UMBC faculty, alumni and partners discuss cybersecurity and industry challenges

UMBC faculty, alumni and corporate partners discuss cybersecurity and industry challenges
Cybersecurity is regularly a headliner in the news, especially when personal information stored online has been compromised, whether through a breach, hack, or threat. On Thursday, December 7, UMBC hosted experts from industry and academia at the National Press Club to discuss the cyber challenges professionals face, and how those groups can work together to prepare future generations of cybersecurity professionals.
Scott Shane, a reporter with The New York Times, led the discussion with five panelists representing industry, small business, and higher education. “I think it’s fair to say the internet was built without adequate attention to security,” stated Shane, who writes about cyber and information attacks regularly. “It’s almost like somebody who starts a bank with branches all over the world, and after it’s up and running and has millions of account holders, suddenly starts to think about safes, locks on the doors and bulletproof glass. I think that’s sort of the stage that we’re at right now.”
UMBC President Freeman Hrabowski and Anupam Joshi, professor and chair of computer science and electrical engineering, and director of the Center for Cybersecurity at UMBC, were joined by alumni and partners who have been working on the challenge of educating the workforce together. Hrabowski explained that there are currently about 350,000 unfilled cybersecurity jobs, and that number is expected to continue to grow. By 2021, it is anticipated that there will be approximately three million job openings in cyber-related fields.
Over the course of his professional career, Nigel Faulkner, chief technology officer at T. Rowe Price, has experienced the emergence of technology and many changes. “As the CTO of a medium-large company, cyber is a defensive investment for us. The best thing that can happen is nothing happens,” Faulkner said, adding that he is always thinking about whether the company is investing enough, doing the right thing, and making the right connections in the industry to keep clients’ information safe.
As president and founder of TCecure, LLC, and cybersecurity academic innovation officer for University System of Maryland (USM), Tina Williams ’02, computer science, shared the importance of building security into technology from the beginning, rather than adding these features on at the “tail end of a development cycle.” Not only does her company handle security, they also monitor threats and risks that can compromise the technology’s health. In her role at USM, Williams represents the system as a whole to integrate academia and academic research, relationships, and resources into what’s taking place nationally, at the Federally Funded Research and Development Centers.
As head of UMBC’s Center for Cybersecurity, Joshi explained that UMBC is combating these national challenges by partnering with industry and government leaders to conduct research that addresses specific real-world needs that benefit both. Collaborative relationships, such as UMBC’s work with Northrop Grumman and T. Rowe Price, is one way that UMBC is working to cultivate the next generation of cybersecurity talent.
As an alumna of UMBC and a current employee at Northrop Grumman, Lauren Mazzoli ’15, computer science and mathematics, M.S. ’17, computer science, a systems engineer in the Future Technical Leaders Program at Northrop Grumman, discussed her experience in the Cyber Scholars Program. The Cyber Scholars Program works to increase the participation of women and underrepresented minorities in the field. Mazzoli explained that her experience at UMBC, in the Cyber Scholars Program, and working alongside mentors on and off-campus led her to be involved with continuing to encourage women to pursue careers in cybersecurity. “For me it’s been a product of the relationship between academia and industry, that have allowed me to find my own career path, and at the same time help others find theirs,” she explained, noting her passion for helping students consider careers in cybersecurity and related fields.
“We know there’s a huge workforce that we need and we can’t fill that pipeline. So yes, we need more women, yes, we need students of all backgrounds, but we need diversity of thought, experience, education, and problem-solving skills,” said Mazzoli, adding that it is important for students to know from a young age that cybersecurity is a field they can pursue.
Adapted from a UMBC News article article written by Megan Hanks Photo by Abnet Shiferaw ’11, visual arts.
