The UMBC Cyber Defense Lab presents
Human Factors in Cyber Security
Dr. Josiah Dykstra
Cyber Security Researcher, US Department of Defense
12:00–1:00pm Friday, 13 April 2018, ITE 229, UMBC
Humans play many roles in the effectiveness of cyber security. While users are often blamed for security compromises, human strengths and weaknesses also affect people who perform design, implementation, configuration, monitoring, analysis, and response. The fields of human computer interaction generally, and usable security specifically, have drawn attention and research to some aspects of human factors, but many opportunities remain for future work.
In this talk, I describe several of my research projects related to human factors in cyber security. The first was a study of how individual differences affect cyber security behavior, and active follow-on research to predict users who might become victimized. The second was a study of stress and fatigue in security operations centers, including a new survey instrument for collecting data in tactical environments. The third was a research prototype using augmented reality to assist humans in cyber security analysis, and an analysis of preliminary results.
Finally, I will present and invite discussion about a new idea for improving security by making it “disappear.” Despite decades of tools and techniques for secure development, and valiant work at adoption and usability, it is clear that many users cannot or will not avail themselves of appropriate cyber security options. It may be time to rethink the amount of interaction required for most users, and if hands-off, behind-the-scenes cyber defense should be the norm.
Josiah Dykstra serves as a Senior Executive Service government civilian and Subject Matter Expert for Computer Network Operations research in the Laboratory for Telecommunication Sciences within the Research Directorate of the National Security Agency. His research includes human augmentation, cyber risk assessment, and cyber effects. He is an active collaborator with academic, industry, and government researchers around the country. Dykstra earned the PhD degree in computer science at UMBC in 2013 studying under Alan T. Sherman. Dr. Dykstra is the author of the 2016 O’Reilly book, Essential Cybersecurity Science, Fellow of the American Academy of Forensic Sciences, and winner of the Presidential Early Career Award for Scientists and Engineers.
Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public.
The post 🗣️ talk: Human Factors in Cyber Security, 12-1 Fri 4/13, ITE 229, UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Human Factors in Cyber Security Dr. Josiah Dykstra Cyber Security Researcher, US Department of Defense 12:00–1:00pm Friday, 13 April 2018, ITE 229, UMBC...
https://www.csee.umbc.edu/2018/04/umbc-talk-human-factors-in-cybersecurity-josiah-dykstra-hci/
https://beta.my.umbc.edu/api/v0/pixel/news/75472/guest@my.umbc.edu/ae3856ee524c6c1193b62d7d794add15/api/pixel
computer-science
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Sun, 08 Apr 2018 16:27:11 -0400
Sun, 08 Apr 2018 16:27:11 -0400
talk: Cybersecurity as a Team Sport – Understanding Counsel’s Role, 6pm Wed 4/4

Allison Bender J.D.
6:00-8:00pm Wednesday, 4 April 2018
The Universities at Shady Grove
Building III (Camille Kendall Academic Center) Room 4230
9636 Gudelsky Drive, Rockville, Maryland 20850
Directions/Parking
In this presentation by seasoned incident response counsel, Allison Bender, you will gain a risk-informed perspective on the role of counsel in cybersecurity governance and incident response. Also, learn strategies for more effective communication and cooperation with other cybersecurity stakeholders (e.g., IT, IT Security, HR, Communications, business leaders, senior executives and the board); and take away practical tips for prioritizing efforts that help tame the chaos of cybersecurity incident response while maintaining privilege as appropriate.
Allison Bender counsels Fortune 50 companies and startups in a range of industries on cybersecurity and privacy matters in the U.S. and internationally. Drawing from her roots in government, national security, and R&D, she helps clients navigate legal issues associated with emerging technologies and aids clients in strategically managing legal, financial, and reputational cybersecurity risks. Allison translates technical, operational, legal, and policy issues to create practical solutions for clients’ legal challenges. Her cybersecurity and national security preparedness counseling is informed by over 80 incident response efforts. When drafting corporate policies and considering product design options, Allison’s advice is seasoned in the management of breaches involving personal data, intellectual property, payment card information, export controlled technical data, and other regulated information. Her experience also extends to counseling on cybersecurity and national security due diligence in mergers and acquisitions, vendor management, and transactions. From DHS, Allison brings experience in incident response as well as cybersecurity policy, information sharing, liability, and incentives. She was the primary operational legal counsel for the federal response to the Heartbleed vulnerability, the USIS-KeyPoint data breach, and the Healthcare.gov data breach.
