MS defense: A Framework for GPU 3D Model...
Full Title: MS defense: A Framework for GPU 3D Model Reconstruction Using Structure-from-Motion
MS Defense
A Framework for GPU 3D Model Reconstruction
Using Structure-from-Motion
Yu Wang
10:00am Thursday, 28 April 2011, ITE 352
A framework for three-dimensional (3D) model reconstruction is described in this thesis. The primary application is scanning forest canopies and assisting scientific applications such as fire hazard evaluation and vegetation biomass estimation, using photos taken from a radio-controlled helicopter, although the methods apply to any series of photographs taken along a path. The approach is based on the fact that the photos are taken in a continuous path, thus taking advantage of the adjacency between images. The major contributions of this project are 1) introduce a linear time complexity algorithm that reduces number of image pairs to match for datasets obtained in a continuous path. 2) present an optimized high performance framework for GPU 3D reconstruction using structure-from-motion.
Thesis Committee:
- Dr. Marc Olano, Chair
- Dr. Penny Rheingans
- Dr. Erle Ellis
]]>
Full Title: MS defense: A Framework for GPU 3D Model Reconstruction Using Structure-from-Motion MS Defense A Framework for GPU 3D Model Reconstruction Using Structure-from-Motion Yu Wang...
http://www.cs.umbc.edu/2011/04/3569/
https://beta.my.umbc.edu/api/v0/pixel/news/6593/guest@my.umbc.edu/f7ee8e2e9b9790faf06d980848806cc5/api/pixel
computer-science
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
false
Mon, 25 Apr 2011 20:51:44 -0400
MS defense: eXtensible Dynamic Form (XDF) for...
Full Title: MS defense: eXtensible Dynamic Form (XDF) for Supplier Discovery
MS Thesis Defense
eXtensible Dynamic Form (XDF) for Supplier Discovery
Yan Kang
1:00PM Tuesday, 26 April 2011, ITE 346
Discovery of suppliers (supplier discovery) is essential for building a flexible network of suppliers in a supply chain. The first step for supplier discovery is to collect manufacturing capabilities of suppliers and requirements of customers. In traditional e-marketplaces, online form interfaces are typically used to collect the requirements and capabilities. However, those forms are mostly lack of flexibility to capture a variety of requirements and capabilities in a structured way. In this thesis, we propose new innovative form architecture called eXtensible Dynamic Form (XDF) to facilitate data collection process of supplier discovery.
This architecture provides several key innovations including: 1) architecture for users (suppliers or customers) to create new structure of form for their own contents; 2) an intelligent search engine facilitating users to reuse the existing form components 3) hierarchical representation of the requirements and capabilities as XML instances. Experimental results demonstrate that the proposed architecture is valuable for facilitating the supplier discovery process.
Thesis Committee:
- Dr. Charles Nicholas
- Dr. Yun Peng (Chair)
- Dr. Yelena Yesha
]]>
Full Title: MS defense: eXtensible Dynamic Form (XDF) for Supplier Discovery MS Thesis Defense eXtensible Dynamic Form (XDF) for Supplier Discovery Yan Kang 1:00PM Tuesday, 26 April 2011,...
http://www.cs.umbc.edu/2011/04/ms-defense-extensible-dynamic-form-xdf-for-supplier-discovery/
https://beta.my.umbc.edu/api/v0/pixel/news/6585/guest@my.umbc.edu/97312fabd23cb4829febec3f4df9dd11/api/pixel
computer-science
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
false
Mon, 25 Apr 2011 14:18:06 -0400
Mon, 25 Apr 2011 14:18:06 -0400
MS defense: Recovering from Soft Node Failures in...
Full Title: MS defense: Recovering from Soft Node Failures in Wireless Sensor Networks using Neural Networks
MS Thesis Defense
Recovering from Soft Node Failures in
Wireless Sensor Networks using Neural Networks
Shivvasangari Subramani
9:00am Tuesday, 26 April 2011, ITE 346
In the past few years, wireless sensor networks (WSNs) have become important in different applications because of their robustness in hostile environments. WSNs need to perform in a timely manner in the face of interference, attacks, accidents, and failures. Being a battery operated system, there is a trade-off between performance and energy utilization. In this thesis we focus on WSN accuracy and consider ways to improve the performance of WSNs when sensors become damaged, resulting in poor input signal quality. When all other components of the sensor like the processor, memory, and battery are working, our proposed solution is to learn to undo the damage in a node by training on neighbors sensor values.