The post UMBC faculty, alumni and partners discuss cybersecurity and industry challenges appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC faculty, alumni and corporate partners discuss cybersecurity and industry challenges Cybersecurity is regularly a headliner in the news, especially when personal information stored...
https://www.csee.umbc.edu/2017/12/umbc-faculty-alumni-and-partners-discuss-cybersecurity-and-industry-challenges/
https://beta.my.umbc.edu/api/v0/pixel/news/72825/guest@my.umbc.edu/dfa76de7478d788248e005724b8a3d28/api/pixel
alumni
cybersecurity
events
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
true
Thu, 14 Dec 2017 20:39:18 -0500
National Press Club Event: Rise to Dominance of Cybersecurity Challenges

National Press Club Event: Rise to Dominance of Cybersecurity Challenges
Join UMBC and industry and government experts for a panel on how cybersecurity touches our everyday lives and how journalists can engage a wide range of readers in cybersecurity news. This panel will touch on topics ranging from online commerce to national conversations about security leaks. It will also explore how to best prepare the next generation of cybersecurity leaders to effectively tackle the challenges we are facing.
Thursday, 7 December 2017, 4:00-6:00pm
National Press Club, Washington, D.C.
Light refreshments will be served.
Registration by December 4 preferred.
Moderator: New York Times reporter Scott Shane
Featured panelists include:
- Freeman A. Hrabowski, III, UMBC President
- Nigel Faulkner, CIO, T. Rowe Price
- Anupam Joshi, Director, UMBC Center for Cybersecurity; Professor and Chair, Department of Computer Science and Electrical Engineering
- Lauren Mazzoli ’15, M.S ’17, Systems Engineer, Future Technical Leaders Program, Northrop Grumman Corporation
- Tina Williams ’02, President, TCecure, LLC; Cybersecurity Academic Innovation Officer for University System of Maryland
Contact Candace Dodson-Reed at *protected email* with questions.
The post National Press Club Event: Rise to Dominance of Cybersecurity Challenges appeared first on Department of Computer Science and Electrical Engineering.
]]>
National Press Club Event: Rise to Dominance of Cybersecurity Challenges Join UMBC and industry and government experts for a panel on how cybersecurity touches our everyday lives and how...
https://www.csee.umbc.edu/2017/12/national-press-club-event-rise-dominance-cybersecurity-challenges-umbc/
https://beta.my.umbc.edu/api/v0/pixel/news/72610/guest@my.umbc.edu/e5172ceea6bcf644bd9f3a74da32e36c/api/pixel
cybersecurity
events
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Fri, 01 Dec 2017 23:02:03 -0500
talk: PKI in the Defense Information Systems Agency, 12-1 Fri 12/1, ITE228

UMBC Cyber Defense Lab
PKI in the Defense Information Systems Agency (DISA)
Phil Scheffler
Chief Engineer – Joint Enablers
ID2 – Cyber Development Directorate
Defense Information Systems Agency
12:00–1pm, Dec 1, 2017, ITE 228
As a combat support agency within the Department of Defense, DISA faces unlimited challenges with Public-Key Infrastructure (PKI). Chief Engineer Phil Scheffler will shed some light on DoD PKI at the Defense Information Systems Agency (DISA), and challenges deploying PKI across such a large enterprise.
Philip Scheffler is the Chief Engineer for the ID2 Joint Enablers Division in DISA’s Cyber Development Directorate. He joined DISA in 2010 as an NSA Information Assurance Scholar on the Public Key Enablement team. Over the past 7 years, Phil has been the technical lead for various PKI initiatives for the DoD. Mr. Scheffler has a B.A. in Economics from Brandeis University and a M.S in Computer Science from Boston University.