Hosts: Dr. Behnam Shariati (*protected email*) and the UMBC Graduate Cybersecurity Association at USG
The UMBC Graduate Cybersecurity Association at USG is an organization created and managed by UMBC Cybersecurity graduate students at Shady Grove. The mission of Cybersecurity Association is to promote the study of Cybersecurity and to raise Cybersecurity awareness and knowledge in the community through panel discussions, conferences, and Cyber competitions. Also, the Cybersecurity Association aspires to create a supportive and positive learning environment in which every member has the opportunity to network, learn, and grow.
The post talk: Cybersecurity as a Team Sport – Understanding Counsel’s Role, 6pm Wed 4/4 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC at Shady Grove Cybersecurity Program Presents Cybersecurity as a Team Sport – Understanding Counsel’s Role Allison Bender J.D. 6:00-8:00pm Wednesday, 4 April 2018 The Universities...
https://www.csee.umbc.edu/2018/03/talk-cybersecurity-team-sport-understanding-counsels-role/
https://beta.my.umbc.edu/api/v0/pixel/news/75116/guest@my.umbc.edu/2f5b7b7cf26b697d3ec816f5139a17d5/api/pixel
csee
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
true
Tue, 27 Mar 2018 22:35:32 -0400

Global Impact, Promise & Perils of Blockchain
UMBC Professors Haibin Zhang (Computer Science and Electrical Engineering) and Karuna Joshi (Information Systems) will be panelists for an event focused on the impact, promise and perils of blockchain technologies at the bwtech@UMBC Research & Technology Park. The event will take place from 8:15 to 11:15am on Tuesday, March 20 2018 at and will include breakfast and time for networking. They will be joined on the panel by Marcus Edwards, from Northrop Grumman’s Cyber & Intelligence Mission Solutions, Steve Cook of Verizon Enterprise Solutions, Sean Manion of Science Distributed and moderator Razvan Miutescu of Whiteford, Taylor & Preston, LLP. For more information and tickets are available on eventbrite.
8:15 – 11:15 Tuesday, March 20, 2018
bwtech@UMBC Research & Technology Park
5520 Research Park Drive, Baltimore, MD 21228
Cryptocurrency market capitalizations have soared over the past year and new innovative blockchain applications are continuing to emerge seemingly by the day. However, the average end-user is left to singularly make sense of a vast and global marketplace that is rapidly converging the core tenets of economics and technology development. The future prospects of traditional business and financial models is uncertain as blockchain technology leaves key decision makers in an untenable position to either adopt and adapt or simply be left behind. Industry and academic experts in the field will discuss the pros and cons and opportunities and challenges of this disruptive technology movement.
The post 🗣️ CyberInnovation Briefing: Global Impact, Promise & Perils of Blockchain appeared first on Department of Computer Science and Electrical Engineering.
]]>
Global Impact, Promise & Perils of Blockchain UMBC Professors Haibin Zhang (Computer Science and Electrical Engineering) and Karuna Joshi (Information Systems) will be panelists for an event...