Thesis Committee:
- Dr. Anupam Joshi
- Dr. Tim Oates (chair)
- Dr. Mohamed Younis
]]>
Full Title: MS defense: Recovering from Soft Node Failures in Wireless Sensor Networks using Neural Networks MS Thesis Defense Recovering from Soft Node Failures in Wireless Sensor Networks...
http://www.cs.umbc.edu/2011/04/3555/
https://beta.my.umbc.edu/api/v0/pixel/news/6581/guest@my.umbc.edu/11f5133ee01961143c83041c7a699b8d/api/pixel
computer-science
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
false
Mon, 25 Apr 2011 11:59:11 -0400
Mon, 25 Apr 2011 11:59:11 -0400
MS defense: Graph-Theoretic Approach to Collusion...
Full Title: MS defense: Graph-Theoretic Approach to Collusion Detection in Multi-Agent Systems
MS Thesis Defense
A Graph-Theoretic Approach to
Collusion Detection in Multi-Agent Systems
Peter Hamilton
9:00am Thursday, 28 April 28 2011, ITE 325B
The study of trust and cooperation is a major component of multi-agent systems research. Such work often focuses on how best to estimate the reliability of a specific agent, or how to create strategies and protocols that engender the most cooperation from the most agents. However, when cooperation is not a desired aspect of a multi-agent system, these actions define collusive behavior, which can have a significant impact on the dynamics of the system.
This thesis defines a generic, graph-theoretic approach to collusion detection known as CODING. This approach detects group-based collusion, targeting two basic collusion mechanisms that rely on large numbers of colluding agents for success. CODING analyzes and classifies agent interactions from the system and constructs a series of interaction graphs from this data. These graphs are processed for structures that correspond to collusion mechanisms; the agents composing these structures are reported as colluders. CODING is applied to a game theory domain, in which it must detect agents adhering to group strategies in round-robin tournaments composed of single-player strategies.
Thesis Committee:
- Dr. Marie desJardins (chair)
- Dr. Tim Finin
- Dr. Tim Oates
]]>
Full Title: MS defense: Graph-Theoretic Approach to Collusion Detection in Multi-Agent Systems MS Thesis Defense A Graph-Theoretic Approach to Collusion Detection in Multi-Agent Systems...
http://www.cs.umbc.edu/2011/04/ms-defense-graph-theoretic-approach-to-collusion-detection-in-multi-agent-systems/
https://beta.my.umbc.edu/api/v0/pixel/news/6571/guest@my.umbc.edu/c44e3e2bab826ef200fa4aa79e13bb83/api/pixel
computer-science
events
graduate
news
other
research
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
false
Sun, 24 Apr 2011 23:38:20 -0400
MS defense: Feature Extraction using a Hierarchical...
Full Title: MS defense: Feature Extraction using a Hierarchical Growing Neural Gas
M.S. Thesis Defense Announcement
Feature Extraction using a Hierarchical Growing Neural Gas
Roger Guseman
12:00pm 25 April 2011, ITE 210
Unsupervised, data-driven, automatic feature extraction from image data is an interesting and difficult problem. High dimensional data, such as images, often contain less information than they do data. For an agent to better reason about this data, finding the "interesting" features in the data is helpful. A current technique, known as the Growing Neural Gas (GNG), is a neural network approach to feature extraction. There are, however, adaptations that can be made to the Growing Neural Gas in order to increase its performance.
Contributions of this work include development of a new neural network algorithm extending the Growing Neural Gas framework, known as the Hierarchical Growing Neural Gas (HGNG), identification of how the parameters of the HGNG affect feature extraction performance, and theoretical and empirical comparisons of performance between the normal GNG and the HGNG neural networks.