Host: Alan T. Sherman, *protected email*
The post talk: PKI in the Defense Information Systems Agency, 12-1 Fri 12/1, ITE228 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Defense Lab PKI in the Defense Information Systems Agency (DISA) Phil Scheffler Chief Engineer – Joint Enablers ID2 – Cyber Development Directorate Defense Information...
https://www.csee.umbc.edu/2017/11/umbc-talk-pki-defense-information-systems-agency/
https://beta.my.umbc.edu/api/v0/pixel/news/72611/guest@my.umbc.edu/56139280fe936ae540e898bc5ad6771f/api/pixel
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Wed, 29 Nov 2017 21:37:22 -0500
talk: An Introduction to Quantum Cryptography, Noon Friday 11/17, ITE231

The UMBC Cyber Defense Lab presents
An Introduction to Quantum Cryptography:
Or, How Alice Outwits Eve
Sam Lomonaco, CSEE, UMBC
12:00–1:00pm, Friday, 17 November 2017, ITE 231, UMBC
Alice and Bob wish to communicate without the archvillainess Eve eavesdropping on their conversation. Alice decides to take two college courses, one in cryptography, the other in quantum mechanics. During the courses, she discovers she can use what she has learned to devise a cryptographic communication system that automatically detects whether or not Eve is up to her villainous eavesdropping. Some of the topics discussed are Heisenberg’s Uncertainty Principle, the Vernam cipher, the BB84 and B92 cryptographic protocols. The talk ends with a discussion of some of Eve’s possible eavesdropping strategies, i.e., opaque eavesdropping, translucent eavesdropping, and translucent eavesdropping with entanglement.
Samuel J. Lomonaco Jr. received his PhD in mathematics from Princeton University. He has been a full professor of computer science and electrical engineering at the University of Maryland, Baltimore County (UMBC) since 1985, serving as founding chair of the CS Department from 1985 to 1991. Representative Awards, Accomplishments, and Honors include: (1) He was a visiting key research scientist at the Mathematical Sciences Research Institute (MSRI) at the University of California at Berkley in 2004. (2) He was a senior LaGrange fellow at the Institute for Scientific Exchange in Torino, Italy in 2005. (3) For contributions made to the development of the programming language Ada, he received an award from the United States Under Secretary of Defense for Research and Engineering, Dr. Richard DeLauer. (4) He was the first to introduce quantum information science to the American Mathematical Society (AMS) by organizing and giving a two-day AMS short course on quantum computation at the Annual Meeting of the AMS in Washington, DC, in January 2000. (5) He published four books on quantum computation and information science. (6) He accepted an invitation to be a guest editor of the Journal of Quantum Information Processing for a special issue on topological quantum computation.
Host: Alan T. Sherman, *protected email*
The post talk: An Introduction to Quantum Cryptography, Noon Friday 11/17, ITE231 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents An Introduction to Quantum Cryptography: Or, How Alice Outwits Eve Sam Lomonaco, CSEE, UMBC 12:00–1:00pm, Friday, 17 November 2017, ITE 231, UMBC Alice...
https://www.csee.umbc.edu/2017/11/umbc-introduction-quantum-cryptography-lomonaco/
https://beta.my.umbc.edu/api/v0/pixel/news/72612/guest@my.umbc.edu/54e3ce4738d132a9095207c57d198708/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Wed, 15 Nov 2017 08:10:40 -0500
talk: A Practitioner’s Introduction to Deep Learning, 1pm Fri 11/17
ACM Tech Talk Series
A Practitioner’s Introduction to Deep Learning
Ashwin Kumar Ganesan, PhD student
1:00-2:00pm Friday, 17 November 2017, ITE325, UMBC
In recent years, Deep Neural Networks have been highly successful at performing a number of tasks in computer vision, natural language processing and artificial intelligence in general. The remarkable performance gains have led to universities and industries investing heavily in this space. This investment creates a thriving open source ecosystem of tools & libraries that aid the design of new architectures, algorithm research as well as data collection.
This talk (and hands-on session) introduce people to some of the basics of machine learning, neural networks and discusses some of the popular neural network architectures. We take a dive into one of the popular libraries, Tensorflow, and an associated abstraction library Keras.
To participate in the hands-on aspects of the workshop, bring a laptop computer with Python installed and install the following libraries using pip. For windows or (any other OS) consider doing an installation of anaconda that has all the necessary libraries.