https://www.csee.umbc.edu/2018/03/umbc-cyberinnovation-briefing-global-impact-promise-perils-of-blockchain/
https://beta.my.umbc.edu/api/v0/pixel/news/74886/guest@my.umbc.edu/071b57ec9d7f66fc52ec392277325cb1/api/pixel
computer-science
cybersecurity
data-science
events
faculty-and-staff
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Fri, 16 Mar 2018 08:34:37 -0400
Fri, 16 Mar 2018 08:34:37 -0400
talk: Creating Educational Cybersecurity Assessment Tools, 12pm Fri 3/9
The UMBC Cyber Defense Lab presents
Creating Educational Cybersecurity Assessment Tools
Alan T. Sherman
Department of Computer Science and Electrical Engineering
University of Maryland, Baltimore County
12:00–1:00pm Friday, March 9, 2018, ITE 229, UMBC
The Cybersecurity Assessment Tools (CATS) Project provides rigorous evidence-based instruments for assessing and evaluating educational practices. The first CAT will be a Cybersecurity Concept Inventory (CCI) that measures how well students understand basic concepts in cybersecurity (especially adversarial thinking) after a first course in the field. The second CAT will be a Cybersecurity Curriculum Assessment (CCA) that measures how well students understand core concepts after completing a full cybersecurity curriculum. These tools can help identify pedagogies and content that are effective in teaching cybersecurity.
In fall 2014, we carried out a Delphi process that identified core concepts of cybersecurity. In spring 2016, we interviewed twenty-six students to uncover their understandings and misconceptions about these concepts. In fall 2016, we generated our first assessment tool—-a draft CCI, comprising approximately thirty multiple-choice questions. Each question targets a concept; incorrect answers are based on observed misconceptions from the interviews. In fall 2017, we began drafting CCA questions. This year we are validating the draft CCI using cognitive interviews, expert reviews, and psychometric testing. In this talk, I highlight our progress to date in developing the CCI and CCA. Audience members will be given an opportunity to answer sample questions.
Presently there is no rigorous, research-based method for measuring the quality of cybersecurity instruction. Validated assessment tools are needed so that cybersecurity educators have trusted methods for discerning whether efforts to improve student preparation are successful.
Joint work with Linda Oliva, David DeLatte, Enis Golaszewski, Geet Parekh, Konstantinos Patsourakos, Dhananjay Phatak, Travis Scheponik (UMBC); Geoffrey Herman, Dong San Choi, Julia Thompson (University of Illinois at Urbana-Champaign)
Alan T. Sherman is a professor of computer science at UMBC in the CSEE Department and Director of UMBC’s Center for Information Security and Assurance. His main research interest is high-integrity voting systems. He has carried out research in election systems, algorithm design, cryptanalysis, theoretical foundations for cryptography, applications of cryptography, and cybersecurity education. Dr. Sherman is also an editor for Cryptologia and a private consultant performing security analyses. Sherman earned the PhD degree in computer science at MIT in 1987 studying under Ronald L. Rivest. www.csee.umbc.edu/~sherman
Support for this research was provided in part by the National Security Agency under grants H98230-15-1-0294 and H98230-15-1-0273 and by the National Science Foundation under SFS grant 1241576.
The post talk: Creating Educational Cybersecurity Assessment Tools, 12pm Fri 3/9 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Creating Educational Cybersecurity Assessment Tools Alan T. Sherman Department of Computer Science and Electrical Engineering University of Maryland,...
https://www.csee.umbc.edu/2018/03/talk-umbc-creating-educational-cybersecurity-assessment-tools/
https://beta.my.umbc.edu/api/v0/pixel/news/74657/guest@my.umbc.edu/91bd7edf5610385a524077e8ba7c9efc/api/pixel
cybersecurity
news
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Fri, 09 Mar 2018 07:30:42 -0500
UMBC Cyber Dawgs Capture The Flag Cybersecurity Competition, Sunday March 11
UMBC Cyber Dawgs
Capture The Flag Cybersecurity Competition
The national champion UMBC Cyber Dawgs will hold the second annual computer security Capture The Flag (CTF) competition on Sunday, March 11th from 11am-7pm in the UC Ballroom. This CTF event is a Jeopardy-style competition where teams of four people use their laptops to discover answers to questions about cybersecurity, including network forensics, reverse engineering, reconnaissance, and cryptography. Each question has a point value based upon its difficulty and whichever team has the most points at the end wins!
The competition is open to all current UMBC students and student from a few other nearby schools. Both beginners and experts are welcome to participate.