Thesis Committee:
- Dr. Tim Oates (chair)
- Dr. Tim Finin
- Dr. Marie desJardins
]]>
Full Title: MS defense: Feature Extraction using a Hierarchical Growing Neural Gas M.S. Thesis Defense Announcement Feature Extraction using a Hierarchical Growing Neural Gas Roger Guseman...
http://www.cs.umbc.edu/2011/04/3539/
https://beta.my.umbc.edu/api/v0/pixel/news/6570/guest@my.umbc.edu/592866d0a82717a51f8f2472af52aaec/api/pixel
computer-science
events
graduate
news
research
talks
thesis-defense
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
false
Sun, 24 Apr 2011 22:51:18 -0400
MS defense: Problem selection of program tracing...
Full Title: MS defense: Problem selection of program tracing tasks in an intelligent tutoring system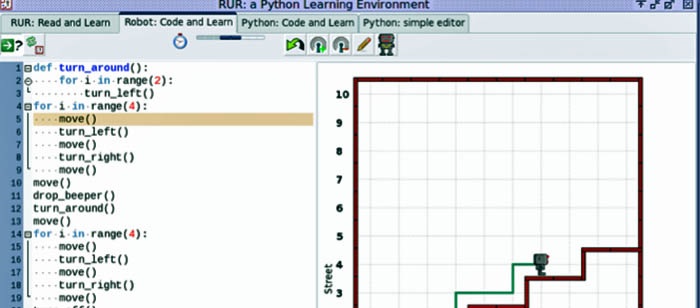
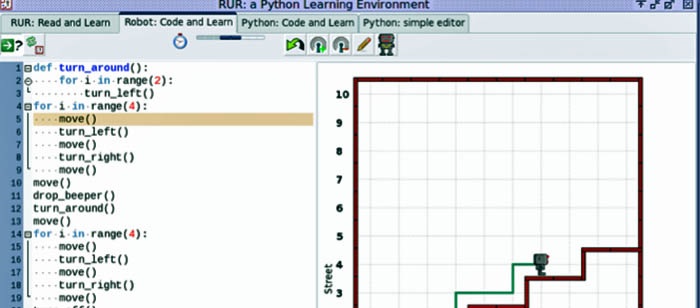
Master's Thesis Defense Announcement
Problem Selection of Program Tracing Tasks in an Intelligent
Tutoring System and Visual Programming Environment
David Walser
2:00pm Thursday, 28 April 2011, ITE 325b
Intelligent tutoring systems (ITSs) have been shown to be an effective supplementary teaching tool or aid for many domains. Applying ITSs in open-ended domains such as computer programming is especially challenging, most notably when trying to assist with the process of programming itself. Existing ITSs for programming focus on a very limited set of problems and concepts and are only useful early in an introductory CS course and a few limited places afterward. Visual programming environments are another tool that have been used in introductory CS courses to help students learn basic concepts. The key idea behind my work is the recognition of the importance of students' ability to read, understand, and trace code in order to write programs successfully. A broader goal of my work is to show that an ITS based on a visual programming environment can be used to support students throughout an entire introductory CS course, without being severely constrained and limited to a small number of concepts and to low-level, simple tasks. In my system, called RUR-ITS, students are given a program and are asked to predict the robot's behavior when running this program in a given environment. RUR-ITS allows each problem to be assigned a difficulty level and multiple concepts that it involves within the conceptual model. RUR-ITS can then use a problem selection algorithm to choose a problem that is most able to help the student master the concepts that they have not yet mastered.
Thesis Committee:
- Dr. Marie desJardins, Chair
- Dr. Tim Finin
- Dr. Tim Oates
]]>
Full Title: MS defense: Problem selection of program tracing tasks in an intelligent tutoring system Master's Thesis Defense Announcement Problem Selection of Program Tracing Tasks in an...
http://www.cs.umbc.edu/2011/04/3524/
https://beta.my.umbc.edu/api/v0/pixel/news/6553/guest@my.umbc.edu/3c5a26b2c632df443e288866fc7adb16/api/pixel
computer-science
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
false
Fri, 22 Apr 2011 20:48:15 -0400
Demand up for technology graduates

USA Today has an article on the increased recruiting by technology companies, Tech jobs boom like it's 1999. Potential employees are being lured with good salaries, bonuses, and perks, and some predict that almost 150,000 technology jobs will be added in 2011.