- numpy, scipy & scikit-learn
- tensorflow / tensoflow-gpu (The first one is the GPU version)
- matplotlib for visualizations (if necessary)
- jupyter & ipython (We will use python2.7 in our experiments)
Following are helpful links:
Contact Nisha Pillai (NPillai1 at umbc.edu) with any questions regarding this event.
The post talk: A Practitioner’s Introduction to Deep Learning, 1pm Fri 11/17 appeared first on Department of Computer Science and Electrical Engineering.
]]>
ACM Tech Talk Series A Practitioner’s Introduction to Deep Learning Ashwin Kumar Ganesan, PhD student 1:00-2:00pm Friday, 17 November 2017, ITE325, UMBC In recent years, Deep Neural...
https://www.csee.umbc.edu/2017/11/practitioner-introduction-deep-learning-umbc-acm-teck-talk/
https://beta.my.umbc.edu/api/v0/pixel/news/72613/guest@my.umbc.edu/e6c0244a9107e67e192737ee9aca6200/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
graduate
news
research
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Tue, 14 Nov 2017 14:56:17 -0500
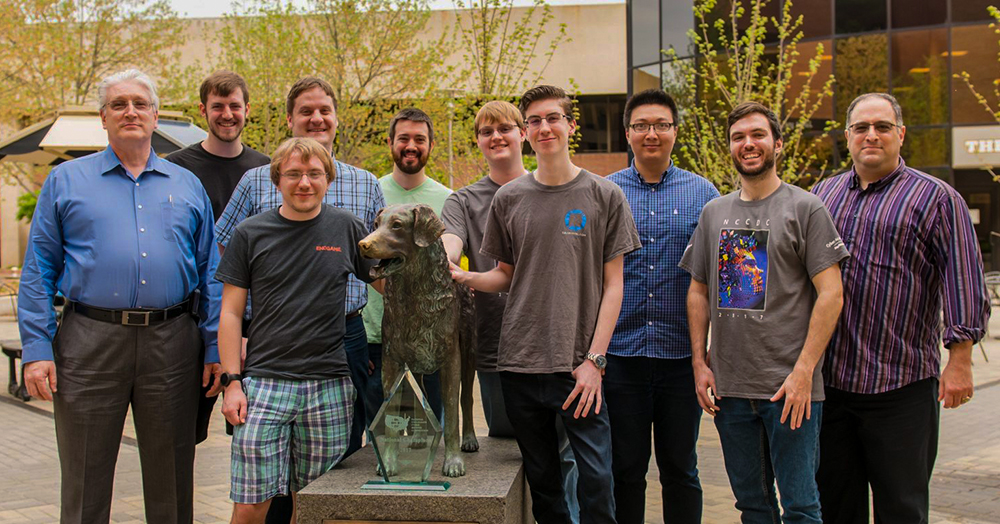
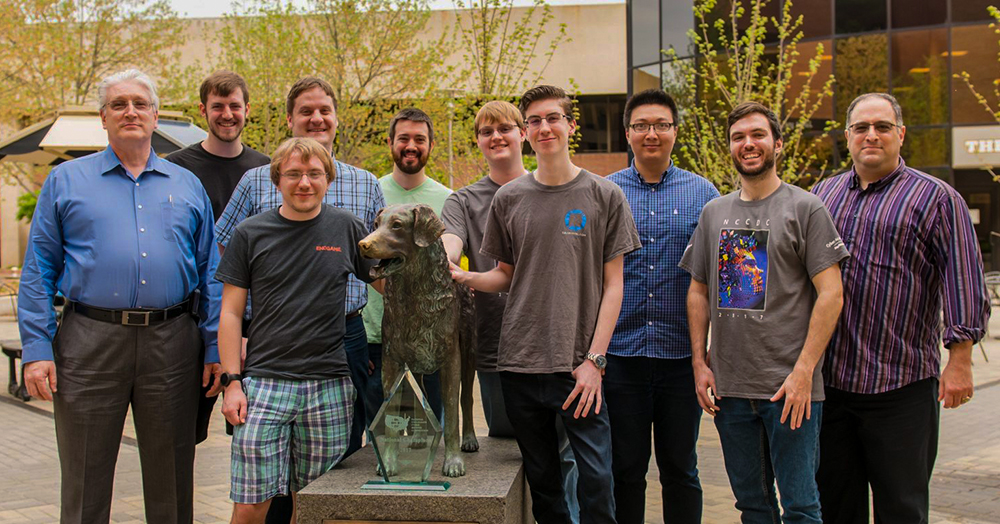
talk: Winning NCCDC, and its practicality in the real world, 12pm 11/3, ITE231
The UMBC Cyber Defense Lab presents
Winning NCCDC, and its practicality in the real world
Bryan Vanek, CSEE, UMBC
12:00noon–1pm Friday, 3 November 2017, ITE 231
The National Collegiate Cyber Defense Competition (NCCDC) takes place every year and gives students an environment where they can develop understanding and operational competency in managing and protecting corporate network infrastructure and business information systems. Competitors participate as the blue team, and try to protect their machines from being infiltrated by the red team, while simultaneously keeping critical services up and running in order for a mock business to stay up and running. After an immense amount of preparation and strife, the UMBC Cyber Defense Team took home its first national title for the competition this year. But what exactly did the team do to prepare for this competition? What exactly happened at the different stages of the competition? And just how practical are these situations in the real world? One of the winning team members will be covering these questions in this week’s CDL, so we hope to see you there!