Prizes will be awarded to the top teams. There will also be door prizes for randomly selected participants as well as T-Shirts for everyone. Some prizes from last year include Raspberry Pis, a Wireless Pineapple Nano, a YARD Stick One, and a Chromebook! Lunch and dinner (Lima’s Chicken) will be provided for everyone.
Students who are interested must register online in advance and bring a laptop to the event. Please note any dietary restrictions on the registration form as well as your T-Shirt size. See the event website for more information
The post UMBC Cyber Dawgs Capture The Flag Cybersecurity Competition, Sunday March 11 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cyber Dawgs Capture The Flag Cybersecurity Competition The national champion UMBC Cyber Dawgs will hold the second annual computer security Capture The Flag (CTF) competition on Sunday,...
https://www.csee.umbc.edu/2018/02/umbc-cyber-dawgs-capture-flag-cybersecurity-competition-sunday-march-11-2018/
https://beta.my.umbc.edu/api/v0/pixel/news/74319/guest@my.umbc.edu/2e5232853dad24355b1c4efb82961c8a/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
students
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Mon, 26 Feb 2018 23:53:40 -0500
talk: Circuit Complexity of One-Way Boolean Functions, 12pm Fri 2/23, ITE229

The UMBC Cyber Defense Lab presents
Experimentally Measuring the Circuit Complexity
of One-Way Boolean Functions
Brian Weber, CSEE, UMBC
12:00–1:00pm, Friday, 23 February 2018, ITE 229
I present preliminary results from an exhaustive search for one-way functions in certain classes of small Boolean functions. One-way functions are functions that are easy to compute but hard to invert. They are vital for cryptography, yet no one has proven their existence for arbitrary input sizes. For any bounded circuit model of computation, it is possible to search exhaustively over all possible Boolean functions of restricted size and thereby determine for the searched class the maximum disparity between the complexity of any function and its inverse. Throughout, we assume a circuit model in which each gate has fan-in 2 and fan-out 1.
In his 1985 dissertation at MIT, Steven Boyack carried out the first such search. For any positive integers n and M, let Fn,M denote the set of Boolean functions with n inputs and Moutputs. Using circuit size as the complexity measure, Boyack searched the space of every combinatorial function in F3,3 by searching each of 52 equivalency classes of functions in this space. He found that every function class in this space has an identically sized inverse. He was able to prove that functions do exist with more complex inverses outside the space he searched, but not by more than a constant factor.
In spring 2017, using circuit depth as the complexity measure, I searched all injective functions up to F8,8 whose coordinate functions are in F2,1. A coordinate function in this context refers to the function that computes an individual output bit. In addition, I searched up to F4,4 allowing coordinate functions in F3,1. In the space I searched, the most one-way function has fixed depth of 1, and an inverse depth exactly equal to the input size of the function. That is, for each 2 < n < 9, the hardest inverse in the space I searched has a depth of n, where n is the number of input bits. In addition, a search space allowing a larger fan-in for the coordinate functions did not yield functions less invertible than were found in the original search space.
Brian Weber is a senior BS/MS computer engineering student and SFS scholar at UMBC. He hopes to extend the work presented here into his Master’s thesis next year. Email: *protected email*
Host: Alan T. Sherman, *protected email*Support for this research was provided in part by the National Science Foundation under SFS grant 1241576.
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public.
The post talk: Circuit Complexity of One-Way Boolean Functions, 12pm Fri 2/23, ITE229 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Experimentally Measuring the Circuit Complexity of One-Way Boolean Functions Brian Weber, CSEE, UMBC 12:00–1:00pm, Friday, 23 February 2018, ITE 229 I...