"Nearly 150,000 tech jobs are expected to be added this year, says Sophia Koropeckyj, an economist at Moody’s Analytics. In February, there were about 6.1 million tech jobs in the U.S., up 2.4% from a year ago. Yet there’s a lot to make up for: From the second quarter of 2008 through the first quarter of 2010, during the economic swoon, 308,000 tech jobs were lost."
Companies such as Google, Facebook, and Microsoft are recruiting students to try to hire them before they graduate, says former Google software engineer Gayle Laakmann McDowell. Some economists see the boom in tech hires as a good indication that the overall U.S. economy is on the rise, since technologies such as wireless, computing, and energy have a big impact on other sectors.
"A surge in tech hires in California could portend an upturn for the overall U.S. economy, says Jesse Harriott, chief knowledge officer at online job site Monster.com. That’s in part because what’s good for tech will touch related industries. Areas such as wireless, computing and energy have an effect on “a substantial part of the economy, such as logistics, inventory management, enterprise coordination, even hybrid autos, says Shane Greenstein, a management professor at Northwestern University’s Kellogg School of Management. Entrepreneurs and venture capitalists foresee growth in wireless apps, online gaming and clean tech, he says. “It is not a classic tech boom, led by a big new opportunity like (Internet) browsing or Web 2.0, but a mixture of a few big and unrelated trends,” Greenstein says.
We've seen the increased interest in our students here in the Computer Science and Electrical Engineering department and it includes both undergraduates and graduates. The demand is up not just for science, engineering, mathematics and technology majors but also for majors in the liberal arts and other areas who have acquired a portfolio of math and technology skills.
]]>
USA Today has an article on the increased recruiting by technology companies, Tech jobs boom like it's 1999. Potential employees are being lured with good salaries, bonuses, and perks, and some...
http://www.cs.umbc.edu/2011/04/demand-up-for-technology-graduates/
https://beta.my.umbc.edu/api/v0/pixel/news/6551/guest@my.umbc.edu/54e4bea04535f19e85e3520f63dddfb7/api/pixel
jobs
news
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
5
0
false
Fri, 22 Apr 2011 17:51:14 -0400
talk: Working Together Apart, 12:00 4/29

Spring 2011 Information Systems Distinguished Lecture
Working Together Apart
Dr. Judy Olson
Donald Bren Professor of Information and Computer Sciences
University of California, Irvine
12:00pm Friday, 29 April 2011, ITE Lecture Hall VII
Our research group has been investigating the factors that make long distance teamwork work. I will review that work and talk about the issues that remain, the factors that technology and social practices can't solve–cultural differences and different timezones. And, I will introduce our "theory made practical," our turning the theory into an online assessment tool.
Judith Olson is the Bren Professor of Information and Computer Sciences in the Informatics Department at the UC Irvine, with courtesy appointments in the School of Social Ecology and the Merage School of Business. She has researched teams whose members are not collocated for over 20 years, summaries of which are found in her most cited paper, “Distance Matters,” (Olson & Olson, 2000), and in her key theoretical contribution in the book Scientific Collaboration on the Internet (Olson, Zimerman, and Bos, Eds., 2008). Her current work focuses on ways to verify the theory's components while at the same time helping new scientific collaborations succeed. She has studied distributed teams both in the field and in the laboratory, the latter focusing on the communication hurdles distributed teams have and the consequent underutilization of remote team members skills and the reduction in trust. She is a Fellow of the Association for Computing Machinery and with her husband and colleague, Gary Olson, holds the Lifetime Achievement award from the Special Interest Group in Computer Human Interaction.