Bryan Vanek is a UMBC undergraduate computer science major and mathematics minor. In addition to being one of the winning team members for NCCDC, he is currently serving as the president for the UMBC Cyber Defense Team, and is a CWIT T-SITE scholar. He currently works at Interclypse Inc. as a security engineer and software developer, and has had multiple internships and jobs dealing with aspects of computer development and security. Most recently he has completed his second internship at the Department of Defense in the Summer Internship Program for Information Assurance. Upon graduation he will be returning to the DoD as a member of the Computer Network Operations development Program.
Host: Alan T. Sherman, *protected email*
The post talk: Winning NCCDC, and its practicality in the real world, 12pm 11/3, ITE231 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Winning NCCDC, and its practicality in the real world Bryan Vanek, CSEE, UMBC 12:00noon–1pm Friday, 3 November 2017, ITE 231 The National Collegiate...
https://www.csee.umbc.edu/2017/11/talk-winning-nccdc-and-its-practicality-in-the-real-world-umbc-national-collegiate-cyber-defense-competition/
https://beta.my.umbc.edu/api/v0/pixel/news/72614/guest@my.umbc.edu/2df3bde02c8ee6cbd28f3eb7cc49260a/api/pixel
cybersecurity
events
students
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Thu, 02 Nov 2017 22:16:56 -0400
Open House: UMBC Graduate Cybersecurity and Data Science Programs, 6-7:30 Wed. 10/25

Open House: UMBC Graduate Professional Programs
The Fall Open House for UMBC Professional Programs, including the graduate programs on Cybersecurity and Data Science, takes place this coming Wednesday evening, 25 October 2017, at BWTECH South (map) from 6:00-7:30pm.
Students interested in pursuing such programs (MPS degrees and/or certificates) or just to learn more about the field are encouraged to register and attend. Current students interested in pursuing a BS/MPS option for selected programs (such as Cybersecurity or Data Science) are especially welcome.
Attendees who apply to start in Spring 18 will have their UMBC application fee waived.
The programs represented include:
Program directors for these programs will present in individual breakout sessions and relevant support staff from DPS, the UMBC Graduate School, Veterans Affairs, etc. will be on-hand to provide administrative overviews, answer questions, and mingle. Refreshments will be provided.
for more information, directions and to register, see here.
