, Threat actors have turned their attention on IoT devices and are exploiting inherent vulnerabilities in these devices. The vulnerabilities, always ON nature, and autonomous mode of operation allow attackers to spy on users, spoof data, or leverage them as botnet infrastructure to launch devastating attacks on third parties. Mirai, a well known IoT malware utilized hundreds and thousands of enslaved IoT devices to launch DDoS attacks on Dyn affecting access to Netflix, Twitter, Github and many other websites. With the release of the Mirai source code numerous variants of the malware are infecting IoT devices across the world and using them to carry out attacks.
These attacks are made possible because the devices are manufactured without security in mind!. In this talk I will demonstrate how one can hack a widely available off-the-shelf IP Camera and router by exploiting the vulnerabilities present in these devices to get on the network, steal personal data, spy on a user, disrupt operation etc. We will also look at what can be done to mitigate the dangers posed by IOT devices.
So attend hack & defend!
Dr. Yatish Joshi is a software engineer in the Firepower division at Cisco Systems where he works on developing new features for Cisco’s security offerings. Yatish has a PhD in Computer Engineering from UMBC. Prior to Cisco Yatish worked as a lecturer at UMBC, and was a senior software engineer developing TV software at Samsung Electronics. When not working, he enjoys reading spy thrillers and fantasy novels.
The post talk and demo: Exploiting IoT Vulnerabilities, 11:45-1:00pm Mon 2/18 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Exploiting IoT Vulnerabilities Dr. Yatish Joshi, Senior Engineer, Cisco Systems 11:45am-1:00pm Monday, 18 February 2019, ITE 325-B The past decade has seen explosive growth in the use and...
https://www.csee.umbc.edu/2019/02/umbc-talk-exploiting-iot-vulnerabilities-security-internet-of-things/
https://beta.my.umbc.edu/api/v0/pixel/news/81984/guest@my.umbc.edu/9dfa6538945e4c821638d88994576150/api/pixel
computer-engineering
computer-science
cybersecurity
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Fri, 08 Feb 2019 22:21:57 -0500
Sun, 17 Feb 2019 16:00:57 -0500
Maryland Data Science Conference, Fri. 1/25, UMBC (new date)
MD Data Science Conference
Friday, 25 January, PAH Concert Hall, UMBC
Miner & Kasch, a AI and data science consulting firm founded by two UMBC alumni, will hold a one-day Data Science Conference at UMBC on Friday, January 25 in the Linehan Concert Hall of the UMBC Performing Arts & Humanities Building. A limited number of free tickets are available for current UMBC students. To attend, you need to register here.
The event was originally scheduled for January 14, but had to be rescheduled due to inclement weather. If you had registered and obtained a ticket earlier, you will need to re-register.
The event brings together local companies and professionals to share what new and exciting things they are doing with their data. It will be attended by business managers, startup founders, software engineers, data scientists, students, and other curious people that want to learn more about the cutting edge of data science, machine learning, and AI. See the conference website for topics and speakers.
The post Maryland Data Science Conference, Fri. 1/25, UMBC (new date) appeared first on Department of Computer Science and Electrical Engineering.
]]>
MD Data Science Conference Friday, 25 January, PAH Concert Hall, UMBC Miner & Kasch, a AI and data science consulting firm founded by two UMBC alumni, will hold a one-day Data Science...
https://www.csee.umbc.edu/2019/01/maryland-data-science-conference-fri-1-25-umbc-new-date/
https://beta.my.umbc.edu/api/v0/pixel/news/81499/guest@my.umbc.edu/a7c10e8671c1c437df7c93a02b6663ae/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Fri, 18 Jan 2019 10:24:02 -0500
Fri, 18 Jan 2019 10:24:02 -0500
MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library
MD-AI Meetup holds 1st event at UMBC
6-8pm Wed 10/3, 7th floor library
A new Maryland-based meetup interest group has been established for Artificial Intelligence (MD-AI Meetup) and will have its first meeting at UMBC this coming Wednesday (Oct 3) from 6:00-8:00pm in the 7th floor of the library. The first meeting will feature a talk by UMCP Professor Phil Resnik on the state of NLP and an AI research agenda. Refreshments will be provided. The meetup is organized by Seth Grimes and supported by TEDCO, local AI startup RedShred, and the Maryland Tech Council.
If you are interested in attending this and possibly future meetings (which will probably be monthly), go to the Meetup site and join (it’s free) and RSVP to attend this meeting (if there’s still room). If you join the meetup and RSVP, you can see who’s registered to attend.
These meetups are good opportunities to meet and network with people in the area who share interests. It’s a great opportunity for students who are will be looking for internships or jobs in the coming year.
The post MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library appeared first on Department of Computer Science and Electrical Engineering.
]]>
MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library A new Maryland-based meetup interest group has been established for Artificial Intelligence (MD-AI Meetup) and will...
https://www.csee.umbc.edu/2018/09/md-ai-meetup-holds-1st-event-at-umbc-6-8pm-wed-10-3-7th-floor-library/
https://beta.my.umbc.edu/api/v0/pixel/news/78988/guest@my.umbc.edu/9f971bc6300fd641f11e4a00be96e2fb/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
events
nlp
robotics
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Sat, 29 Sep 2018 23:50:53 -0400
Sat, 29 Sep 2018 23:50:53 -0400
Machine learning and AI for cybersecurity: a technical chat with DISA

The UMBC Cyber Defense Lab
Machine Learning and Artificial Intelligence: A Technical Chat with the Defense Information Systems Agency
James Curry
Lead Engineer–DoD Cyber Security Range
Defense Information Systems Agency (DISA)
12:00–1:00pm Friday, 28 September 2018, ITE 227, UMBC
A broad reaching brief on the scope and scale of the DISA Mission, followed by a dive into DISA’s efforts to develop Machine Learning and Artificial Intelligence to help defend the nation’s cyber infrastructure. Attendees are highly encouraged to ask questions.
James Curry is the Lead Engineer of the DoD Cyber Security Range (CSR). The CSR’s mission is to replicate the DoD Information Network (DODIN) environment at lab scale, while maintaining high-fidelity realism. As Lead Engineer, Mr. Curry led the design, acquisition, and implementation of two first-of-its-kind technologies: a Virtual Internet Access Point (vIAP) and a Virtual Joint Regional Security Stack (vJRSS). These technologies enable the DoD Workforce to train in an IaaS-on-demand environment that realistically matches DISA’s core infrastructure. Mr. Curry is a Scholarship for Service (SFS) recipient (2008-2009) and received his masters and bachelors of science in computer science from New Mexico Tech. Email: *protected email*
Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming meetings for Fall 2018 include the following.
- Oct 12 Enis Golaszewski, The 2018 UMBC SFS study
- Oct 26 Enis Golaszewski, Using tools in the formal analysis of cryptographic protocols
- Nov 9 Razvan Mintesu, Legal aspects privacy
- Dec 7 Tim Finin, A knowledge graph for cyber threat intelligence
The post Machine learning and AI for cybersecurity: a technical chat with DISA appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab Machine Learning and Artificial Intelligence: A Technical Chat with the Defense Information Systems Agency James Curry Lead Engineer–DoD Cyber Security Range...
https://www.csee.umbc.edu/2018/09/machine-learning-and-ai-for-cybersecurity-a-technical-chat-with-disa/
https://beta.my.umbc.edu/api/v0/pixel/news/78945/guest@my.umbc.edu/1d7e79c959c784379822047cd7dd1737/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
machine-learning
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Thu, 27 Sep 2018 12:49:08 -0400