https://www.csee.umbc.edu/2018/02/umbc-talk-experimentally-measuring-circuit-complexity-one-way-boolean-functions/
https://beta.my.umbc.edu/api/v0/pixel/news/74246/guest@my.umbc.edu/186a018dd105cdb013ccb23caf98fdaa/api/pixel
computer-science
cybersecurity
news
sfs
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Thu, 22 Feb 2018 22:28:33 -0500
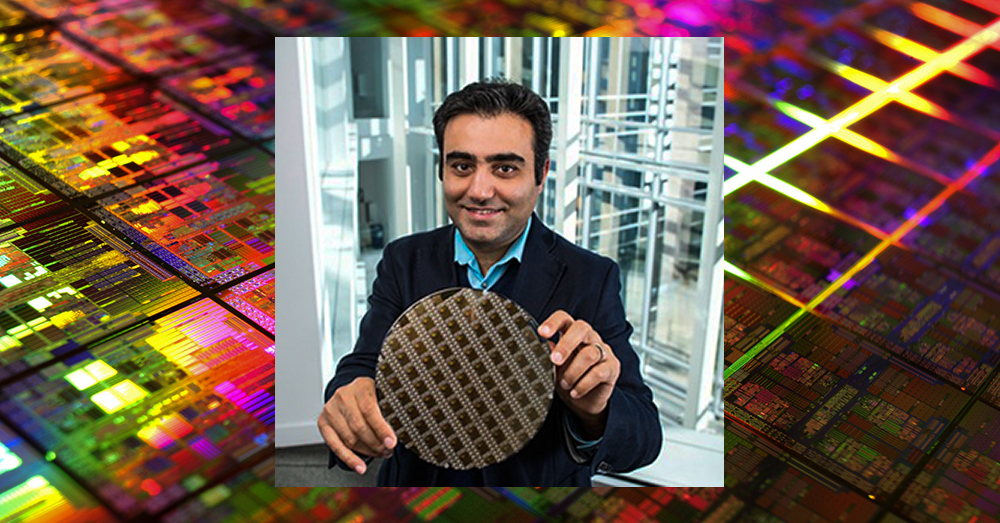
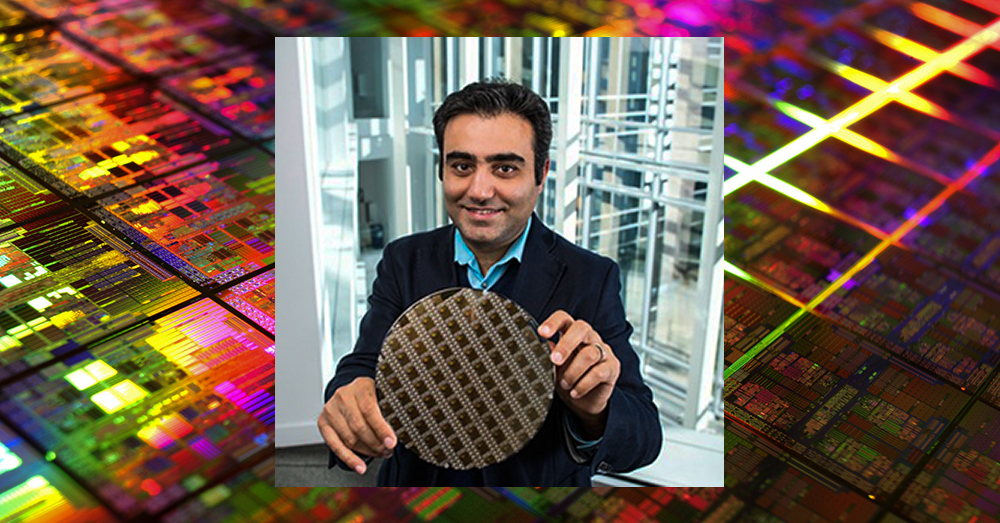
UMBC’s Haibin Zhang shares tips to secure data in the cloud

UMBC’s Haibin Zhang shares tips to secure data in the cloud
As more consumers rely on cloud-based data storage for everything from family photos to financial information, both experts and general users have voiced concerns about cloud security. In a new Conversation article recently published by Scientific American, Haibin Zhang, assistant professor of computer science and electrical engineering, explains precautions consumers can take to protect their files in the cloud.