The post Open House: UMBC Graduate Cybersecurity and Data Science Programs, 6-7:30 Wed. 10/25 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Open House: UMBC Graduate Professional Programs The Fall Open House for UMBC Professional Programs, including the graduate programs on Cybersecurity and Data Science, takes place this coming...
https://www.csee.umbc.edu/2017/10/open-house-umbc-graduate-cybersecurity-and-data-science-programs/
https://beta.my.umbc.edu/api/v0/pixel/news/72615/guest@my.umbc.edu/d9644a383040b8e674bb8afcdf28b093/api/pixel
cybersecurity
data-science
education
engineering-management
graduate
news
systems-engineering
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Sat, 21 Oct 2017 15:56:12 -0400
talk: H. Zhang on BFT- From the “Saddest Moment” to the Era of Blockchains, 12pm Fri 10/20
The UMBC Cyber Defense Lab presents
BFT—From the “Saddest Moment” to the Era of Blockchains
Haibin Zhang, CSEE, UMBC
12:00–1:00pm, Friday, 20 October 2017, ITE 231
Blockchains can generally be divided into two categories: permissionless blockchains (e.g., Bitcoin, Ethereum), and permissioned blockchains (e.g., Hyperledger Fabric). In permissionless blockchains, anyone can participate in the protocol. In permissioned blockchains, participants know the IDs of all other participants but do not need to trust them, a particularly useful scenario for business applications. As an emerging technology transforming business models, permissioned blockchains inspired a large number of industrial implementations. The Hyperledger Project (under the Linux Foundation) became a global collaborative project, now with 150+ industry members. Byzantine fault-tolerant (BFT) protocols regained prominence because they can support permissioned blockchain systems. For building permissioned blockchains, BFT is widely regarded as the most appropriate primitive, one accepted by academe and industry. In this talk, I will describe a number of efficient BFT blockchain systems that I helped invent, including BChain, ByzID, CBFT, and secure causal BFT. In addition, I will share my vision for blockchains and associated research opportunities.
Haibin Zhang is an assistant professor in the CSEE Department at UMBC. He is interested in cloud computing, cryptography, security, privacy, and distributed systems. He received the best paper candidate award at the 33rd IEEE International Symposium on Reliable Distributed Systems and proved the security of a NIST standard on ciphertext stealing. Zhang is one of the main inventors of Norton Zone, Symantec’s scalable cloud storage, and BChain, a highly efficient BFT protocol fully implemented within Hyperledger blockchain framework.
Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public
In spring 2018, Sherman will teach a CMSC-491/691 special topics class on blockchains and digital currencies.
The post talk: H. Zhang on BFT- From the “Saddest Moment” to the Era of Blockchains, 12pm Fri 10/20 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents BFT—From the “Saddest Moment” to the Era of Blockchains Haibin Zhang, CSEE, UMBC 12:00–1:00pm, Friday, 20 October 2017, ITE 231 Blockchains can...
https://www.csee.umbc.edu/2017/10/byzantine-fault-tolerant-blockchain-systems/
https://beta.my.umbc.edu/api/v0/pixel/news/72616/guest@my.umbc.edu/151cd79322f938bdf727aa624b9d759d/api/pixel
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Mon, 16 Oct 2017 22:56:46 -0400
talk: Bill Fisher (NCCOE) on IoT Security @ USG 10/30 6-8PM

The UMBC Cybersecurity program at USG Speaker Series Presents
The Internet of Things (IoT)
With speaker
William (Bill) Fisher, NCCoE Security Engineer
Monday, October 30th 6:00-8:00 pm
The Internet of Things (IoT) is the inevitable result of years of Moore’s law – compact, cheap, chip platforms that can take ordinarily house hold items and make them data generating and collection devices that users can manage with their smart phone, web browser or their favorite automation platform. Physical proximity is no longer needed for things like cameras, door locks or thermostats. Instead users remotely access all of these “things” while on the go, even sharing some of their favorite things with friends and family, who need not own the thing, but simply be granted access through a web portal or mobile application. Like many technology trends before it, the IoT has brought great innovation but also great security challenges. These challenges go beyond standards and technology to economic and market forces that hinder security best practices, even for some of the most basic cyber hygiene. Join Bill Fisher of the National Cybersecurity Center of Excellence for a presentation on these challenges and basic mitigations organizations can put into place to help alleviate the risk that the IoT devices pose to consumers and the enterprise.