· directions · talks · events ·
]]>
Spring 2011 Information Systems Distinguished Lecture Working Together Apart Dr. Judy Olson Donald Bren Professor of Information and Computer Sciences University of California, Irvine...
http://www.cs.umbc.edu/2011/04/talk-working-together-apart-1200-429/
https://beta.my.umbc.edu/api/v0/pixel/news/6508/guest@my.umbc.edu/f58a31ef312184fef03fa9ab030ef8d8/api/pixel
events
news
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
false
Wed, 20 Apr 2011 19:43:47 -0400
Maryland Cyber Conference and Challenge (MDC3)
The Maryland Cyber Challenge and Conference site is up and student teams can now register for the competition, with the first qualifying round early in September. It is a chance to demonstrate your ability to work in a team and your cybersecurity and problem solving skills.
MDC3 is a joint effort between SAIC, UMBC, DBED, TCM and NCSA to bring people together to promote Maryland's commitment to cybersecurity and STEM education. The competition includes three levels: high school, collegiate and professionals from industry/government, providing opportunities to network with cybersecurity professionals, researchers, and scholars.
There will be orientation sessions at the UMBC Technology Center (1450 South Rolling Rd., 21224) on May 2, May 18 and June 21 at 4:30pm for professionals and 6:00pm for students.
]]>
The Maryland Cyber Challenge and Conference site is up and student teams can now register for the competition, with the first qualifying round early in September. It is a chance to demonstrate...
http://www.cs.umbc.edu/2011/04/maryland-cyber-conference-and-challenge-mdc3/
https://beta.my.umbc.edu/api/v0/pixel/news/6506/guest@my.umbc.edu/3c7f48729256822f715e2fbe0c1bdbaa/api/pixel
computer-engineering
computer-science
cybersecurity
electrical-engineering
events
graduate
news
undergraduate
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
false
Wed, 20 Apr 2011 14:55:34 -0400
Semantic Analysis of XML Schema Matching for B2B...
Full Title: Semantic Analysis of XML Schema Matching for B2B (Dissertation Defense)
PhD Dissertation Defense Announcement
A Semantic Analysis of XML Schema Matching
for B2B Systems Integration
Jaewook Kim
11:00am Thursday, 21 April 2011, ITE 346
One of the most critical steps to integrating heterogeneous e-Business applications using different XML schemas is schema matching, which is known to be costly and error-prone. Many automatic schema matching approaches have been proposed, but the challenge is still daunting because of the complexity of schemas and immaturity of technologies in semantic representation, measuring, and reasoning. The dissertation focuses on three challenging problems in the schema matching. First, the existing approaches have often failed to sufficiently investigate and utilize semantic information imbedded in the hierarchical structure of the XML schemas. Secondly, due to synonyms and polysemies found in natural languages, the meaning of a data node in the schema cannot be determined solely by the words in its label. Thirdly, it is difficult to correctly identify the best set of matching pairs for all data nodes between two schemas. To overcome these problems, we propose new innovative approaches for XML schema matching, particularly applicable to XML schema integration and data transformation between heterogeneous e-Business systems. Our research supports two different tasks: integration task between two different component schemas; and transformation task between two business documents which confirm to different document schemas.
Dissertation Committee:
- Dr. Yun Peng, Chair
- Dr. Charles Nicholas
- Dr. Zary Segall
- Dr. Milton Halem
- Dr. Hyunbo Cho (POSTECH, Korea)
- Dr. Nenad Ivezic (NIST)
]]>
Full Title: Semantic Analysis of XML Schema Matching for B2B (Dissertation Defense) PhD Dissertation Defense Announcement A Semantic Analysis of XML Schema Matching for B2B Systems...
http://www.cs.umbc.edu/2011/04/3486/
https://beta.my.umbc.edu/api/v0/pixel/news/6467/guest@my.umbc.edu/7cbee9daf6bed3b5a8fea58e5426878f/api/pixel
computer-science
dissertation
graduate
news
talks
Computer Science and Electrical Engineering
https://beta.my.umbc.edu/groups/csee
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-beta.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
false
Mon, 18 Apr 2011 14:33:19 -0400
Mon, 18 Apr 2011 14:33:19 -0400