Zhang explains that data stored and secured using commercial cloud storage systems is encrypted, which means that without the key, the information looks like a series of meaningless characters. Encryption keys have the potential to be misused, if they end up in the wrong hands, which can compromise the security of files stored in a cloud.
“Just like regular keys, if someone else has them, they might be stolen or misused without the data owner knowing,” says Zhang. “And some services might have flaws in their security practices that leave users’ data vulnerable.”
Zhang notes that some cloud services allow customers to maintain their encryption key themselves, which give the consumer the control in ensuring that their data remains safe. Other services keep the encryption keys internally and manage the security for their customers. He says that while each option has benefits, it is important to recognize that “some services might have flaws in their security practices that leave users’ data vulnerable.”
To keep data secure in the cloud, Zhang suggests using enhanced security features offered by cloud storage companies and taking additional precautions that are available to individual customers. He recommends that people use a cloud storage service that allows customers to encrypt their data before uploading it for storage, and to rely on services that have been “validated by independent security researchers.”
Read “How secure is your data when it’s stored in the cloud?” in The Conversation for Zhang’s additional recommendations on securing data on the cloud. The piece also appeared in Scientific American, and has so far been read nearly 20,000 times.
Adapted from a UMBC News article by Megan Hanks. Photo by Yuri Samoilov, CC by 2.0.
The post UMBC’s Haibin Zhang shares tips to secure data in the cloud appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC’s Haibin Zhang shares tips to secure data in the cloud As more consumers rely on cloud-based data storage for everything from family photos to financial information, both experts and...
https://www.csee.umbc.edu/2018/02/umbc-haibin-zhang-tips-secure-data-cloud-cybersecurity-computer-security/
https://beta.my.umbc.edu/api/v0/pixel/news/73767/guest@my.umbc.edu/ac1cc011dc557e189defafd6aae1fa07/api/pixel
computer-science
cybersecurity
faculty-and-staff
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
true
Wed, 07 Feb 2018 14:14:06 -0500
talk: Results of the 2018 SFS Research Study at UMBC, 12pm Fri 2/9, ITE228

The UMBC Cyber Defense Lab presents
Results from the January 2018 SFS Research Study at UMBC
Enis Golaszewski
Department of Information Systems
University of Maryland, Baltimore County
12:00–1:00pm, Friday, 9 February 2018, ITE 228 (or nearby)
January 22-26, 2018, UMBC SFS scholars worked collaboratively to analyze the security of a targeted aspect of the UMBC computer system. The focus of this year’s study was the WebAdmin module that enables users to perform various functions on their accounts, including changing the password. Students identified vulnerabilities involving failure to sanitize user input properly and suggested mitigations. Participants comprised BS, MS, MPS, and PhD students studying computer science, computer engineering, information systems, and cybersecurity, including SFS scholars who transferred from Montgomery College and Prince George’s Community College to complete their four-year degrees at UMBC. We hope that other universities can benefit from our motivational and educational strategy of cooperating with the university’s IT staff to engage students in active project-based learning centering on focused questions about the university computer system.
This project was supported in part by the National Science Foundation under SFS grant 1241576.
Enis Golaszewski (*protected email*) is a PhD student and SFS scholar in computer science working with Dr. Sherman on blockchain, protocol analysis, and the security of software-defined networks.
Host: Alan T. Sherman, *protected email*
The post talk: Results of the 2018 SFS Research Study at UMBC, 12pm Fri 2/9, ITE228 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Results from the January 2018 SFS Research Study at UMBC Enis Golaszewski Department of Information Systems University of Maryland, Baltimore County...
https://www.csee.umbc.edu/2018/02/talk-results-2018-research-study-umbc-cybersecurity-security/
https://beta.my.umbc.edu/api/v0/pixel/news/73664/guest@my.umbc.edu/ceecd69001ec678793247f539105a2f0/api/pixel
computer-science
cybersecurity
students
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Sun, 04 Feb 2018 21:08:32 -0500
talk: Towards Hardware Cybersecurity, 11am Tue 2/20, ITE325, UMBC
Towards Hardware Cybersecurity
11:00am-12:00pm Tuesday, 20 Febuary 2018, ITE 325, UMBC
Electronic system security, trust and reliability has become an increasingly critical area of concern for modern society. Secure hardware systems, platforms, as well as supply chains are critical to industry and government sectors such as national defense, healthcare, transportation, and finance.