Speaker Bio:
Bill Fisher is a security engineer at the National Cybersecurity Center of Excellence (NCCoE). In this role, he is responsible for leading a team of engineers that work collaboratively with industry partners to address cybersecurity business challenges facing the nation. He leads the center’s Attribute Based Access Control (ABAC) project, Mobile Application Single Sign On (SSO) for the Public Safety and First Responder Sector, and is part of the ITL Cybersecurity for IoT program. Prior to his work at the NCCoE, Mr. Fisher was a program security advisor for the System High Corporation in support of the Network Security Deployment division at the Department of Homeland Security. He holds a bachelor’s degree in business administration from American University and a master’s degree in cybersecurity from Johns Hopkins University.
Host: Dr. Behnam Shariati (*protected email*) and UMBC Graduate Cybersecurity Association at USG
The post talk: Bill Fisher (NCCOE) on IoT Security @ USG 10/30 6-8PM appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cybersecurity program at USG Speaker Series Presents The Internet of Things (IoT) With speaker William (Bill) Fisher, NCCoE Security Engineer Building III – Room 4230...
https://www.csee.umbc.edu/2017/10/talk-bill-fisher-nccoe-iot-security-usg-1030-6-8pm/
https://beta.my.umbc.edu/api/v0/pixel/news/72617/guest@my.umbc.edu/85d6e62ef63ac2033b32c576bc185d28/api/pixel
computer-science
csee
cybersecurity
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Mon, 16 Oct 2017 11:47:51 -0400
talk: Keith Mayes on Attacks on Smart Cards, RFIDs and Embedded System

Attacks on Smart Cards, RFIDs and Embedded Systems
Prof. Keith Mayes
Royal Holloway University of London
10-11:00am Tuesday, 10 October 2017, ITE 325, UMBC
Smart Cards and RFIDs exist with a range of capabilities and are used in their billions throughout the world. The simpler devices have poor security, however, for many years, high-end smart cards have successfully been used in a range of systems such as banking, passports, mobile communication, satellite TV etc. Fundamental to their success is a specialist design to offer remarkable resistance to a wide range of attacks, including physical, side-channel and fault. This talk describes a range of known attacks and the countermeasures that are employed to defeat them.
Prof. Keith Mayes is the Head of the School of Mathematics and Information Security at Royal Holloway University of London. He received his BSc (Hons) in Electronic Engineering in 1983 from the University of Bath, and his PhD degree in Digital Image Processing in 1987. He is an active researcher/author with 100+ publications in numerous conferences, books and journals. His interests include the design of secure protocols, communications architectures and security tokens as well as associated attacks/countermeasures. He is a Fellow of the Institution of Engineering and Technology, a Founder Associate Member of the Institute of Information Security Professionals, a Member of the Licensing Executives Society and a member of the editorial board of the Journal of Theoretical and Applied Electronic Commerce Research (JTAER).
The post talk: Keith Mayes on Attacks on Smart Cards, RFIDs and Embedded System appeared first on Department of Computer Science and Electrical Engineering.
]]>
Attacks on Smart Cards, RFIDs and Embedded Systems Prof. Keith Mayes Royal Holloway University of London 10-11:00am Tuesday, 10 October 2017, ITE 325, UMBC Smart Cards and RFIDs exist...
https://www.csee.umbc.edu/2017/10/talk-keith-mayes-attacks-smart-cards-rfids-embedded-system-cybersecurity-rfid/
https://beta.my.umbc.edu/api/v0/pixel/news/72618/guest@my.umbc.edu/f693b6777313d350fc774fad7d734ed2/api/pixel
computer-engineering
computer-science
cybersecurity
events
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Fri, 06 Oct 2017 21:46:20 -0400