Traditionally, authenticity and integrity of data has been protected with various security protocol at the software level with the underlying hardware assumed to be secure, and reliable. This assumption however is no longer true with an increasing number of attacks reported on the hardware. Counterfeiting electronic components, inserting hardware trojans, and cloning integrated circuits are just few out of many malicious byproducts of hardware vulnerabilities, which need to be urgently addressed.
In the first part of this talk I will address the security and vulnerability challenges in the horizontal integrated hardware development process. I will then present the concept of hybrid spin-transfer torque CMOS look up table based design which is our latest effort on developing a cost-effective solution to prevent physical reverse engineering attacks.
In the second part of my talk I will present how information at the hardware level can be used to address some of the major challenges of software security vulnerabilities monitoring and detection methods. I will first discuss these challenges and will then show how the use of data at the hardware architecture level in combination with an effective machine learning based predictor helps protecting systems against various classes of hardware vulnerability attacks.
I will conclude the talk by emphasizing the importance of this emerging area and proposing a research agenda for the future.
Dr. Houman Homayoun is an Assistant Professor in the Department of Electrical and Computer Engineering at George Mason University. He also holds a courtesy appointment with the Department of Computer Science as well as Information Science and Technology Department. He is the director of GMU’s Accelerated, Secure, and Energy-Efficient Computing Laboratory (ASEEC). Prior to joining GMU, Houman spent two years at the University of California, San Diego, as NSF Computing Innovation (CI) Fellow awarded by the CRA-CCC. Houman graduated in 2010 from University of California, Irvine with a Ph.D. in Computer Science. He was a recipient of the four-year University of California, Irvine Computer Science Department chair fellowship. Houman received the MS degree in computer engineering in 2005 from University of Victoria and BS degree in electrical engineering in 2003 from Sharif University of Technology. Houman conducts research in hardware security and trust, big data computing, and heterogeneous computing, where he has published more than 80 technical papers in the prestigious conferences and journals on the subject. Since 2012 he leads ten research projects, a total of $7.2 million in funding, supported by DARPA, AFRL, NSF, NIST, and GM on the topics of hardware security and trust, big data computing, heterogeneous architectures, and biomedical computing. Houman received the 2016 GLSVLSI conference best paper award for developing a manycore accelerator for wearable biomedical computing. Since 2017 he has been serving as an Associate Editor of IEEE Transactions on VLSI. He is currently serving as technical program co-chair of 2018 GLSVLSI conference.
The post talk: Towards Hardware Cybersecurity, 11am Tue 2/20, ITE325, UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
Towards Hardware Cybersecurity Professor Houman Homayoun George Mason University 11:00am-12:00pm Tuesday, 20 Febuary 2018, ITE 325, UMBC Electronic system security, trust and reliability...
https://www.csee.umbc.edu/2018/02/talk-umbc-towards-hardware-cybersecurity-homayoun/
https://beta.my.umbc.edu/api/v0/pixel/news/73663/guest@my.umbc.edu/346faa5a3054d6e7d0b17a902843a9e0/api/pixel
computer-engineering
computer-science
cybersecurity
data-science
events
talks
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Sun, 04 Feb 2018 19:08:51 -0500
Sat, 17 Feb 2018 19:08:51 -0500
UMBC faculty, alumni and partners discuss cybersecurity and industry challenges

UMBC faculty, alumni and corporate partners discuss cybersecurity and industry challenges
Cybersecurity is regularly a headliner in the news, especially when personal information stored online has been compromised, whether through a breach, hack, or threat. On Thursday, December 7, UMBC hosted experts from industry and academia at the National Press Club to discuss the cyber challenges professionals face, and how those groups can work together to prepare future generations of cybersecurity professionals.
Scott Shane, a reporter with The New York Times, led the discussion with five panelists representing industry, small business, and higher education. “I think it’s fair to say the internet was built without adequate attention to security,” stated Shane, who writes about cyber and information attacks regularly. “It’s almost like somebody who starts a bank with branches all over the world, and after it’s up and running and has millions of account holders, suddenly starts to think about safes, locks on the doors and bulletproof glass. I think that’s sort of the stage that we’re at right now.”
UMBC President Freeman Hrabowski and Anupam Joshi, professor and chair of computer science and electrical engineering, and director of the Center for Cybersecurity at UMBC, were joined by alumni and partners who have been working on the challenge of educating the workforce together. Hrabowski explained that there are currently about 350,000 unfilled cybersecurity jobs, and that number is expected to continue to grow. By 2021, it is anticipated that there will be approximately three million job openings in cyber-related fields.
Over the course of his professional career, Nigel Faulkner, chief technology officer at T. Rowe Price, has experienced the emergence of technology and many changes. “As the CTO of a medium-large company, cyber is a defensive investment for us. The best thing that can happen is nothing happens,” Faulkner said, adding that he is always thinking about whether the company is investing enough, doing the right thing, and making the right connections in the industry to keep clients’ information safe.
As president and founder of TCecure, LLC, and cybersecurity academic innovation officer for University System of Maryland (USM), Tina Williams ’02, computer science, shared the importance of building security into technology from the beginning, rather than adding these features on at the “tail end of a development cycle.” Not only does her company handle security, they also monitor threats and risks that can compromise the technology’s health. In her role at USM, Williams represents the system as a whole to integrate academia and academic research, relationships, and resources into what’s taking place nationally, at the Federally Funded Research and Development Centers.
As head of UMBC’s Center for Cybersecurity, Joshi explained that UMBC is combating these national challenges by partnering with industry and government leaders to conduct research that addresses specific real-world needs that benefit both. Collaborative relationships, such as UMBC’s work with Northrop Grumman and T. Rowe Price, is one way that UMBC is working to cultivate the next generation of cybersecurity talent.
As an alumna of UMBC and a current employee at Northrop Grumman, Lauren Mazzoli ’15, computer science and mathematics, M.S. ’17, computer science, a systems engineer in the Future Technical Leaders Program at Northrop Grumman, discussed her experience in the Cyber Scholars Program. The Cyber Scholars Program works to increase the participation of women and underrepresented minorities in the field. Mazzoli explained that her experience at UMBC, in the Cyber Scholars Program, and working alongside mentors on and off-campus led her to be involved with continuing to encourage women to pursue careers in cybersecurity. “For me it’s been a product of the relationship between academia and industry, that have allowed me to find my own career path, and at the same time help others find theirs,” she explained, noting her passion for helping students consider careers in cybersecurity and related fields.
“We know there’s a huge workforce that we need and we can’t fill that pipeline. So yes, we need more women, yes, we need students of all backgrounds, but we need diversity of thought, experience, education, and problem-solving skills,” said Mazzoli, adding that it is important for students to know from a young age that cybersecurity is a field they can pursue.
Adapted from a UMBC News article article written by Megan Hanks Photo by Abnet Shiferaw ’11, visual arts.
The post UMBC faculty, alumni and partners discuss cybersecurity and industry challenges appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC faculty, alumni and corporate partners discuss cybersecurity and industry challenges Cybersecurity is regularly a headliner in the news, especially when personal information stored...
https://www.csee.umbc.edu/2017/12/umbc-faculty-alumni-and-partners-discuss-cybersecurity-and-industry-challenges/
https://beta.my.umbc.edu/api/v0/pixel/news/72825/guest@my.umbc.edu/dfa76de7478d788248e005724b8a3d28/api/pixel
alumni
cybersecurity
events
news
UMBC Cybersecurity Institute Group
https://beta.my.umbc.edu/groups/cybersecurity
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
2
0
true
Thu, 14 Dec 2017 20:39:18 -0500